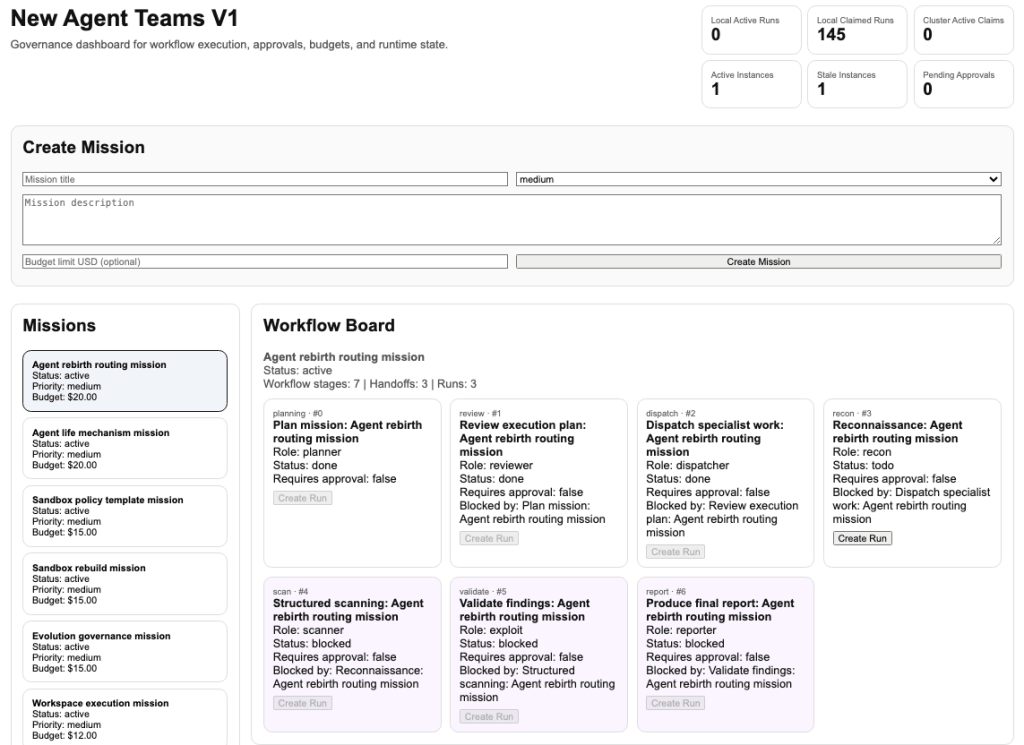
The SOCRadar Menace Analysis Staff has found an enormous, automated cybercrime setup linked to menace actors based mostly in China. This operation makes use of a central backend known as Paperclip and an agent-based workflow system referred to as OpenClaw.
Utilizing these instruments, the hackers run their campaigns like a enterprise, with a step-by-step workflow that begins with Planning, adopted by Overview, Dispatch, Recon, Scan, Validate, and ends with a Report on the stolen knowledge. The small print of this analysis had been shared with Hackread.com.
How the Assaults Work
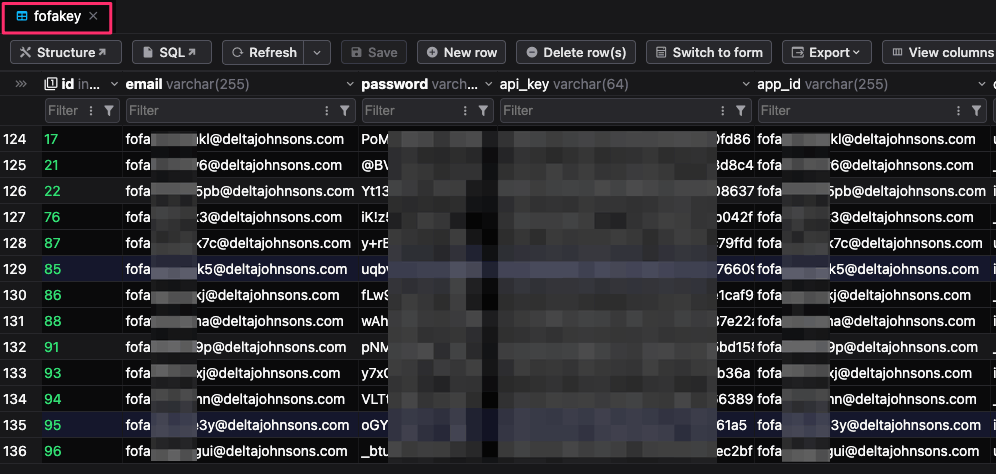
Hackers use web mapping engines equivalent to FOFA and 360Quake to establish the Exterior Assault Floor (internet-facing belongings). They significantly goal high-value teams like fintech firms, Web3 platforms, and safety distributors. To make sure their scanning stays uninterrupted, they’ve created 1000’s of automated accounts utilizing the e-mail sample fofa.
This scanning helps them discover techniques working software program with recognized safety flaws. They like flaws that permit distant code execution (RCE) to realize full management over the compromised system, equivalent to React2Shell (CVE-2025-55182) and CVE-2025-66478, and Log4Shell (CVE-2021-44228).
Researchers noticed 4 customized Python scripts, 2.py, 3.py, 4.py, and 11.py, which assist the attackers make this whole course of quicker and bypass safety filters. This additionally helps them run instructions on lots of of targets directly.
“Customized Python scripts automate exploitation by executing instructions equivalent to surroundings variable dumps. These scripts assist WAF bypass and parallel execution, enabling scalable exploitation throughout lots of of targets. The first goal is dependable distant code execution relatively than easy vulnerability detection,” researchers famous within the weblog put up.
Stealing Knowledge and Sustaining Persistence
After reaching preliminary entry, the menace actors seek for delicate knowledge, primarily concentrating on AI API keys, Stripe tokens, and database credentials saved in PostgreSQL. To keep up persistence, they use a number of strategies to make sure they keep hidden, like deploying Cloudflare tunnels through cf-client, P2P purchasers named mayun, and backdoors recognized in logs as d2 and pl.
The group additionally makes use of a fileless execution chain utilizing instructions that feed net content material straight into Node.js to run malicious code within the system’s reminiscence with out saving any recordsdata to the disk. This makes malware detection rather more tough.
The Scale of the Operation
This can be a very giant operation. The hackers’ personal logs present round 45,000 assault makes an attempt. Their database exhibits they’ve positioned the d2 backdoor on 3,981 hosts and the pl backdoor on 1,393 hosts. Additionally they managed 900 webshell implants and are monitoring practically 22,000 cryptocurrency addresses.
For context, d2 and pl are two customized backdoor implants utilized by the attackers to keep up entry to the compromised system.
“The operation is coordinated by way of a centralised backend,” the report explains, which helps the group handle and enrich stolen knowledge. The hackers use blockchain intelligence APIs equivalent to OKLink and Tatum to observe practically 22,000 cryptocurrency addresses. Additionally they use automated scripts to validate stolen Stripe keys by checking for energetic accounts with obtainable balances. This organised strategy permits the menace actors to instantly prioritise probably the most worthwhile targets.