Evasive Panda, a complicated menace actor recognized by the aliases Bronze Highland, Daggerfly, and StormBamboo, has escalated its offensive capabilities by way of a two-year marketing campaign that has deployed superior assault methods,, together with adversary-in-the-middle (AitM) assaults and DNS poisoning.
In accordance with June 2025 analysis, the group maintained persistent operations between November 2022 and November 2024, focusing on victims throughout Turkey, China, and India with evolving malware supply mechanisms designed to evade detection.
The marketing campaign reveals a marked evolution within the menace actor’s operational method. Slightly than counting on direct distribution strategies, Evasive Panda orchestrated highly-targeted assaults utilizing AitM methods mixed with DNS poisoning to intercept authentic visitors and redirect victims to attacker-controlled servers.
The attackers distributed loaders disguised as authentic utility updates together with SohuVA, iQIYI Video, IObit Sensible Defrag, and Tencent QQ exploiting consumer belief in acquainted software program distributors to determine preliminary system entry.
Technical Sophistication
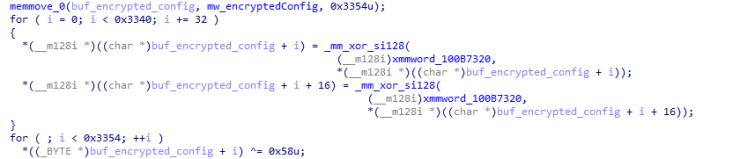
The sophistication of Evasive Panda’s loader demonstrates vital growth funding. Written in C++ utilizing the Home windows Template Library (WTL), the malware employs a number of encryption layers and obfuscation methods to complicate evaluation.
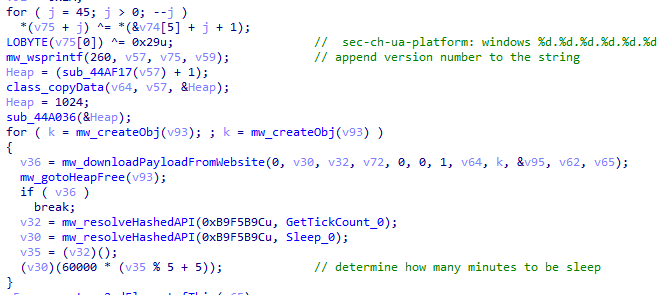
The loader makes use of XOR-based decryption algorithms to show configuration components solely after execution, whereas all crucial strings together with system paths and command execution parameters stay encrypted till runtime.
Most notably, the attackers developed a novel injector enabling in-memory execution of their MgBot implant inside authentic processes.
By leveraging DLL sideloading methods with a decade-old signed executable (evteng.exe), the group achieved persistent presence with out writing major payloads to disk. This method considerably reduces detection floor and complicates forensic investigation.
The DNS poisoning mechanism represents the marketing campaign’s most modern ingredient. Attackers manipulated DNS responses for authentic web sites, together with dictionary.com, redirecting victims’ programs to attacker-controlled infrastructure based mostly on geographical location and ISP affiliation.
The malware retrieves encrypted payloads disguised as PNG photos from these poisoned domains, with payload choice tailor-made to the sufferer’s Home windows model and system configuration.
The an infection chain employs multi-stage execution: the preliminary loader decrypts shellcode and retrieves encrypted second-stage payloads by way of DNS-poisoned visitors.
To stop interception and evaluation, attackers carried out customized hybrid encryption combining Microsoft’s Information Safety API (DPAPI) with RC5 encryption.
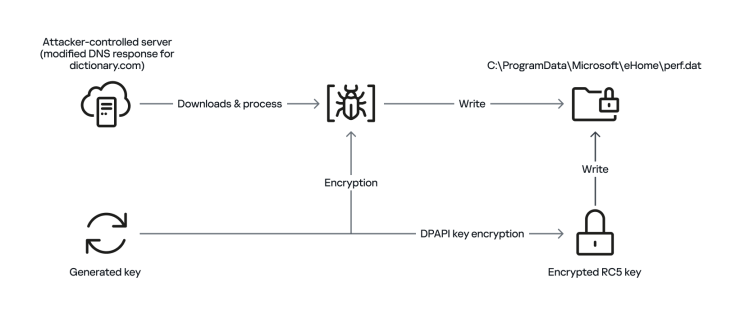
This method ensures payload decryption happens solely on compromised programs, creating uneven benefits for defenders trying forensic restoration.
Persistence and Attribution
Some compromised programs maintained energetic infections for over one yr, indicating sustained operational dedication.
The attackers maintained a number of command-and-control (C2) servers energetic for years, suggesting deliberate infrastructure redundancy designed to protect management regardless of potential takedown operations.
Attribution to Evasive Panda seems extremely assured based mostly on tactical convergence with historic operations.
The group’s constant use of supply-chain compromise, AitM methods, and watering-hole assaults mixed with the resurgent MgBot implant with enhanced configuration components aligns with established menace actor behaviors.
Regardless of technical visibility, crucial operational gaps stay. Researchers have but to find out how Evasive Panda initially compromises community infrastructure to execute DNS poisoning at scale.
Two believable eventualities exist: both selective ISP community implants had been deployed, or victim-controlled community gadgets (routers, firewalls) had been independently compromised.
The marketing campaign demonstrates sustained evolution inside Evasive Panda’s toolkit. New loader growth suggests extra functionality enhancements stay forthcoming.
Organizations ought to implement strong DNS monitoring, community segmentation limiting lateral motion potential, and endpoint detection mechanisms tuned for multi-stage shellcode execution patterns.
Comply with us on Google Information, LinkedIn, and X to Get Instantaneous Updates and Set GBH as a Most well-liked Supply in Google.










