Hackers are abusing adversary-in-the-middle (AiTM) session hijacking to steal worker salaries in a brand new “payroll pirate” marketing campaign tracked by Microsoft as Storm-2755 and focusing on Canadian customers.
By hijacking reside Microsoft 365 classes, the group redirects payroll deposits to attacker-controlled financial institution accounts whereas bypassing multifactor authentication (MFA) and mixing in with regular person exercise.
The group’s finish purpose is to switch payroll and HR data in order that salaries are silently routed to accounts they management, inflicting direct monetary losses for each employees and employers.
As an alternative of spear-phishing a particular sector, Storm-2755 depends on malvertising and search engine optimization poisoning for broad, generic searches like “Workplace 365” or mistyped queries comparable to “Workplace 265.”
Based on Microsoft Incident Response Detection and Response Crew (DART), Storm-2755 is a financially motivated actor centered on Canadian staff relatively than any single business or group.
These poisoned outcomes push an attacker area, bluegraintours[.]com, to the highest of search outcomes, luring victims right into a faux Microsoft 365 sign-in web page that intently mimics the official portal.
AiTM signal‑in web page and Axios hijack
When customers enter their company credentials on the spoofed web page, the attacker’s infrastructure proxies the true Microsoft 365 sign-in circulate, stealing each passwords and session tokens in actual time.
Logs from affected tenants present a 50199 signal‑in interrupt error simply earlier than Storm-2755 efficiently takes over the account, adopted by the identical session ID persevering with below a distinct person‑agent, Axios 1.7.9, indicating token replay relatively than a traditional login.
This sample matches an AiTM assault, the place the adversary sits between the person and the cloud service to seize session cookies and OAuth entry tokens that characterize a totally authenticated session.
As a result of these tokens are already validated, the attacker can reuse them to entry Microsoft 365 providers with out re-entering credentials or passing conventional MFA challenges, successfully bypassing non–phishing-resistant MFA.
Storm-2755 then makes use of Axios 1.7.9 as an HTTP consumer to silently replay stolen tokens again into the sufferer’s atmosphere, sustaining non‑interactive sign-ins to the OfficeHome software roughly each half-hour.
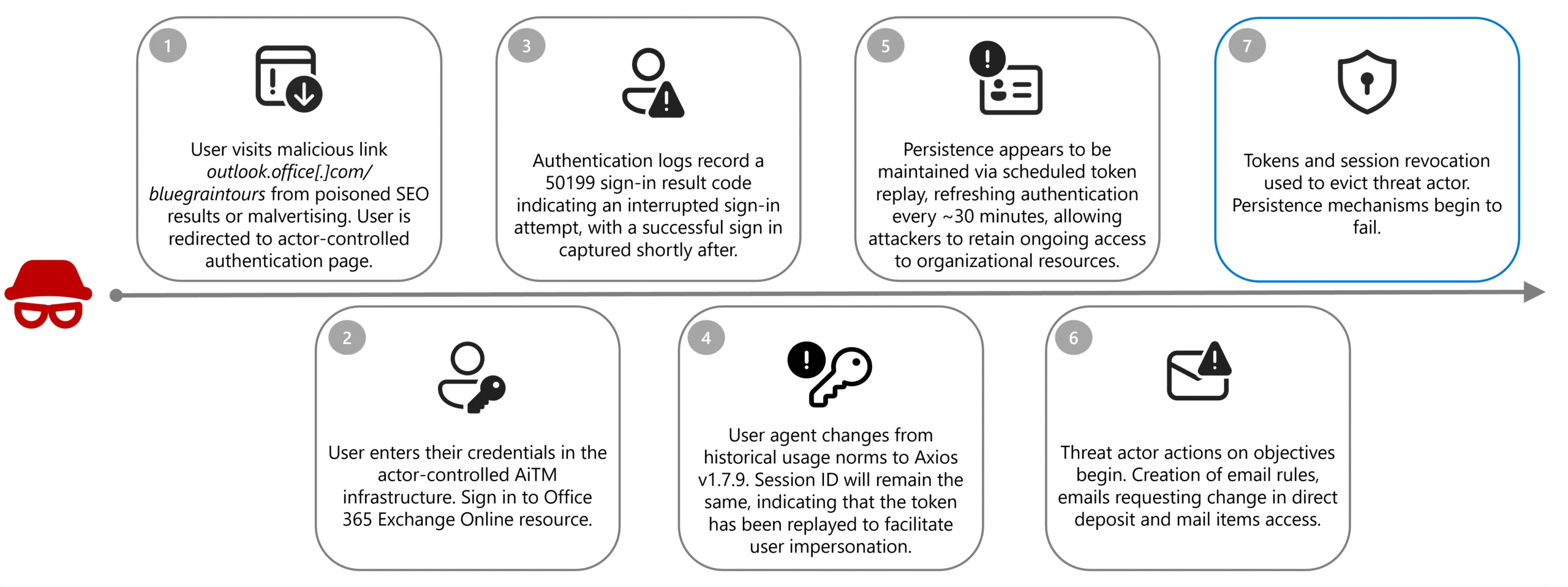
This periodic token replay preserves their entry with out prompting the person till defenders revoke lively classes, reset credentials, or implement stricter token-lifetime insurance policies.
