The FBI efficiently recovered personal Sign messages from a defendant’s iPhone even after the app was deleted. Find out how this safety loophole works and the easy setting you need to change at present to maintain your chats personal.
Most of us desire utilizing the Sign app as a result of it’s purported to be very safe with a exceptional end-to-end encryption system that hides our chats from everybody else. It additionally has a message-disappearing function to assist us set a message deletion time.
However the Federal Bureau of Investigation (FBI) discovered a technique to learn personal Sign messages on an iPhone, even after the app was deleted. This was revealed in a court docket case in Texas that these messages can keep hidden within the telephone’s reminiscence longer than we anticipated.
How the loophole works
The case includes a girl named Lynette Sharp and an assault on a Texas detention centre in July 2025. In the course of the trial in April 2026, the FBI revealed they recovered her messages even when she had deleted the Sign app. The bureau, reportedly, retrieved the messages from the iPhone’s push notification database.
In the course of the trial, FBI Particular Agent Clark Wiethorn defined how investigators accessed the proof. When a message arrives, the telephone exhibits slightly preview on the display screen, which is dealt with by the telephone’s working system and never the Sign app.
Even when Sign deletes the message later, the telephone’s system can save a duplicate of that preview in its personal information. To learn these saved messages from Sign, the FBI used Cellebrite, a forensic instrument usually utilized by regulation enforcement to scan seized units.
A key discovering is that the FBI might solely see incoming messages, not those Sharp despatched, which confirms the info got here from the notification storage. It exhibits that whereas the app’s encryption is powerful, the telephone’s working system retains its personal logs of every little thing.
Are different messaging apps protected?
You will need to be aware that this isn’t only a drawback for Sign, and might occur with any messaging app that exhibits previews, together with WhatsApp or Telegram. Telegram’s founder, Pavel Durov, has overtly criticised WhatsApp’s encryption in his current publish on X, calling it an enormous shopper fraud.
He pointed to a lawsuit claiming {that a} secret backdoor exists that may enable WhatsApp and Meta, in addition to different teams, to bypass the encryption and see personal messages.
Learn how to defend your messages
You may cease your telephone from storing message previews by altering each your iPhone and app settings.
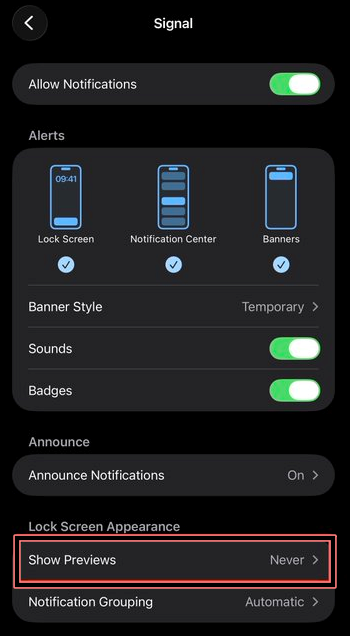
In your iPhone, go to notification settings for Sign and set Present Previews to By no means. Then open the Sign app, go to Settings > Notifications > Notification Content material, and choose No Identify or Content material.
Your telephone will nonetheless warn you when a message arrives, however it won’t show or retailer the textual content. With out preview information, there’s nothing for the system to retain or for forensic instruments to extract. Apply the identical settings to different messaging apps to keep away from exposing message content material by means of notification logs.