Hackers have discovered a brand new option to exploit the software program world, and this time, they’re utilizing our personal belief in opposition to us. Researchers at Sonatype have simply caught a nasty marketing campaign the place official developer accounts have been hijacked to unfold malicious code. This wasn’t only a random particular person making a faux app; it seems to be like a focused takeover of established creators to inject tampered instruments into the system with out anybody noticing.
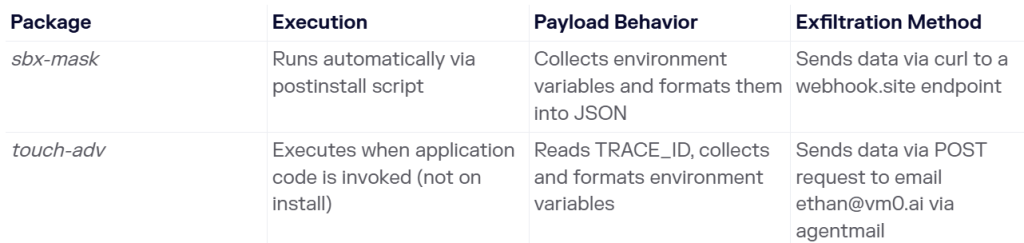
In a report shared with Hackread.com, the agency recognized two harmful packages named sbx-mask and touch-adv. These have been quietly revealed to the npm registry (an enormous library of code utilized by thousands and thousands) to behave as a digital backdoor right into a developer’s machine.
Researchers discovered that these two packages have been basically programmed to behave like credential stealers. As soon as they get onto a pc, they hunt for “surroundings variables,” that are hidden areas the place a pc shops its most non-public keys, like passwords, API tokens, and login credentials for cloud companies.
The 2 threats, which Sonatype is monitoring beneath the codes Sonatype-2026-001275 and Sonatype-2026-001276, didn’t behave the identical approach. The sbx-mask package deal was daring; it triggered its theft the second it was downloaded. However, touch-adv was extra undercover. It stayed quiet till the developer really began utilizing the software program, making it a lot tougher to identify throughout a fast scan.
Additional investigation revealed a really clear path of the place the stolen secrets and techniques have been being despatched. The malware was caught directing knowledge to a selected e-mail handle, [email protected], and utilizing a device known as a webhook to maneuver the knowledge out.
As quickly because the crew realised what was taking place, they moved quick and reported it to GitHub’s Safety Incident Response Group on March 19, 2026. Whereas the damaging recordsdata have since been kicked off the general public platform, they could nonetheless be sitting within the non-public folders of any developer who downloaded them not too long ago.
This reveals that avoiding unknown apps may not be sufficient, even trusted builders can be utilized to unfold malicious code. When you put in these packages, change your passwords and examine for uncommon community exercise instantly.