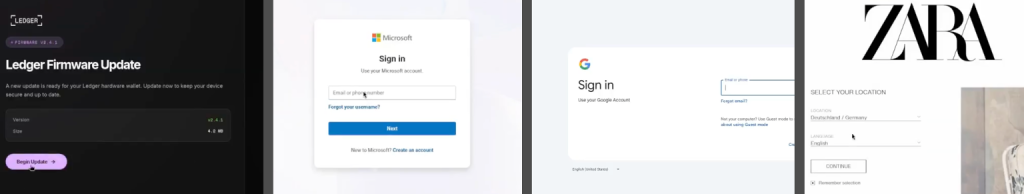
Varonis Risk Labs has found a brand new phishing-as-a-service equipment referred to as Bluekit that’s making it a lot simpler for cyberattackers to bypass safety, even when customers have further protections turned on. This equipment is mainly like a one-stop store for hackers, providing over 40 pretend web site templates that mimic huge names like iCloud, Apple ID, Gmail, Outlook, Hotmail, Yahoo, ProtonMail, GitHub, Twitter, Zoho, Zara, and Ledger.
Previously, a hacker needed to change between totally different providers to arrange a rip-off. Bluekit adjustments all that by providing every thing on a single dashboard the place menace actors can purchase domains, arrange pretend login pages, and monitor their victims in real-time.
Bypassing the MFA
Probably the most harmful a part of Bluekit is that it handles safety codes utilizing a way referred to as Adversary-in-the-Center (AiTM). In response to Varonis’ specialists, when a sufferer enters their particulars on a pretend Bluekit web page, the equipment doesn’t simply seize the password; it additionally steals session cookies and native storage information. It is a big drawback as a result of it facilitates an MFA (multi-factor authentication) bypass.
These stolen cookies act like authenticated session tokens, which show to a server {that a} person has already accomplished the login and id verification course of. By replaying these tokens, hackers can achieve unauthorised entry to an account with out ever needing to work together with the sufferer’s multi-factor authentication immediate. The equipment even retains a dwell view of the goal’s browser and sends all stolen information on to the hacker through Telegram.
“Operators can purchase or join domains from the identical interface used to handle phishing pages and captured logs, fairly than splitting that work throughout separate providers. That setup circulation additionally extends into web site creation itself. Within the view we reviewed, operators may choose a site, select a mode, and choose from a broad checklist of goal manufacturers and providers, together with client e mail suppliers and developer-facing platforms,” researchers defined.
AI With out the Guardrails
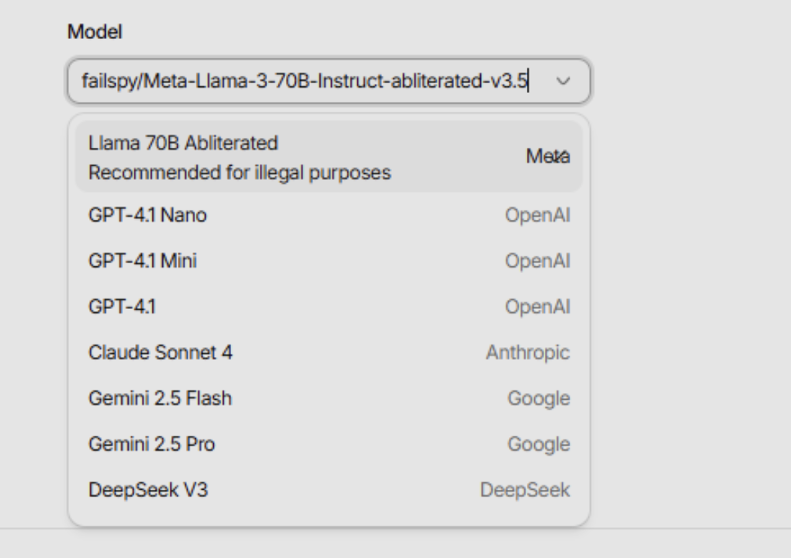
Researchers famous that Bluekit additionally comes with its personal AI assistant referred to as Abliterated Llama, though it lists well-known fashions like GPT-4. On your info, abiliterated is a selected sort of AI with security filters stripped away, so whereas the precise Llama gained’t comply, the abliterated model gained’t refuse to assist with a cyberattack.
Varonis menace researcher Daniel Kelley identified within the weblog put up shared with Hackread.com that whereas hackers used to attempt to jailbreak normal AI to assist them, Bluekit reveals a shift “towards open-weight fashions with out security guardrails, which is extra constant than working round prompt-level filters.”
Proper now, the AI assistant principally builds the marketing campaign framework, usually leaving placeholders for the hacker to fill in later. Nevertheless, the developer is transferring quick. New options like voice cloning, geolocation emulation, and antibot cloaking are being added continually. With the equipment evolving this shortly, researchers count on to see Bluekit showing in lots of extra cyberattacks quickly.