A prolific cybercriminal group that calls itself “Scattered LAPSUS$ Hunters” has dominated headlines this yr by commonly stealing information from and publicly mass extorting dozens of main companies. However the tables appear to have turned considerably for “Rey,” the moniker chosen by the technical operator and public face of the hacker group: Earlier this week, Rey confirmed his actual life id and agreed to an interview after KrebsOnSecurity tracked him down and contacted his father.
Scattered LAPSUS$ Hunters (SLSH) is regarded as an amalgamation of three hacking teams — Scattered Spider, LAPSUS$ and ShinyHunters. Members of those gangs hail from most of the identical chat channels on the Com, a largely English-language cybercriminal neighborhood that operates throughout an ocean of Telegram and Discord servers.
In Could 2025, SLSH members launched a social engineering marketing campaign that used voice phishing to trick targets into connecting a malicious app to their group’s Salesforce portal. The group later launched an information leak portal that threatened to publish the inner information of three dozen firms that allegedly had Salesforce information stolen, together with Toyota, FedEx, Disney/Hulu, and UPS.
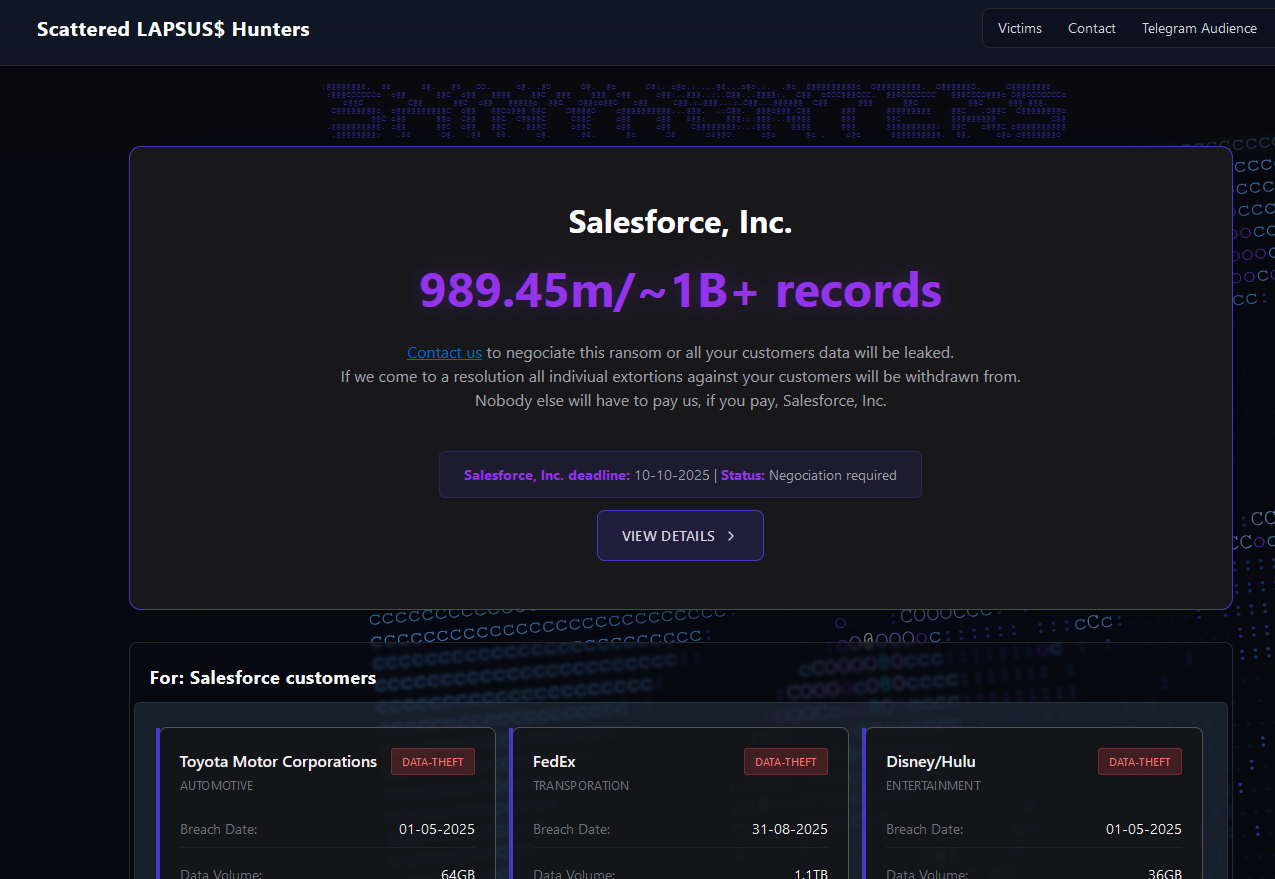
The brand new extortion web site tied to ShinyHunters, which threatens to publish stolen information until Salesforce or particular person sufferer firms comply with pay a ransom.
