Some cyber enterprise dangers solely present up whenever you take a more in-depth look. Provide chain blind spots are an ideal instance. Behind these important third-party connections, services can lurk unseen vulnerabilities that precipitate main cyber incidents – halting operations, triggering downstream chaos, and making headlines with their monetary, reputational, and authorized/compliance impacts.
As provide chains turn into more and more digitized and complicated, they supply cybercriminals a much bigger “threat floor” to purpose for. Organizations want to know their provide chain dependencies in depth to allow them to map the dangers and deploy efficient resilience methods to guard delicate knowledge and maintain enterprise continuity. But in keeping with the newest analysis from ESET and different sources, SMBs largely underestimate the potential dangers they face from disruption attributable to their provide chain, both from a malicious assault or operational outage.
What’s a provide chain and what dangers does it pose?
A provide chain is the entire community of organizations, individuals, actions, data, and sources concerned in shifting a services or products from its origin to the ultimate buyer, encompassing sourcing, manufacturing, distribution, and supply. Trendy provide chains are sometimes international and contain complicated worldwide logistics or connections.
Provide chain disruption provides rise to a number of, interrelated forms of enterprise threat. These embody cybersecurity, operational, geopolitical, monetary, reputational, compliance, environmental, and societal dangers. In real-world situations the dangers are likely to blur. For instance, knowledge breaches linked to companions typically have operational, monetary, compliance, and/or reputational components.
However notion doesn’t all the time mirror actuality on the subject of cybersecurity hazards. Maybe reflecting the media’s current concentrate on AI-powered exploits and geopolitical cyber battle, ESET’s 2026 SMB Cyber Readiness Index launched at this time discovered that 16% of Canadian and 17% of United States small companies fee provide chain assaults among the many threats they’re most involved about. Conversely, 34% Canadian and 32% United States SMBs recognized AI-powered malware of their high threats.
This appears extraordinarily low given the size and frequency of provide chain incidents – and the way broadly ‘provide chain’ actually stretches. The 3CX compromise of 2023 – the place bad actors trojanized a authentic software program replace to the VOIP developer’s product, doubtlessly exposing its 600,000 clients – confirmed how an incident affecting a single compromised vendor can cascade throughout industries. Notably, 3CX itself was the downstream sufferer of one other provide chain assault, courtesy of a compromised Buying and selling Applied sciences X_TRADER installer. It was the first-ever documented occasion of 1 provide chain assault seeding one other, and a reminder of how deep these chains can run.
Extra not too long ago, the CDK and Change Healthcare ransomware assaults in 2024 and the Jaguar Land Rover (JLR) ransomware assault of August 2025 illustrate how an incident at a vendor that sits at a crucial node propagates throughout a complete sector. JLR belongs on the record for a second motive: the intrusion reached the automaker by way of one among its IT service suppliers, putting it squarely in traditional provide chain territory.
The defective CrowdStrike replace from July 2024 made the identical level with out an attacker concerned, exhibiting confirmed that offer chain threat isn’t solely about malice. A botched replace launch travels the identical rails as a malware-laden one, and dependence on a single vendor can flip one level of failure into a worldwide disruption.
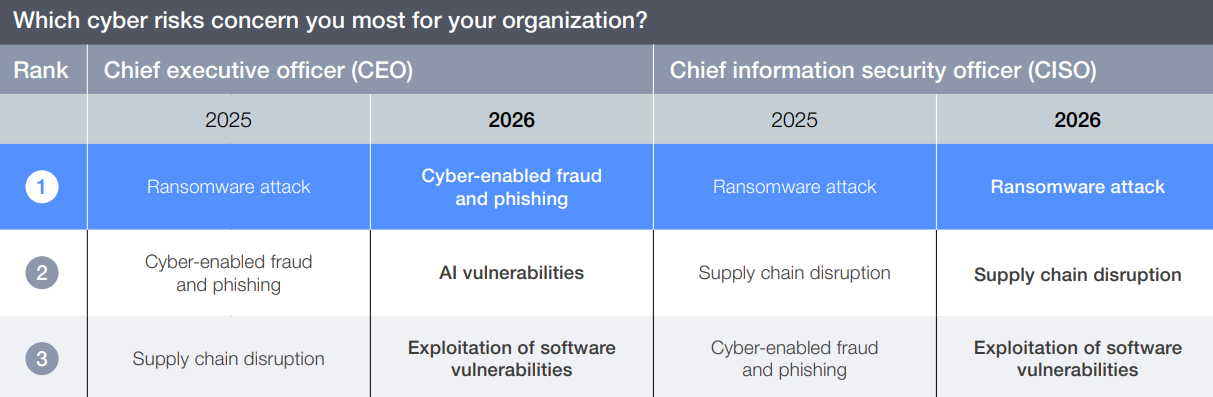
Echoing ESET’s findings, the World Financial Discussion board’s International Cybersecurity Outlook 2026 requested enterprise leaders throughout industries and areas to rank the cyber dangers that involved them most. CISOs rated provide chain disruption #2 for 2025 and #2 once more for 2026, whereas CEOs fee provide chain disruption #3 for 2025. I discover it shocking that offer chain disruption doesn’t proceed to rank in a CEO’s high 3.
