A extreme scoping vulnerability was just lately found in Microsoft Entra ID’s new Agent Identification Platform.
The safety flaw allowed customers assigned the Agent ID Administrator position to hijack arbitrary service principals throughout a company’s tenant, resulting in potential privilege escalation.
Though the executive position was designed strictly to handle AI agent identities, a boundary breakdown allowed it to regulate non-agent service principals as properly. Microsoft has absolutely patched the vulnerability throughout all cloud environments.
Nonetheless, the incident highlights the continuing dangers of introducing new management planes constructed on present listing primitives.
When an software is registered in Microsoft Entra ID, it creates a worldwide software object and a neighborhood service principal.
The service principal acts because the localized id that authenticates, receives position assignments, and accesses enterprise assets.
Microsoft Entra Agent ID is a preview characteristic that permits organizations to control and safe AI brokers by treating them as first-class identities. The platform introduces new listing objects, comparable to agent identities and blueprints.
As a result of these AI agent identities are technically carried out as specialised service principals, they share a standard foundational infrastructure with normal enterprise functions.
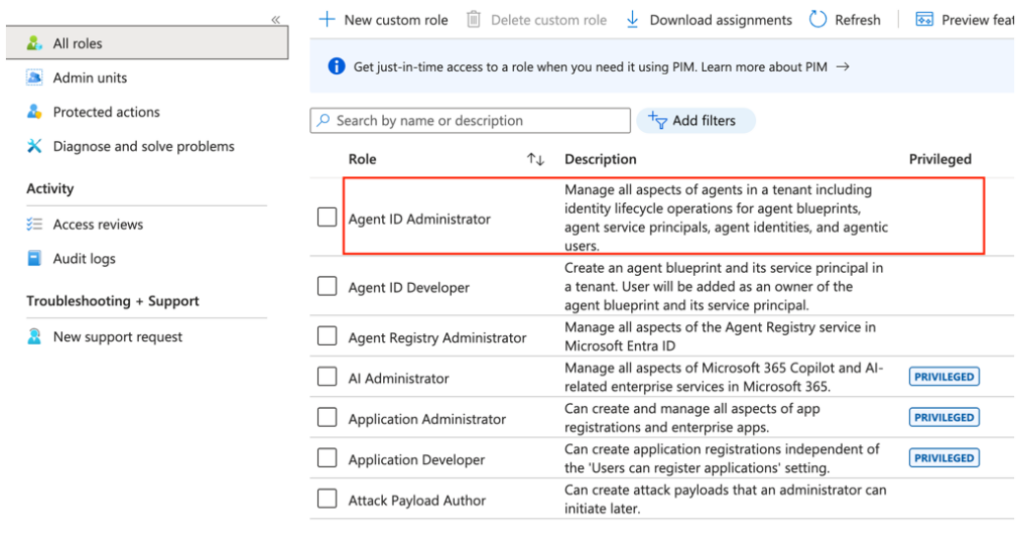
To handle these new AI objects, Microsoft created the Agent ID Administrator position. The documentation said that this position was restricted to agent-related objects. Nonetheless, because of the shared underlying structure between brokers and functions, a vital scoping hole emerged.
Hackers Exploit Agent ID Administrator Function
Cybersecurity researchers from SilverFort discovered that accounts holding solely the Agent ID Administrator position may exploit this scoping hole to take over any service principal.
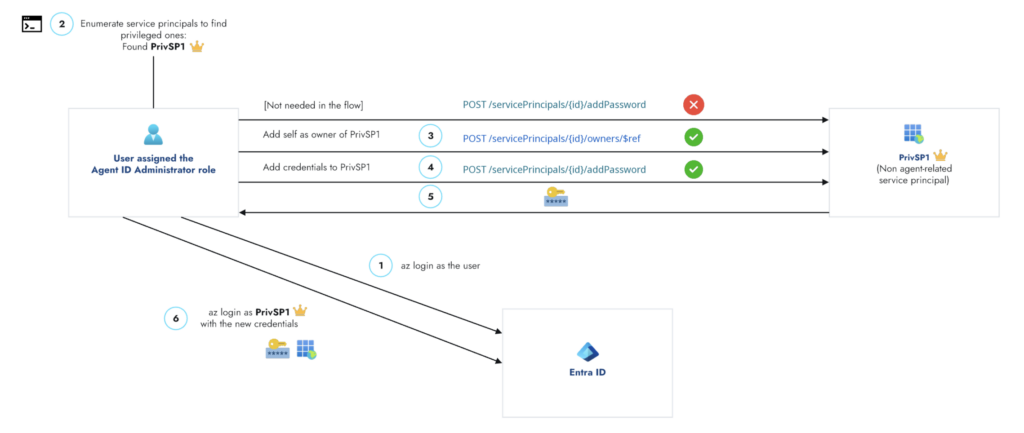
The assault stream executes by a easy however devastating takeover primitive:
- Assign Unauthorized Possession: An attacker with the Agent ID Administrator position can drive themselves because the proprietor of any service principal, bypassing meant agent-only restrictions.
- Generate New Credentials: As soon as possession is established, the attacker can seamlessly connect a brand new secret or certificates to the focused service principal.
- Authenticate and Hijack: The attacker makes use of the newly created credentials to authenticate because the hijacked service principal, gaining all of its related entry rights.
This course of grants the attacker full management over the compromised software id. Curiously, the vulnerability was strictly restricted to the service principal floor, because the system efficiently blocked makes an attempt to change possession on broader software objects maliciously.
The first hazard of this vulnerability lies in extreme privilege escalation. Service principals incessantly function because the digital identities behind vital CI/CD pipelines, automated workflows, and high-level safety instruments.
If an attacker efficiently hijacks a service principal that holds highly effective Microsoft Graph permissions or administrative listing roles, they instantly inherit these elevated rights.
Whereas the Agent ID Administrator position is comparatively new, practically all enterprise tenants make the most of extremely privileged service principals.
Moreover, the Entra consumer interface did not visually flag the Agent ID Administrator position as privileged, doubtlessly deceptive IT directors into assigning it with out enough safety scrutiny.
Following accountable disclosure in February 2026, Microsoft confirmed the flaw and efficiently deployed a complete repair by April 9, 2026.
The Agent ID Administrator position is now completely blocked from modifying the house owners of non-agent service principals.
To keep up sturdy safety, organizations should actively monitor delicate position utilization and alert safety groups to any sudden adjustments in service principal possession.
Privileged service principals have to be handled as vital infrastructure and require steady auditing of any newly created credentials.
Observe us on Google Information, LinkedIn, and X to Get On the spot Updates and Set GBH as a Most well-liked Supply in Google.








