Cybersecurity researchers at Guardio Labs have found a large phishing operation that makes use of Google’s personal infrastructure to hijack Fb accounts. This analysis reveals a Vietnamese-linked operation code-named AccountDumpling that has already compromised over 30,000 customers globally.
AppSheet Abuse
Guardio Labs researchers defined within the report that this marketing campaign abuses the notification system of Google AppSheets (a no-code software designed for enterprise automation). Through the use of this service, hackers ship emails from [email protected] and appsheet.bounces.google.com.
These emails originate from Google’s servers, and that’s why passing the authentication checks like SPF, DKIM, and DMARC turns into potential. Researchers famous that the phishing lures contain Meta-related themes. Similar to faux copyright complaints or account disablement warnings. One e-mail from April 2026 included the textual content “Case ID: 6480258166” and warned of everlasting disablement inside 24 hours.
Technical Strategies and Assault Clusters
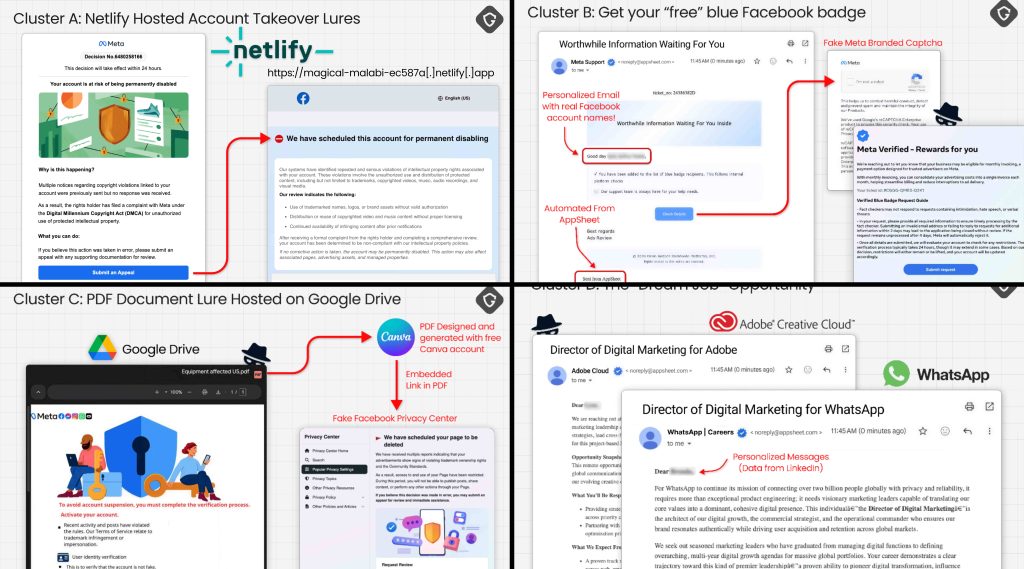
Researchers famous that this isn’t only one easy trick. The operation is cut up into completely different strategies, or clusters, to catch various kinds of victims:
- Cluster A- Netlify Clones: Some attackers used a software referred to as HTTrack to repeat the Fb Assist Centre. They hosted these on Netlify to steal passwords and pictures of presidency IDs.
- Cluster B- The Reward Entice: One other group used social engineering to lure customers, reminiscent of by promising Blue Badge verification. They used zero-font ways like Cyrillic homoglyphs (a Cyrillic “а” as a substitute of a Latin “a”) and hair areas (invisible Unicode characters) to bypass spam filters.
- Cluster C- Dwell Management: This cluster is the scariest as it’s extremely superior. It makes use of a Google Drive-hosted PDF and Socket IO and WebSockets to create a reside operator panel. When the sufferer clicks on it, the hackers can work together with the victims in real-time to request 2FA (two-factor authentication) codes.
- Cluster D: This includes faux job recruitment for manufacturers like Adobe, Apple, and Coca-Cola, and redirects victims to personal WhatsApp chats.
Attribution
Additional investigation revealed a transparent path main again to Vietnam. A Canva-generated PDF file from the assault contained the identify Phạm Tài Tân within the metadata. This similar identify is linked to a enterprise that overtly ‘helps’ individuals recuperate locked Fb accounts.
In line with researchers, the info stolen by these kits is shipped to Telegram bots like @haixuancau_bot and @globalglobalglobalbot_bot. These channels are run by customers recognized by their aliases “Huge Bosss” and “@mansinblack.”
Whereas the assault is world, 68.6% of the victims in the primary dataset had been from the US, adopted by the UK, Canada, and Italy. Guardio Labs warned that it is a skilled provide chain. One group steals the account, and one other sells the entry again or makes use of it for fraud. It’s a darkish enterprise mannequin that turns person belief right into a product.
Assault clusters (Supply: Guardio Labs)