New analysis from Varonis Risk Labs reveals Storm infostealer, a malicious subscription service that bypasses Google Chrome encryption. Learn the way this device makes use of server-side decryption and cookie theft to focus on crypto wallets and personal accounts with out triggering safety alarms.
A brand new risk dubbed Storm infostealer is discovering methods to interrupt into our net browsers. Found by Varonis Risk Labs in early 2026, Storm is a trojan horse that, upon an infection, seems to be to reap victims’ browser credentials, session cookies, crypto wallets, and associated knowledge, amongst different info.
As soon as the knowledge is collected, it’s then despatched to a non-public server owned by the attackers. In accordance with researchers, Storm infostealer makes use of a way known as server-side decryption for this goal, which additionally makes it troublesome for antivirus software program to detect, since there isn’t any telemetry knowledge left.
It is a direct response to App-Certain Encryption, a safety defend Google launched in Chrome 127 again in July 2024. Whereas that replace was meant to tie encryption keys on to the browser to forestall knowledge theft, Storm infostealer has the power to bypass this impediment.
Moreover, in addition to Google Chrome, it might additionally extract knowledge from different Chromium-based browsers and Gecko-based browsers, together with Microsoft Edge, Firefox, and Waterfox.
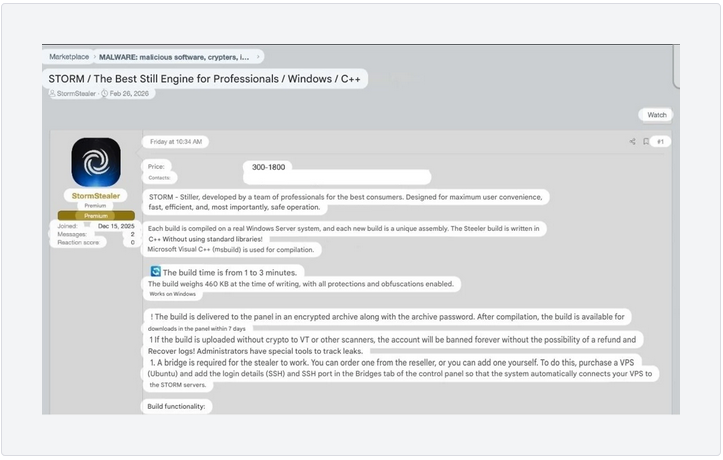
As Varonis researchers famous, the device has a really broad vary of goal browsers. No marvel it has been “productised and bought as a subscription characteristic,” with costs beginning at $300 for a seven-day demo and climbing to $1,800 for skilled felony groups.
What’s worse, since Storm infostealer can hijack periods, in your info, if a hacker has your session cookie, your Multi-Issue Authentication (MFA) turns into fully irrelevant as a result of they’re already “in.” Varonis discovered that the device is already getting used within the wild, with a logs panel exhibiting 1,715 entries from victims within the following nations:
- India
- Brazil
- United States
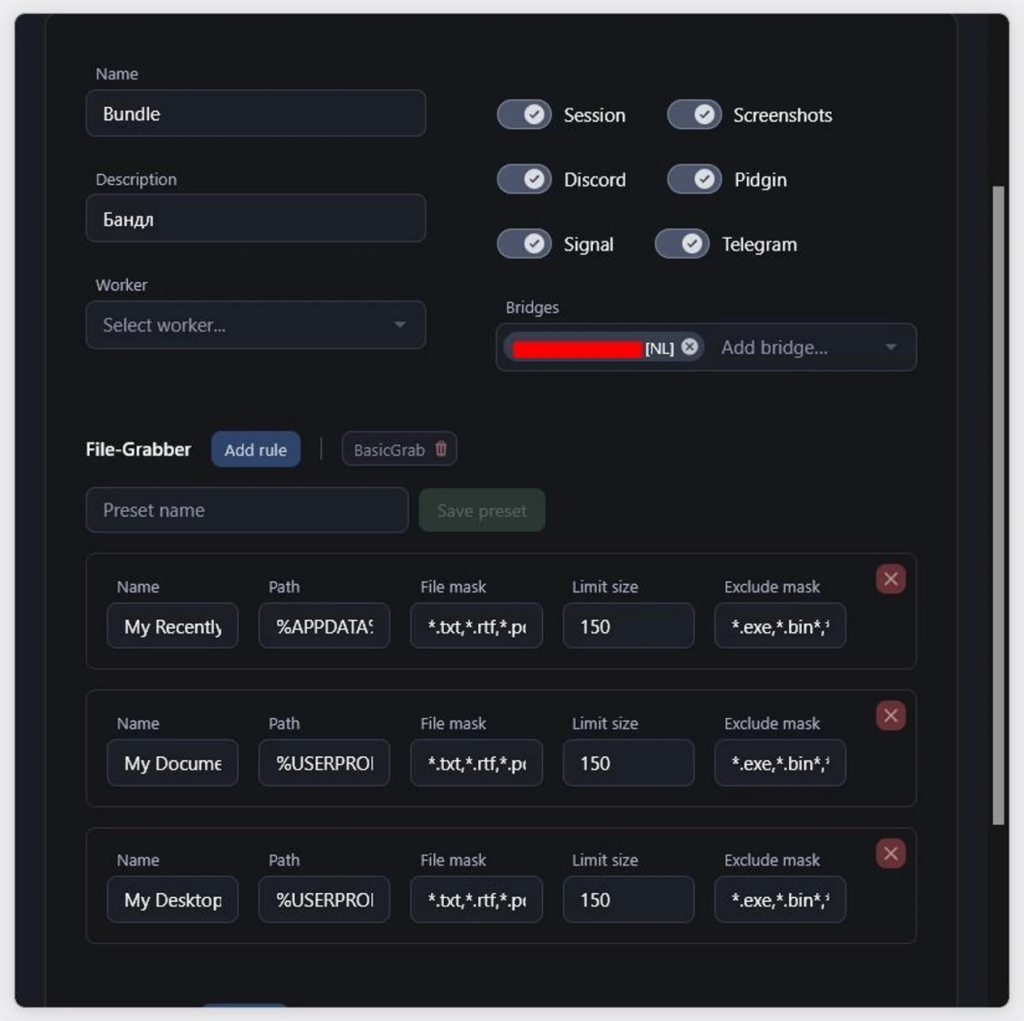
- United Kingdom
Nonetheless, the risk doesn’t finish there. Storm Infostealer additionally targets Telegram, Sign, and Discord accounts, whereas concurrently trying to find crypto wallets on platforms like Binance and Coinbase. It will probably even take screenshots throughout a number of screens to see precisely what you’re engaged on.
To guard your gadgets and knowledge from Storm infostealers, customers ought to know that hackers depend on their periods staying energetic for lengthy intervals; subsequently, manually logging out of delicate banking or crypto accounts when you find yourself completed is necessary, somewhat than simply closing the tab. As Varonis risk specialists warn within the report, these stolen periods are normally simply “the beginning of what comes subsequent,” resulting in whole account takeovers that ignore even the strongest passwords.