Barts Well being NHS Belief has confirmed that the Russian-speaking Cl0p ransomware group stole information from certainly one of its bill databases after exploiting a vulnerability in Oracle E-Enterprise Suite. The breach uncovered knowledge linked to funds for therapy and providers, with some data going again a number of years.
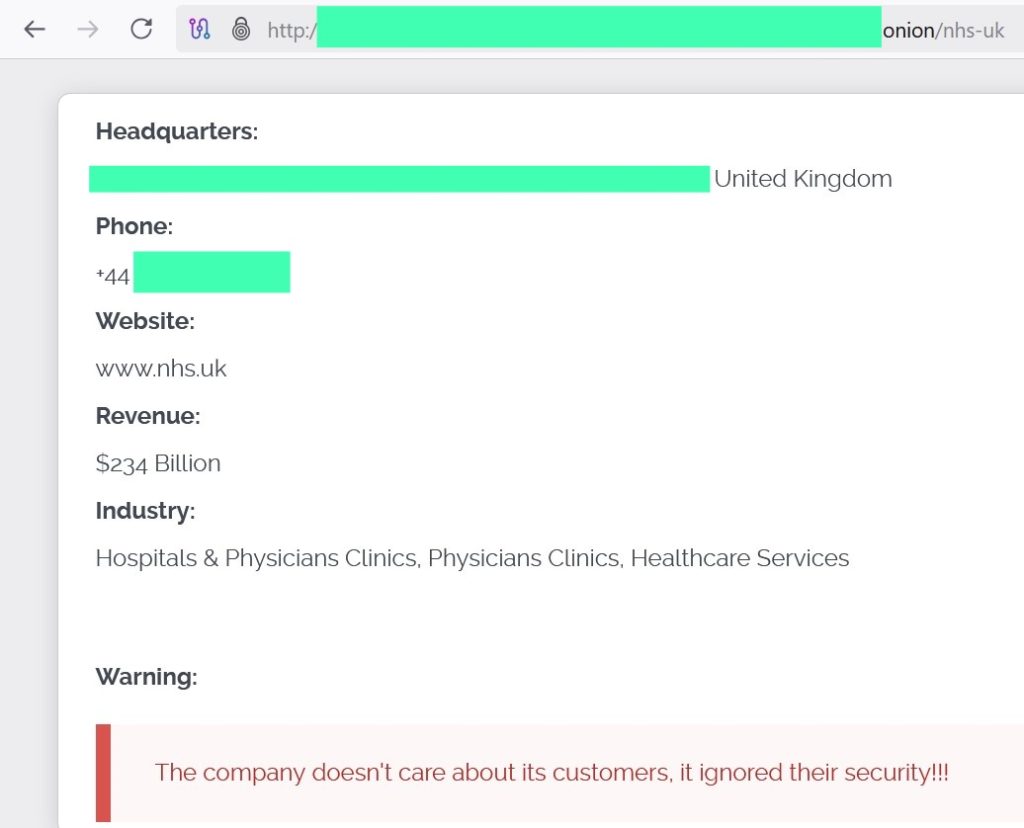
Hackread.com first reported on the Cl0p exercise in November twenty twenty 5, noting the group had leaked 241 GB of NHS knowledge on its hidden web site shortly after claiming accountability for a wider marketing campaign in opposition to healthcare targets.
Now, in keeping with Barts’ press launch, the stolen materials contains names and addresses of sufferers who have been billed for care, data of former employees with unresolved wage points and fee particulars for suppliers. Most provider data is already public. Medical methods and affected person data weren’t affected.
Recordsdata linked to accounting providers offered to Barking Havering and Redbridge College Hospitals NHS Belief since April 2024 have been additionally compromised. Barts advises sufferers to assessment any invoices they obtained to know if their knowledge was concerned.
The breach occurred in August however went undetected till November, when the information surfaced on the Cl0p ransomware‘s darkish net leak web site. Oracle has since patched the exploited flaw. Barts has reported the incident to NHS England, the Nationwide Cyber Safety Centre, the Metropolitan Police and knowledge regulators. Additionally it is searching for a Excessive Courtroom order to dam the circulation of the stolen knowledge.
NHS and ransomware assaults
The Barts incident provides to a rising checklist of ransomware exercise aimed toward UK well being providers. In current months, Qilin ransomware has launched affected person data on personal channels after hitting an NHS provider, which affected emergency care in London. Hackread reported that a type of incidents has been linked by employees to the demise of a affected person after a disruption prompted delays in therapy.
Extra assaults have focused NHS our bodies in Scotland. The INC group claimed to have taken a number of terabytes of affected person information and later launched the fabric on hidden boards whereas additionally publishing threats in opposition to UK well being providers.
These circumstances share widespread traits. Attackers search for safety vulnerabilities in broadly used enterprise methods. As soon as inside, they transfer towards administrative knowledge that may be offered or used for stress campaigns. Even when scientific methods keep intact, the fallout strains employees who should rebuild belief and handle fraud dangers for these affected.
Though the Barts theft includes bill knowledge reasonably than scientific data, it nonetheless creates alternatives for social engineering. Cyber criminals usually use primary private particulars to help fee fraud. Barts is directing individuals to Cease Assume Fraud for recommendation and is urging anybody with inquiries to contact its knowledge safety officer.