Hackers have been exploiting an as-yet unidentified flaw in Adobe Reader since no less than November 2025. This zero-day vulnerability was first found by safety knowledgeable Haifei Li, founding father of EXPMON, a sandbox-based exploit detection system.
How the assault works
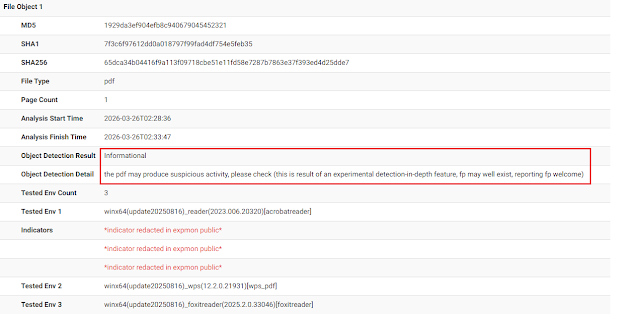
Haifei Li discovered that the assault is triggered as quickly as a sufferer opens a specifically crafted PDF file. One pattern recognized on VirusTotal was named “Invoice540.pdf,” suggesting the attackers are utilizing pretend invoices as a lure. Li notes that the exploit is especially harmful as a result of it runs on the most recent model of Adobe Reader with out requiring any further consumer interplay.
As soon as the file is open, it runs hidden, closely obfuscated JavaScript code. This code hijacks two built-in software program instruments known as APIs: util.readFileIntoStream, which is generally used to deal with recordsdata, and RSS.addFeed, which often manages net updates. By abusing these, the hackers can secretly steal information from the pc and ship it to a distant server on the handle 169.40.2.68.
Li additional defined in a weblog submit that that is simply step one as a result of by amassing information and fingerprinting the pc, hackers can put together for even worse actions. This consists of Distant Code Execution (RCE), which lets them run their very own programmes on the sufferer’s machine, or a Sandbox Escape (SBX) to bypass built-in safety boundaries and take full management.
Russian oil and gasoline lures
The attackers appear to be centered on concentrating on particular teams. A safety analyst, Giuseppe Massaro (Gi7w0rm), appeared into the malicious paperwork, figuring out that they have been written in Russian and that the textual content within the PDFs talks about information and occasions within the Russian oil and gasoline trade to make the emails look actual.
Extra regarding is that this isn’t the primary time Adobe Reader has confronted related points. A earlier flaw, tracked as CVE-2024-41869, was additionally reported by Haifei Li, though Adobe didn’t verify whether or not it had been exploited in real-world assaults on the time.
Adobe was notified in regards to the flaw round 7 April, however they haven’t launched an replace to repair it simply but. Li, who has a protracted historical past of discovering bugs at corporations like Microsoft, mentioned it is important for the general public to find out about this now to allow them to keep protected.
Since there isn’t any official repair or patch obtainable as but, be cautious when opening any PDF recordsdata from individuals you don’t know, and people who handle workplace networks should block web visitors that mentions Adobe Synchronizer within the header to cease the hackers from speaking with the contaminated computer systems.