Right here’s how open-source intelligence helps hint your digital footprint and uncover your weak factors, plus a number of important instruments to attach the dots
20 Nov 2025
•
,
5 min. learn

Regardless of the cause, we spend huge quantities of time on-line, tapping into the untold expanse of data, communication and assets. Typically, the problem isn’t discovering some information, however figuring out what’s related, actual and price trusting. Anybody working with data wants to have the ability to lower by the noise and discern the authenticity of the information, which requires being methodical and deliberate when selecting and utilizing our sources – and having the fitting instruments to expedite the method.
And that is the place OSINT is available in. Brief for “Open Supply Intelligence”, OSINT refers back to the gathering and evaluation of publicly obtainable information to supply actionable insights. Journalists can use it for investigations and fact-checking. Companies can depend on it for monitoring their repute or monitor opponents. Researchers can leverage it for his or her research. Principally, for those who’re making an attempt to make sense of public information, you’re already in OSINT territory. For sure, OSINT has use instances in cybersecurity, too.
OSINT in cybersecurity
What began as a apply for army and regulation enforcement functions has turn out to be an vital self-discipline in cybersecurity, enabling safety practitioners to gauge dangers, spot uncovered belongings and perceive potential threats. The advantages are apparent: OSINT offers organizations a clearer image of their digital footprint and helps them spot their weak spots earlier than they are often exploited for unhealthy ends.
For instance, pentesters can use it throughout reconnaissance to find uncovered domains or providers. Menace intelligence groups can depend on it to comply with malicious exercise on social media or underground boards. Meanwhiie, pink and blue groups can each use OSINT to check how seen their infrastructure is from the surface. It additionally permits safety professionals to enhance their understanding of unhealthy actors by recognizing their techniques and watching their chatter.
After all, the identical strategies work each methods. Each piece of details about a company that’s publicly accessible is equally obtainable to adversaries, who can leverage OSINT for spearphishing assaults, amongst different issues, as figuring out a goal’s habits or coworkers makes the bait extra convincing.
Instruments and strategies
OSINT practitioners can use a plethora of open-source and proprietary instruments that automate information assortment and evaluation. Among the commonest ones are:
- Shodan and Censys: these are staples amongst serps for internet-connected gadgets, corresponding to routers and IP cameras. They provide help to see what’s publicly uncovered and shouldn’t be, corresponding to open ports, uncovered APIs and insecure certificates, which helps determine uncovered methods in a company’s community.
- Maltego: a visible mapping software to hyperlink folks, domains, and IPs to disclose hidden connections.
- TheHarvester, Recon-ng, SpiderFoot: units of scripts that acquire e-mail addresses, subdomains, hosts, usernames, and so on., from a number of sources (corresponding to WHOIS, serps, social media websites and public databases). They turn out to be useful within the reconnaissance section of penetration testing assaults.
- OSINT Framework and OSINTCombine: these instruments manage lots of of free assets by class (internet search, social media platforms, authorities websites, and so on.), making it simple for each newcomers and seasoned analysts to search out the fitting software for every activity.
