Since not less than late 2023, a gaggle of hackers referred to as REF1695 has been working a quiet however extremely worthwhile cryptomining operation by hiding malware inside pretend software program installers. In line with Elastic Safety Labs, which found the rip-off, these hackers aren’t in search of a fast payday, and their system is constructed to remain in your pc for months, hiding in plain sight whereas draining your processing energy for his or her achieve.
The Non-Revenue Lure
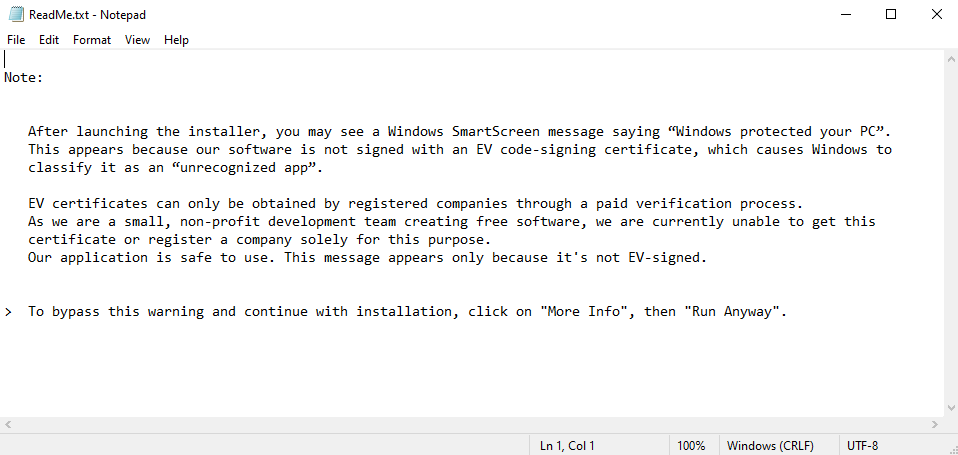
The rip-off normally begins with a pretend obtain, usually an ISO file. To dodge safety checks, the hackers embody a ReadMe.txt file that makes use of social engineering. It claims the software program is from a small non-profit crew of builders that may’t afford official Home windows certificates and is offering the software program at no cost. They speak the person via bypassing SmartScreen by clicking Extra Information and Run Anyway.
Nevertheless, as an alternative of the promised software program, a collection of loaders installs a malicious toolkit together with CNB Bot, PureRAT, and SilentCryptoMiner. These instruments give the hackers full distant entry to your information, the flexibility to replace their malicious code, and the ability to hijack your pc’s {hardware} for cryptocurrency mining.
A Sport of Cover and Search
This assault is intelligent due to how arduous it tries to remain invisible, researchers defined of their weblog submit. whereas noticing that the malware always displays the sufferer’s system for 35 completely different safety instruments, from the fundamental Process Supervisor to skilled software program like Wireshark.
If you happen to open considered one of these, maybe as a result of your PC feels sluggish, the malware immediately kills the mining course of. Your pc’s efficiency returns to regular, leaving you with nothing to search out. When you shut the device, the miner quietly restarts.
Turning Your PC Right into a Money Cow
The hackers monetize your {hardware} in two major methods. Via cryptojacking, they use a driver known as WinRing0x64.sys to get deep entry to your processor, permitting them to mine Monero (XMR) a lot sooner. By extracting information from the malware and monitoring public mining dashboards, researchers discovered 4 particular wallets which have already collected over 27.88 Monero (roughly $9,400).
Secondly, victims are tricked into CPA (Price Per Motion) fraud, the place they need to full surveys or join trials to unlock a registration key, incomes the hackers a fee for each sign-up.
Staying Underneath the Radar
To remain hidden, the group hosts malicious information on trusted platforms like GitHub and makes use of high-level RSA-2048 encryption to regulate their bots. This implies even when specialists discover the management panel, they’ll’t simply shut it down.
The very best safety towards this menace is to keep away from unofficial installers and cracked software program. If a obtain asks you to manually disable security measures, it’s nearly actually a entice.