Safety researchers have uncovered a classy malware marketing campaign that leverages the ClickFix social engineering method to distribute information-stealing malware throughout Home windows and macOS platforms.
The marketing campaign demonstrates how risk actors are exploiting authentic search queries for cracked software program to ship devastating payloads that compromise person credentials and delicate knowledge.paste.txt
The an infection chain begins when customers seek for cracked or pirated software program on-line, a well-established lure for cybercriminals.
As a substitute of receiving authentic outcomes, victims encounter malicious touchdown pages hosted on Google-hosted providers, together with Colab, Drive, Looker Studio, Websites, and Teams.
This multi-hop infrastructure is intentionally designed to evade conventional safety measures, as directors are much less prone to block Google providers outright.paste.txt
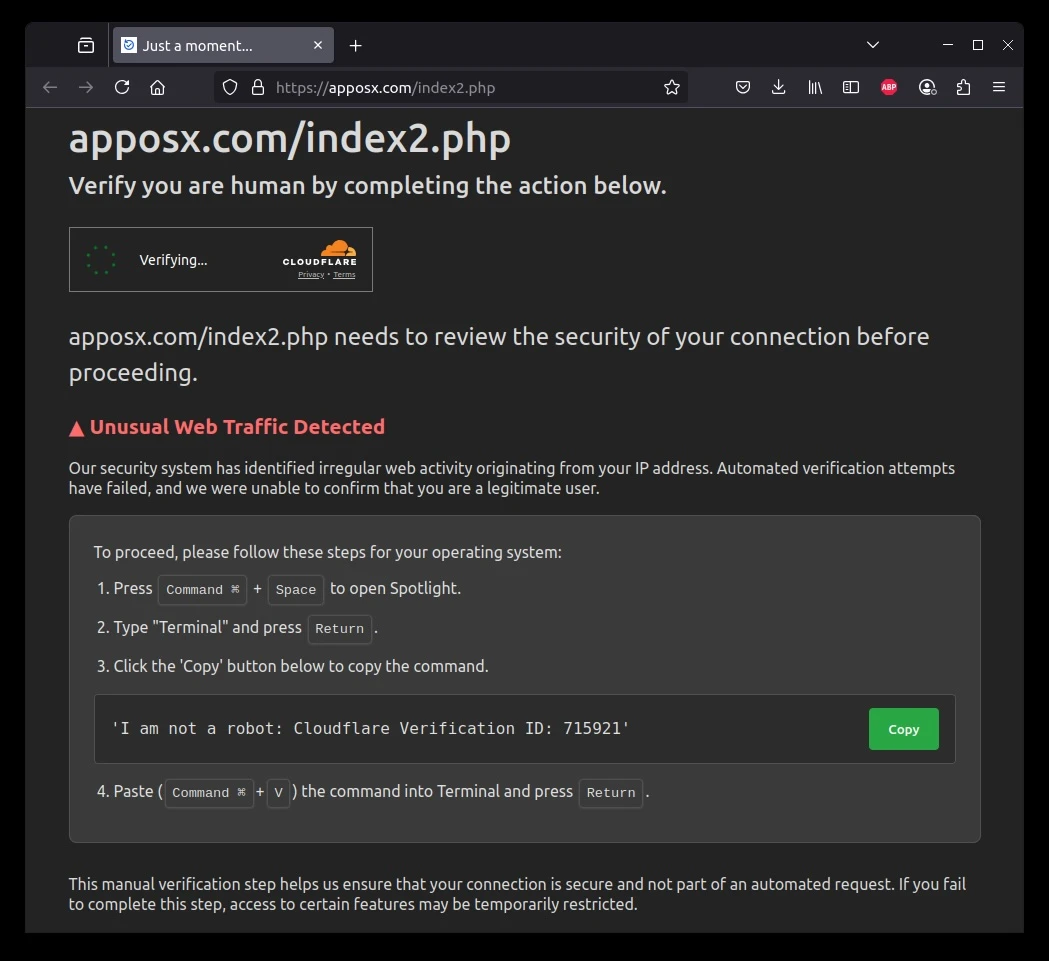
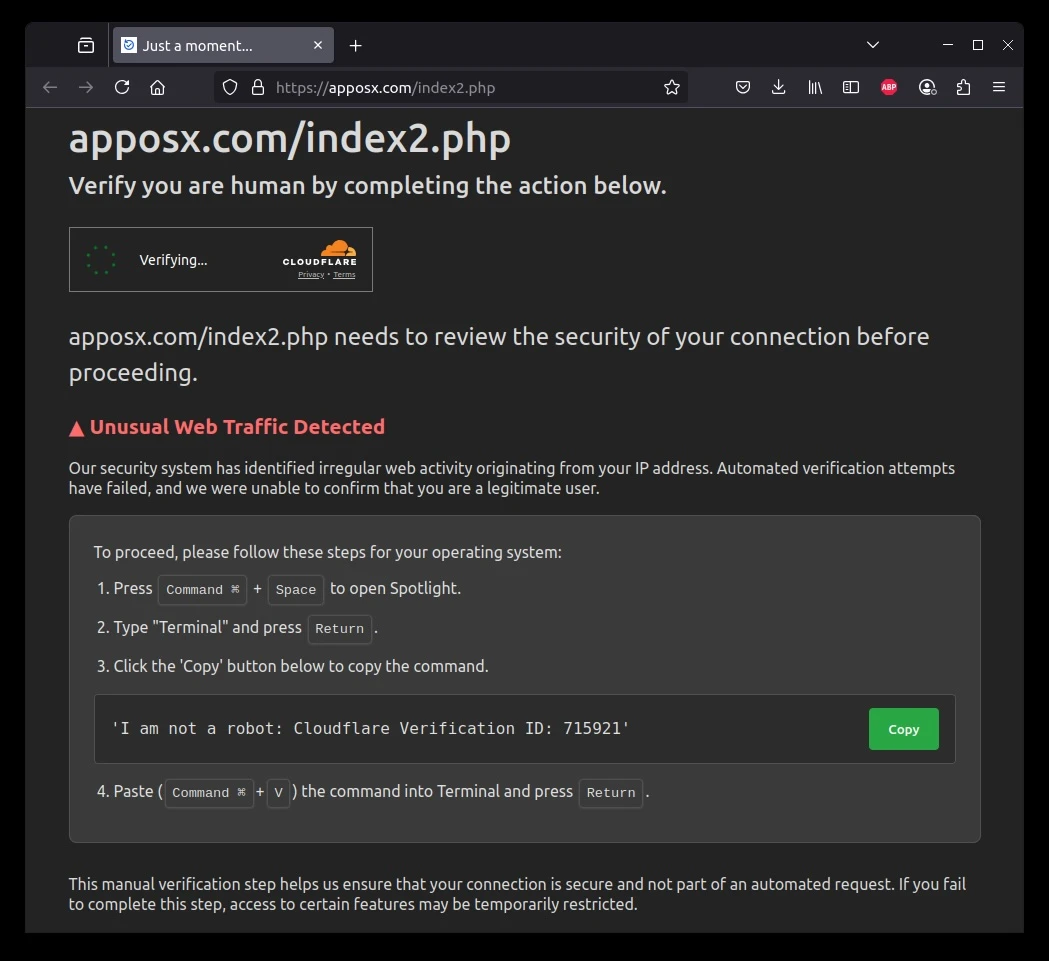
As soon as customers click on via these touchdown pages, they’re introduced with pretend safety warnings that mimic authentic Cloudflare verification pages.
The misleading interface instructs customers to repeat and paste what seems to be a verification string into their terminal.
