A risk actor group figuring out itself as “LAPSUS$” is claiming accountability for an alleged information breach involving AstraZeneca, one of many world’s largest multinational pharmaceutical and biotechnology firm. The group claims to have obtained roughly 3GB of inside information, together with supply code, cloud infrastructure configurations, and employee-related data.
What the Risk Actor Claims
Based on a submit circulating on a hacker discussion board and the group’s official web site, it alleges entry to:
- Worker-related datasets
- Full supply code (Java, Angular, Python)
- Secrets and techniques and entry credentials (personal keys, vault information)
- Cloud infrastructure configurations (AWS, Azure, Terraform)
and extra…
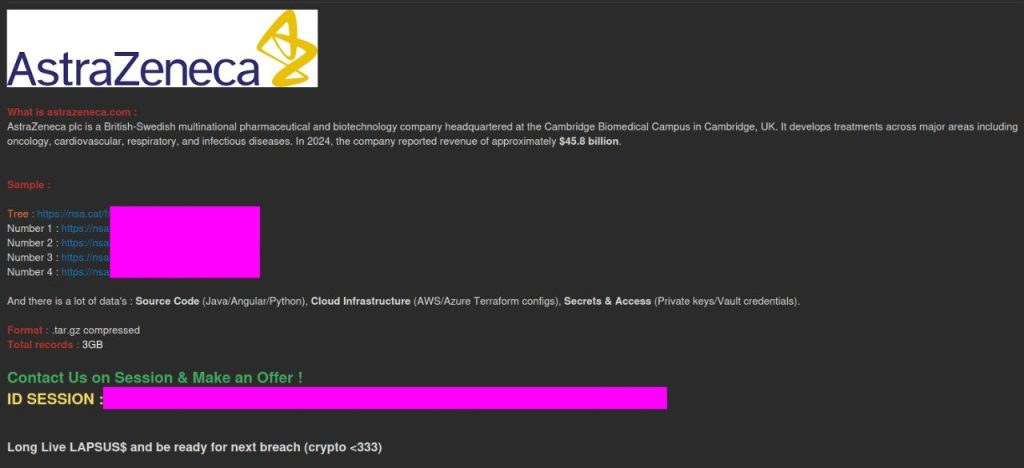
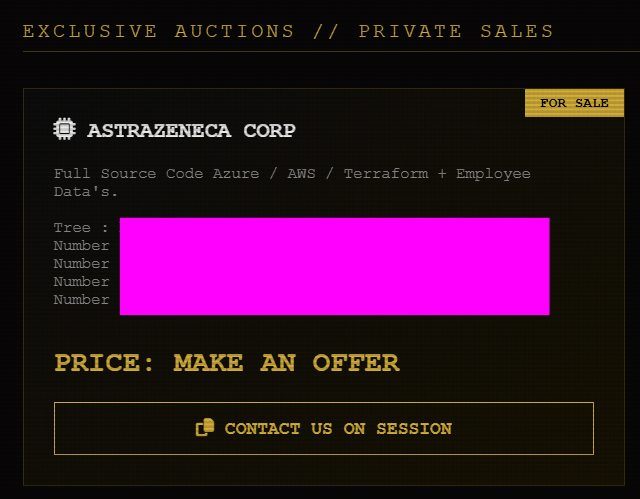
The submit contains references to downloadable archives in .tar.gz format and states a complete information measurement of round 3GB. The hackers try to promote the information to the very best bidder and have shared pattern recordsdata to assist their claims.
A screenshot with the submit shows AstraZeneca branding and a message promoting the information, alongside a session ID for negotiation and a slogan referencing earlier breach exercise.
Evaluation of the Leaked Samples
Hackread.com managed to overview the pattern information, which is split into 3 predominant classes: GitHub-related information, third-party information, and monetary information. Listed here are the small print of what every class incorporates and whether or not the information seems genuine or fabricated.
1. GitHub Enterprise Consumer Information
One pattern file contains structured information resembling exports from a GitHub Enterprise atmosphere. Fields embody:
- Worker names
- Price middle references
- License varieties (Enterprise)
- Enterprise roles and permissions
- Two-factor authentication standing
- GitHub usernames and profile URLs
- Group roles (Proprietor, Member)
Evaluation:
The info construction is in keeping with what could be anticipated from actual enterprise exports tied to GitHub or id and entry administration methods. Its detailed position mappings all through a number of inside organizations recommend visibility from inside a company atmosphere reasonably than data gathered by way of public scraping.
The presence of quite a few accounts with “Proprietor” privileges throughout a number of repositories additionally will increase the stakes, as a result of if genuine, that type of entry information could be extremely delicate. If real, this information might expose inside entry hierarchies and allow focused assaults.
2. Third-Occasion / Contractor Entry Information
One other dataset seems to trace entry requests and onboarding for exterior collaborators, together with:
- Inside person IDs
- Full names and e mail addresses
- Feedback from inside groups
- Firm affiliations (IQVIA, Parexel, Labcorp, and so forth.)
- Entry standing to inside methods (e.g., Confluence)
Evaluation:
This information seems to be an inside entry administration or onboarding log, containing personally identifiable data together with particulars about organizational relationships. The inclusion of operational feedback factors to real inside workflow information reasonably than fabricated content material.
Given the character of the knowledge, the danger degree may be thought of average to excessive, as publicity of contractor relationships and entry methods could possibly be used to assist focused social engineering campaigns.
3. Generic Monetary Information
A 3rd dataset incorporates high-level monetary statistics labeled “All industries” with fields resembling:
- Property
- Salaries
- Whole earnings
- Expenditure
Evaluation:
This information seems to encompass public or generic statistical data reasonably than something particular to AstraZeneca. It was possible included to extend the quantity of the pattern or distract from extra related information. As such, it carries a low threat degree, with no clear sensitivity or direct connection to AstraZeneca’s operations.
Sensitivity of the Alleged Information
| Information Kind | Sensitivity | Impression |
|---|---|---|
| GitHub enterprise roles | Excessive | Privilege escalation, inside mapping |
| Worker / contractor information | Average to Excessive | Phishing, social engineering |
| Cloud infrastructure configs (claimed) | Essential | Full atmosphere compromise |
| Generic monetary information | Low | No direct threat |
If the claimed “secrets and techniques and entry” information is actual, that will characterize probably the most extreme threat, although no direct proof of such materials is current within the samples reviewed. Nevertheless, attribution in cybercrime boards is unreliable, and the usage of the title doesn’t verify the group’s involvement.
On the time of writing, these claims stay unverified. We now have reached out to AstraZeneca for affirmation or remark. We’ll replace this story if and when the corporate responds.