GnuPG, generally often called GPG, is an open supply implementation of the Fairly Good Privateness cryptography commonplace. It gives symmetric and uneven encryption for information at relaxation and in transit.
This text introduces the right way to use GPG, demonstrates its set up on widespread OSes and offers directions for its use.
How does GPG shield information?
Encryption seeks to fulfill the next three targets:
- Authenticity. Guaranteeing the supply of a message.
- Integrity. Guaranteeing a message didn’t change unexpectedly.
- Nonrepudiation. Guaranteeing the supply of the message.
GPG satisfies all three targets by combining symmetric and uneven cryptography to guard saved information and digital communications.
Symmetric and uneven cryptography are important parts of in the present day’s safety and privateness methods. Symmetric cryptography makes use of a single non-public key (shared secret) to each encrypt and decrypt information, whereas uneven cryptography makes use of a mathematically associated private and non-private key pair. Knowledge encrypted with one key can solely be decrypted by the opposite — for instance, information encrypted utilizing the general public key can solely be decrypted utilizing the associated non-public key.
GPG combines these two approaches and allows customers to make sure information privateness, supply and integrity. Consequently, GPG is broadly used and supported.
Widespread GPG use circumstances
Take into account the next methods to make use of GPG to safe information storage and transmission:
- Encrypted electronic mail for confidentiality.
- Digitally signed electronic mail for authenticity.
- Encrypted information for information confidentiality.
- Digitally signed software program packages, scripts and different functions.
- Digitally signed Git commits.
Take into account your personal workflow to find out further methods GPG can shield your data.
Set up GPG
GPG is free and open supply software program, serving to to make sure its safety and stability. It’s out there for widespread platforms, together with Linux, macOS and Home windows.
Most Linux distributions embrace GPG by default. Use the gpg –version command to confirm you will have a present model. Use your distribution’s most well-liked package deal supervisor if GPG is not current.
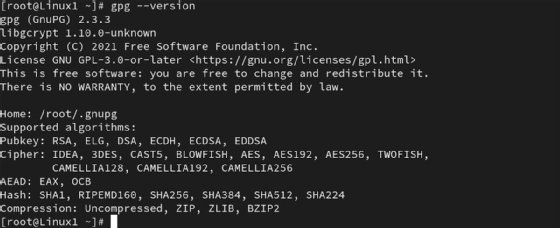
For Ubuntu, Debian Linux Mint and comparable distributions, sort:
sudo apt set up gnupg
On Crimson Hat Enterprise Linux, Fedora, Rocky and comparable distributions, sort:
sudo dnf -y set up gnupg
MacOS customers can set up GPG utilizing the Homebrew package deal supervisor by typing:
brew set up gnupg
MacOS customers may use the GPG Suite graphical utility to handle encryption.
Those that want the Home windows platform can entry GPG two methods: GnuPG binary is the official installer from the GnuPG web site, and Gpg4win is the graphical/command-line utility.
Easy methods to use GPG for symmetric cryptography
Symmetric encryption gives probably the most simple administration course of. You have to, nevertheless, be capable to securely ship the important thing to any distant connections the place decryption must happen. This strategy works greatest for information encryption situations on a single system or inside a safe surroundings.
The best technique to encrypt a file makes use of this command:
gpg -c private-file.txt
It ends in an encrypted file named private-file.txt.gpg.
GPG prompts you to enter a passphrase to guard the file.
You possibly can specify extra element, reminiscent of a particular file title, by utilizing the next extra advanced command:
gpg --output new-private-file.txt.gpg --symmetric private-file.txt
To then decrypt the new-private-file.txt.gpg file, sort:
gpg --output private-file.txt --decrypt private-file.txt.gpg
You possibly can substitute the -o and -d flags for rather less typing. GPG routinely prompts for the passphrase you set for the non-public key.