Final week, the SLSH Telegram channel featured a proposal to recruit and reward “insiders,” workers at massive firms who comply with share inner entry to their employer’s community for a share of no matter ransom cost is in the end paid by the sufferer firm.
SLSH has solicited insider entry beforehand, however their newest name for disgruntled workers began making the rounds on social media on the identical time information broke that the cybersecurity agency Crowdstrike had fired an worker for allegedly sharing screenshots of inner programs with the hacker group (Crowdstrike stated their programs have been by no means compromised and that it has turned the matter over to regulation enforcement businesses).
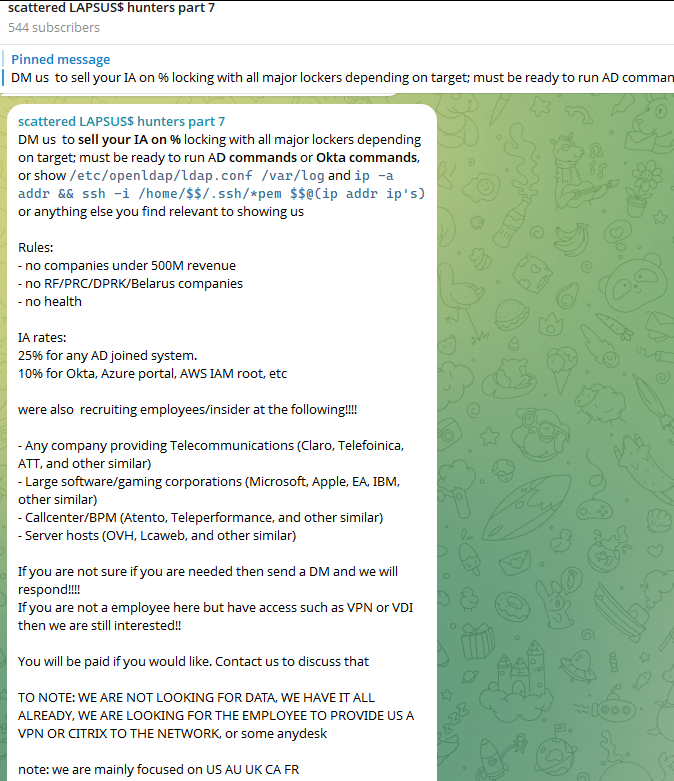
The Telegram server for the Scattered LAPSUS$ Hunters has been trying to recruit insiders at massive firms.
Members of SLSH have historically used different ransomware gangs’ encryptors in assaults, together with malware from ransomware affiliate packages like ALPHV/BlackCat, Qilin, RansomHub, and DragonForce. However final week, SLSH introduced on its Telegram channel the discharge of their very own ransomware-as-a-service operation referred to as ShinySp1d3r.
