A current investigation as uncovered how a suspected North Korean IT employee allegedly used a stolen identification, AI-generated resume content material, and scripted interview solutions to attempt to safe a senior distant position at U.S.-based menace intelligence agency Nisos.
The case highlights how DPRK IT employment schemes are evolving by combining conventional fraud with fashionable AI and distant entry applied sciences.
He used stolen personally identifiable data (PII), a newly created e-mail deal with, and a VoIP telephone quantity designed to match the claimed U.S. location.
In accordance with Nisos, the person utilized in June 2025 for a Lead AI Architect position, posing as a Florida-based senior full stack developer and AI specialist.
Community indicators tied the applicant to IP addresses believed to belong to the Astrill VPN anonymization community, a service beforehand linked to North Korean distant IT employee exercise.
Investigators decided the resume was doubtless generated or closely assisted by an AI chatbot.
AI-Generated Resume
The doc mirrored the employer’s personal job description, repeating lengthy lists of expertise and applied sciences, together with programming languages, agentic AI instruments, cloud platforms, databases, and OSINT tooling, immediately lifted from the posting.
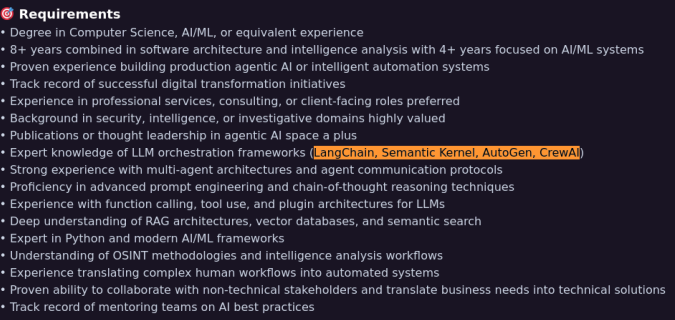
The abstract part additionally reused language about researching and evaluating rising agentic AI applied sciences, suggesting automated content material creation reasonably than genuine expertise.
In the course of the digital interview, Nisos analysts suspected the candidate was counting on an AI chatbot to reply questions in actual time.
The operative continuously regarded away from the digital camera and repeatedly started solutions with the phrase “How can I say?”, showing to attend for scripted responses.
When interviewers requested a faux query a couple of current “hurricane George” in Florida a non-existent occasion the candidate nonetheless tried to reply, reinforcing suspicions that he was studying generic AI-generated textual content reasonably than talking from private expertise.
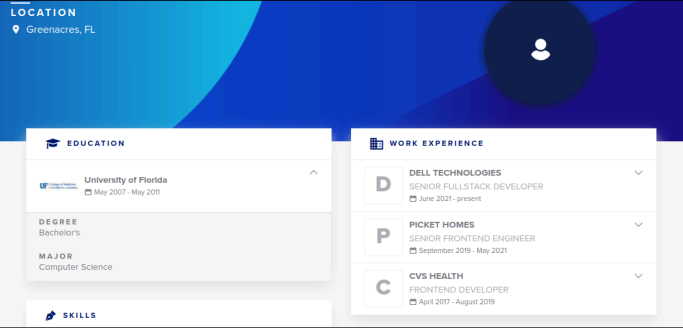
Pre-employment OSINT uncovered three completely different resume platform profiles tied to the identical identify however with inconsistent places, universities, and employment histories.
All profiles appeared to reference the actual addresses of an precise Florida resident, indicating that the operative had doubtless stolen that individual’s identification.
Nisos’ investigation confirmed the community had looked for details about this actual particular person and later coordinated sufferer notification with regulation enforcement.
Nisos shipped a company laptop computer to the deal with offered by the applicant, which differed from the deal with on the resume a sample frequent in DPRK workforce fraud.
As soon as activated, monitoring confirmed the machine stayed at that location, and the built-in digital camera revealed a “laptop computer farm” setup inside a closet containing quite a few laptops.
Entry to the machine uncovered Raspberry Pi–primarily based PiKVM {hardware} used for stealthy keyboard-video-mouse management, permitting distant operators to handle a number of company machines as if bodily current, whereas evading typical endpoint detection mechanisms.
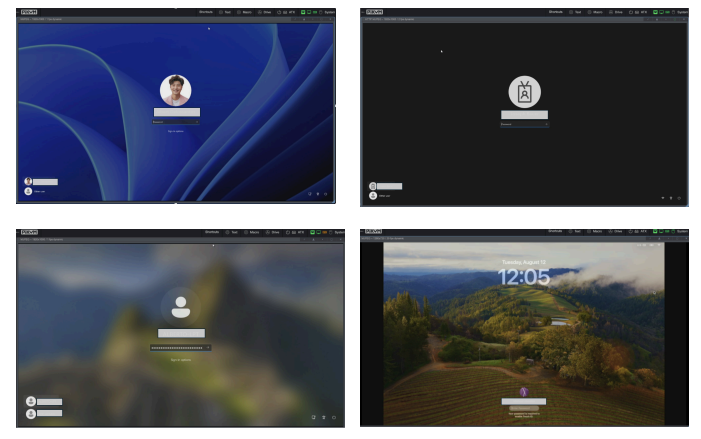
laptop computer farm (Supply : Nisos).
The community additionally used Tailscale, a mesh VPN service, to construct an encrypted non-public community amongst these gadgets, enabling distant command execution and information exfiltration over point-to-point connections.
Nisos recognized round 40 gadgets on the community, with roughly 20 believed to be a part of the laptop computer farm, every tied to completely different worker identities at completely different firms.
Researchers warn that this mannequin permits DPRK IT employees to covertly earn overseas forex and achieve entry to delicate company information worldwide.
Nisos stresses that firms ought to strengthen distant hiring controls with pre-employment OSINT screening, verification of identities and portfolios, and deeper technical interviews that may expose scripted or AI-assisted solutions.
With out these measures, organizations danger unknowingly onboarding DPRK-linked contractors, creating openings for mental property theft, information breaches, and regulatory publicity.
Observe us on Google Information, LinkedIn, and X to Get Immediate Updates and Set GBH as a Most popular Supply in Google.










