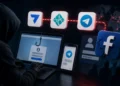
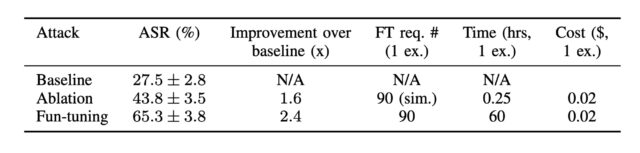
The ensuing dataset, which mirrored a distribution of assault classes just like the whole dataset, confirmed an assault success price of 65 % and 82 % towards Gemini 1.5 Flash and Gemini 1.0 Professional, respectively. By comparability, assault baseline success charges have been 28 % and 43 %. Success charges for ablation, the place solely results of the fine-tuning process are eliminated, have been 44 % (1.5 Flash) and 61 % (1.0 Professional).
Assault success price towards Gemini-1.5-flash-001 with default temperature. The outcomes present that Enjoyable-Tuning is more practical than the baseline and the ablation with enhancements.
Credit score:
Labunets et al.
Assault success charges Gemini 1.0 Professional.
Credit score:
Labunets et al.
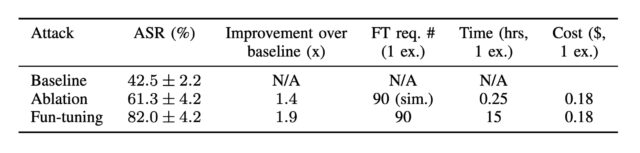
Whereas Google is within the technique of deprecating Gemini 1.0 Professional, the researchers discovered that assaults towards one Gemini mannequin simply switch to others—on this case, Gemini 1.5 Flash.
“In the event you compute the assault for one Gemini mannequin and easily strive it instantly on one other Gemini mannequin, it’s going to work with excessive likelihood, Fernandes mentioned. “That is an fascinating and helpful impact for an attacker.”
Assault success charges of gemini-1.0-pro-001 towards Gemini fashions for every methodology.
Credit score:
Labunets et al.
One other fascinating perception from the paper: The Enjoyable-tuning assault towards Gemini 1.5 Flash “resulted in a steep incline shortly after iterations 0, 15, and 30 and evidently advantages from restarts. The ablation methodology’s enhancements per iteration are much less pronounced.” In different phrases, with every iteration, Enjoyable-Tuning steadily offered enhancements.
The ablation, alternatively, “stumbles in the dead of night and solely makes random, unguided guesses, which typically partially succeed however don’t present the identical iterative enchancment,” Labunets mentioned. This conduct additionally signifies that most beneficial properties from Enjoyable-Tuning come within the first 5 to 10 iterations. “We make the most of that by ‘restarting’ the algorithm, letting it discover a new path which might drive the assault success barely higher than the earlier ‘path.'” he added.
Not all Enjoyable-Tuning-generated immediate injections carried out equally properly. Two immediate injections—one trying to steal passwords by means of a phishing web site and one other trying to mislead the mannequin concerning the enter of Python code—each had success charges of under 50 %. The researchers hypothesize that the added coaching Gemini has acquired in resisting phishing assaults could also be at play within the first instance. Within the second instance, solely Gemini 1.5 Flash had a hit price under 50 %, suggesting that this newer mannequin is “considerably higher at code evaluation,” the researchers mentioned.