The person liable for releasing the ShinySp1d3r ransomware providing is a core SLSH member who goes by the deal with “Rey” and who’s presently one in all simply three directors of the SLSH Telegram channel. Beforehand, Rey was an administrator of the information leak web site for Hellcat, a ransomware group that surfaced in late 2024 and was concerned in assaults on firms together with Schneider Electrical, Telefonica, and Orange Romania.
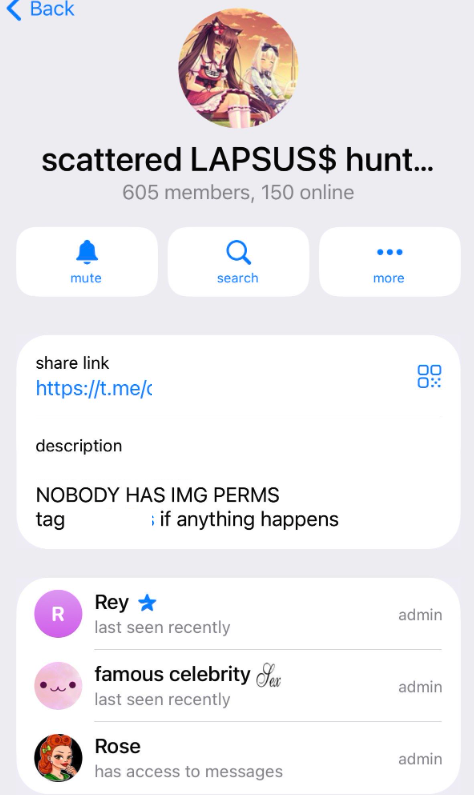
A current, barely redacted screenshot of the Scattered LAPSUS$ Hunters Telegram channel description, exhibiting Rey as one in all three directors.
Additionally in 2024, Rey would take over as administrator of the most up-to-date incarnation of BreachForums, an English-language cybercrime discussion board whose domains have been seized on a number of events by the FBI and/or by worldwide authorities. In April 2025, Rey posted on Twitter/X about one other FBI seizure of BreachForums.
On October 5, 2025, the FBI introduced it had as soon as once more seized the domains related to BreachForums, which it described as a serious legal market utilized by ShinyHunters and others to site visitors in stolen information and facilitate extortion.
“This takedown removes entry to a key hub utilized by these actors to monetize intrusions, recruit collaborators, and goal victims throughout a number of sectors,” the FBI stated.
Extremely, Rey would make a sequence of vital operational safety errors final yr that offered a number of avenues to establish and make sure his real-life id and placement. Learn on to study the way it all unraveled for Rey.
WHO IS REY?
In keeping with the cyber intelligence agency Intel 471, Rey was an lively person on numerous BreachForums reincarnations over the previous two years, authoring greater than 200 posts between February 2024 and July 2025. Intel 471 says Rey beforehand used the deal with “Hikki-Chan” on BreachForums, the place their first put up shared information allegedly stolen from the U.S. Facilities for Illness Management and Prevention (CDC).
In that February 2024 put up in regards to the CDC, Hikki-Chan says they could possibly be reached on the Telegram username @wristmug. In Could 2024, @wristmug posted in a Telegram group chat referred to as “Pantifan” a replica of an extortion electronic mail they stated they acquired that included their electronic mail handle and password.
The message that @wristmug reduce and pasted seems to have been a part of an automated electronic mail rip-off that claims it was despatched by a hacker who has compromised your laptop and used your webcam to file a video of you whilst you have been watching porn. These missives threaten to launch the video to all of your contacts until you pay a Bitcoin ransom, they usually sometimes reference an actual password the recipient has used beforehand.
“Noooooo,” the @wristmug account wrote in mock horror after posting a screenshot of the rip-off message. “I have to be achieved guys.”
