A Brazilian tech agency that makes a speciality of defending networks from distributed denial-of-service (DDoS) assaults has been enabling a botnet chargeable for an prolonged marketing campaign of large DDoS assaults towards different community operators in Brazil, KrebsOnSecurity has discovered. The agency’s chief government says the malicious exercise resulted from a safety breach and was seemingly the work of a competitor making an attempt to tarnish his firm’s public picture.

An Archer AX21 router from TP-Hyperlink. Picture: tp-link.com.
For the previous a number of years, safety specialists have tracked a sequence of large DDoS assaults originating from Brazil and solely concentrating on Brazilian ISPs. Till lately, it was lower than clear who or what was behind these digital sieges. That modified earlier this month when a trusted supply who requested to stay nameless shared a curious file archive that was uncovered in an open listing on-line.
The uncovered archive contained a number of Portuguese-language malicious applications written in Python. It additionally included the personal SSH authentication keys belonging to the CEO of Enormous Networks, a Brazilian ISP that primarily presents DDoS safety to different Brazilian community operators.
Based in Miami, Fla. in 2014, Enormous Networks’s operations are centered in Brazil. The corporate originated from defending recreation servers towards DDoS assaults and developed into an ISP-focused DDoS mitigation supplier. It doesn’t seem in any public abuse complaints and isn’t related to any recognized DDoS-for-hire providers.
However, the uncovered archive exhibits {that a} Brazil-based menace actor maintained root entry to Enormous Networks infrastructure and constructed a robust DDoS botnet by routinely mass-scanning the Web for insecure Web routers and unmanaged area title system (DNS) servers on the Internet that could possibly be enlisted in assaults.
DNS is what permits Web customers to achieve web sites by typing acquainted domains as an alternative of the related IP addresses. Ideally, DNS servers solely present solutions to machines inside a trusted area. However so-called “DNS reflection” assaults depend on DNS servers which might be (mis)configured to simply accept queries from wherever on the Internet. Attackers can ship spoofed DNS queries to those servers in order that the request seems to come back from the goal’s community. That method, when the DNS servers reply, they reply to the spoofed (focused) handle.
By making the most of an extension to the DNS protocol that permits massive DNS messages, botmasters can dramatically increase the scale and influence of a mirrored image assault — crafting DNS queries in order that the responses are a lot larger than the requests. For instance, an attacker may compose a DNS request of lower than 100 bytes, prompting a response that’s 60-70 instances as massive. This amplification impact is very pronounced when the perpetrators can question many DNS servers with these spoofed requests from tens of hundreds of compromised units concurrently.
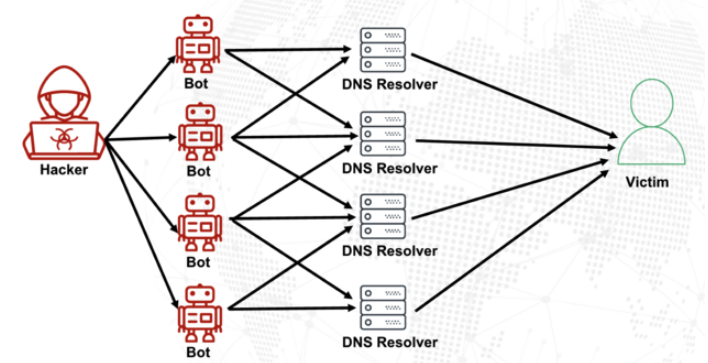
A DNS amplification and reflection assault, illustrated. Picture: veracara.digicert.com.
The uncovered file archive consists of a command-line historical past displaying precisely how this attacker constructed and maintained a robust botnet by scouring the Web for TP-Hyperlink Archer AX21 routers. Particularly, the botnet seeks out TP-Hyperlink units that stay susceptible to CVE-2023-1389, an unauthenticated command injection vulnerability that was patched again in April 2023.
