Since April 2024, Sednit’s superior improvement staff has reemerged with a contemporary toolkit centered on two paired implants, BeardShell and Covenant, every utilizing a distinct cloud supplier for resilience. This twin‑implant strategy enabled lengthy‑time period surveillance of Ukrainian navy personnel. Apparently, these present toolsets present a direct code lineage to the group’s 2010‑period implants.
Key factors of this blogpost:
- ESET researchers traced the reactivation of Sednit’s superior implant staff to a 2024 case in Ukraine, the place a keylogger named SlimAgent was deployed.
- SlimAgent code was derived from Xagent, Sednit’s flagship backdoor from the 2010s.
- Throughout that operation, BeardShell, a second Sednit‑developed implant, was deployed. It executes PowerShell instructions by way of a legit cloud supplier used as its C&C channel.
- BeardShell makes use of a particular obfuscation method additionally present in Xtunnel, Sednit’s community‑pivoting device from the 2010s.
- Throughout 2025 and 2026, Sednit repeatedly deployed BeardShell along with Covenant, a 3rd main piece of its fashionable toolkit.
- Sednit closely reworked this open‑supply implant to help lengthy‑time period espionage and to implement a brand new community protocol based mostly on one more legit cloud supplier.
Sednit profile
The Sednit group – often known as APT28, Fancy Bear, Forest Blizzard, or Sofacy – has been working since not less than 2004. The US Division of Justice named the group as a kind of accountable for the Democratic Nationwide Committee (DNC) hack simply earlier than the 2016 US elections and linked the group to Unit 26165 of the GRU, a Russian Federation intelligence company inside the Foremost Intelligence Directorate of the Russian navy. The group can also be presumed to be behind the hacking of world tv community TV5Monde, the World Anti-Doping Company (WADA) e mail leak, and lots of different incidents.
What turned of Sednit’s superior implant staff?
The Sednit group is arguably one of many APT teams with probably the most spectacular document of compromised targets. Notable amongst its recognized compromises are the German parliament (2015), the French tv community TV5Monde (2015), and the United States Democratic Nationwide Committee (2016).
Throughout these years of high-profile assaults, Sednit relied on an in depth set of customized implants, starting from full-fledged espionage backdoors corresponding to Xagent and Sedreco, to specialised toolkits such because the network-pivoting device Xtunnel and the info stealer for air-gapped machines USBStealer. In 2016, we extensively documented this subtle arsenal in our white paper En Route with Sednit.
Nevertheless, in 2019, a shift occurred. Since then, and till just lately, Sednit’s high-end implants have hardly ever been noticed within the wild (with only some exceptions, such because the Graphite malware documented by Trellix in 2021), whereas the group concurrently ramped up its phishing operations. The customized malware utilized in these phishing assaults consisted largely of straightforward script-based implants. The explanations behind that technical shift stay a thriller to us.
This blogpost paperwork the reappearance of Sednit’s high-end customized arsenal since 2024. Right here we give attention to attributing its fashionable toolsets, as prior publications by CERT-UA and Sekoia have lined their inside workings.
A boutique developer store
Sednit maintains in-house improvement of its espionage implants, a particular trait that helps an attribution strategy based mostly on shared code artifacts.
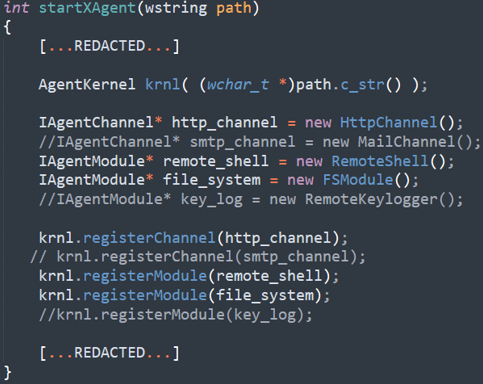
As an instance this functionality, take into account Xagent, the group’s flagship backdoor throughout the 2010s. In 2015, we discovered the Xagent supply code on a Linux server in Ukraine, left in an unprotected archive after the attackers had compiled it. Determine 1 exhibits that plugins and C&C channels had been enabled or disabled by commenting code in or out – chosen per goal in response to operational necessities – leaving little doubt that builders and operators labored in shut coordination.
As well as, the 2018 US DOJ indictment explicitly states that Xagent was developed in-house, accusing particular members of GRU Unit 26165 of being its builders.
On this blogpost, we leverage that improvement footprint as an attribution mechanism. By monitoring shared code artifacts throughout completely different implants, we hyperlink the group’s 2010-era toolsets to these at present in use.
