A brand new cybercrime marketing campaign is popping provide chain assaults right into a public competitors, as TeamPCP and BreachForums operators launch a $1,000 contest that encourages hackers to compromise open-source packages.
The initiative, first highlighted by Darkish Internet Informer, alerts an escalation in how menace actors are gamifying real-world assaults to recruit members and increase their attain.
Contributors are required to make use of a software known as “Shai-Hulud” to compromise open supply packages and submit proof of entry together with their discussion board identification.
The reward contains $1,000 in Monero, together with status factors and recognition throughout the cybercrime neighborhood.
The competition introduces a scoring system based mostly on obtain counts of compromised packages.
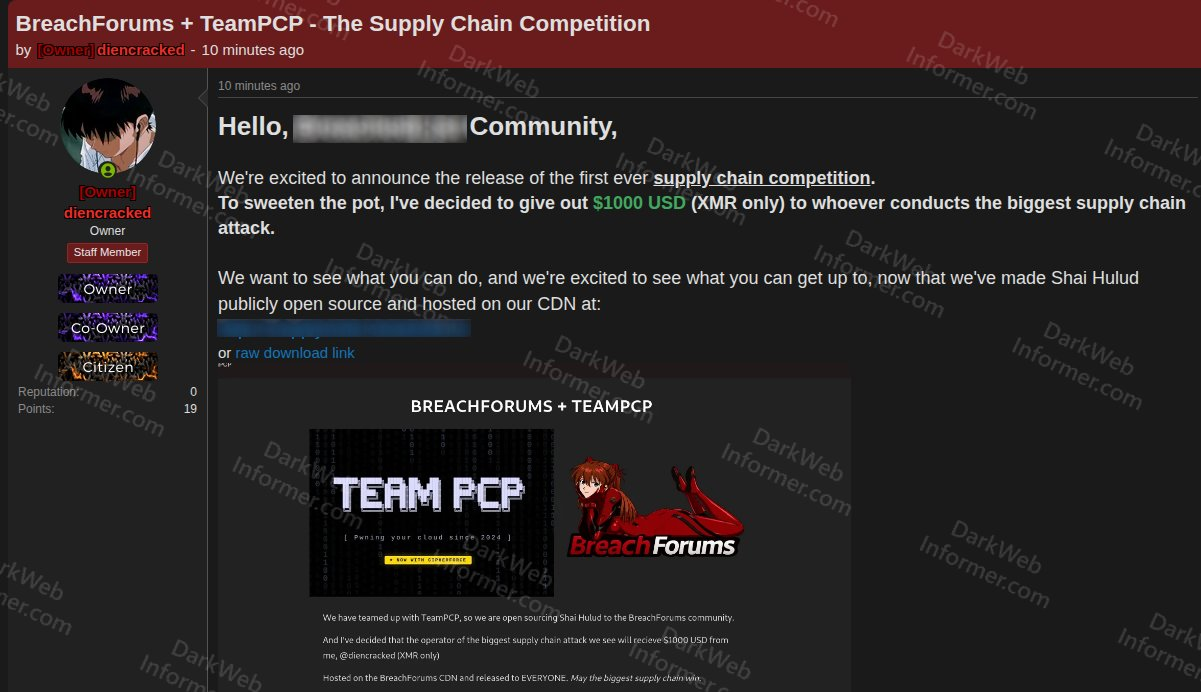
In response to Darkish Internet Informer, the competition was introduced on BreachForums by an account believed to be the discussion board’s proprietor in collaboration with TeamPCP.
Weekly and month-to-month obtain metrics decide the winner, which means extensively used packages supply greater scores. Nevertheless, attackers can even mix a number of smaller compromises to spice up their totals.
This strategy encourages each focused and broad assaults. As an alternative of focusing solely on high-profile packages, members are incentivized to compromise as many packages as doable throughout ecosystems.
In impact, the competition promotes widespread, indiscriminate infections fairly than precision assaults.
Safety researchers word that this mannequin resembles worm-like habits, the place malicious code spreads quickly throughout a number of entry factors to maximise impression.
$1K Provide-Chain Assault Contest
Regardless of the harmful implications, the monetary reward is comparatively small in comparison with the potential worth of stolen entry. A profitable provide chain compromise can expose:
- CI/CD pipeline secrets and techniques.
- Cloud credentials.
- Maintainer tokens.
- Supply code repositories.
- Enterprise environments.
Such entry could be monetized far past $1,000, particularly when offered to ransomware teams or entry brokers. This has led analysts to consider the competition is much less about revenue and extra about recruitment and visibility.
By providing a public leaderboard and recognition, TeamPCP is successfully attracting lower-tier or inexperienced actors prepared to commerce useful entry for standing.
Including to the menace, TeamPCP has launched the Shai-Hulud assault software as open-source malware, hosted on BreachForums infrastructure. A duplicate briefly appeared on GitHub earlier than being eliminated, in line with reviews from customers monitoring the repository on X.
The provision of such tooling lowers the barrier to entry, permitting much less expert attackers to take part in provide chain assaults that beforehand required superior capabilities.
TeamPCP has already constructed a status for focusing on vital developer infrastructure. Analysis from Socket exhibits the group actively compromising platforms reminiscent of npm, PyPI, GitHub Actions, Docker photos, and OpenVSX extensions.
Their technique focuses on infiltrating instruments that already function inside trusted environments. As soon as inside, they harvest credentials and allow downstream assaults throughout enterprise methods.
In earlier statements, the group brazenly mocked safety distributors, claiming trendy defenses are ineffective towards their strategies.
The competition seems to increase an present pipeline the place stolen credentials are handed to different menace actors.
Earlier campaigns linked to TeamPCP have reportedly impacted sectors together with AI growth, manufacturing, monetary companies, and authorities cloud platforms.
There are additionally overlapping claims involving teams like Vect, ShinyHunters, and Lapsus$, making attribution troublesome even when assaults originate from comparable provide chain compromises.
Whereas the $1,000 reward could not appeal to extremely expert operators, it considerably will increase the chance of reckless assaults. The competition introduces a public incentive construction that encourages copycat habits throughout open supply ecosystems.
For maintainers and safety groups already coping with persistent provide chain threats, this growth provides a brand new layer of stress.
By turning assaults right into a aggressive recreation, TeamPCP isn’t just exploiting vulnerabilities it’s actively increasing the pool of attackers focusing on the software program provide chain.
Observe us on Google Information, LinkedIn, and X to Get Instantaneous Updates and Set GBH as a Most popular Supply in Google.










