Cybersecurity researchers have found a brand new, extremely harmful Android banking malware referred to as Sturnus, named after the frequent starling or ‘songbird’ due to its complicated and ‘chaotic’ communication model.
The Dutch cybersecurity agency ThreatFabric recognized this privately-operated risk, which has options which are merely way more superior and harmful than what we’ve seen earlier than.
Based on ThreatFabric’s weblog put up, revealed on November 20, 2025, Sturnus is way extra superior than earlier malware, able to stealing your financial institution particulars, in a position to view chat content material on apps like WhatsApp, Telegram, and Sign by abusing Android’s Accessibility Service
The way it Decodes Your ‘Encrypted’ Chats
Although these apps use end-to-end encryption, which suggests solely you and the individual you’re chatting with can learn the messages, Sturnus fully will get round this safety. It really works by counting on the Android Accessibility Service to learn the message content material instantly from the display screen after the official app has decrypted it. This implies the attackers can see full conversations, contacts, and all incoming and outgoing messages in actual time.
A Absolutely Featured Menace
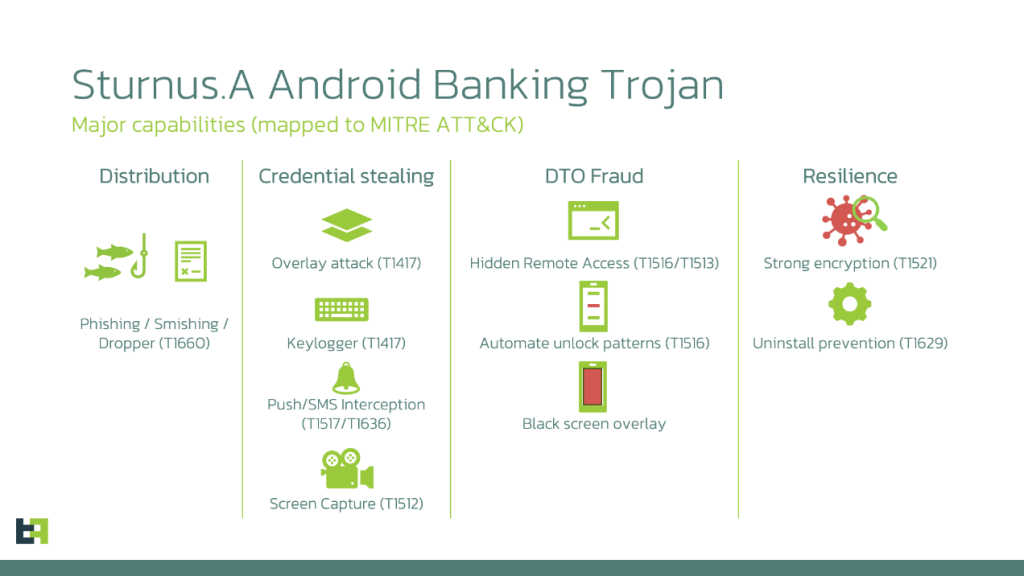
The malware is distributed via social engineering campaigns, together with Phishing (electronic mail), Smishing (SMS textual content messages), or by way of a malicious Dropper software, which tips customers into putting in the ultimate malware as an unofficial APK file
As soon as Sturnus infects a cellphone, it makes use of two built-in strategies to steal delicate information: deploying faux login screens, referred to as HTML overlays, that completely mimic banking apps; and concurrently using a complete keylogging pipeline by way of the Accessibility Service to report each keystroke and display screen faucet.
Additional probing revealed that the malware offers the attackers intensive distant management. They will sort, monitor all exercise, and, most disturbingly, show a black display screen overlay to cover their actions whereas it silently executes fraudulent transactions within the background. The malware even makes use of its keylogging skill to steal PINs and Passwords, making it straightforward to unlock the system itself.
The Assault Standing and Targets
It’s price noting that Sturnus is extremely persistent. It positive aspects particular privileges on the cellphone, referred to as Gadget Administrator rights, and actively protects them. If a consumer tries to disable these rights or uninstall the malware in settings, Sturnus detects the try and routinely stops the motion. This defence makes it very troublesome to eliminate it as soon as put in.
Researchers assess that though this malware will not be but widespread and is at the moment in an early testing section, it’s already totally purposeful. Its configurations present a direct concentrate on focusing on monetary establishments throughout Southern and Central Europe. This focus on high-value apps and particular areas suggests the criminals are merely preparing for a a lot bigger, extra coordinated international assault.
Knowledgeable Commentary
In commentary shared completely with Hackread.com, Aditya Sood, VP of Safety Engineering and AI Technique at Aryaka, supplied perception into the malware’s technical edge and broader dangers.
“Sturnus poses a special sort of risk in comparison with different Android malware as a result of its skill to make use of a mixture of plaintext, RSA, and AES-encrypted communication with the C2 server it responds to,” Sood mentioned.
“The mix of those three permits Sturnus to mix extra simply into regular community patterns, whereas additionally hiding instructions and stolen information from defence methods. This superior degree of evasion and resilience from the malware disrupts signature-based detection and may impede reverse-engineering efforts, making it tougher to examine Sturnus’ community visitors or recuperate the contents that it steals.”
Sood additionally highlighted the chance to organisations: “As a banking trojan, Sturnus is primarily focusing on monetary organisations. Nonetheless, the flexibility to steal messages from end-to-end encrypted platforms like Sign might spell critical issues for organisations, as these purposes are used throughout a number of industries to safe delicate or confidential info.”
He advises, “People who’re at-risk, or who’re in charge of delicate info, should keep away from downloading APK information from outdoors Google Play, and will constantly monitor for malicious exercise if an infection is suspected.”