A brand new Proofpoint report reveals how attackers are utilizing Microsoft 365’s Direct Ship and unsecured SMTP relays to ship internal-looking phishing emails.
The newest analysis from cybersecurity agency Proofpoint reveals a intelligent phishing marketing campaign that makes use of a reliable Microsoft 365 characteristic to trick individuals into opening malicious emails. The assault, reportedly, sends messages that look like from inside an organization, making them look extremely reliable to workers.
Proofpoint researchers noticed that attackers are benefiting from a setting in Microsoft 365 referred to as Direct Ship. This characteristic is meant for issues like workplace printers to ship faxes and scans on to an e mail inbox with out a password. Nonetheless, hackers are misusing it to ship pretend emails that appear to come back from inside a company. This enables them to bypass most of the ordinary safety checks.
How The Assault Works
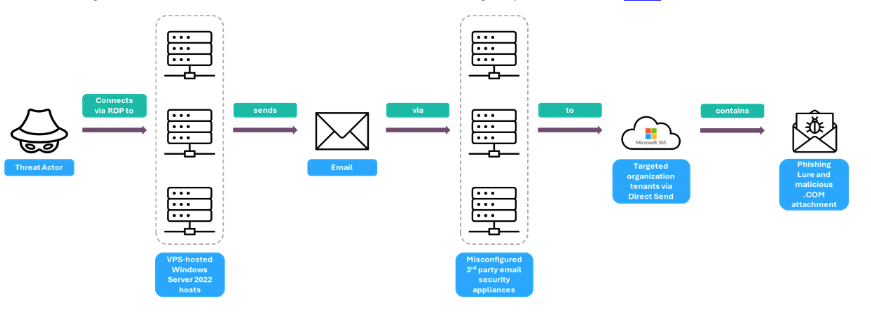
The malicious marketing campaign makes use of a classy chain to ship its payload. As illustrated in a stream chart under, a risk actor first connects to a pc server working Home windows Server 2022. From there, they ship an e mail via third-party e mail safety home equipment, which act as SMTP relays, a service that forwards emails from one server to a different, to ahead the messages. The emails are designed to seem reliable, and the sending infrastructure even current legitimate DigiCert SSL certificates to look reliable.
Nonetheless, the home equipment themselves have been left unsecured, with particular communication ports (8008, 8010, and 8015) uncovered. These ports have been protected solely by expired or self-signed certificates, making them susceptible.
The message is designed to seem as if it was despatched by a coworker, with a spoofed or pretend “From” handle. These emails usually have a enterprise theme, with titles like “activity reminders,” “wire authorizations,” and “voicemails” to entice the person to click on. Despite the fact that a few of these messages are flagged by Microsoft’s inside safety as a possible spoof, they’re nonetheless delivered to a person’s junk folder, leaving them susceptible to the assault.
Defending Your Group
Proofpoint’s report highlights that this kind of assault is a part of a rising development the place cybercriminals abuse trusted cloud companies to launch their schemes. As researchers state within the report, “The abuse of Microsoft 365’s Direct Ship characteristic is not only a technical flaw. It’s a strategic threat to a company’s belief and status.”
This makes it essential for corporations to re-evaluate their safety settings and configurations. Researchers recommend auditing their e mail techniques and implementing stricter e mail authentication to dam these spoofed messages. Additionally, disabling the Direct Ship characteristic if a company doesn’t want it’s endorsed.