Malicious domains within the uncovered Python assault scripts included DNS lookups for hikylover[.]st, and c.loyaltyservices[.]lol, each domains which were flagged up to now yr as management servers for an Web of Issues (IoT) botnet powered by a Mirai malware variant.
The leaked archive exhibits the botmaster coordinated their scanning from a Digital Ocean server that has been flagged for abusive exercise a whole lot of instances up to now yr. The Python scripts invoke a number of Web addresses assigned to Enormous Networks that have been used to determine targets and execute DDoS campaigns. The assaults have been strictly restricted to Brazilian IP handle ranges, and the scripts present that every chosen IP handle prefix was attacked for 10-60 seconds with 4 parallel processes per host earlier than the botnet moved on to the following goal.
The archive additionally exhibits these malicious Python scripts relied on personal SSH keys belonging to Enormous Networks’s CEO, Erick Nascimento. Reached for remark concerning the recordsdata, Mr. Nascimento stated he didn’t write the assault applications and that he didn’t notice the extent of the DDoS campaigns till contacted by KrebsOnSecurity.
“We acquired and notified many Tier 1 upstreams relating to very very massive DDoS assaults towards small ISPs,” Nascimento stated. “We didn’t dig deep sufficient on the time, and what you despatched makes that clear.”
Nascimento stated the unauthorized exercise is probably going associated to a digital intrusion first detected in January 2026 that compromised two of the corporate’s improvement servers, in addition to his private SSH keys. However he stated there’s no proof these keys have been used after January.
“We notified the crew in writing the identical day, wiped the packing containers, and rotated keys,” Nascimento stated, sharing a screenshot of a January 11 notification from Digital Ocean. “All documented internally.”
Mr. Nascimento stated Enormous Networks has since engaged a third-party community forensics agency to analyze additional.
“Our working evaluation thus far is that this all began with a single inner compromise — one pivot level that gave the attacker downstream entry to some assets, together with a legacy private droplet of mine,” he wrote.
“The compromise occurred via a bastion/leap server that a number of individuals had entry to,” Nascimento continued. “Digital Ocean flagged the droplet on January 11 — compromised as a result of a leaked SSH key, of their wording — I used to be touring on the time and addressed it on return. That droplet was deprecated and destroyed, and it was by no means a part of Enormous Networks infrastructure.”
The malicious software program that powers the botnet of TP-Hyperlink units used within the DDoS assaults on Brazilian ISPs is predicated on Mirai, a malware pressure that made its public debut in September 2016 by launching a then record-smashing DDoS assault that stored this web site offline for 4 days. In January 2017, KrebsOnSecurity recognized the Mirai authors because the co-owners of a DDoS mitigation agency that was utilizing the botnet to assault gaming servers and scare up new purchasers.
In Might 2025, KrebsOnSecurity was hit by one other Mirai-based DDoS that Google known as the biggest assault it had ever mitigated. That report implicated a 20-something Brazilian man who was working a DDoS mitigation firm in addition to a number of DDoS-for-hire providers which have since been seized by the FBI.
Nascimento flatly denied being concerned in DDoS assaults towards Brazilian operators to generate enterprise for his firm’s providers.
“We don’t run DDoS assaults towards Brazilian operators to promote safety,” Nascimento wrote in response to questions. “Our gross sales mannequin is generally inbound and thru channel integrator, distributors, companions — not lively prospecting primarily based on market incidents. The targets within the scripts you acquired are small regional suppliers, the overwhelming majority of that are neither in our buyer base nor in our business pipeline — a truth verifiable via public sources like QRator.”
Nascimento maintains he has “robust proof saved on the blockchain” that this was all achieved by a competitor. As for who that competitor is likely to be, the CEO wouldn’t say.
“I’d like to share this with you, nevertheless it couldn’t be printed as it will lose the shock issue towards my dishonest competitor,” he defined. “Coincidentally or not, your contact occurred per week earlier than an vital occasion – one which this competitor has NEVER participated in (and it’s a conventional occasion within the sector). And this yr, they are going to be collaborating. Unusual, isn’t it?”
Unusual certainly.