SlimAgent
Our account of contemporary Sednit actions begins with SlimAgent, an espionage implant found on a Ukrainian governmental machine by CERT-UA in April 2024. SlimAgent is an easy but environment friendly spying device able to logging keystrokes, capturing screenshots, and accumulating clipboard knowledge.
Ancestors
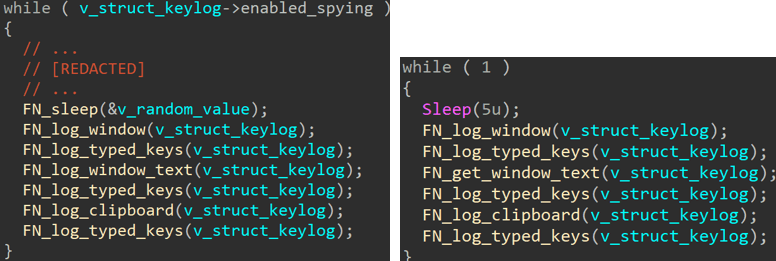
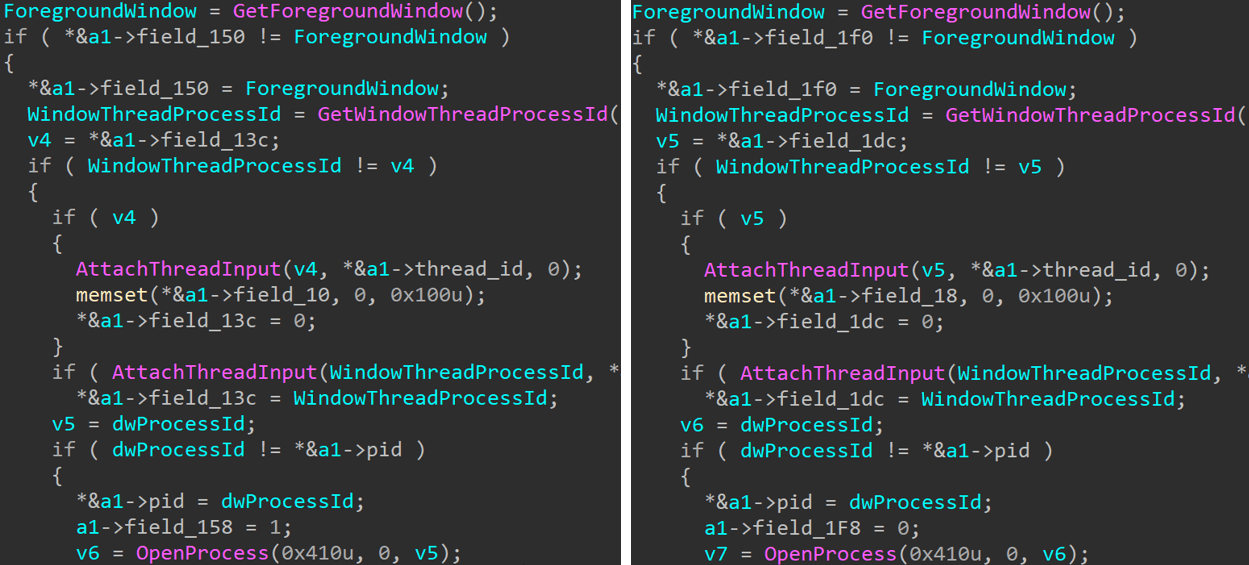
Apparently, we recognized in ESET telemetry beforehand unknown samples with code just like SlimAgent, which had been deployed as early as 2018 – six years earlier than the Ukrainian case – towards governmental entities in two European nations. These samples exhibit robust code-level similarities with SlimAgent, together with an similar six-step data-collection loop, proven in Determine 2. Every step is carried out in a virtually similar method, as illustrated in Determine 3 with the routine accountable for logging the foreground window’s executable; the one variations lie within the format of the interior knowledge constructions.
SlimAgent contains a number of options that had been absent from the 2018 samples, corresponding to encryption of the collected logs. However, it’s outstanding that samples deployed six years aside exhibit such robust code similarities.
We subsequently assess with excessive confidence that each the 2018 samples and the 2024 SlimAgent pattern had been constructed from the identical codebase. The remaining query is: the place did the 2018 samples originate?
An notorious lineage
The 2018 samples have an inside title that will resonate with fellow analysts: RemoteKeyLogger.dll. That is the title of the keylogging module of Xagent, Sednit’s flagship espionage backdoor from 2012 to 2018 (documented in our white paper En Route with Sednit).