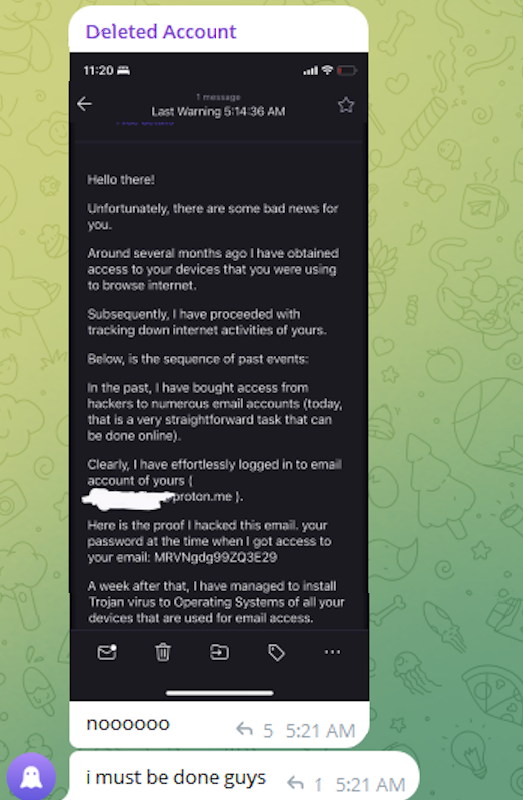
A message posted to Telegram by Rey/@wristmug.
In posting their screenshot, @wristmug redacted the username portion of the e-mail handle referenced within the physique of the rip-off message. Nevertheless, they didn’t redact their previously-used password, they usually left the area portion of their electronic mail handle (@proton.me) seen within the screenshot.
O5TDEV
Looking on @wristmug’s relatively distinctive 15-character password within the breach monitoring service Spycloud finds it’s recognized to have been utilized by only one electronic mail handle: cybero5tdev@proton.me. In keeping with Spycloud, these credentials have been uncovered no less than twice in early 2024 when this person’s gadget was contaminated with an infostealer trojan that siphoned all of its saved usernames, passwords and authentication cookies.
Intel 471 exhibits the e-mail handle cybero5tdev@proton.me belonged to a BreachForums member who glided by the username o5tdev. Looking on this nickname in Google brings up no less than two web site defacement archives exhibiting {that a} person named o5tdev was beforehand concerned in defacing websites with pro-Palestinian messages. The screenshot under, for instance, exhibits that 05tdev was a part of a gaggle referred to as Cyb3r Drag0nz Workforce.

Rey/o5tdev’s defacement pages. Picture: archive.org.
A 2023 report from SentinelOne described Cyb3r Drag0nz Workforce as a hacktivist group with a historical past of launching DDoS assaults and cyber defacements in addition to participating in information leak exercise.
“Cyb3r Drag0nz Workforce claims to have leaked information on over one million of Israeli residents unfold throughout a number of leaks,” SentinelOne reported. “Up to now, the group has launched a number of .RAR archives of purported private info on residents throughout Israel.”
The cyber intelligence agency Flashpoint finds the Telegram person @05tdev was lively in 2023 and early 2024, posting in Arabic on anti-Israel channels like “Ghost of Palestine” [full disclosure: Flashpoint is currently an advertiser on this blog].
‘I’M A GINTY’
Flashpoint exhibits that Rey’s Telegram account (ID7047194296) was significantly lively in a cybercrime-focused channel referred to as Jacuzzi, the place this person shared a number of private particulars, together with that their father was an airline pilot. Rey claimed in 2024 to be 15 years previous, and to have household connections to Eire.
Particularly, Rey talked about in a number of Telegram chats that he had Irish heritage, even posting a graphic that exhibits the prevalence of the surname “Ginty.”
