Many firm executives and get in touch with middle leaders know in regards to the struggles to guard buyer knowledge. With elevated distractions or assessing how new know-how, like AI, can enhance contact middle providers, firm leaders cannot lose concentrate on rising safety threats that would compromise knowledge.
Contact middle safety should stay a focus to guard buyer knowledge and improve buyer confidence when interacting with a company, which is vital to higher buyer relationships and experiences.
The rising significance of contact middle safety
Contact middle safety should be entrance and middle when creating and implementing a strategic buyer expertise framework. Organizations that do not make use of correct safety controls may threat severe destructive penalties, equivalent to the next:
- Monetary. A safety or knowledge breach can lead to misplaced enterprise income and fines levied by numerous entities that considerably have an effect on the underside line.
- Fame. Clients who really feel their private knowledge is not safe or who’ve been affected by safety incidents, equivalent to identification theft, would possibly now not do enterprise with the group or submit their issues on numerous social channels. The goodwill and constructive status a company builds over time is likely one of the largest drivers to buying and retaining prospects.
- Enterprise disruption. Assets devoted to operating the enterprise should be redirected to analysis and resolve the incident and enhance safety protocols.
Sorts of contact middle safety finest practices
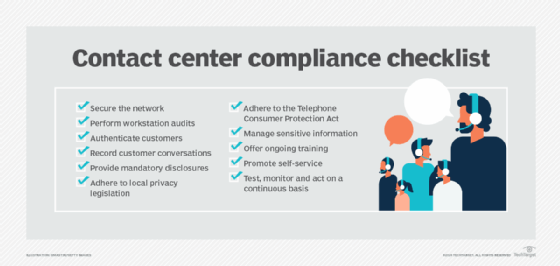
To keep away from safety issues, companies must implement a contact middle safety guidelines that covers three classes: know-how, buyer and enterprise finest practices.
Expertise finest practices
To be able to shield buyer knowledge and keep safety, corporations and their contact facilities ought to implement the next know-how guidelines:
Encrypt knowledge. Encryption interprets a company’s saved or transmitted knowledge into totally different kinds, which require a particular key to translate it again into its authentic format. Organizations usually encrypt knowledge to guard particular buyer data, together with medical, bank card or private data.
Replace know-how. Maintaining know-how present ensures methods and elements have the most recent safeguards in place. Dangerous actors constantly check methods, in search of cracks that permit them entry knowledge. Key practices to replace know-how embrace antivirus software program, putting in software program patches and eliminating legacy methods that distributors now not help.
Reduce knowledge availability and entry. Extra knowledge is being saved every day. And, with extra people given entry to that data, a company multiplies its threat of a possible knowledge breach. Greatest practices to reduce availability and entry to knowledge embrace the next:
- Limit the quantity of people that can entry delicate data.
- Use system permissions to handle who can entry particular knowledge.
- Automate session timeout guidelines.
- Delete worker entry to accounts as quickly because the particular person leaves the group.
- Masks delicate knowledge to restrict the knowledge exhibited to workers. For instance, place asterisks over the primary 5 digits of a Social Safety quantity.
- Use alternate applied sciences to seize delicate data. For instance, ship a caller to an interactive voice response system to enter bank card data.
- Restrict the storage of crucial data. For instance, delete knowledge after a buyer gives a bank card quantity in a transaction. This situation represents a tradeoff between buyer comfort and knowledge safety.
- Use firewalls and intrusion detectors to stop and report tried and unauthorized exercise.
Carry out common knowledge backups. Common knowledge backups ought to be established to reduce knowledge loss and supply the flexibility to recreate buyer data within the occasion of a safety breach.
https://www.youtube.com/watch?v=https://youtu.be/SuNtmCgIhiM
Buyer finest practices
Companies ought to institute the next customer-related finest practices to guard buyer knowledge:
Preserve transparency. Corporations should be clear with prospects, together with telling them why the enterprise requires delicate knowledge and the way it makes use of and protects that data. Efficient transparency goes past typical privateness statements, and organizations ought to share this data in an easy-to-understand format.
Transparency improves buyer confidence, which instills a better stage of belief within the group. Moreover, if a company can educate its prospects easy methods to shield themselves — like easy methods to monitor bank card utilization — they really feel higher about sharing data.
Use authentication protocols. Authentication goals to show anyone is the particular person they declare to be. Prior to now, typical authentication protocols used single-factor authentication that required customers to enter a single piece of figuring out data, equivalent to a password. Many organizations have shifted to multifactor authentication, the place customers should enter a number of items of figuring out data, like a password and a further code. In lots of instances, the system sends the code to a person’s cellular system.
Voice authentication is a lesser-used know-how. Because the know-how improves, it ought to turn into a extra viable buyer identification instrument.
Enterprise finest practices
Organizations ought to adhere to the next business-related procedures to guard buyer knowledge:
Prepare workers. Organizations must constantly practice contact middle brokers to make sure they perceive how simply unhealthy actors can steal buyer knowledge. Worker coaching ought to concentrate on particular behaviors to guard buyer knowledge together with understanding the method to speak suspicious exercise. Coaching ought to embrace the next:
- Comply with good practices to maximise password power, like avoiding simply identifiable data.
- Shred paperwork with private data and do not depart written notes round. Get rid of the necessity for paper paperwork wherever doable.
- Restrict the knowledge despatched electronically to prospects, like private medical data.
- Do not open attachments or entry hyperlinks except they arrive from a dependable supply.
- Comply with facility bodily safety protocols whether or not working on-site or remotely.
Implement improved distant work practices. Distant workers create new safety gaps that may be addressed by the next measures:
- Require the usage of company-issued units.
- Develop necessities and monitor compliance for house community safety and knowledge entry.
- Do not enable third-party listening methods within the distant office.
Share duty for knowledge safety. Everybody, even people exterior of the contact middle, is accountable for buyer knowledge safety. Organizations can apply broad possession of buyer knowledge safety in some ways, together with the next:
- Monitor and report suspicious exercise.
- Limit unauthorized {hardware} or software program and entry to questionable web sites and paperwork.
- Deliver unattended delicate paperwork to management.
Use safety experience. Safety experience is crucial to remain forward of malicious actors. Organizations should deliver on employees or use consulting companies specializing in cybersecurity and different security-related issues.
Defending a company from safety breaches and managing delicate data is not a part-time job, and guaranteeing the right controls are in place — and maintaining a tally of the long run — requires devoted effort and experience.
Take a look at safety controls. Organizations should constantly check their applied sciences and processes to guard buyer knowledge. Enterprise leaders ought to by no means assume all the things will work as deliberate, particularly when coping with human behaviors and complicated unhealthy actors. Examples of testing safety controls embrace the next:
- Implement safety audits, together with safety log opinions if a breach happens.
- Scan for malware and different unauthorized software program often.
- Carry out workplace and residential workstation opinions to make sure brokers comply with safety finest practices.
- Embody the testing of safety controls and the restoration course of as a part of the general enterprise continuity planning.
Put together for a safety breach. Clients usually tend to really feel assured within the restoration course of if a company shortly controls a breach and has an motion plan to guard prospects. Safety breach preparation ought to be included in catastrophe restoration and enterprise continuity plans with particular actions outlining how and when to inform workers and prospects, and easy methods to help continued operations.
Enterprise executives and get in touch with middle leaders mustn’t get distracted by different initiatives. As safety threats turn into extra subtle, CX leaders ought to all the time prioritize contact middle safety.
Scott Sachs is president and founding father of SJS Options, a consultancy that makes a speciality of contact middle technique assessments and know-how choice.