Researchers at Howler Cell have found a brand new .NET AOT malware marketing campaign that makes use of a intelligent scoring system to bypass safety instruments and steal your information.
Cybersecurity researchers at Howler Cell have found a brand new multi-layered malware marketing campaign that makes use of a selected programming methodology known as .NET Forward-of-Time (AOT) compilation to make the malware practically invisible to plain safety instruments.
For context, most fashionable software program accommodates metadata (a digital map that helps safety instruments perceive what a program is doing). This new AOT methodology strips that map away, turning the code right into a black field, which forces specialists to depend on guide, native-level instruments to see what is definitely occurring underneath the hood.
A Advanced Recreation of Digital Disguise-and-Search
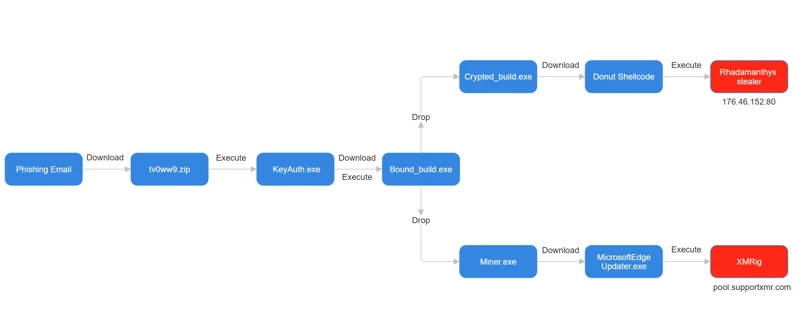
The difficulty normally begins with a suspicious hyperlink, probably unfold by way of phishing emails. When a sufferer opens this ZIP file, they see a number of legitimate-looking modules that make the folder seem secure. Nevertheless, the actual risk is a file named KeyAuth.exe. When this downloader is energetic, it quietly fetches a second-stage file known as bound_build.exe.
As researchers probed additional, they realised that bound_build.exe is the principle architect for the assault. It’s chargeable for XOR-decrypting and launching two further threats. The primary, Crypted_build.exe, retrieves a infamous infostealer referred to as Rhadamanthys, whereas the second, Miner.exe, ultimately installs MicrosoftEdgeUpdater, which is a disguised loader for the XMRig cryptocurrency miner.
How the Malware Exams Your PC
What makes this risk stand out is the way it evaluates a pc earlier than it strikes. Researchers famous that the loader makes use of a intelligent scoring system to determine whether it is operating on an actual sufferer’s PC or a researcher’s sandbox machine. It checks issues like your RAM, including factors in case you have over 8GB, and your system uptime.
The malware even counts your recordsdata; in case you have greater than ten recordsdata in your Paperwork folder, it considers you a possible human goal. Moreover, it appears to be like for frequent antivirus processes like WinDefend or Kaspersky. If the ultimate rating is under 5, the malware assumes it’s being watched and easily shuts itself right down to keep away from detection.
Cracking the Black Field
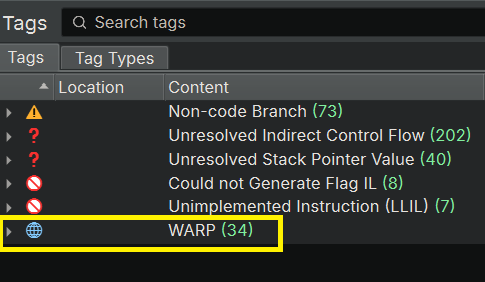
Regardless of these hurdles, the staff at Howler Cell used a software known as Binary Ninja to interrupt by way of the defences, the weblog submit reads. By making a customized WARP signature, they may reconstruct this system’s inside workings. “WARP eradicated the necessity to manually examine virtually 4,000 library features,” researchers famous. This course of was an enormous success, taking their visibility from lower than 1% to over 85%.
The important thing takeaway from this marketing campaign is that hackers are getting higher at staying dormant to evade detection. To remain secure, you must by no means obtain ZIP recordsdata from untrusted hyperlinks, and maintaining your system up to date stays your finest defence in opposition to these rising threats.