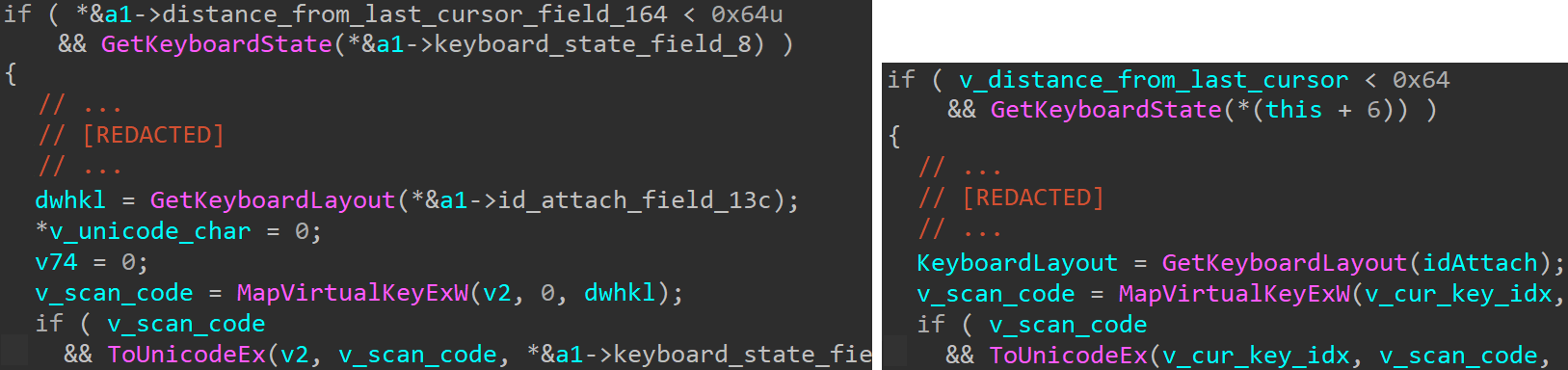
Digging into some outdated Xagent samples (e.g., SHA-1: D0DB619A7A160949528D46D20FC0151BF9775C32), we had been certainly capable of finding some hanging similarities, such because the one proven in Determine 4. On this code, the keylogging logic is executed provided that the mouse cursor has not moved greater than 10 pixels (by evaluating the sq. of the gap between the final and the present place with 0x64, i.e., 100), and it’s carried out with the identical API calls.
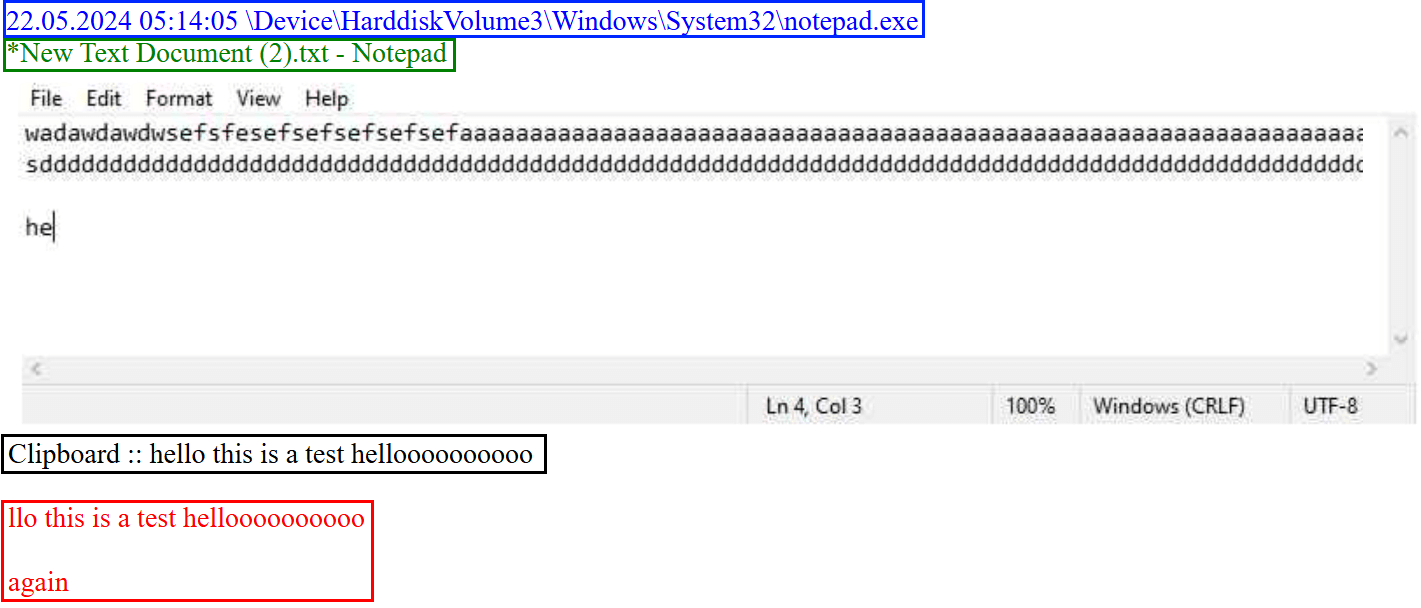
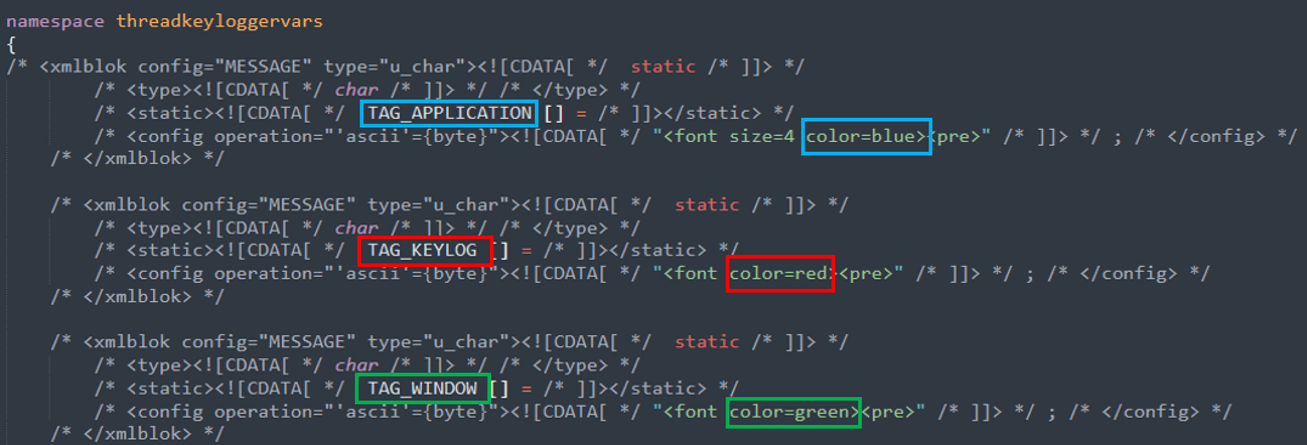
As one other instance, SlimAgent emits its espionage logs within the HTML format, with the applying title, the logged keystrokes, and the window title in blue, crimson, and inexperienced, respectively. Determine 5 exhibits an instance generated whereas typing and copying textual content in a newly created TXT file utilizing notepad.exe. The Xagent keylogger additionally produces HTML logs utilizing the identical coloration scheme. That is illustrated in Determine 6 with the definition of the corresponding coloration HTML tags within the 2015 Xagent supply code.
Based mostly on these similarities, we consider that SlimAgent is an evolution of the Xagent keylogger module, which has been deployed as a standalone element since not less than 2018. Furthermore, as a result of Xagent is a customized toolset used solely by the Sednit group for greater than six years, we attribute SlimAgent to Sednit with excessive confidence.
This raises a query: why would Sednit reuse an implant derived from such a widely known codebase? One attainable clarification is diminished improvement capability. Nevertheless, SlimAgent was not the one implant discovered on the Ukrainian machine in 2024; BeardShell – a way more current addition to Sednit’s customized arsenal – was deployed there as effectively.
BeardShell
BeardShell is a classy implant able to executing PowerShell instructions inside a .NET runtime surroundings, whereas leveraging the legit cloud storage service Icedrive as its C&C channel.
This element bears the marks of intense improvement efforts and is the first motive we consider that Sednit’s superior improvement staff is as soon as once more energetic. For instance, as a result of Icedrive doesn’t present a publicly documented API, the builders reimplemented the requests made by the official Icedrive shopper. Every time adjustments to Icedrive’s personal API disrupt BeardShell communications, Sednit builders produce an up to date model inside hours to revive entry.
A mathematical blast from the previous
Whereas we couldn’t discover different malware households straight associated to BeardShell, we uncovered a stunning similarity with previous Sednit tooling, beginning with a C++ static initializer executed on the very begin of BeardShell. This routine’s objective, whose code is proven in Determine 7, is to decrypt the authentication token for the Icedrive cloud storage.
