A gaggle of China-linked hackers often called Mustang Panda has expanded its spying efforts to focus on the Indian monetary sector and political circles in South Korea. The Acronis Risk Analysis Unit found the group’s newest exercise after its earlier marketing campaign involving Venezuela-related lures designed to focus on US authorities earlier in 2026.
Concentrating on HDFC Financial institution and Diplomacy Specialists
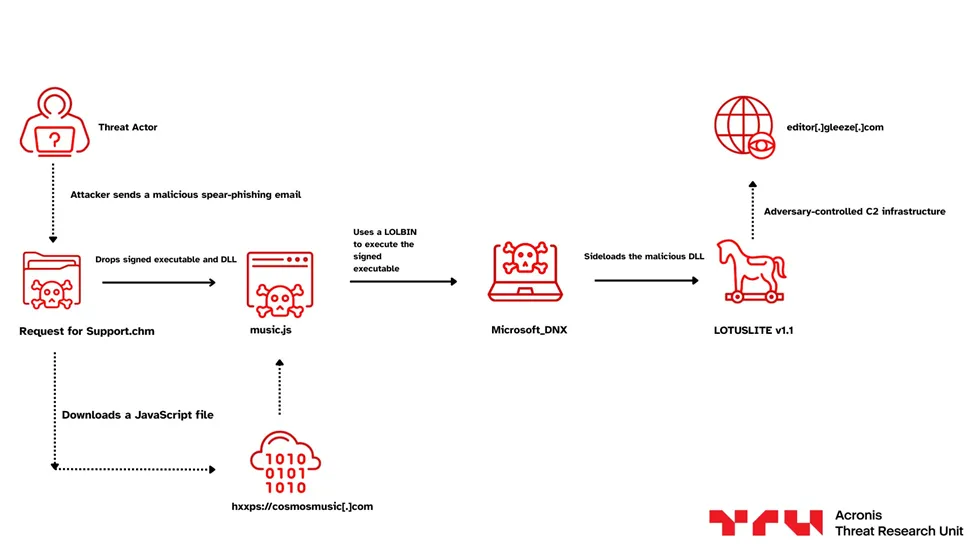
The hackers reportedly started this dual-sided marketing campaign in March 2026. In India, they used a file named Request for Help.chm to trick staff within the banking sector. This file contained a pop-up window that talked about HDFC Financial institution Restricted to look official, and when a consumer clicked the file, it triggered a series of occasions that concerned downloading a malicious JavaScript file referred to as music.js from the area cosmosmusiccom.
Acronis’ investigation, shared with Hackread.com, revealed that the hackers didn’t cease at assist tickets. They even made faux pop-up home windows that appeared like actual HDFC Financial institution software program. Whereas the employees thought they have been a banking app, a brand new model of the LOTUSLITE backdoor, referred to as LOTUSLITE v1.1, was truly spying on the system.
In one other a part of the marketing campaign, the group pretended to be Victor Cha, a former Director for Asian Affairs on the US Nationwide Safety Council. Utilizing a faux Gmail account ([email protected]) with Mr Cha’s actual photograph, they despatched out Google Drive hyperlinks to folders named March 30. Inside have been faux invitation letters crafted to contaminate the computer systems of policy-makers.
Similar Tips, New Names
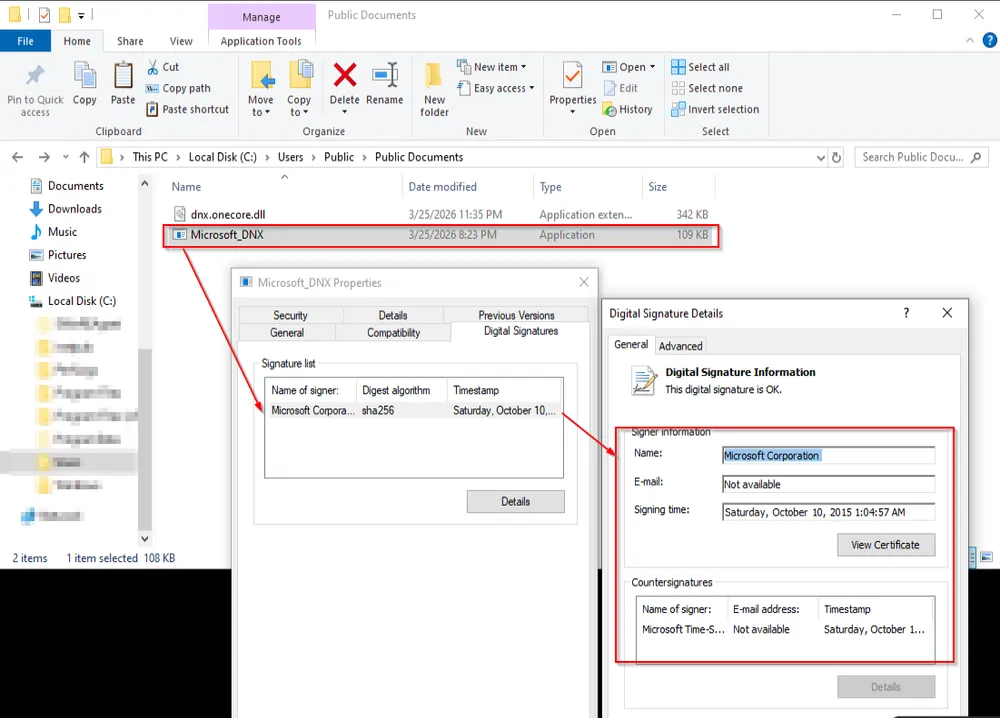
The hackers are utilizing a way referred to as DLL sideloading. They principally take a secure file signed by Microsoft (like Microsoft_DNX.exe) and put their very own malicious file proper subsequent to it. The pc trusts the Microsoft title, so it lets that contaminated file run with out a second thought.
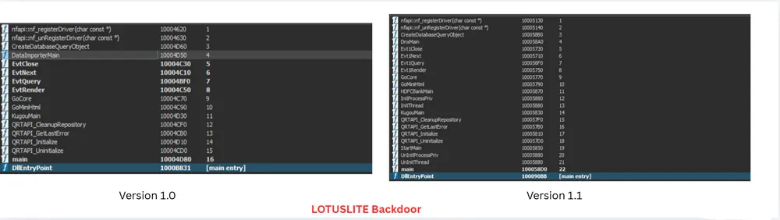
In accordance with researchers, the group is making an attempt to cover higher. They rotated the interior code marker or ‘magic worth,’ a selected code used to establish their site visitors, from 0x8899AABB to 0xB2EBCFDF, and likewise changed a command flag named –DATA with a brand new one referred to as –ZoneMAX.
Researchers additionally famous that the hackers used a service referred to as Gleeze to speak with their server at editorgleezecom. This is identical infrastructure utilized in earlier assaults, which helped specialists hyperlink the exercise to Mustang Panda.
Though the group tried to replace their strategies, they left behind previous code names like KugouMain and DataImporterMain within the new recordsdata. They even left a message within the code mentioning a safety researcher who has been monitoring them.
Nonetheless, they’re consistently upgrading their impersonating experience and utilizing trusted software program to lure customers, which makes it important for everybody to remain sceptical of any sudden emails or recordsdata, even when they give the impression of being official.