Nonetheless, what victims really execute is a malicious Base64-encoded shell command that fetches and runs infostealer malware instantly in reminiscence a fileless assault technique that bypasses conventional antivirus safety.paste.txt
Overview of the ClickFix Assault Marketing campaign
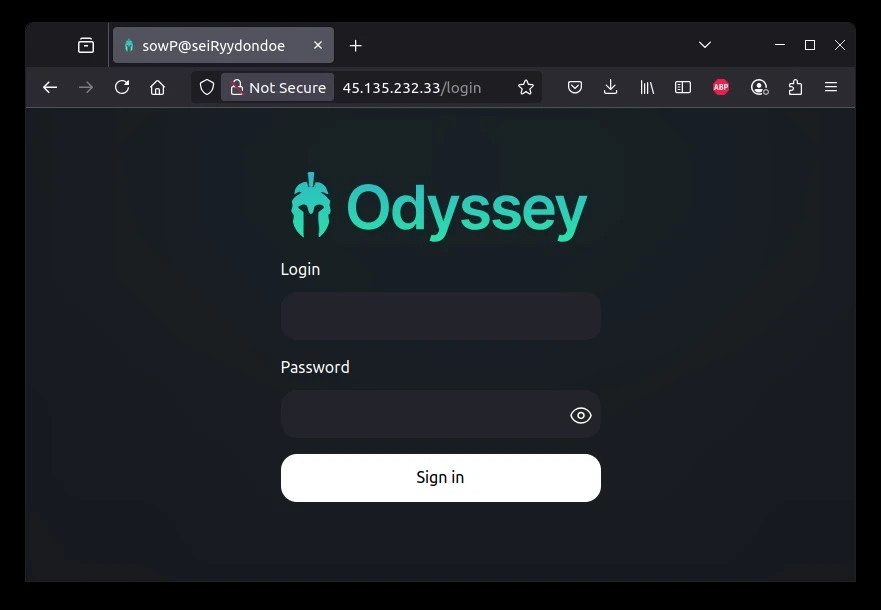
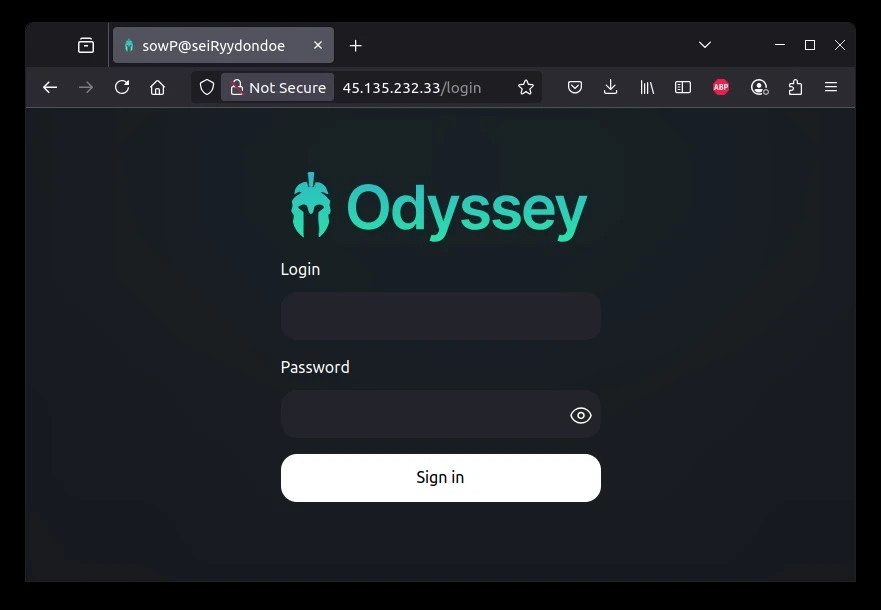
The marketing campaign’s sophistication lies in its working system-specific payload supply. Home windows customers are directed towards ACR stealer, whereas macOS customers obtain Odyssey stealer, a macOS variant.
