The job of the safety operations heart skilled is not getting any simpler. SOC groups proceed to grapple with abilities gaps, an amazing inflow of safety alerts and daunting useful resource constraints. In the meantime, IT environments have grown more and more advanced, compounded by multi-cloud methods, extremely scalable deployments and evolving cybersecurity threats.
Many CISOs and IT decision-makers are confronting these challenges by embracing instruments that assist safety groups management and optimize incident responses utilizing superior detection and remediation. One such know-how is SOAR, or safety orchestration, automation and response, which contains a stack of applied sciences designed to automate and coordinate incident response, menace identification and routine operations.
Utilizing predefined automated workflows and playbooks to execute repetitive duties and validate safety configurations, SOAR can lighten the load for safety groups.
Extra incidents, extra complexity: The case for SOAR
The sophistication and quantity of safety incidents proceed to rise as enterprise environments change into extra advanced. Contemplate the present panorama: Multivector and AI-fueled cyberattacks are frequent, assault frequency has doubled in comparison with pre-pandemic ranges, and monetary losses are anticipated to rise from about $10.5 trillion in 2025 to over $12.2 trillion in 2031. Enterprise reliance on multi-cloud, hybrid cloud, edge and IoT deployments contributes to the complexity and will increase the assault floor. Increasing compliance necessities additionally complicate configurations and incident dealing with.
All this leaves CISOs and IT management questioning how safety workers can realistically deal with the escalating workload. With overworked SOC groups chasing false constructive alerts and missing the sources to deal with them, organizations will expertise response delays and inefficient mitigation processes, which may end in vulnerabilities or breaches.
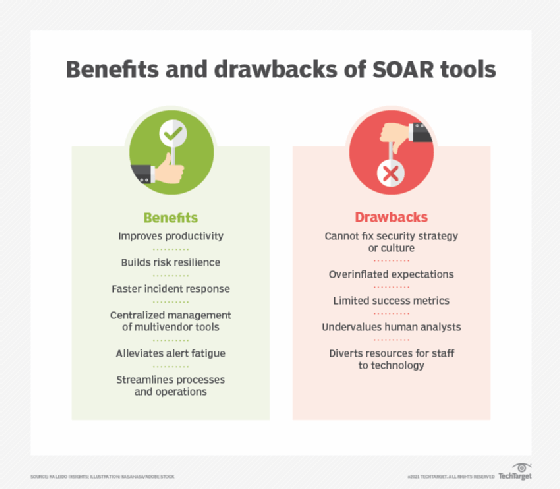
That is the place SOAR is available in. By automating and orchestrating incident response and centralizing incident administration, SOAR platforms assist groups tackle a number of IT safety challenges. For instance, when built-in into safety operations, SOAR can alleviate alert overload and fatigue, enhance alert prioritization, cut back human error and guarantee consistency. It thereby helps SOC groups decrease the affect of abilities gaps and workers shortages. Moreover, the studies generated by SOAR platforms present info to help human responders and velocity decision-making.
Core elements of SOAR
SOAR deployments sometimes include the next components:
- Occasion administration. Occasion ingestion, correlation and enrichment engine.
- Ecosystem alignment. Integration of SIEM, endpoint detection and response (EDR), firewalls, menace intelligence platforms and APIs for exterior safety instruments.
- Process growth. Automated incident response and remediation workflows and playbooks.
- Monitoring and reporting. Monitoring dashboards and reporting options that provide SOC groups a transparent, up-to-date view of present incidents and potential points.
What are SOAR workflows and playbooks?
SOAR workflows and playbooks are comparable however not the identical. Some distributors, nonetheless, use the phrases interchangeably.
SOAR workflows are automated sequences of steps executed by a SOAR platform to carry out a selected activity in an IT system. Playbooks are full units of incident response procedures that usually comprise a number of workflows.
Contemplate a phishing assault. A SOAR workflow would do the next:
- Obtain an alert about an e mail containing probably malicious content material from an e mail safety gateway or different associated device.
- Extract URLs and attachments from the suspicious e mail.
- Enrich the alert with menace intelligence knowledge.
- Assign menace indicators a threat degree.
- Ship an alert to the safety workforce.
A SOAR playbook containing a number of workflows would do the next:
- Analyze the e-mail (as outlined above).
- Set off a remediation — for instance, blocklist the IP tackle of the sender.
- Alert the person concerning the phishing try.
- Set off follow-up investigations and remediations — for instance, search different customers’ e mail inboxes and take away the malicious e mail.
- Ship an alert to the safety workforce.
- Create a report concerning the incident.
Playbooks cowl numerous situations, together with configuration safety, useful resource entry, configuration validation and vulnerability administration. Potential use instances vary from ransomware containment to insider menace investigations. CISOs should consider how properly every situation aligns with the group’s safety and regulatory compliance necessities.
The main points of SOAR workflows and playbooks will differ by incident, deployed SOAR instruments and the diploma of automation versus human oversight.
Tips on how to undertake SOAR
Adopting SOAR includes the next implementation phases:
- Assess the group’s present cybersecurity maturity degree, incident response processes and SOC workflows.
- Outline clear aims with measurable objectives.
- Establish the operational points the SOAR platform ought to remedy. Deal with high-volume, repetitive alerts primarily based on frequent incidents and threats.
- Assess the group’s present safety stack to establish wanted integrations.
- Choose a SOAR platform that matches the group’s wants and combine it into present techniques.
- Design SOAR workflows and playbooks.
- Check and refine automated workflows and playbooks primarily based on incident precedence with the purpose of decreasing the safety workers’s workload.
- Prepare analysts and different workforce members to make sure a constructive ROI.
- Deploy SOAR into manufacturing. Begin small and scale from there.
- Construct metrics and steady enchancment into the deployment. Monitor and optimize workflows and playbooks when threats evolve, processes change or each time wanted.
A profitable SOAR deployment can assist SOCs overcome restricted sources, abilities gaps, disparate applied sciences, advanced compliance necessities and alert fatigue. Placing SOAR close to the highest of the safety to-do checklist will strengthen the group’s safety posture and free groups to deal with what issues most — strategic menace evaluation, incident investigation, innovation and development.
Damon Garn owns Cogspinner Coaction and gives freelance IT writing and enhancing companies. He has written a number of CompTIA research guides, together with the Linux+, Cloud Necessities+ and Server+ guides, and contributes extensively to TechTarget Editorial, The New Stack and CompTIA Blogs.










