The assault arsenal by extensively abusing Microsoft Visible Studio Code configuration recordsdata to ship and execute malicious payloads on compromised methods.
This evolution within the Contagious Interview marketing campaign represents a classy shift towards weaponizing reputable developer instruments.
The an infection chain begins when victims clone and open malicious Git repositories hosted on GitHub or GitLab, sometimes underneath the guise of recruitment processes or technical assignments.
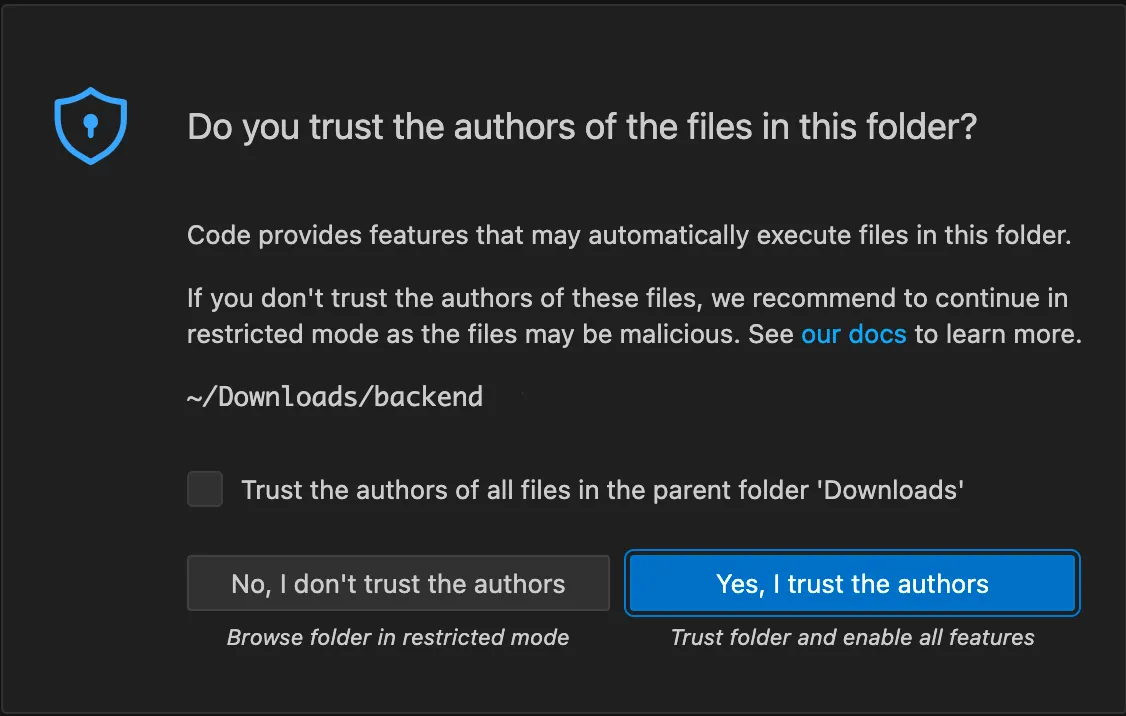
When the mission opens in Visible Studio Code, the appliance prompts customers to belief the repository creator. Upon approval, VS Code mechanically processes the repository’s duties.json configuration file, which might comprise embedded arbitrary instructions that execute on the system.
On macOS methods, this runs a background shell command utilizing nohup bash -c , mixed with curl -s , to retrieve a JavaScript payload from a distant server and pipe it immediately into the Node.js runtime.
This strategy ensures execution continues independently if VS Code is terminated, whereas suppressing all command output.
The malicious JavaScript payloads have been hosted on vercel.app, a platform more and more favored by DPRK-linked menace actors following strikes away from different infrastructure.
Jamf Menace Labs noticed that menace actors modified the URLs referenced inside repositories on a number of events, significantly after Vercel took down beforehand recognized payload internet hosting infrastructure.
Backdoor Performance and Capabilities
The JavaScript payload implements core backdoor logic with three major capabilities: distant code execution, system fingerprinting, and chronic command-and-control (C2) communication.
The distant code execution functionality permits attackers to dynamically execute arbitrary JavaScript code by passing the require operate into the execution context, enabling the import of further Node.js modules for expanded performance.
For system profiling, the backdoor collects host identifiers, together with hostname, MAC addresses from community interfaces, and working system particulars.

It additionally queries ipify.org to find out the sufferer’s public-facing IP tackle a method beforehand noticed in different DPRK-linked campaigns.
Persistent C2 communication operates by a polling routine that beacons to the distant server each 5 seconds. The beacon sends system fingerprinting knowledge and waits for server responses containing tasking directions.
If the server response incorporates particular standing values, the message contents are handed on to the distant code execution routine, enabling attackers to situation new instructions dynamically.
Throughout monitoring of compromised methods, Jamf Menace Labs noticed further JavaScript directions being executed roughly eight minutes after preliminary an infection, establishing related payloads pointing to the identical C2 infrastructure.
Rising Obfuscation Methods
In December, Jamf recognized the introduction of dictionary recordsdata containing closely obfuscated JavaScript that executes when victims open malicious repositories.
These payloads comprise substantial unused capabilities, redundant logic, and extraneous code that inflate file measurement and complexity with out impacting conduct a method designed to evade static evaluation and signature-based detection.
Organizations ought to allow Menace Prevention and Superior Menace Controls set to dam mode. Builders should train warning when interacting with third-party repositories, significantly these from unfamiliar sources.
Earlier than trusting repositories in VS Code, customers ought to assessment repository contents completely, scrutinize bundle.json recordsdata, set up scripts, and job configuration recordsdata earlier than execution.
This marketing campaign underscores how subtle menace actors constantly adapt supply mechanisms to combine with reputable developer workflows, making developer safety consciousness important to organizational protection.
Comply with us on Google Information, LinkedIn, and X to Get On the spot Updates and Set GBH as a Most well-liked Supply in Google.