Advert blockers are supposed to preserve us secure, however a latest discovery by threat-hunting agency Huntress reveals simply how simply these instruments may be turned towards us. Huntress’ menace analysts not too long ago recognized a sneaky new marketing campaign by the KongTuke hacking group, involving utilizing a trick named CrashFix to interrupt into company computer systems by pretending to repair the very issues they created.
The Entice
It begins with a faux advert blocker referred to as NexShield, which is a near-perfect clone of the favored “uBlock Origin Lite. To make it seem genuine, the hackers solid the code headers to falsely credit score the true developer, Raymond Hill, included hyperlinks to a non-existent “assist” web site, and even hosted it on the official Chrome Internet Retailer beneath the developer’s electronic mail [email protected].
As soon as put in, NexShield waits 60 minutes earlier than launching a denial-of-service (DoS) assault towards your laptop. It does this by operating a hidden script that makes an attempt to attach a billion occasions directly, which deliberately exhausts your system assets. This causes your tabs to freeze and ultimately triggers a complete browser crash.
How the CrashFix Really Infects You
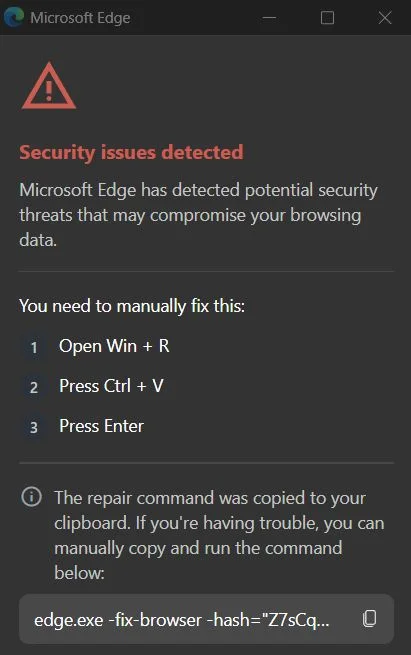
Once you restart your browser, a professional-looking “Safety Warning” pops up claiming your browser “stopped abnormally.” This can be a new model of the ClickFix assault. If you happen to run the recommended scan, a faux alert seems saying “Safety points detected!” The extension tells you to hit Win+R and paste a command with Ctrl+V to repair it.
In the meantime, the extension has already silently copied a malicious command to your clipboard. This command abuses an actual Home windows device referred to as finger.exe, renaming it to ‘ct.exe’ to obtain the backdoor onto your system, researchers defined within the weblog publish.
The Backdoor: ModeloRAT
The ultimate payload is ModeloRAT, a spying device written within the Python programming language. This malware acts as a hidden entrance, permitting hackers to watch your information and steal firm passwords. It even hides in your settings utilizing names like “Spotify47” or “Adobe2841” to appear like regular software program.
What makes KongTuke’s marketing campaign so harmful is the way it avoids detection. It makes use of a method referred to as Fingerprinting to examine if it’s being watched, scans for over 50 completely different safety instruments, like Wireshark or x64dbg, and checks for usernames like “John Doe” which are generally utilized in analysis labs. If the virus detects a researcher’s machine, it merely stops working or sends again a faux message saying “TEST PAYLOAD!!!!” to waste the knowledgeable’s time.
It’s price noting that KongTuke prioritises enterprise targets and ignores residence customers for now. To remain secure, at all times double-check the developer of a browser extension earlier than downloading. In case your browser crashes and all of a sudden asks you to run handbook instructions, it’s doubtless a entice.