Open Supply Safety Basis (OpenSSF), a bunch of open supply software program safety specialists, is warning a couple of new phishing rip-off the place hackers are concentrating on software program builders utilizing the Slack chat app.
These scammers faux to be well-known leaders from the Linux Basis, with the intention of getting builders to obtain malware that would give them complete management over a pc. Their modus operandi relies on mimicking a reputable Google Workspace stream, which redirects unsuspecting builders to a malicious web page.
How the rip-off works
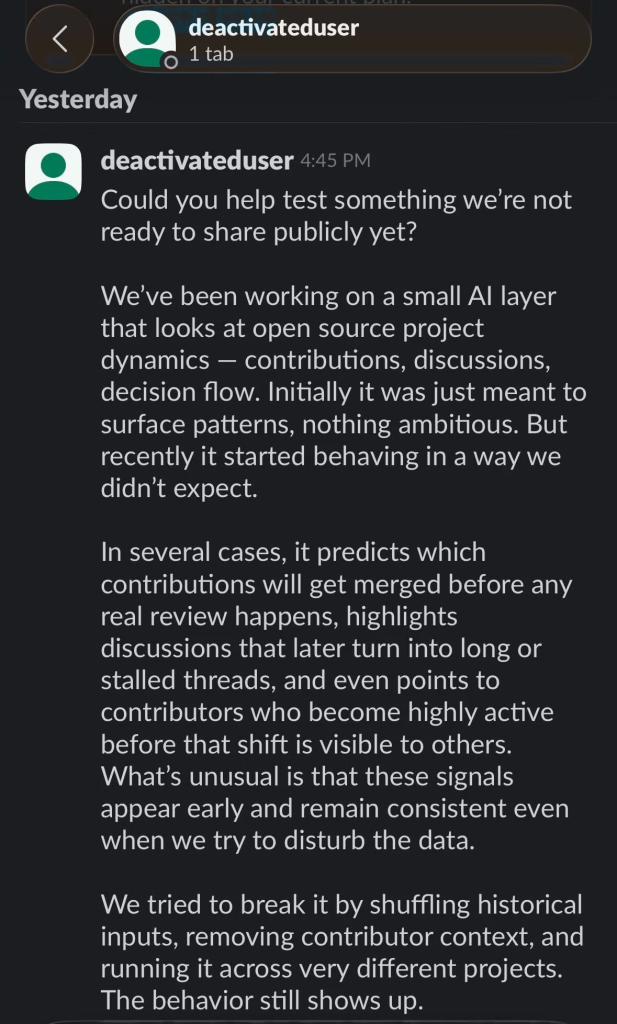
Researchers famous within the safety advisory that the assault particularly focused the TODO Group Slack workspace, which is a neighborhood for open supply professionals. It begins with a easy non-public message supposedly from a neighborhood chief, however truly, it’s the scammer.
The message is a couple of new, secret AI device that may guess which bits of code might be accepted by a challenge earlier than anybody even seems to be at them. To make it appear actual, they are saying they’re “solely sharing this with a couple of individuals for now,” and even present a faux e mail ([email protected]) and an entry key (CDRX-NM71E8T) to look official.
If an individual believes the story, they’re despatched to an internet site that appears like a standard Google web page. This web site asks for an e mail and a particular code. When the particular person enters these particulars, the positioning asks them to put in a Google certificates, which is a malicious root certificates that lets hackers bypass safety to spy in your non-public, encrypted net site visitors and steal your information. Merely put, it lets the hackers monitor the whole lot the particular person does on-line.
The now-deleted hyperlink used within the marketing campaign: https://websites.google.com/view/workspace-business/be a part of.
Totally different Dangers for Mac and Home windows
Additional investigation revealed that the assault adjustments relying on the pc you employ. On Apple Mac computer systems, the positioning tries to run a file referred to as gapi, which might result in a full system takeover. On Home windows, the positioning tries to get the person to click on a button to belief the faux certificates.
It should be famous that these ways are much like these utilized in a current marketing campaign in opposition to builders of different fashionable software program like Node.js, and safety researchers at Mandiant have linked these assaults to North Korean state-sponsored hackers.
Christopher Robinson, a high safety skilled at OpenSSF, says that folks ought to by no means belief a message simply due to the identify or picture on the profile. He additionally gave some clear recommendation for anybody utilizing these discussion groups: “Don’t set up certificates from hyperlinks,” as most actual firms won’t ever ask you to try this.
In case you suspect that you simply clicked a suspicious hyperlink, instantly change all of your passwords and at all times use further login steps, like utilizing MFA (multi-factor authentication) to maintain your accounts secure.
Picture by Jon Tyson on Unsplash