Community safety agency Infoblox has disclosed particulars on a long-running fraud operation that has been quietly draining financial institution accounts since not less than June 2020. This rip-off makes use of faux CAPTCHA pages to hold out a selected sort of cybercrime often known as Worldwide Income Share Fraud, or IRSF.
Whereas most individuals see CAPTCHA as a boring however crucial solution to show they’re human, the scammers behind this marketing campaign have transformed this course of right into a profit-making device by tricking customers into sending high-cost worldwide textual content messages.
The Assault Chain
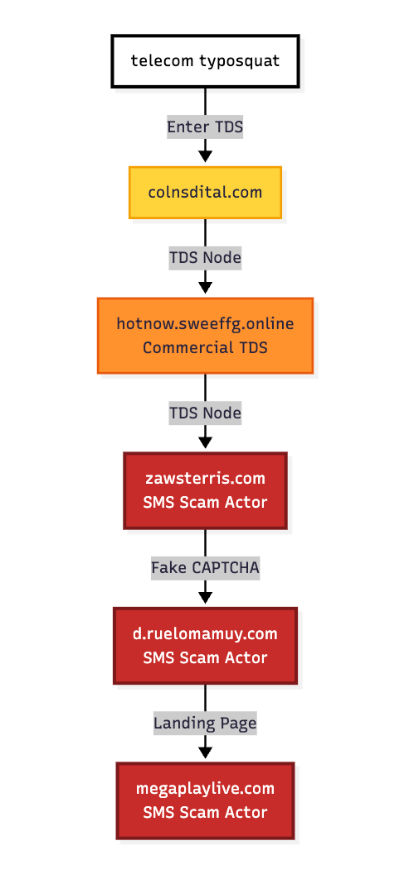
In keeping with cybersecurity researchers at Infoblox Menace Intelligence, the assault begins when an individual unintentionally visits a typosquatted area. These are lookalike addresses designed to imitate well-known telecommunications manufacturers. When the person lands on the mistaken web page, they’re compelled in the direction of a fancy Site visitors Distribution System (TDS).
In a latest statement from March 2026, researchers tracked this path because it moved by way of a number of nodes, together with a business promoting community in Germany, earlier than reaching a touchdown web page managed by the scammers, corresponding to zawsterriscom.
Technical Strategies of Deception
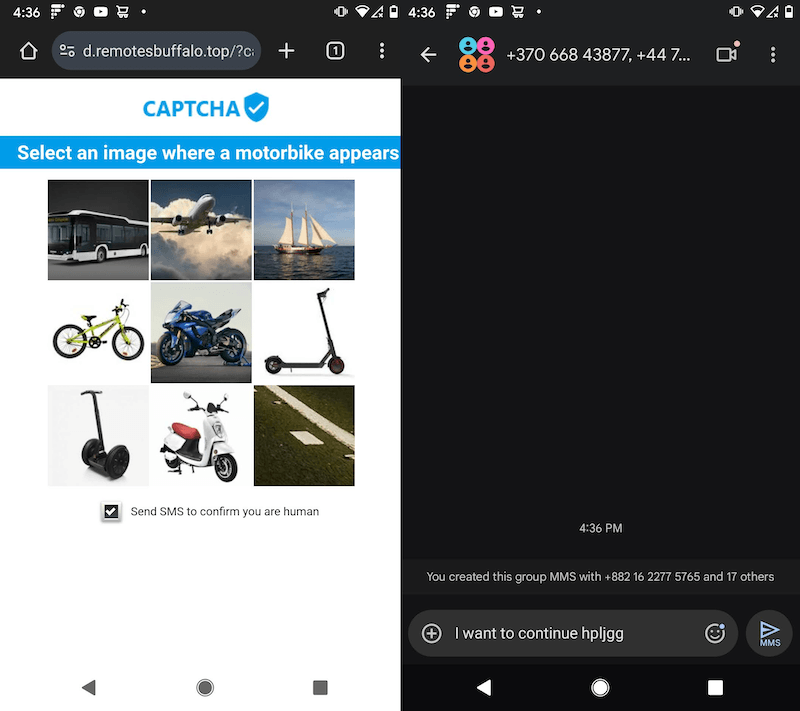
When the sufferer visits the faux CAPTCHA, they’re requested easy questions on their gadget sort (iOS or Android) or community pace (4G or WiFi), which is in contrast to how CAPTCHA checks really work. And, that’s the place the trick lies; each time the sufferer clicks a solution, a JavaScript operate referred to as makeTrackerDownload.php is triggered, which forces their cellphone to open its SMS app with a pre-filled message and an extended record of worldwide cellphone numbers.
By the point the four-step verification is full, the sufferer could have despatched 60 messages to over 50 completely different locations. These messages are routed to 35 cellphone numbers throughout 17 completely different nations with excessive termination charges, like Azerbaijan, Kazakhstan, and Myanmar.
Trapping the Sufferer
To make sure the sufferer doesn’t depart earlier than the job is completed, the risk actors use a method referred to as again button hijacking, which Google not too long ago banned. Through the use of a selected coding technique to govern the browser historical past, the hackers entice the person in a loop. If the particular person tries to click on again to a protected web site, the script merely refreshes the rip-off web page.
This persistent interplay permits the scammers to maximise their income throughout a number of carriers. Researchers famous that the fees, which might complete $30 or extra per session, typically don’t seem on a cellphone invoice for weeks, and the sufferer has likely forgotten the web site by the point they see the monetary injury.
Attribution
Infoblox researchers have attributed this exercise to an affiliate of a European Click2SMS community, which makes use of infrastructure hosted on AS15699, also called Adam Ecotech. Additional investigation discovered that the identical methods used to unfold malware and scareware are actually getting used to industrialise cellphone fraud.
Nonetheless, be careful for such scams, as a reputable safety test won’t ever require you to ship a textual content message to show your id.
(Photograph by kuu akura on Unsplash)