A extremely adaptable risk named VoidLink is placing cloud environments on excessive alert. First delivered to gentle by Verify Level Analysis on January 14, 2026, and reported by hackread.com, this Chinese language-developed framework is designed to infiltrate essential enterprise infrastructure.
The Breakthrough: Serverside Rootkit Compilation (SRC)
Following the invention, the Sysdig Risk Analysis Staff (TRT) recognized a ground-breaking technical characteristic: Serverside Rootkit Compilation (SRC). Usually, hackers face a portability drawback, the place a virus constructed for one model of Linux crashes on one other.
VoidLink solves this by not together with a rootkit within the preliminary obtain. As a substitute, its Command-and-Management (C2) server compiles a customized rootkit on demand for every particular sufferer. The malware profiles the precise kernel model of the contaminated machine and sends these particulars to the C2. The server then builds a “stealth cloak” (an eBPF or LKM rootkit) made particularly for that system, making certain it runs completely with out crashing or leaving apparent clues.
The Zig Programming Alternative
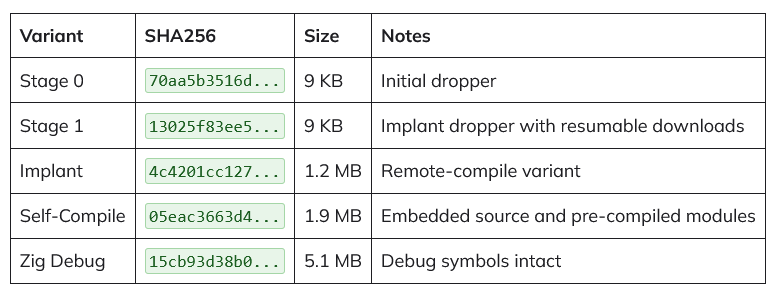
Researchers additionally discovered that VoidLink is the primary Chinese language-language malware written in Zig. This contemporary programming language is an uncommon alternative for attackers, nevertheless it gives a definite benefit; safety instruments aren’t but tuned to recognise Zig’s particular patterns. This permits VoidLink’s 1.2MB implant to evade commonplace safety filters that search for C++ or Go patterns whereas sustaining highly effective, low-level management over the contaminated system.
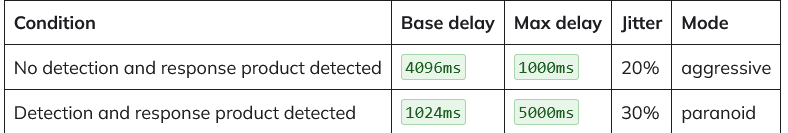
Sysdig’s evaluation highlights that VoidLink doesn’t simply conceal; it actively hunts for defenders. The malware scans for 14 distinct safety merchandise, together with CrowdStrike, SentinelOne, Carbon Black, and Sysdig’s personal Falco. If detected, it intelligently adjusts its evasion technique by switching from an “aggressive” mode to a “paranoid” mode.
In paranoid mode, it slows down its exercise and will increase the time between its check-ins (heartbeats) to keep away from triggering behavioural alerts or being flagged by runtime scanners.
Fileless Execution
To minimise its footprint, VoidLink makes use of a three-stage supply mechanism designed to remain completely in reminiscence (fileless execution).
- Stage 0: A tiny 9KB dropper that masquerades as a background activity referred to as .
- Execution: It makes use of particular system calls (memfd_create and execveat) to create nameless reminiscence information, making certain the malware by no means touches the bodily arduous drive.
- Communication: Outdoors commonplace internet visitors, it makes use of a covert ICMP “ping” channel to obtain instructions, making its community presence appear to be routine connectivity checks.
Defending Your Workspace
Since VoidLink is so adept at hiding, fundamental safety scans merely gained’t detect it. The malware makes use of specialised plugins to flee remoted digital containers and take over Kubernetes environments. Nevertheless, even a risk this superior isn’t invisible. Researchers famous that the malware nonetheless leaves a path. Through the use of instruments to observe for uncommon reminiscence exercise or the loading of unauthorised kernel modules, safety groups can catch VoidLink earlier than it does actual injury.
Knowledgeable’s commentary
In a remark shared with hackread.com, Mayuresh Dani, Safety Analysis Supervisor at Qualys Risk Analysis Unit, famous that whereas the risk is critical, the malware seems to be a piece in progress.
“The saving grace is that the framework was found as an ‘in progress’ construct with debug symbols nonetheless embedded. Because of this it’s nonetheless not a completed product, and that risk actors are making ready for imminent operational deployment however haven’t but begun large-scale concentrating on.”
(Photograph by Growtika on Unsplash)