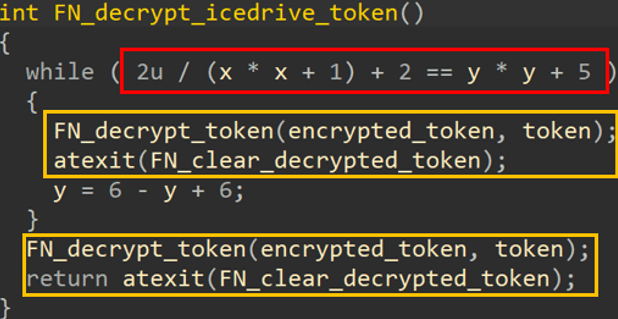
The routine accommodates a textbook instance of the obfuscation method generally known as opaque predicate insertion (highlighted within the crimson field in Determine 7):
- An arithmetic expression evaluating to zero for all attainable inputs – named x and y in Determine 7 – is used as a situation for a whereas loop. In observe, the loop physique is rarely executed, as a result of the predicate 2 (x2 + 1) + 2 = y2 + 5 has no integer resolution.
- The physique of this synthetic loop consists of two authentic directions (proven within the yellow field in Determine 7), plus a dummy replace of the enter variable y to imitate an actual loop physique construction.
- Following the faux loop are the 2 authentic directions that might be executed: a name to the Icedrive token decryption routine and the registration of a cleaner routine.
Opaque predicates are usually used to hinder static evaluation however should not notably helpful in such a small routine. Word that different BeardShell static initializers – which aren’t dealing with vital knowledge – are protected with the identical method, so evidently the builders merely utilized the safety to all of them indiscriminately.
Now, the predicate method might be simplified as (by subtracting 2 on each side) 2 (x2 + 1) = y2 + 3 . Apparently, that identical opaque predicate was utilized in Xtunnel, a network-pivoting device used solely by Sednit, from 2013 to 2016, and documented in our white paper En Route with Sednit. Determine 8 exhibits an instance of obfuscated code from Xtunnel (SHA-1: 99B454262DC26B081600E844371982A49D334E5E), with an if assertion whose predicate can’t be true.
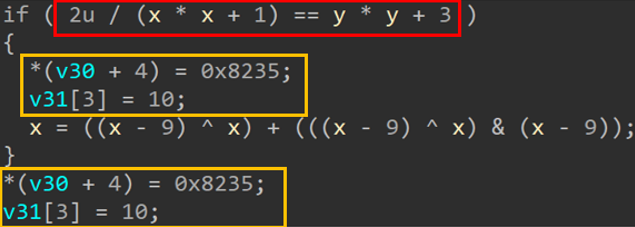
Not solely is the predicate similar to the one utilized in BeardShell, however the never-executed block is constructed in a similar way, by duplicating the 2 authentic directions (within the yellow field) and doing a dummy replace of one of many predicate inputs (right here, x).
To the perfect of our data, this opaque predicate has not been noticed anyplace else besides in Xtunnel. One would possibly even surprise if it couldn’t have been used as a false flag, particularly because it was publicly talked about as being distinctive to Xtunnel, for instance in a BlackHat Europe 2016 presentation. However, a false flag operation would have doubtless used the similar predicate, not the variant with +2 on each side of the equation.
The shared use of this uncommon obfuscation method, mixed with its co‑location with SlimAgent, leads us to evaluate with excessive confidence that BeardShell is a part of Sednit’s customized arsenal.
Because the preliminary 2024 case, Sednit has continued deploying BeardShell by way of 2025 and into 2026, primarily in long-term espionage operations focusing on Ukrainian navy personnel. To take care of persistent entry to those high-value targets, Sednit systematically deploys one other implant alongside BeardShell: Covenant, the ultimate element of its fashionable arsenal.