In lots of instances, stolen tokens stay usable for round 30 days except disrupted by expiration, rotation, or coverage modifications, throughout which the actor can sign up to Outlook, My Signal‑Ins, My Profile, and HR platforms.
For a subset of victims, Storm-2755 goes additional by altering passwords and MFA settings to determine longer‑time period persistence even after unique tokens expire.
Mitigations
As soon as inside, Storm-2755 conducts focused searches throughout intranet portals, SharePoint, and mailboxes for key phrases like “payroll”, “HR”, “finance”, “account”, and “admin” to find wage and HR workflows.
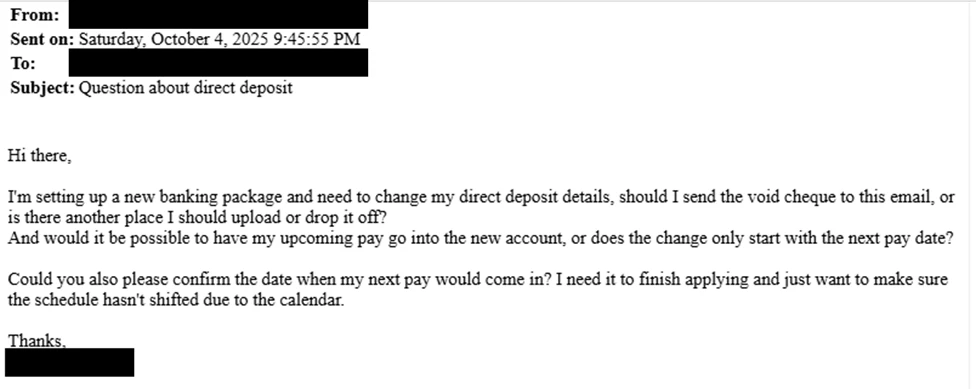
Additionally they ship emails with topics comparable to “Query about direct deposit” to HR or finance groups, impersonating staff to request modifications to financial institution particulars.
The place social engineering fails, the actor pivots instantly into SaaS platforms like Workday utilizing the hijacked session to replace direct deposit data manually.
In a single confirmed case, Storm-2755 efficiently modified Workday banking particulars in order that the sufferer’s paycheck was routed to an attacker-owned account, with the worker solely realizing after lacking a wage cost.
To cover their exercise, the attackers create inbox guidelines that transfer emails containing “direct deposit” or “financial institution” into hidden folders comparable to Dialog Historical past, stopping victims from seeing HR responses about account modifications.
Additionally they are likely to refresh stolen classes round 5:00 AM within the person’s time zone, lowering the prospect {that a} official login will invalidate their token replay.
Microsoft recommends instant token revocation, elimination of malicious inbox guidelines, and compelled credential and MFA resets for impacted accounts, together with implementing phishing‑resistant MFA comparable to FIDO2/WebAuthn.
Organizations are additional urged to use Conditional Entry with adaptive session lifetimes and Steady Entry Analysis, monitor for uncommon person‑brokers like Axios accessing OfficeHome, and alert on suspicious inbox rule creation as a part of their broader zero‑belief and SIEM monitoring technique.
Comply with us on Google Information, LinkedIn, and X to Get On the spot Updates and Set GBH as a Most well-liked Supply in Google.