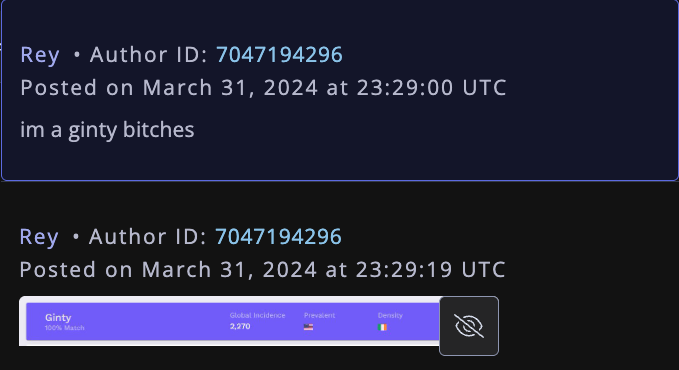
Rey, on Telegram claiming to have affiliation to the surname “Ginty.” Picture: Flashpoint.
Spycloud listed tons of of credentials stolen from cybero5dev@proton.me, and people particulars point out that Rey’s laptop is a shared Microsoft Home windows gadget situated in Amman, Jordan. The credential information stolen from Rey in early 2024 present there are a number of customers of the contaminated PC, however that each one shared the identical final identify of Khader and an handle in Amman, Jordan.
The “autofill” information lifted from Rey’s household PC accommodates an entry for a 46-year-old Zaid Khader that claims his mom’s maiden identify was Ginty. The infostealer information additionally exhibits Zaid Khader often accessed inner web sites for workers of Royal Jordanian Airways.
MEET SAIF
The infostealer information makes clear that Rey’s full identify is Saif Al-Din Khader. Having no luck contacting Saif instantly, KrebsOnSecurity despatched an electronic mail to his father Zaid. The message invited the daddy to reply through electronic mail, telephone or Sign, explaining that his son gave the impression to be deeply enmeshed in a critical cybercrime conspiracy.
Lower than two hours later, I acquired a Sign message from Saif, who stated his dad suspected the e-mail was a rip-off and had forwarded it to him.
“I noticed your electronic mail, sadly I don’t assume my dad would reply to this as a result of they assume its some ‘rip-off electronic mail,’” stated Saif, who advised me he turns 16 years previous subsequent month. “So I made a decision to speak to you instantly.”
Saif defined that he’d already heard from European regulation enforcement officers, and had been attempting to extricate himself from SLSH. When requested why then he was concerned in releasing SLSH’s new ShinySp1d3r ransomware-as-a-service providing, Saif stated he couldn’t simply all of a sudden stop the group.
“Properly I cant simply dip like that, I’m attempting to scrub up every part I’m related to and transfer on,” he stated.

The previous Hellcat ransomware web site. Picture: Kelacyber.com
He additionally shared that ShinySp1d3r is only a rehash of Hellcat ransomware, besides modified with AI instruments. “I gave the supply code of Hellcat ransomware out mainly.”
Saif claims he reached out on his personal just lately to the Telegram account for Operation Endgame, the codename for an ongoing regulation enforcement operation concentrating on cybercrime companies, distributors and their clients.
“I’m already cooperating with regulation enforcement,” Saif stated. “Actually, I’ve been speaking to them since no less than June. I’ve advised them almost every part. I haven’t actually achieved something like breaching right into a corp or extortion associated since September.”
Saif advised {that a} story about him proper now may endanger any additional cooperation he could possibly present. He additionally stated he wasn’t positive if the U.S. or European authorities had been involved with the Jordanian authorities about his involvement with the hacking group.
“A narrative would convey a lot undesirable warmth and would make issues very tough if I’m going to cooperate,” Saif stated. “I’m uncertain whats going to occur they stated they’re involved with a number of international locations concerning my request however its been like a whole week and I obtained no updates from them.”
Saif shared a screenshot that indicated he’d contacted Europol authorities late final month. However he couldn’t identify any regulation enforcement officers he stated have been responding to his inquiries, and KrebsOnSecurity was unable to confirm his claims.
“I don’t actually care I simply need to transfer on from all these items even when its going to be jail time or no matter they gonna say,” Saif stated.