Covenant
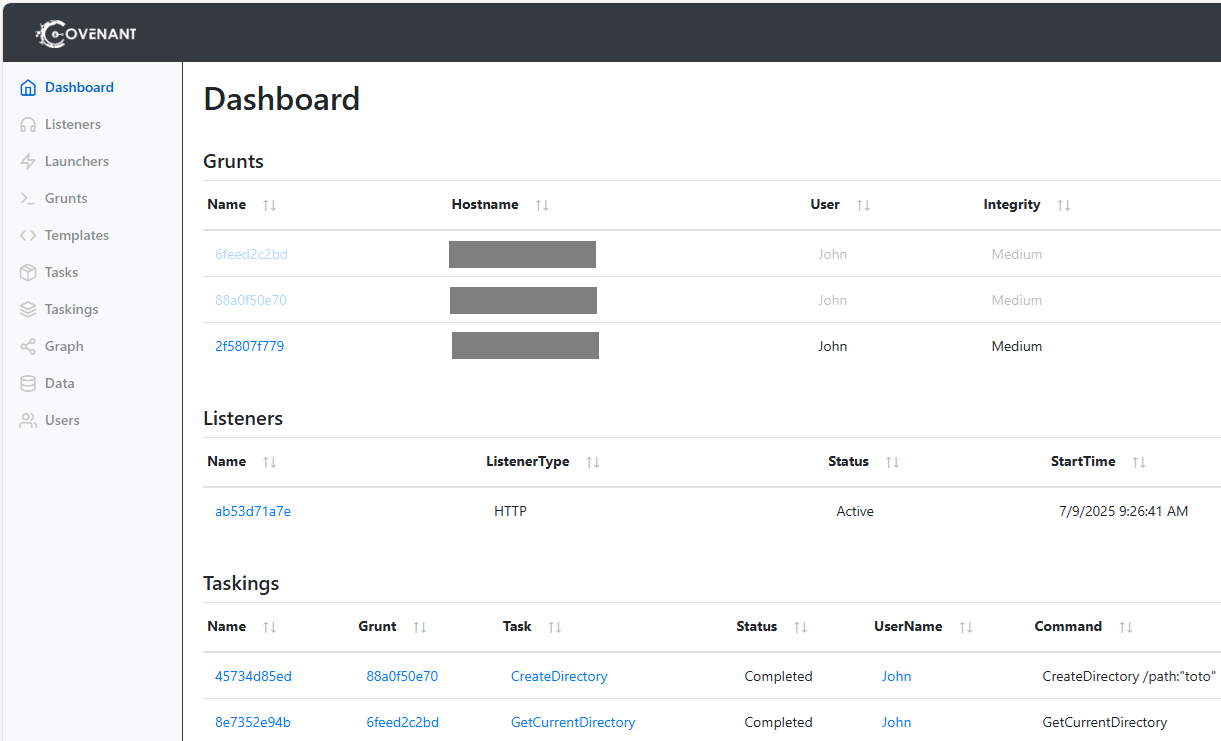
Covenant is an open-source .NET submit exploitation framework first launched in February 2019. It permits the creation and administration of .NET implants by way of a web-based dashboard – see the instance in Determine 9 – and offers over 90 built-in duties, supporting capabilities corresponding to knowledge exfiltration, goal monitoring, and community pivoting.
Since 2023, Sednit builders have made quite a few modifications and experiments with Covenant to determine it as their main espionage implant, maintaining BeardShell primarily as a fallback in case Covenant encounters operational points, such because the takedown of its cloud-based infrastructure.
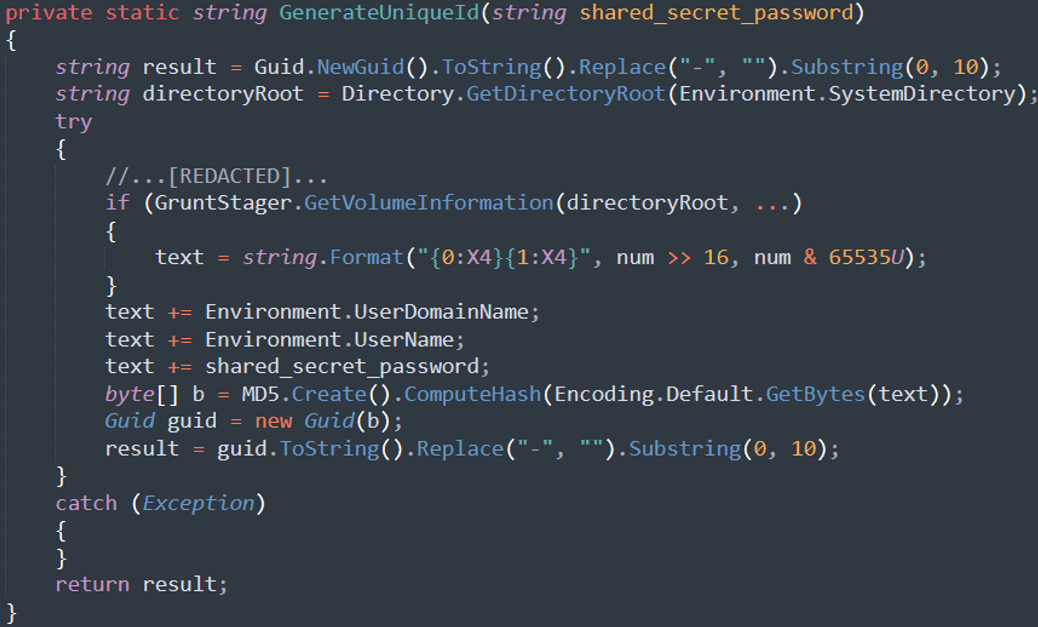
For instance, Sednit changed Covenant’s authentic implant name-generation mechanism with a deterministic methodology (see Determine 10), producing identifiers derived from machine traits quite than producing a brand new random worth at every execution (see the Identify column within the Grunts part in Determine 9). This modification illustrates how Sednit tailored Covenant for long-term espionage quite than for short-term, post-exploitation exercise: in lengthy‑working operations, having the identical machine seem underneath completely different identifiers after every reboot would muddle the dashboard and cut back operational effectivity.
