The favored textual content editor EmEditor fell sufferer to a classy provide chain assault between December 19-22, 2025, during which attackers compromised the official web site to distribute malware-laced set up packages.
Emurasoft, Inc., the software program’s developer, confirmed on December 23 that malicious MSI installers had been served to customers by way of tampered obtain hyperlinks, bearing fraudulent digital signatures from “WALSHAM INVESTMENTS LIMITED” as a substitute of the professional writer credentials.
Qianxin Menace Intelligence Heart’s RedDrip Staff recognized the incident by way of its intelligence monitoring methods, capturing the whole malicious payload chain.
Given EmEditor’s substantial consumer base amongst Chinese language builders, operations personnel, and technical professionals dealing with delicate knowledge, safety researchers assess that the assault poses important dangers to authorities and enterprise establishments throughout the area.
Refined Multi-Stage Assault Chain
The compromised MSI installer (emed64_25.4.3.msi) contained embedded malicious scripts designed to execute PowerShell instructions that flip off system logging and deploy C# courses for knowledge exfiltration.
The malware systematically collected system info together with OS model and usernames, encrypting stolen knowledge with RSA encryption earlier than transmitting it to the command-and-control server at emeditorgb.com.
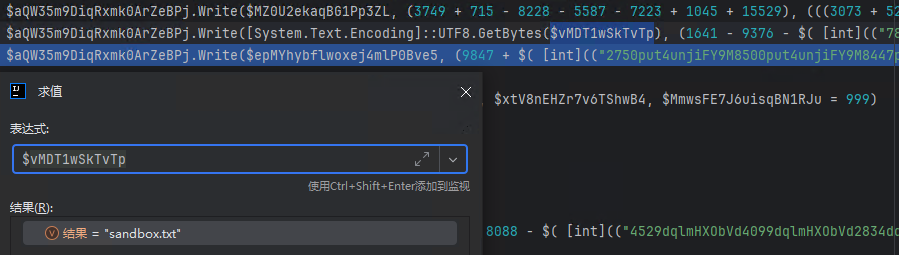
The infostealer focused a number of high-value directories together with Desktop, Paperwork, and Downloads, harvesting file lists and packaging them into encrypted archives named “sandbox.txt” and “system.txt.”
The malware demonstrated superior credential theft capabilities, extracting VPN configurations, Home windows login credentials, and browser knowledge encompassing cookies, saved passwords, and consumer preferences from fashionable functions.
Among the many focused software program had been enterprise collaboration platforms together with Zoho Mail, Evernote, Notion, Discord, Slack, Mattermost, Microsoft Groups, and Zoom, alongside safe file switch instruments like WinSCP and PuTTY.
The malware additionally captured screenshots and compressed all stolen knowledge right into a file named “array.bin” for exfiltration. Notably, the malware included geographic restrictions, terminating execution if it detected system languages related to former Soviet international locations or Iran.
The assault’s most regarding part concerned putting in a persistent browser extension masquerading as “Google Drive Caching.”
