BI.ZONE mentioned the Paper Werewolf delivered the exploits in July and August by means of archives hooked up to emails impersonating staff of the All-Russian Analysis Institute. The last word objective was to put in malware that gave Paper Werewolf entry to contaminated techniques.
Whereas the discoveries by ESET and BI.ZONE had been unbiased of one another, it’s unknown if the teams exploiting the vulnerabilities are linked or acquired the information from the identical supply. BI.ZONE speculated that Paper Werewolf might have procured the vulnerabilities in a darkish market crime discussion board.
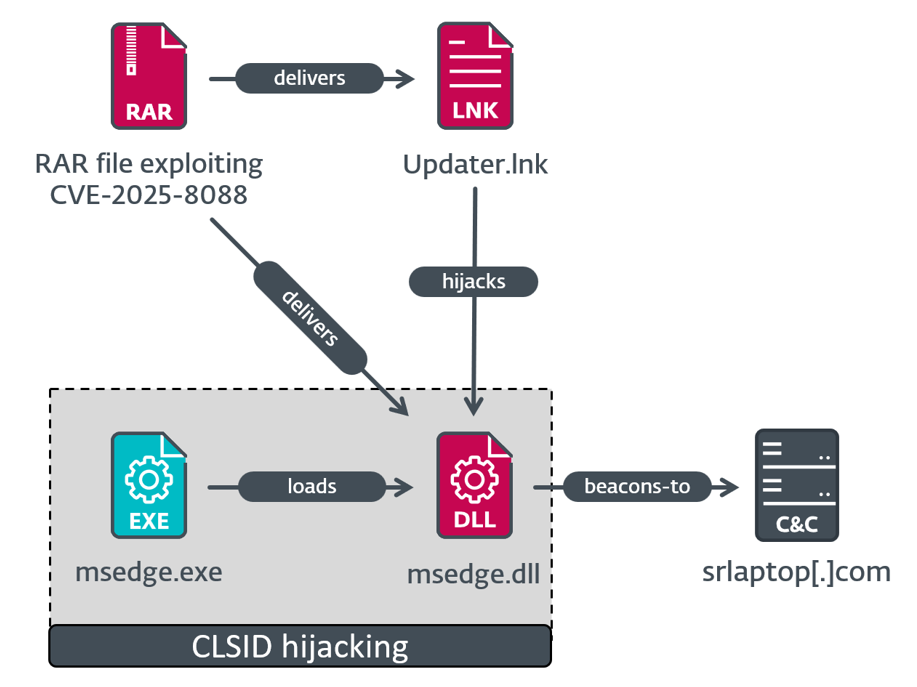
ESET mentioned the assaults it noticed adopted three execution chains. One chain, utilized in assaults focusing on a particular group, executed a malicious DLL file hidden in an archive utilizing a technique often called COM hijacking that precipitated it to be executed by sure apps corresponding to Microsoft Edge. It regarded like this:
Illustration of the execution chain putting in Mythic Agent.
Credit score:
ESET
The DLL file within the archive decrypted embedded shellcode, which went on to retrieve the area identify for the present machine and examine it with a hardcoded worth. When the 2 matched, the shellcode put in a customized occasion of the Mythic Agent exploitation framework.
A second chain ran a malicious Home windows executable to ship a last payload putting in SnipBot, a identified piece of RomCom malware. It blocked some makes an attempt at being forensically analyzed by terminating when opened in an empty digital machine or sandbox, a follow widespread amongst researchers. A 3rd chain made use of two different identified items of RomCom malware, one often called RustyClaw and the opposite as Melting Claw.
WinRAR vulnerabilities have beforehand been exploited to put in malware. One code-execution vulnerability from 2019 got here beneath broad exploitation in 2019 shortly after being patched. In 2023, a WinRAR zero-day was exploited for greater than 4 months earlier than the assaults had been detected.
Moreover its huge person base, WinRAR makes an ideal car for spreading malware as a result of the utility has no automated mechanism for putting in new updates. Meaning customers should actively obtain and set up patches on their very own. What’s extra, ESET mentioned Home windows variations of the command-line utilities UnRAR.dll and the moveable UnRAR supply code are additionally weak. Individuals ought to avoid all WinRAR variations previous to 7.13, which, on the time this put up went dwell, was probably the most present. It has fixes for all identified vulnerabilities, though given the seemingly endless stream of WinRAR zero-days, it isn’t a lot of an assurance.