A financially motivated information theft and extortion group is trying to inject itself into the Iran warfare, unleashing a worm that spreads by poorly secured cloud companies and wipes information on contaminated techniques that use Iran’s time zone or have Farsi set because the default language.
Specialists say the wiper marketing campaign towards Iran materialized this previous weekend and got here from a comparatively new cybercrime group referred to as TeamPCP. In December 2025, the group started compromising company cloud environments utilizing a self-propagating worm that went after uncovered Docker APIs, Kubernetes clusters, Redis servers, and the React2Shell vulnerability. TeamPCP then tried to maneuver laterally by sufferer networks, siphoning authentication credentials and extorting victims over Telegram.

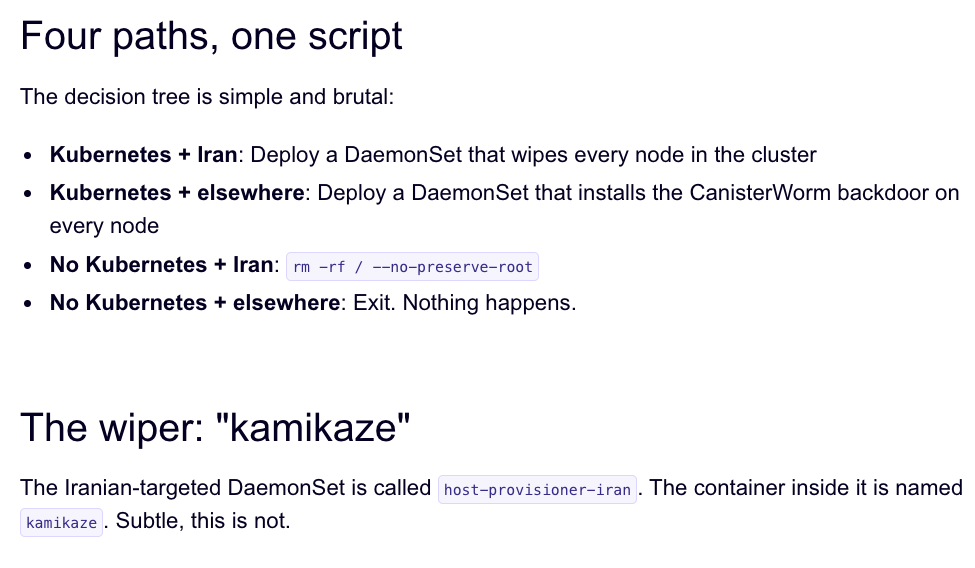
A snippet of the malicious CanisterWorm that seeks out and destroys information on techniques that match Iran’s timezone or have Farsi because the default language. Picture: Aikido.dev.
In a profile of TeamPCP printed in January, the safety agency Flare stated the group weaponizes uncovered management planes moderately than exploiting endpoints, predominantly focusing on cloud infrastructure over end-user gadgets, with Azure (61%) and AWS (36%) accounting for 97% of compromised servers.
“TeamPCP’s power doesn’t come from novel exploits or authentic malware, however from the large-scale automation and integration of well-known assault methods,” Flare’s Assaf Morag wrote. “The group industrializes current vulnerabilities, misconfigurations, and recycled tooling right into a cloud-native exploitation platform that turns uncovered infrastructure right into a self-propagating prison ecosystem.”
On March 19, TeamPCP executed a provide chain assault towards the vulnerability scanner Trivy from Aqua Safety, injecting credential-stealing malware into official releases on GitHub actions. Aqua Safety stated it has since eliminated the dangerous information, however the safety agency Wiz notes the attackers had been in a position to publish malicious variations that snarfed SSH keys, cloud credentials, Kubernetes tokens and cryptocurrency wallets from customers.
Over the weekend, the identical technical infrastructure TeamPCP used within the Trivy assault was leveraged to deploy a brand new malicious payload which executes a wiper assault if the person’s timezone and locale are decided to correspond to Iran, stated Charlie Eriksen, a safety researcher at Aikido. In a weblog put up printed on Sunday, Eriksen stated if the wiper part detects that the sufferer is in Iran and has entry to a Kubernetes cluster, it would destroy information on each node in that cluster.
“If it doesn’t it would simply wipe the native machine,” Eriksen informed KrebsOnSecurity.
Picture: Aikido.dev.
Aikido refers to TeamPCP’s infrastructure as “CanisterWorm” as a result of the group orchestrates their campaigns utilizing an Web Pc Protocol (ICP) canister — a system of tamperproof, blockchain-based “good contracts” that mix each code and information. ICP canisters can serve Internet content material on to guests, and their distributed structure makes them immune to takedown makes an attempt. These canisters will stay reachable as long as their operators proceed to pay digital foreign money charges to maintain them on-line.
Eriksen stated the individuals behind TeamPCP are bragging about their exploits in a gaggle on Telegram and declare to have used the worm to steal huge quantities of delicate information from main corporations, together with a big multinational pharmaceutical agency.
“After they compromised Aqua a second time, they took lots of GitHub accounts and began spamming these with junk messages,” Eriksen stated. “It was nearly like they had been simply displaying off how a lot entry they’d. Clearly, they’ve a whole stash of those credentials, and what we’ve seen to this point might be a small pattern of what they’ve.”
Safety specialists say the spammed GitHub messages might be a means for TeamPCP to make sure that any code packages tainted with their malware will stay distinguished in GitHub searches. In a e-newsletter printed right this moment titled GitHub is Beginning to Have a Actual Malware Downside, Dangerous Enterprise reporter Catalin Cimpanu writes that attackers usually are seen pushing meaningless commits to their repos or utilizing on-line companies that promote GitHub stars and “likes” to maintain malicious packages on the high of the GitHub search web page.
This weekend’s outbreak is the second main provide chain assault involving Trivy in as many months. On the finish of February, Trivy was hit as a part of an automatic menace referred to as HackerBot-Claw, which mass exploited misconfigured workflows in GitHub Actions to steal authentication tokens.
Eriksen stated it seems TeamPCP used entry gained within the first assault on Aqua Safety to perpetrate this weekend’s mischief. However he stated there is no such thing as a dependable method to inform whether or not TeamPCP’s wiper truly succeeded in trashing any information from sufferer techniques, and that the malicious payload was solely lively for a short while over the weekend.
“They’ve been taking [the malicious code] up and down, quickly altering it including new options,” Eriksen stated, noting that when the malicious canister wasn’t serving up malware downloads it was pointing guests to a Rick Roll video on YouTube.
“It’s a bit of everywhere, and there’s an opportunity this complete Iran factor is simply their means of getting consideration,” Eriksen stated. “I really feel like these individuals are actually taking part in this Chaotic Evil position right here.”
Cimpanu noticed that provide chain assaults have elevated in frequency of late as menace actors start to understand simply how environment friendly they are often, and his put up paperwork an alarming variety of these incidents since 2024.
“Whereas safety companies seem like doing an excellent job recognizing this, we’re additionally gonna want GitHub’s safety workforce to step up,” Cimpanu wrote. “Sadly, on a platform designed to repeat (fork) a challenge and create new variations of it (clones), recognizing malicious additions to clones of reliable repos may be fairly the engineering downside to repair.”
Replace, 2:40 p.m. ET: Wiz is reporting that TeamPCP additionally pushed credential stealing malware to the KICS vulnerability scanner from Checkmarx, and that the scanner’s GitHub Motion was compromised between 12:58 and 16:50 UTC right this moment (March twenty third).