General, about 30% of knowledge breaches contain a 3rd occasion, a determine that doubled year-over-year, in keeping with Verizon’s 2025 Knowledge Breach Investigations Report (DBIR). The entire financial price of software program provide chain assaults skyrocketed from $46 billion in 2023 to $60 billion in 2025, and is predicted to succeed in $138 billion by 2031. Statistics like these ought to put cyber provide chain threat on each enterprise chief’s quick record of considerations.
What are the highest cyber provide chain blind spots?
Provide chain cybersecurity threat considerations all doable ways in which attackers might infiltrate an organization’s networks or different IT infrastructure and steal its knowledge by focusing on vulnerabilities within the methods of third-party service suppliers, distributors, or companions. These assaults typically exploit conditions the place communications are trusted by default, doubtlessly compromising knowledge, private privateness, operational stability, and even nationwide safety.
Provide chain cyber vulnerabilities take varied varieties, akin to:
- Compromising network-connected SMB suppliers with weaker safety to create a backdoor into the goal enterprise.
- Injecting malicious code into software program elements (e.g., open-source libraries) or updates, doubtlessly compromising many customers.
- Utilizing phishing assaults and different social engineering ploys to steal privileged credentials or seed ransomware or different malware by way of a third-party akin to an IT companies firm.
- Hacking or vulnerabilities in bodily property like chipsets or IoT units on the supply.
A few of the cyber provide chain blind spots that threaten many organizations embody:
- Pondering your enterprise is extra resilient than it really is (false sense of safety) resulting from insufficient threat evaluation.
- Geopolitically motivated incidents (see beneath), the place “collateral harm” can hurt quite a few organizations indirectly associated to a battle.
- Cyber vulnerabilities a number of ranges deep within the provide chain the place the top buyer has no visibility (so-called fourth-party, nth-party, or oblique vendor threat).
- “Reverse” provide chain disruptions impacting an organization’s clients.
- Assuming new and unassessed vulnerabilities together with new provide chain companions that had been onboarded rapidly resulting from geopolitical occasions, pure disasters, or different chaotic situations.
- Trusting communications with companions as a substitute of leveraging zero belief rules to validate all connections.
- “Monoculture” points, akin to wide-scale reliance amongst MSSPs or cyber insurance coverage suppliers on one or a couple of well-liked cybersecurity options that, if compromised, would wreak instantaneous havoc on a big scale.
The sheer complexity of many trendy provide chains makes figuring out each single threat untenable. The query then turns into, the place do you draw the road? How deep and detailed is your vendor threat evaluation? And what degree of provide chain cyber threat are you prepared to simply accept as past your management?
What have been the impacts from main provide chain assaults?
A few of the most damaging incidents in current reminiscence hit organizations that sit at crucial nodes in provide chains, and the ensuing disruptions cascaded far past the unique goal.
A main instance of a cyberattack with an unlimited blast radius is the JLR ransomware assault from August 2025. Attackers reached the automaker by way of an outsourced IT service supplier, then disrupted manufacturing strains and IT companies for over 5 weeks. The outcome was a worldwide manufacturing shutdown that brought on a 25% drop in automobile manufacturing throughout the complete sector within the UK in September 2025. Components demand crumpled in a single day, forcing JLR’s suppliers and associated companies to put off a whole lot of employees and driving the UK authorities to challenge a £1.5 billion emergency mortgage assure to forestall a nationwide financial and workforce disaster. Deemed the most costly cyberattack in UK historical past, it resulted in over £1.9 billion in whole financial harm.
The Marks & Spencer (M&S) assault of April 2025 adopted the same sample. The hackers efficiently employed social engineering in opposition to an outsourced IT service supplier, impersonating staff and convincing assist desk employees to reset crucial system credentials. Contact particulars, delivery dates, and order histories from thousands and thousands of consumers had been apparently exfiltrated, and the corporate’s on-line and app-based order processing had been down for weeks. The prolonged outage price on the order of £300 million and inflicted lasting reputational harm.
Compromising generally used open-source software program libraries with malicious code is the same and more and more well-liked assault vector, with open-source malware proliferating 188% from 2024 to 2025.
In a stark illustration of geopolitical blind spots throughout the software program provide chain, a malicious backdoor positioned right into a authentic replace to the favored M.E.Doc accounting software program in 2017 brought on widespread distribution. Meant to focus on the Ukrainian economic system, the assault unfold NotPetya wiper malware to organizations worldwide, sowing destruction estimated to price $10 billion. The assault was later attributed to a Russia-aligned supply.
