Hackers are abusing GitHub and Jira’s constructed‑in notification methods to ship phishing emails that seem utterly respectable.
As a result of these emails are despatched from the platforms’ personal mail servers, they cross commonplace checks like SPF, DKIM, and DMARC, making them very exhausting for conventional e mail gateways to dam.
The messages are routed by way of the official mail infrastructure of those providers, so safety merchandise see them as trusted site visitors from known-good domains.
Most campaigns concentrate on phishing and credential harvesting, usually used as a primary step earlier than additional assaults as soon as accounts are compromised.
Throughout one marketing campaign on 17 February 2026, round 2.89% of all emails noticed coming from GitHub had been seemingly tied to this abuse, highlighting the dimensions of the issue.
Cisco Talos has noticed a latest spike in spam and phishing exercise delivered by means of notification pipelines in common SaaS collaboration instruments, particularly GitHub and Atlassian Jira.
Over a 5‑day window, about 1.20% of messages from “[email protected]” carried an “bill” lure within the topic line, signaling a centered billing‑themed phishing run.
Platform‑as‑a‑Proxy (PaaP) method
This rising “Platform‑as‑a‑Proxy” mannequin makes use of respectable SaaS platforms as supply proxies for malicious content material.
As a result of the emails are generated and signed by GitHub or Jira, they meet all authentication necessities and inherit the popularity of the supplier.
This successfully separates the attacker’s intent from the underlying infrastructure and provides the phishing mail a constructed‑in “seal of approval” many gateways don’t problem.
Attackers embed their social‑engineering lures inside regular workflow notifications, resembling commit alerts or service desk invites.
Customers see notifications they’re used to receiving and usually tend to click on, particularly when the content material mentions invoices, assist points, or pressing account issues.
On GitHub, risk actors exploit the automated commit notification system. They create repositories and push commits that include malicious textual content within the two commonplace commit fields: a brief abstract and an extended description.
The abstract line, which seems first and most prominently in e mail alerts, is crafted because the preliminary hook, usually referencing billing or account points.
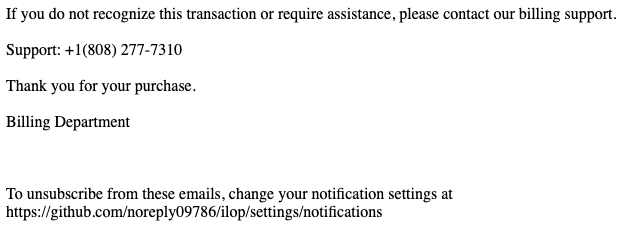
The prolonged description area is then used to host the primary rip-off content material, resembling faux billing statements, fraudulent assist numbers, or phishing hyperlinks.
When the commit is pushed, GitHub infrastructure sends an automated e mail to collaborators from a respectable SMTP host like “out‑28.smtp.github.com”, signed with a legitimate “d=github.com” DKIM signature.
As a result of the message construction and headers are real, it simply slips previous safety filters and lands immediately in customers’ inboxes.
Jira invitation hijacking
In Jira, attackers concentrate on invitation and repair desk workflows reasonably than uncooked notification pipelines.
They arrange Jira Service Administration tasks and abuse configurable fields resembling “Challenge Identify”, “Welcome Message”, or “Challenge Description” to insert their lures.
When Jira sends automated “Buyer Invite” or “Service Desk” emails, Atlassian’s backend injects this content material into its personal trusted, cryptographically signed templates.
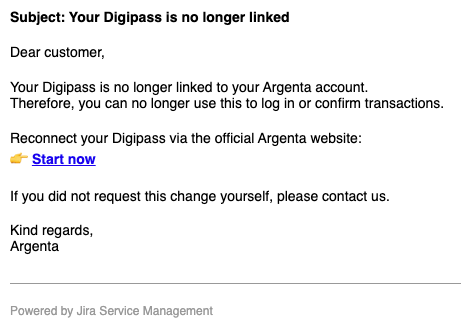
Victims then obtain skilled‑trying messages that seem to return from a respectable Jira challenge, full with Atlassian branding within the footer.
As a result of Jira notifications are frequent in company environments and infrequently vital for IT workflows, these emails are hardly ever blocked, permitting phishing content material to masquerade as inside helpdesk or challenge alerts.
This exercise exposes a rising “belief paradox,” the place organizations deal with emails from main SaaS platforms as inherently secure.
Defenders ought to: identification‑test which particular SaaS cases and sender identities are allowed, ingest GitHub and Atlassian API logs into SIEM/SOAR to detect suspicious repository or challenge exercise, and profile “regular” enterprise utilization in order that pressing billing or monetary lures from code or ticketing instruments are flagged as semantically irregular.
GitHub is abused for its sturdy developer popularity, whereas Jira is leveraged for its position in enterprise‑vital processes, letting attackers launder malicious content material by means of trusted manufacturers.
Cisco Talos recommends transferring away from binary area‑degree belief in the direction of a Zero‑Belief mindset for SaaS notifications.
Including friction for prime‑threat notifications and automating takedowns of malicious repositories or Jira tasks can additional increase attacker prices and cut back the effectiveness of this PaaP mannequin.
Observe us on Google Information, LinkedIn, and X to Get Prompt Updates and Set GBH as a Most well-liked Supply in Google.