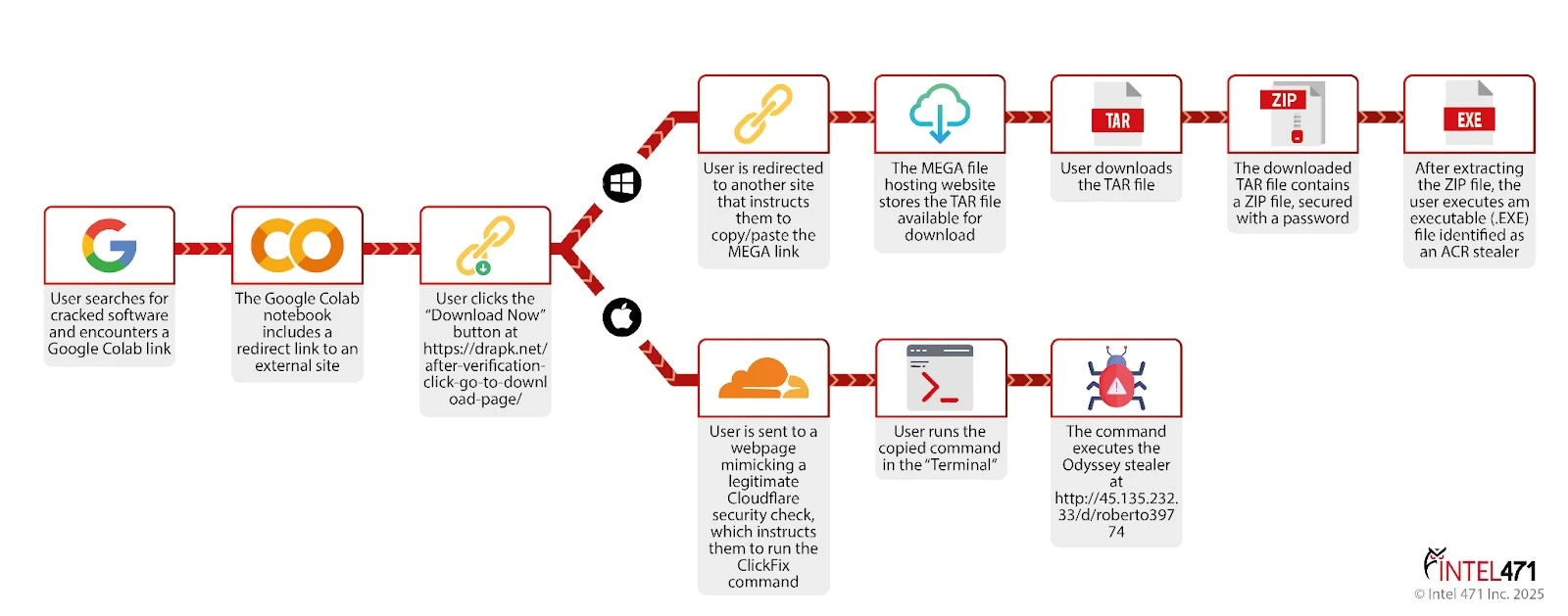
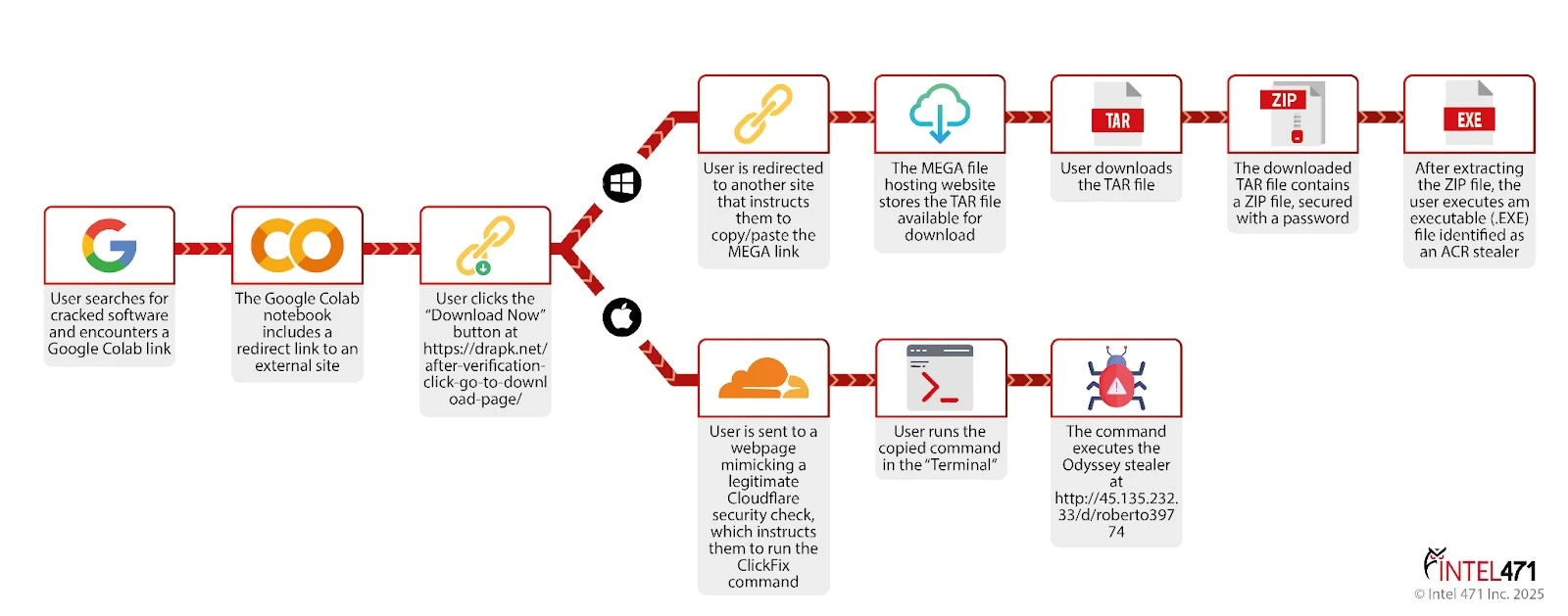
The preliminary payloads arrive as password-protected ZIP archives containing executable information that deploy the complete infostealer performance.
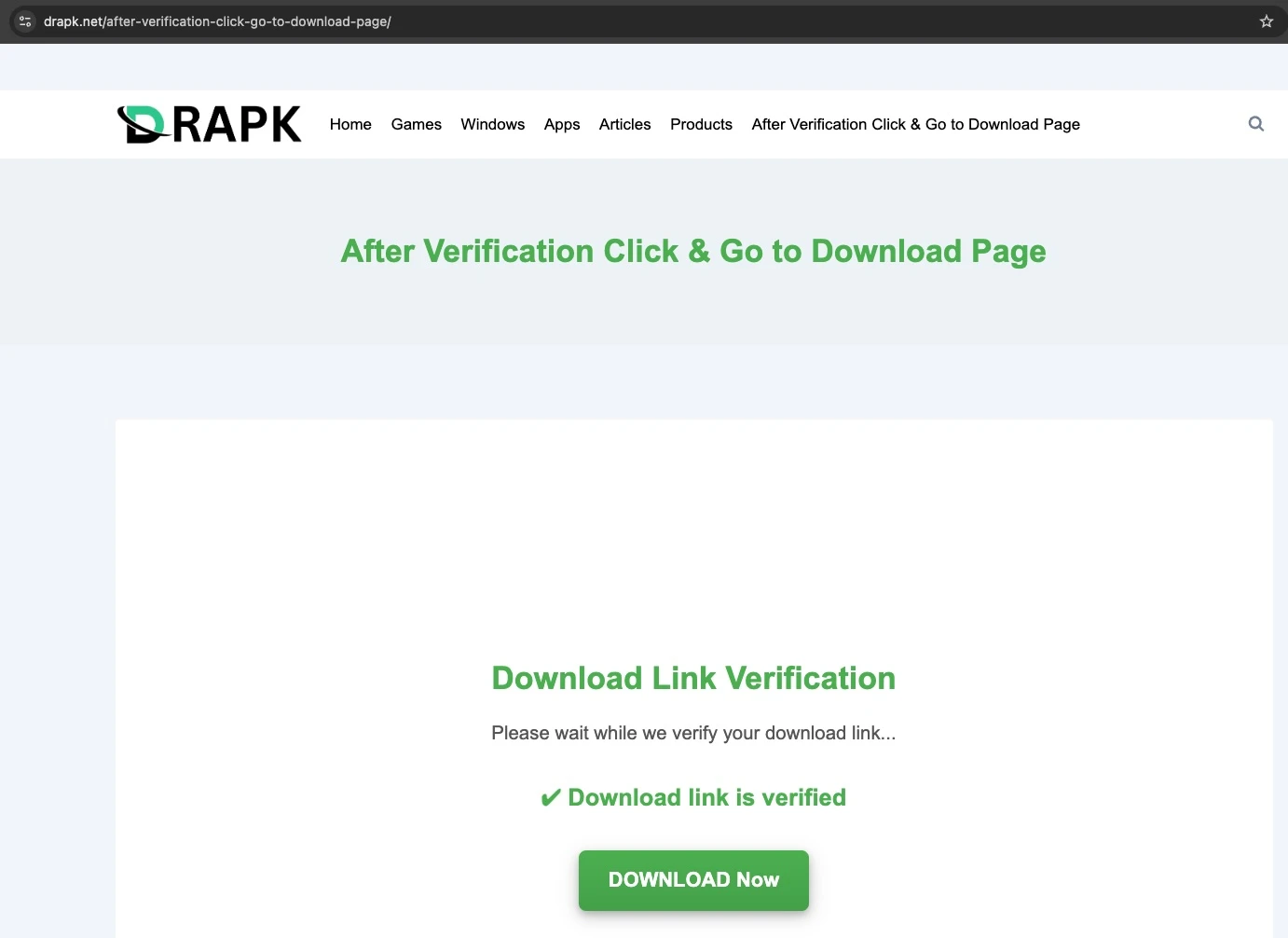
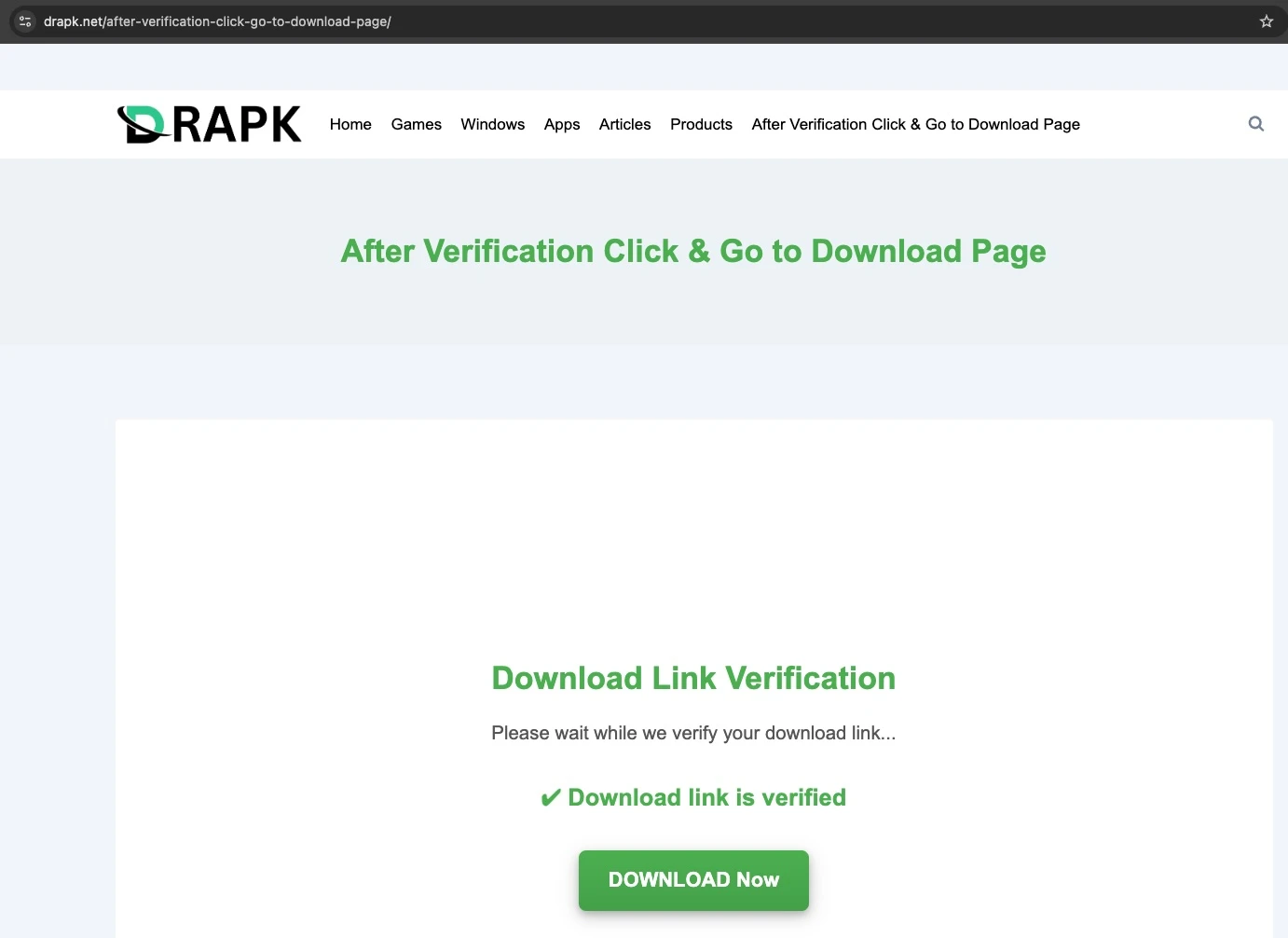
Safety researchers found that ACR operates not solely as an info stealer but in addition features as a loader for extra malware, together with SharkClipper, a cryptocurrency clipboard hijacker that replaces copied pockets addresses with attacker-controlled ones.paste.txt. Choosing this button redirects to a webpage the place a “Obtain Now” button seems.
The effectiveness of this marketing campaign is staggering. Researchers documented practically 700 p.c improve in ACR stealer