149 million stolen usernames and passwords for TikTok, Disney+, Netflix, Roblox, and crypto wallets have been discovered on-line with none safety authentication. Be taught in regards to the newest huge information leak and the best way to safe your digital identification at present.
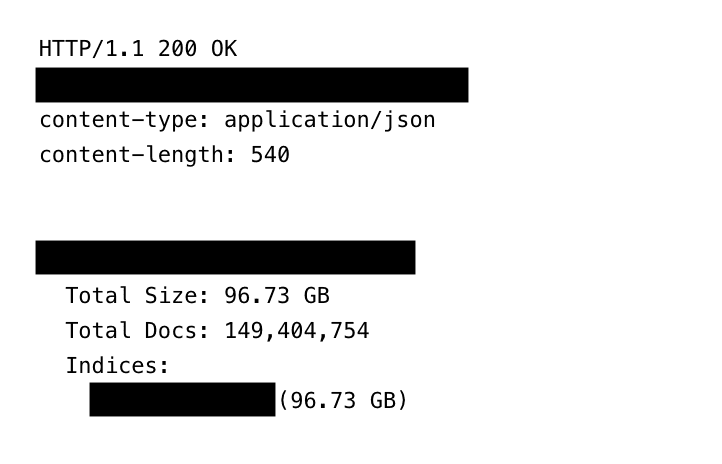
A large database containing over 149 million stolen usernames and passwords has been taken offline after sitting extensive open on the web for weeks. Cybersecurity researcher Jeremiah Fowler found the uncovered cache, noting that the publicity “highlights the worldwide risk” of information theft as a result of it allowed anybody with an online browser to view and search the data. This analysis was revealed by ExpressVPN and shared with Hackread.com.
A One-Cease Store for Hackers
The database, totalling 96 GB, was not only a static pile of previous leaks. Whereas Fowler spent almost a month making an attempt to alert the internet hosting supplier, he seen the gathering was truly rising in real-time. The sheer number of the stolen information is what makes this discovery so troubling. The data included accounts for:
- Social Media: Fb (17M logins), Instagram, TikTok, and X.
- Streaming and Video games: 3.4M Netflix logins, plus HBOmax, Disney+, and Roblox.
- Financials: Banking portals, bank card accounts, and 420,000 Binance crypto logins.
- Delicate Websites: Courting apps and OnlyFans accounts, affecting each creators and clients.
The database contained 48 million Gmail accounts, roughly 4 million Yahoo logins, 1.5 million for Microsoft Outlook, and 900,000 for Apple’s iCloud. Much more regarding, it contained login particulars for presidency (.gov) domains from a number of international locations. Fowler famous that even restricted entry to those accounts might enable hackers to impersonate officers or slip into safe authorities networks.
The Thriller of the Infostealer
How did all this information get there? As per Fowler’s analysis, the culprits possible used infostealer malware, a software program that infects your pc or cellphone and data every little thing you kind. However this was completely different from earlier leaks as a result of this particular operation appeared way more organised than common.
Equivalent to, the system used a reversed labelling technique to kind information by the precise machine and the web site it got here from. This should’ve made it straightforward for criminals to look victims whereas serving to the malware dodge primary safety scans. Moreover, each entry had a novel fingerprint (or hash) to make sure no duplicates have been saved.
Morey Haber, Chief Safety Advisor at BeyondTrust commented on this, stating, “Authentication greatest practices all the time advocate: distinctive passwords for each web site, by no means reusing passwords, enabling MFA or a minimum of 2FA for web site (and avoiding 1FA at any time when doable), utilizing a monitoring service like LegalShield, LifeLock, and many others. and even the inbuilt password safety detection constructed into Apple IOS to find out if credentials are uncovered on the darkish net so customers can change their passwords – and lastly, by no means accepting 2FA/MFA notifications except you’ve gotten initiated them.“
“As for the supply of the info, infostealing malware can come from quite a lot of sources, like sideloading purposes, jailbreaking, vulnerabilities/exploits, and many others. Customers ought to solely use verified sources for purposes (AppStore) and on relevant units, guaranteeing they’re working anti-virus options with the newest updates,” Haber warned.
A Month of Publicity
Velocity, as we all know it, is crucial when securing a leak, however Fowler hit a wall throughout the reporting course of. It took a month of “a number of makes an attempt” earlier than the internet hosting supplier lastly suspended the server. Nonetheless, the harm could already be completed. Because the data included actual login net addresses (URLs), it turned extremely straightforward for criminals to automate assaults.
To remain secure, the most effective defence is utilizing a password supervisor and enabling two-factor authentication. Conserving your working system up to date can also be a significant step in patching the holes that malware makes use of to get inside.