A complicated AI-generated provide chain assault is focusing on researchers, builders, and safety professionals by means of compromised GitHub repositories, based on findings from Morphisec Menace Labs.
The marketing campaign leverages dormant GitHub accounts and polished, AI-crafted repositories to distribute a beforehand undocumented backdoor generally known as PyStoreRAT.
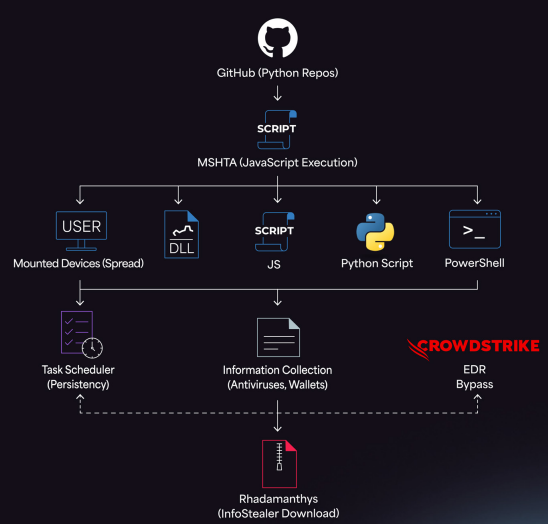
Assault Methodology
The attackers employed a fastidiously orchestrated technique by reactivating dormant GitHub accounts and publishing seemingly respectable repositories that gave the impression to be AI-generated instruments or utilities.
As soon as these repositories gained traction inside the developer neighborhood, risk actors quietly injected the PyStoreRAT backdoor into the codebase, exploiting the belief builders place in established repositories.
This strategy represents an evolution in provide chain assaults, the place adversaries weaponize the open-source ecosystem by creating convincing faux initiatives that originally seem benign.
By focusing on the particular viewers of researchers and builders who ceaselessly obtain and take a look at new instruments, the marketing campaign maximizes its potential impression inside the expertise sector.
PyStoreRAT distinguishes itself from typical malware loaders by means of its refined capabilities.
The backdoor performs complete system profiling to assemble intelligence about contaminated machines earlier than deploying a number of secondary payloads tailor-made to the surroundings.
Notably, PyStoreRAT contains detection logic particularly designed to establish endpoint detection and response (EDR) options akin to CrowdStrike Falcon.
When safety instruments are detected, the malware alters its execution path to evade evaluation and preserve persistence.
The backdoor additionally employs rotating command-and-control (C2) infrastructure, making it considerably tougher for defenders to dam communications and monitor the risk actors.
Morphisec researchers recognized Russian-language indicators inside the malware code and related infrastructure.
The marketing campaign utilized GitHub cluster mapping strategies to establish and goal particular developer communities, suggesting a well-resourced and coordinated operation.
Morphisec has revealed indicators of compromise (IOCs) to help safety groups in detecting and defending towards this risk.
Organizations are suggested to scrutinize GitHub repositories earlier than integrating code, implement enhanced monitoring for suspicious repository exercise, and validate the authenticity of seemingly AI-generated initiatives.
Observe us on Google Information, LinkedIn, and X to Get Prompt Updates and Set GBH as a Most popular Supply in Google.