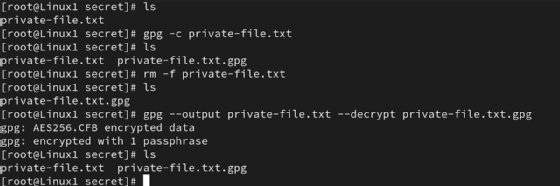

Use this course of to guard information backup information, confidential data on shared computer systems or sources you are transferring to and from distant storage gadgets.
Observe that GPG generates a brand new model of the file through the encryption course of. The unique nonencrypted file stays on the drive. Take into account securely deleting it utilizing a command reminiscent of shred.
Easy methods to generate key pairs for uneven cryptography
Start utilizing GPG by producing a public-private key pair. These keys are mathematically associated. With uneven cryptography, in case you encrypt information with one key, you should decrypt it with the opposite key. Listed here are examples of the 2 choices:
- Confidentiality. Encrypt with the general public key, decrypt with the non-public key.
- Digital signatures, integrity. Encrypt with the non-public key, decrypt with the general public key.
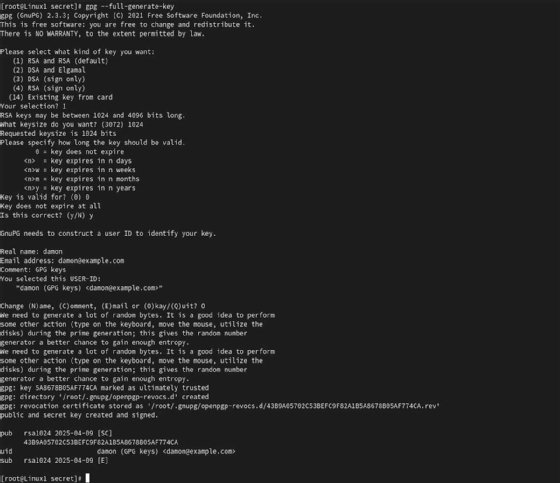
On a Linux system, sort the next command to generate the important thing pair:
gpg --full-generate-key
You’ve got varied choices to customise the important thing size, sort and different settings. GPG prompts you to enter your title and electronic mail deal with as a part of your key identification. You can even set a powerful passphrase to guard your non-public key.
You’ll possible must share your public key with different customers to allow them to decrypt information encrypted utilizing your non-public key. Use the next command to export the required public key data:
gpg --armor --export [email protected] > pubkey.asc
For those who obtain one other consumer’s public key or want to supply directions to a recipient of your public key, use this command to import it into your system:
gpg --import pubkey.asc
Confirm the important thing exists by typing gpg –list-public-keys. The consumer’s public key lets you decrypt information encrypted with the associated non-public key.
Easy methods to use GPG for uneven cryptography
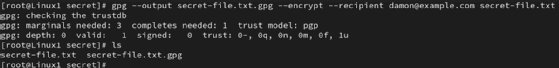
To encrypt a file utilizing one other consumer’s public key — due to this fact guaranteeing solely that consumer can decrypt the info primarily based on their possession of the associated non-public key — sort the next command:
gpg --output secret-file.txt.gpg --encrypt --recipient [email protected] secret-file.txt
This command specifies the title of the encrypted file — secret-file.txt.gpg — and the recipient’s electronic mail deal with — [email protected]. You might be encrypting the secret-file.txt file on this instance.
On the different finish of the info switch, the consumer enters the next command to start the decryption course of:
gpg --output secret-file.txt --decrypt secret-file.txt.gpg
That consumer enters the passphrase defending their non-public key to finish the method.
Integrating GPG encryption into your day by day routine can vastly improve the safety of your information. You already do backups, proper? Now, you may encrypt these backups for larger confidentiality. You additionally conduct important enterprise utilizing electronic mail. Studying the right way to use GPG to digitally signal messages provides a considerable layer of safety to communications.
Damon Garn owns Cogspinner Coaction and offers freelance IT writing and enhancing companies. He has written a number of CompTIA examine guides, together with the Linux+, Cloud Necessities+ and Server+ guides, and contributes extensively to Informa TechTarget, The New Stack and CompTIA Blogs.










