Examine Level Analysis reveals that China-linked hackers, together with the Camaro Dragon group, are focusing on Qatar with malware disguised as Center East battle information. Utilizing instruments like PlugX and Cobalt Strike, these attackers are turning their focus towards the Gulf’s power trade and navy targets amid rising regional tensions.
Latest shifts in Center Jap politics have triggered a sudden wave of on-line interference. Teams linked to China have launched cyberattacks directed at Qatar, timed to coincide with a significant spike in regional battle. These actors started their operations on 1 March 2026, simply in the future after the launch of Operation Epic Fury. It reveals simply how rapidly these teams can flip breaking information right into a weapon to trick their targets.
Misleading Ways and Pretend Information Lures
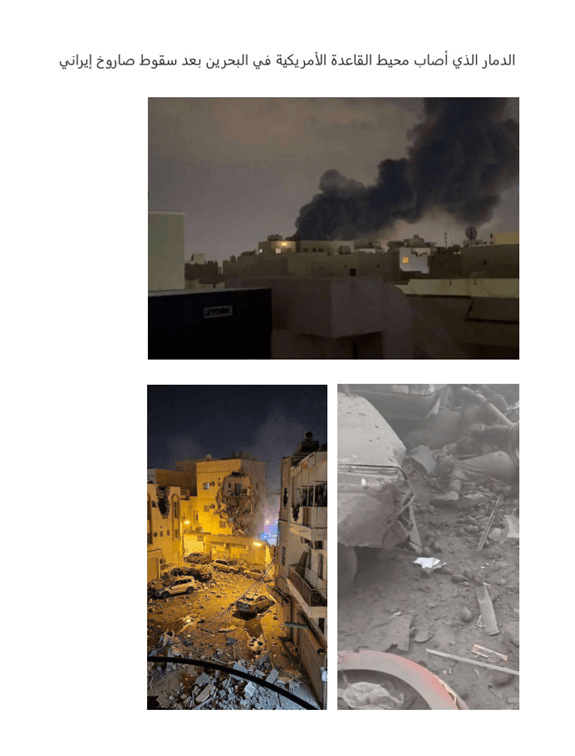
In response to Examine Level Analysis, which detected and reported this spike, these hackers are utilizing the chaos of the battle to make their lures extra plausible. In a single occasion, they despatched out a file disguised as images titled “The destruction brought on by an Iranian missile strike across the US base in Bahrain.” Individuals, as we all know it, usually tend to click on on pressing information throughout a disaster, and the attackers took full benefit of this.
Additional investigation by CPR researchers revealed a surprisingly lengthy an infection chain as soon as a sufferer opens the file. The method begins by contacting a hacked server to drag down extra information. It then makes use of a trick referred to as DLL hijacking, the place the malware hides inside a professional program, on this case, the favored Baidu NetDisk app, to secretly run the PlugX backdoor.
The malware permits hackers to steal information, report what you kind, and even take photos of your display. It’s price noting that this particular group, generally known as Camaro Dragon, used a decryption key labelled 20260301@@@, and the identical methodology was used months earlier, in late December, to focus on the Turkish navy, researchers famous, suggesting the group merely moved its focus to Qatar when the chance arose.
Power Sector Targets and the NVDA Trick
The marketing campaign didn’t cease at navy lures; attackers additionally focused Qatar’s important oil and fuel industries utilizing a password-protected file named “Strike at Gulf oil and fuel services.zip.” This assault used low-quality, AI-generated content material pretending to be from the Israeli authorities to ship a brand-new loader program written within the Rust language.
This particular assault was fairly intelligent as a result of it hid its malicious code inside a element of NVDA, a professional open-source display reader for the blind. By hijacking a trusted software, the hackers make it a lot tougher for safety software program to identify them. The ultimate purpose was to plant Cobalt Strike, a software usually utilized by safety professionals for simulating assaults, however within the flawed fingers, permits hackers to map out a community for a full-scale intrusion.
In response to researchers, these intrusions “spotlight how quickly China-nexus espionage actors can pivot” in response to international occasions. By mixing into the fast-moving communications of a disaster, these hackers hope to stay unnoticed whereas gathering intelligence on one of many area’s most influential states.
Chinese language-linked hackers will not be the one actors lively amid the continuing battle. Though the scenario largely impacts Iran, Iranian-linked hackers from MuddyWater had been lately noticed focusing on U.S. and Israeli organizations with a brand new malware pressure dubbed DinDoor by researchers.