Even {hardware} elements like chips and circuit boards can doubtlessly be exploited or weaponized, creating blind spots which might be extraordinarily troublesome to detect or defend in opposition to. An ongoing instance is the Kr00k firmware provide chain vulnerability (CVE-2019-15126) found by ESET in 2019. Attackers can power affected units, together with thousands and thousands of smartphones, laptops, and IoT units, to encrypt Wi-Fi transmissions with an all-zero key that enables for straightforward decryption. It’s doubtless that many affected units nonetheless wouldn’t have firmware patches put in because of the mass scale of use.
And as an excessive instance, the “Operation Grim Beeper” provide chain assault of September 2024 noticed pagers and walkie-talkies utilized by Hezbollah members in Lebanon and Syria explode as a part of an Israeli intelligence operation. Over 30 individuals had been killed and three,000 injured after gear bought by Hezbollah was systematically intercepted and weaponized for years. Speak about a provide chain blind spot…
What are key concerns round geopolitical provide chain threat?
With Iran launching drone strikes in opposition to Amazon Net Companies (AWS) knowledge facilities in Bahrain and the UAE, geopolitical provide chain cyber threat is front-page information. The place kinetic and cyber warfare overlap, nation state actors and their proxies can exploit crucial provide chain dependencies to perpetrate wide-scale financial sabotage for strategic ends which will embody financial theft. Collateral harm is a part of the plan.
Some questions that organizations can ask to doubtlessly cut back geopolitical provide chain threat embody:
- Rigorously audit all third-party internet hosting relationships, vendor entry to your community, and many others. Is your knowledge shifting by way of knowledge facilities in unstable areas – both immediately or by way of service supplier actions? Cloud service disruptions can propagate unpredictably by way of the provision chain.
- Are you reliant on {hardware} or software program that cyber combatants are at present focusing on with specialised assaults, akin to Israeli-made OT {hardware}?
- Verify whether or not your managed safety answer supplier(s) and different crucial distributors have reviewed their very own geopolitical cyber threat publicity. If a 3rd occasion manages your incident detection and response (MDR) functionality, for instance, their answer turns into a part of your assault floor.
How can organizations construct provide chain cyber-resilience?
Common methods for mitigating provide chain cyber threat embody rigorously vetting suppliers’ cybersecurity postures, adopting rising expertise to reinforce monitoring, leveraging zero belief rules to cut back assault impacts, and creating and testing incident response and enterprise continuity plans to construct resilience and higher handle provide chain associated incidents. Your whole provider net must be a part of the danger evaluation.
To construct and operationalize provide chain cyber resilience, I like to recommend a sequence of actions that collectively construct resilience over a one-year interval.
First 3 months
- Nominate enterprise and IT homeowners for provide chain threat.
- Establish all of your third-party IT and enterprise provide chain distributors and prioritize them by 1) Entry to delicate knowledge, and a pair of) Criticality to the enterprise.
- Create a coverage that defines your minimal acceptable cybersecurity posture or controls for distributors.
- Verify vendor compliance along with your cyber necessities and exchange them as wanted.
First 6 months
- Proceed to watch vendor compliance along with your cyber necessities.
- Describe key {hardware} and software program provide chain dangers (e.g., open-source dependencies) in enterprise phrases.
- Incorporate your cyber necessities into procurement actions and contract negotiations. Negotiate the precise to watch and audit crucial distributors.
- Conduct a tabletop incident response train that features strategic distributors.
First 12 months
- Implement classes realized out of your tabletop train.
- Audit distributors in opposition to contractual cyber necessities (e.g., common time to patch). Examine provider cyber incidents the place related.
- Construct redundancy and fail-safes into IT methods wherever doable, whereas avoiding answer “monoculture” points.
- Evaluation and replace your cyber necessities coverage.
- Monitor and reply to international cyber regulatory/compliance adjustments that impression your enterprise.
Resilience is crucial
In a world of escalating threats and dangerous interdependencies, provide chain cyber resilience is a aggressive differentiator on the survival degree. Cybercriminals are eager to determine and goal a company’s third-party linkages both upstream or downstream. It’s doable {that a} chain of disrupted companions might face collective extortion strain – successfully a “crowdfunded” ransomware state of affairs.
As a foundational resilience constructing block, companies should comprehensively map their crucial third-party dependencies and vulnerabilities throughout digital and non-digital methods, together with people who is probably not apparent. Some methods to look past typical operational provide chain threat evaluation embody:
- AI-assisted steady provide chain monitoring
- Automated provide chain dependency mapping
- Zero-trust provide chain structure and connections
- Utility of menace intelligence to provide chain configurations
- Extending resilience planning/concerns past inside methods to incorporate the broader provide chain ecosystem
- Potential enter and help out of your cyber legal responsibility insurer, which can have data-driven insights into distributors’ provide chain cyber efficiency