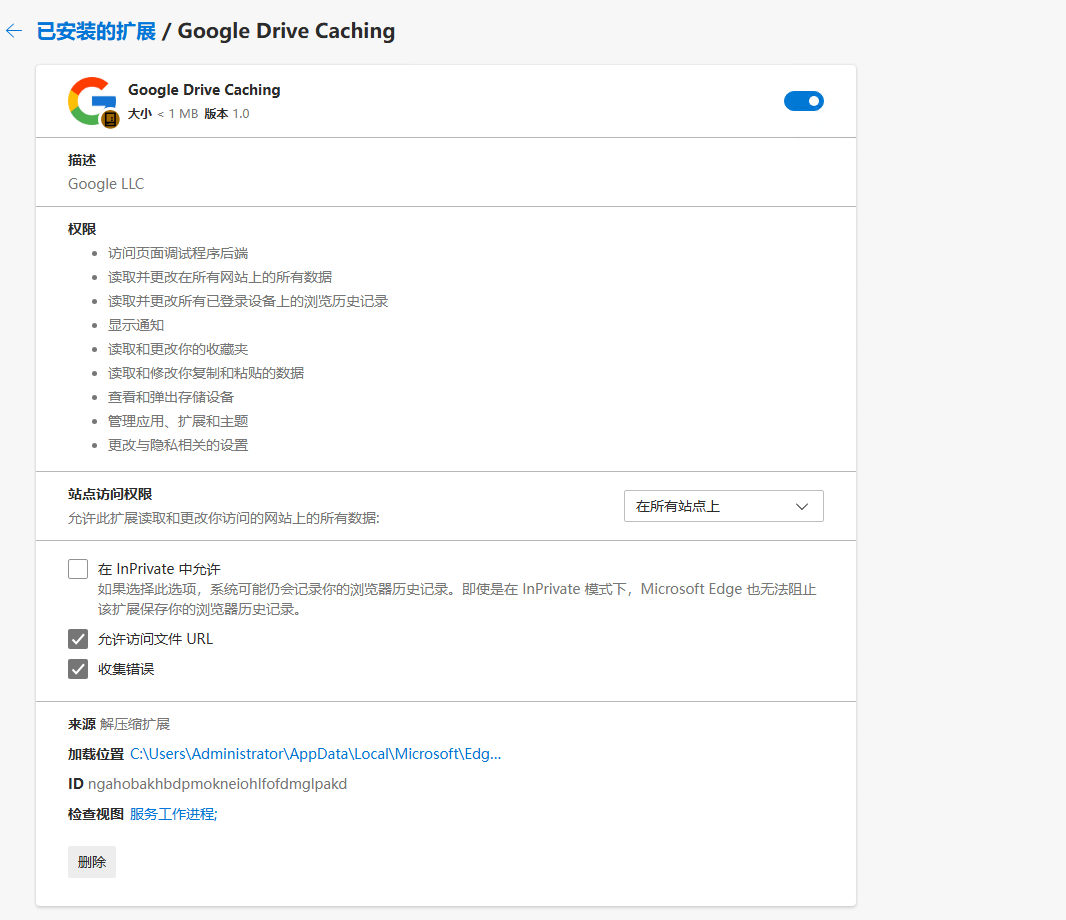
This fully-featured infostealer communicated with cachingdrive.com and included Area Era Algorithm (DGA) logic to keep up operations even when main infrastructure confronted takedown efforts. The DGA generates weekly fallback domains utilizing seed values mixed with 12 months and week quantity calculations.
The extension harvested complete system metadata together with CPU, GPU, reminiscence specs, display screen decision, and time zone knowledge.
It captured full browser historical past, cookies, put in extensions, and bookmarks whereas implementing clipboard hijacking performance supporting over 30 cryptocurrency pockets deal with codecs.
Further capabilities included keylogging categorized by particular net pages, Fb promoting account theft, and distant management capabilities enabling operators to execute screenshots, learn native information, set up proxy connections, and run arbitrary JavaScript code.
Detection and Mitigation
Qianxin’s Tianqing “Liuhe” engine detects and blocks the malicious MSI installers. The corporate recommends authorities and enterprise clients deploy this safety engine to defend towards the menace.
Emurasoft confirmed that customers who up to date by way of EmEditor’s built-in Replace Checker, downloaded from obtain.emeditor.data straight, or used moveable/retailer variations stay unaffected.
The professional installer bears Emurasoft, Inc.’s digital signature with SHA-256 hash e5f9c1e9b586b59712cefa834b67f829ccbed183c6855040e6d42f0c0c3fcb3e, whereas the malicious model shows an 80,380,416-byte file measurement signed by WALSHAM INVESTMENTS LIMITED.
Organizations ought to instantly isolate doubtlessly affected methods, conduct complete malware scans, and implement password resets with multi-factor authentication enablement for uncovered credentials.
Comply with us on Google Information, LinkedIn, and X to Get Prompt Updates and Set GBH as a Most popular Supply in Google.










