Cybercriminals are abusing a widespread lack of authentication within the customer support platform Zendesk to flood focused e-mail inboxes with menacing messages that come from lots of of Zendesk company clients concurrently.
Zendesk is an automatic assist desk service designed to make it easy for folks to contact corporations for buyer help points. Earlier this week, KrebsOnSecurity began receiving hundreds of ticket creation notification messages by way of Zendesk in speedy succession, every bearing the identify of various Zendesk clients, corresponding to CapCom, CompTIA, Discord, GMAC, NordVPN, The Washington Publish, and Tinder.
The abusive missives despatched by way of Zendesk’s platform can embrace any topic line chosen by the abusers. In my case, the messages variously warned a couple of supposed regulation enforcement investigation involving KrebsOnSecurity.com, or else contained private insults.
Furthermore, the automated messages which are despatched out from this kind of abuse all come from buyer domains — not from Zendesk. Within the instance under, replying to any of the junk buyer help responses from The Washington Publish’s Zendesk set up exhibits the reply-to handle is assist@washpost.com.
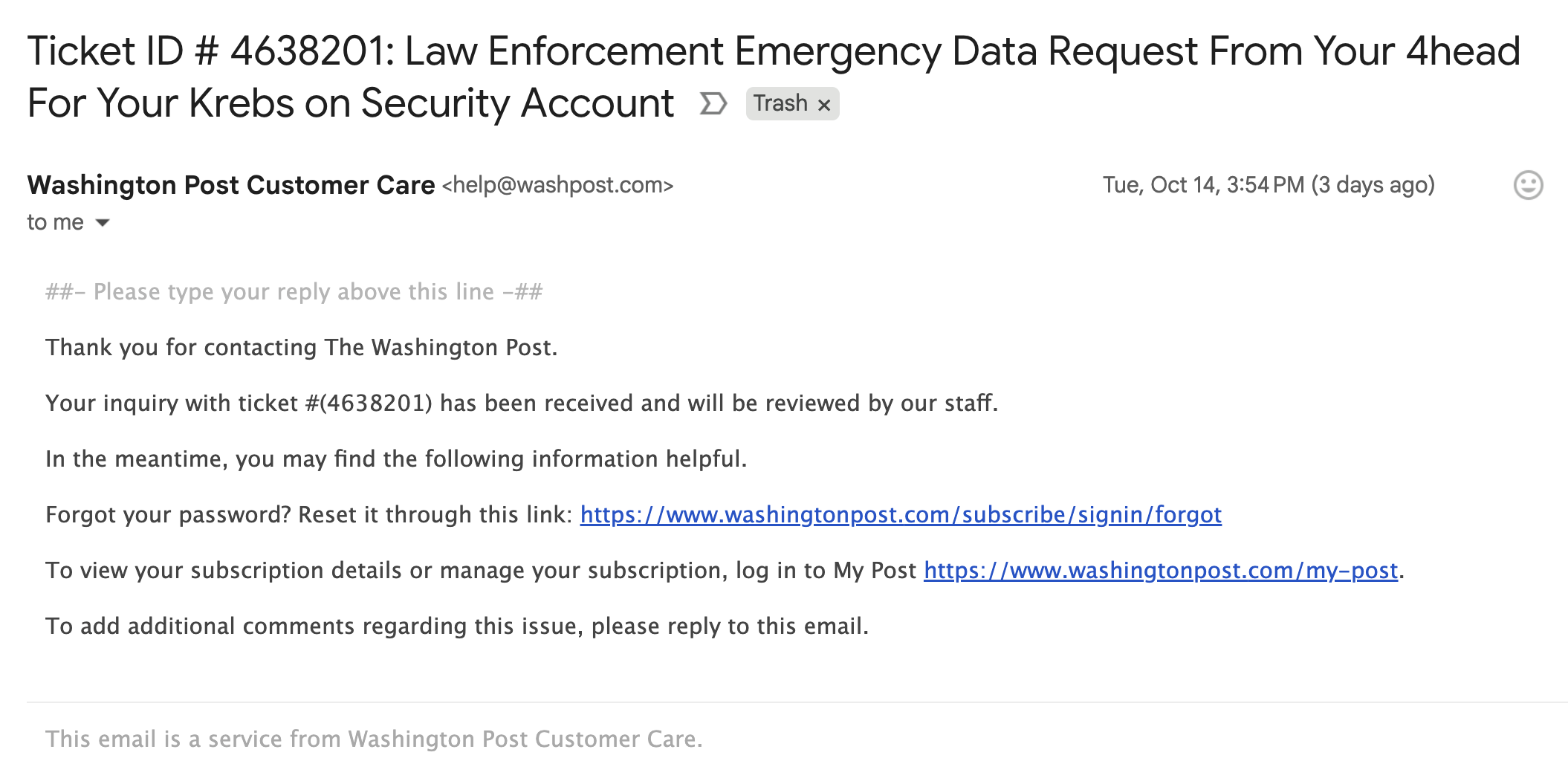
One among dozens of messages despatched to me this week by The Washington Publish.
Notified concerning the mass abuse of their platform, Zendesk stated the emails have been ticket creation notifications from buyer accounts that configured their Zendesk occasion to permit anybody to submit help requests — together with nameless customers.
“These kind of help tickets could be a part of a buyer’s workflow, the place a previous verification just isn’t required to permit them to interact and make use of the Help capabilities,” stated Carolyn Camoens, communications director at Zendesk. “Though we suggest our clients to allow solely verified customers to submit tickets, some Zendesk clients desire to make use of an nameless setting to permit for tickets to be created because of numerous enterprise causes.”
Camoens stated requests that may be submitted in an nameless method may make use of an e-mail handle of the submitter’s alternative.
“Nonetheless, this technique can be used for spam requests to be created on behalf of third celebration e-mail addresses,” Camoens stated. “If an account has enabled the auto-responder set off based mostly on ticket creation, then this permits for the ticket notification e-mail to be despatched from our buyer’s accounts to those third events. The notification can even embrace the Topic added by the creator of those tickets.”
Zendesk claims it makes use of fee limits to forestall a excessive quantity of requests from being created directly, however these limits didn’t cease Zendesk clients from flooding my inbox with hundreds of messages in only a few hours.
“We acknowledge that our methods have been leveraged in opposition to you in a distributed, many-against-one method,” Camoens stated. “We’re actively investigating further preventive measures. We’re additionally advising clients experiencing this kind of exercise to comply with our common safety greatest practices and configure an authenticated ticket creation workflow.”
In the entire instances above, the messaging abuse wouldn’t have been doable if Zendesk clients validated help request e-mail addresses previous to sending responses. Failing to take action might make it simpler for Zendesk shoppers to deal with buyer help requests, nevertheless it additionally permits ne’er-do-wells to sully the sender’s model in service of disruptive and malicious e-mail floods.