- Google Dorks and GooFuzz: superior search strategies (utilizing operators like website: or filetype:) that assist uncover delicate information listed by serps.
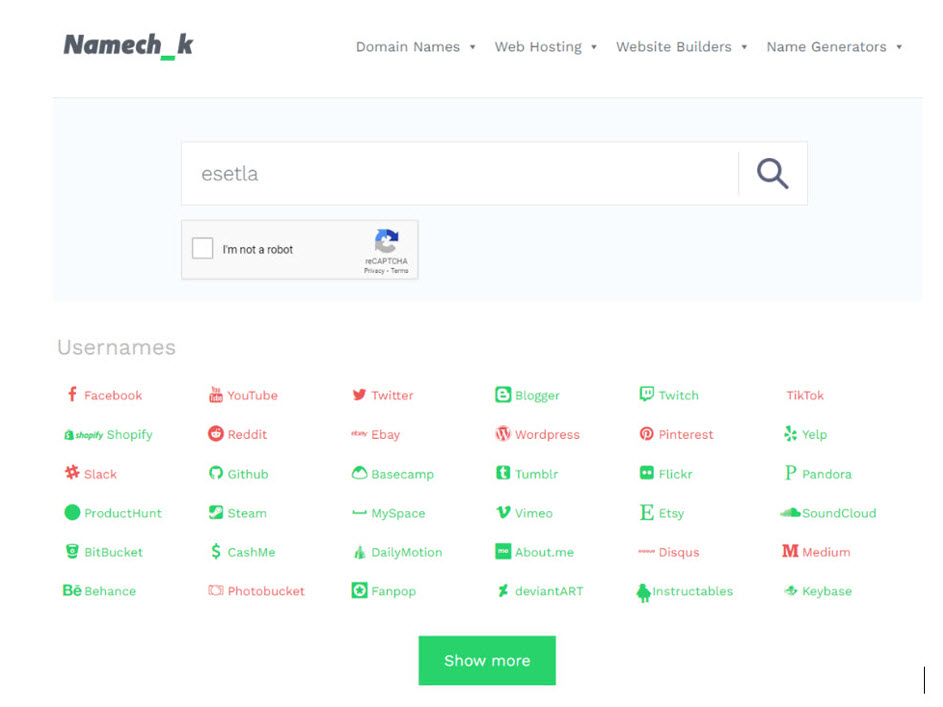
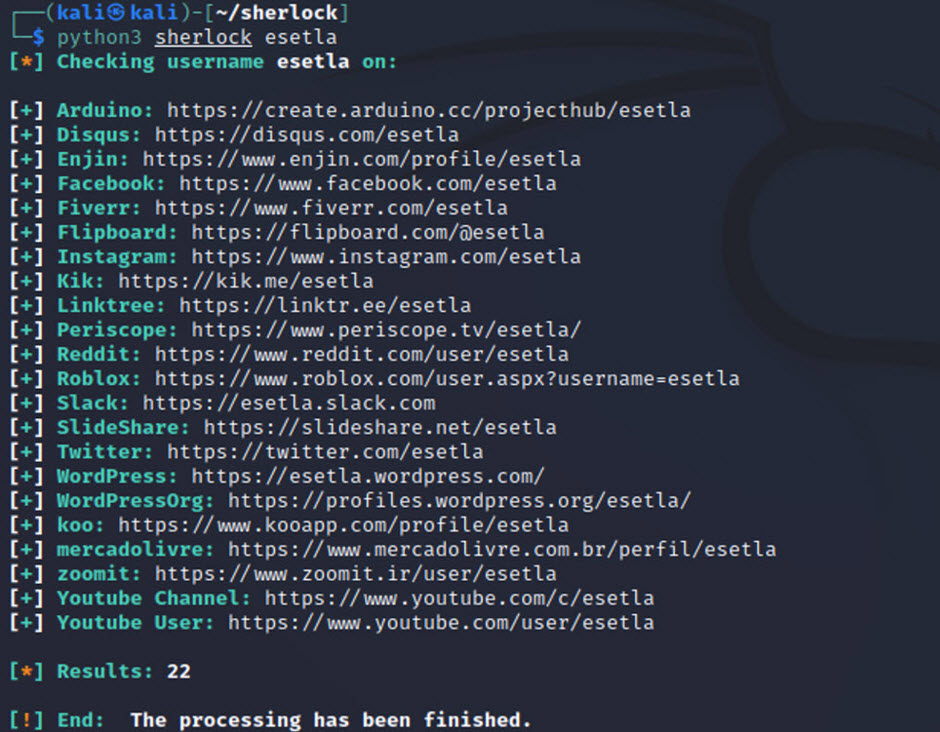
- Social media instruments: platforms like Namechk and Sherlock test whether or not a username exists throughout dozens of websites and are, subsequently, helpful for constructing digital profiles. Extra superior instruments corresponding to Skopenow, Telegago, or AccountAnalysis analyze habits and connections on platforms like X, Fb, or Telegram.
- Metadata evaluation: instruments corresponding to ExifTool, FOCA, and Metagoofil extract geolocation, writer names, timestamps and different information contained in pictures and paperwork.
- Menace monitoring: automated tasks can mix OSINT with real-time alerts. For instance, FBI Watchdog warns of legally seized domains and DNS modifications in actual time. There are additionally varied instruments that observe legal boards for early indicators of ransomware campaigns.
Getting began with OSINT
Should you’re ranging from scratch, follow the standard intelligence cycle:
- Outline your objectives; in different phrases, be clear about what you’re investigating and what questions you’re in search of to reply.
- Determine related sources, corresponding to social media, web sites, authorities databases, or public information.
- Gather and analyze information with the assistance of choose OSINT instruments.
- Doc what you discover, and assess how dependable every nugget of data is. Make certain to supply and rigorously doc your findings so that you just scale back errors and guarantee your evaluation is credible.
Really helpful starter instruments
Should you’re simply beginning out, listed here are a number of free instruments with strong documentation:
- Discover the OSINT Framework to search out categorized assets.
- Experiment with TheHarvester, SpiderFoot, and Recon-ng to know automated information gathering.
- Study primary Google Dorking and how one can work with Shodan.
- Attempt Maltego, which integrates a number of APIs into one interface, to visualize relationships and datasets.
Mock case examine
Let’s say an organization suspects a knowledge breach. An OSINT analyst may take these steps:
- They test breach databases corresponding to Have I Been Pwned to see if firm emails seem in recognized leaks.
- In addition they use Google Dorks to seek for publicly uncovered paperwork (e.g., “filetype:xls CEO e-mail”)
- They scan for unprotected servers utilizing Shodan or Censys.
- Utilizing Maltego or social media intelligence (SocMINT) instruments, they map worker social profiles instruments to determine unintended publicity of confidential information.
- In the end, they uncover {that a} server listed by Google was utilizing weak credentials. The crew updates configurations and notifies customers, stopping a probably severe breach.
Parting ideas
Figuring out how one can use OSINT instruments is one factor; figuring out how one can examine responsibly is one other. Study when to create sock puppet accounts for investigations, when to make use of scraping to deal with giant datasets, and when it’s acceptable to discover the darkish internet. Simply bear in mind by no means to lose sight of privateness legal guidelines and the ethics behind the search – they’re a part of the craft.
We’re nearly about to enter 2026, and open-source intelligence is extra related than ever. it’s a part of how cybersecurity, journalism, and analysis all function. The explosion of obtainable information, coupled with smarter automation and synthetic intelligence, implies that nearly anybody can extract significant intelligence from open sources. Carried out proper, OSINT turns the noise of the web world into actionable insights.