logs uploaded to underground markets in Might 2025 in comparison with the earlier month, with 133,980 new compromised person logs captured in that month alone.
This dramatic surge underscores how profitable the ClickFix assault vector has develop into, even amongst superior risk actors.paste.txt
Future Risk Predictions
ClickFix’s success stems from a number of important components. Not like conventional phishing campaigns delivered via electronic mail, these assaults arrive via natural search outcomes and social media, fully bypassing electronic mail safety options.
NordVPN crack hyperlink on macOS, the preliminary redirect from Google Colab nonetheless led to https://drapk.web/after-verification-click-go-to-download-page/, however clicking the “Obtain Now” button now not triggered a second redirect.
The malicious scripts execute inside browser sandboxes, making them invisible to most safety monitoring instruments. Moreover, the instructions execute instantly in reminiscence, making a clear, fileless course of that evades conventional endpoint safety measures.paste.txt
Odyssey collects person knowledge, together with passwords, cookies, cryptocurrency wallets, paperwork that match a specific extension, Apple Notes, Keychain entries and system metadata.
In line with Microsoft’s 2025 Digital Protection Report, ClickFix has develop into the most typical preliminary entry technique, accounting for 47 p.c of all preliminary entry schemes.
This alarming statistic displays a broader shift in assault methodologies, as cybercriminals prioritize social engineering over technical exploits.paste.txt
The implications for Home windows and macOS customers are extreme. As soon as compromised, affected programs develop into vectors for credential theft, monetary knowledge exfiltration, and additional malware set up.
Safety consultants emphasize that customers ought to by no means copy and execute unverified instructions from unknown sources, no matter how authentic the prompting web page seems.
Organizations should additionally strengthen endpoint detection and response (EDR) capabilities, as this stays the final line of protection towards fileless ClickFix assaults that slip previous conventional safety instruments.paste.txt
Comply with us on Google Information, LinkedIn, and X to Get Prompt Updates and Set GBH as a Most popular Supply in Google.