Sednit additionally modified Covenant’s execution move, which is a two-stage implant, most likely to keep away from behavioral detection. As a substitute of getting the first-stage downloader invoke the primary methodology of the second-stage .NET meeting utilizing a hard and fast index (as initially carried out), they launched a DisplayName attribute and iterated over methodology attributes to search out the entry level. In early 2023 variants, Sednit builders even experimented with embedding each phases right into a single binary.
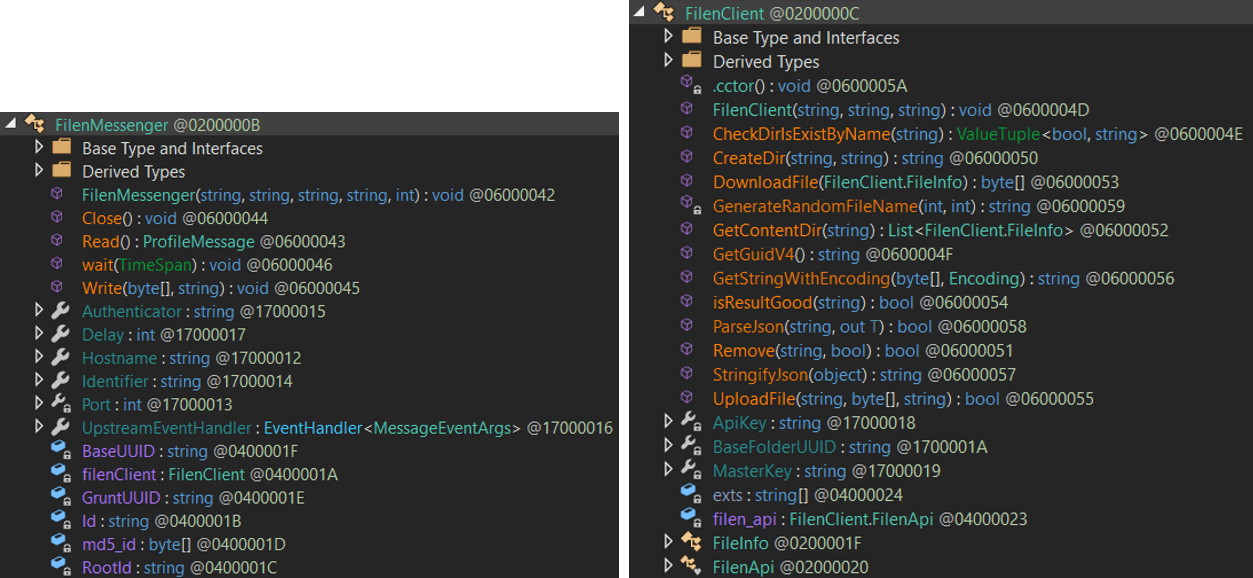
Covenant formally helps solely HTTP and SMB, which ends up in Sednit’s most important Covenant modification: the addition of a cloud-based community protocol. To attain this, Sednit builders leveraged the C2Bridge venture, a standalone framework created by Covenant’s authentic writer to facilitate integration of recent communication protocols. With C2Bridge, builders want solely implement a category conforming to the IMessenger interface on the implant facet, offering Learn and Write strategies to handle low-level communications. C2Bridge can then run as a standalone element on the controller to relay messages, whereas new implants created by the controller use the carried out communication strategies.
Determine 11 exhibits the courses launched by Sednit builders to speak with the Filen cloud supplier, used since July 2025. The FilenMessenger class implements IMessenger and depends on FilenClient to work together with the Filen API. Beforehand, in 2023, Sednit’s Covenant abused the legit cloud service pCloud, and in 2024–2025, Koofr, utilizing related implementations.
These variations present that Sednit builders acquired deep experience in Covenant – an implant whose official improvement ceased in April 2021 and will have been thought of unused by defenders. This stunning operational alternative seems to have paid off: Sednit has efficiently relied on Covenant for a number of years, notably towards chosen targets in Ukraine. For example, in 2025, our evaluation of Sednit-controlled Covenant cloud drives revealed machines that had been monitored for greater than six months. In January 2026, Sednit additionally deployed Covenant in a collection of spearphishing campaigns exploiting the CVE-2026-21509 vulnerability, as reported by CERT‑UA.
