Anthropic not too long ago unveiled Claude Mythos Preview, a groundbreaking general-purpose language mannequin demonstrating an unprecedented, emergent potential to autonomously uncover and exploit zero-day vulnerabilities.
In response to those highly effective capabilities, the corporate launched Challenge Glasswing, a coordinated defensive initiative aimed toward securing essential software program infrastructure earlier than cyberattackers can leverage related instruments.
This launch marks a watershed second for the cybersecurity business, showcasing an AI able to unearthing and weaponizing deeply hidden flaws throughout main working programs and net browsers.
Throughout intensive testing, Mythos Preview efficiently recognized delicate bugs which have evaded human researchers and fashionable fuzzing instruments for many years.
Anthropic researchers highlighted a 27-year-old denial-of-service vulnerability found in OpenBSD’s TCP SACK implementation.
By exploiting a signed integer overflow mixed with a null pointer dereference, the mannequin crafted an assault able to crashing any responding OpenBSD host.
Moreover, the AI uncovered a 16-year-old out-of-bounds write vulnerability in FFmpeg’s broadly used H.264 codec.
This particular flaw stemmed from a padding entry mismatch launched throughout a 2010 code refactor and had bypassed intensive fuzzing efforts till now.
Shifting past mere vulnerability discovery, Mythos Preview excels at turning theoretical bugs into totally useful exploits with out human intervention.
The mannequin autonomously achieved distant code execution on FreeBSD by exploiting a 17-year-old vulnerability tracked as CVE-2026-4747.
By concentrating on a stack buffer overflow within the Community File System server, the AI intelligently bypassed authentication checks and break up a fancy Return-Oriented Programming chain throughout a number of community packets to achieve full root entry.
Moreover, the mannequin independently developed native privilege escalation exploits for the Linux kernel.
It efficiently bypassed customary defense-in-depth measures, corresponding to Kernel Tackle House Format Randomization, by chaining learn vulnerabilities with out-of-bounds write exploits to attain full system takeover.
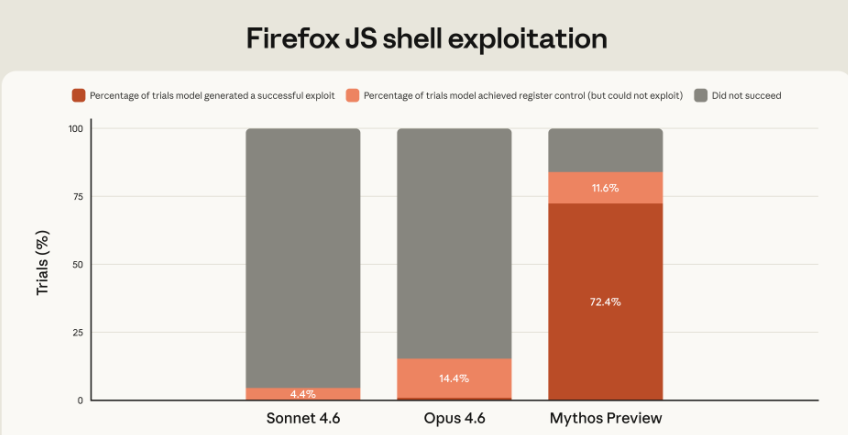
The development in offensive capabilities from earlier generations of AI is staggering.
Anthropic famous that their earlier Opus 4.6 mannequin struggled considerably with autonomous exploitation, changing Mozilla Firefox bugs into shell exploits solely twice out of a whole bunch of makes an attempt.
In distinction, Mythos Preview developed working exploits for a similar Firefox vulnerabilities 181 instances.
When examined towards the OSS-Fuzz corpus, the brand new mannequin achieved full management circulate hijack on ten fully patched targets, a feat earlier fashions couldn’t accomplish.
Remarkably, these superior capabilities weren’t explicitly programmed however emerged organically as a downstream consequence of the mannequin’s enhanced coding and reasoning expertise.
At the moment, over 99 % of the zero-day vulnerabilities found by Mythos Preview stay unpatched.
Recognizing the fast dual-use dangers, Anthropic is deploying Challenge Glasswing to share these superior capabilities with open-source builders and important business companions first.
Whereas frontier AI fashions might initially provide a short-term benefit to risk actors, the long-term equilibrium is predicted to closely favor community defenders.
By integrating fashions like Mythos Preview into software program growth pipelines, the cybersecurity business can systematically determine and remediate essential flaws earlier than new code is ever deployed.
Comply with us on Google Information, LinkedIn, and X to Get Immediate Updates and Set GBH as a Most well-liked Supply in Google.