Conclusion
On this blogpost, we have now proven that Sednit’s superior improvement staff is energetic as soon as once more, working an arsenal centered on two implants – BeardShell and Covenant – deployed in tandem and every leveraging a distinct cloud supplier. This setup permits operators to reestablish entry shortly if the infrastructure for one is taken down. We consider that this dual-implant technique isn’t new. For instance, within the 2021 marketing campaign documented by Trellix, Sednit deployed two implants in parallel: Graphite, which used OneDrive as its C&C channel, and PowerShell Empire, which relied on separate devoted infrastructure.
The sophistication of BeardShell and the intensive modifications made to Covenant display that Sednit’s builders stay absolutely able to producing superior customized implants. Moreover, the shared code and methods linking these instruments to their 2010-era predecessors strongly counsel continuity inside the improvement staff.
This raises the query of what these builders had been doing throughout all these years, when the safety group primarily noticed phishing exercise from Sednit. One chance is that superior improvement efforts had been reactivated following the Russian invasion of Ukraine. One other is that they by no means stopped working, however as an alternative turned extra cautious.
For any inquiries about our analysis revealed on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Analysis gives personal APT intelligence experiences and knowledge feeds. For any inquiries about this service, go to the ESET Menace Intelligence web page.
IoCs
Recordsdata
A complete record of indicators of compromise (IoCs) and samples might be present in our GitHub repository.
| SHA-1 | Filename | Detection | Description |
| 5603E99151F8803C13D4 |
eapphost.dll | Win64/Spy.KeyLogger.LS | SlimAgent. |
| 6D39F49AA11CE0574D58 |
tcpiphlpsvc.dll | Win64/BeardShell.A | BeardShell. |
MITRE ATT&CK methods
This desk was constructed utilizing model 18 of the MITRE ATT&CK framework.
| Tactic | ID | Identify | Description |
| Useful resource Growth | T1583.006 | Purchase Infrastructure: Internet Companies | BeardShell depends on Icedrive cloud storage. Covenant depends on Filen cloud storage. |
| T1587.001 | Develop Capabilities: Malware | BeardShell and SlimAgent are customized malware. | |
| Execution | T1059.001 | Command and Scripting Interpreter: PowerShell | BeardShell executes PowerShell instructions. |
| T1129 | Shared Modules | BeardShell and SlimAgent are full-fledged DLL recordsdata. | |
| Privilege Escalation | T1546.015 | Occasion Triggered Execution: Element Object Mannequin Hijacking | BeardShell and SlimAgent are made persistent by hijacking COM objects. |
| Protection Evasion | T1027 | Obfuscated Recordsdata or Data | BeardShell Icedrive token decryption is obfuscated. |
| T1140 | Deobfuscate/Decode Recordsdata or Data | BeardShell decrypts its strings. | |
| T1480 | Execution Guardrails | BeardShell solely executes in taskhost.exe or taskhostw.exe. SlimAgent solely executes in explorer.exe. |
|
| T1564 | Disguise Artifacts | SlimAgent logs are written right into a hidden file. | |
| Discovery | T1082 | System Data Discovery | BeardShell sends a fingerprint of the compromised machine. |
| Assortment | T1005 | Knowledge from Native System | BeardShell, Covenant, and SlimAgent acquire knowledge from a compromised machine. |
| T1056.001 | Enter Seize: Keylogging | SlimAgent performs keylogging. | |
| T1113 | Display Seize | SlimAgent captures screenshots of the compromised machine. | |
| T1115 | Clipboard Knowledge | SlimAgent collects clipboard knowledge. | |
| Command and Management | T1001 | Knowledge Obfuscation | BeardShell exfiltrates knowledge in faux photos. |
| T1071.001 | Utility Layer Protocol: Internet Protocols | BeardShell and Covenant use HTTPS for C&C. | |
| T1102 | Internet Service | BeardShell will get instructions from Icedrive. Covenant will get instructions from Filen. |
|
| T1573.002 | Encrypted Channel: Uneven Cryptography | BeardShell communications with Icedrive are encrypted utilizing HTTPS. Covenant communications with its controller makes use of RSA-encrypted session keys. |
|
| Exfiltration | T1567 | Exfiltration Over Internet Service | BeardShell exfiltrates knowledge to Icedrive. Covenant exfiltrates knowledge to Filen. |











