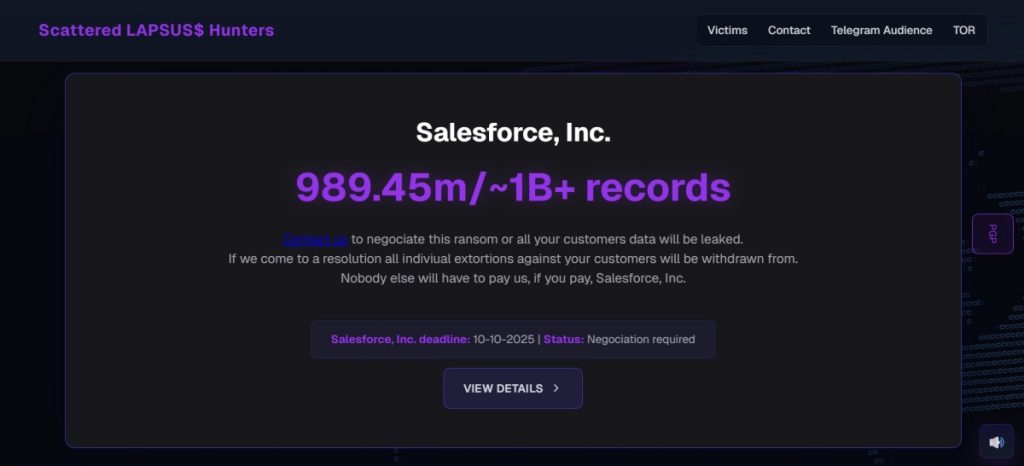
A brand new leak website has gone dwell, operated by the infamous group calling itself “Scattered Lapsus$ Hunters,” (a coalition that mixes the techniques and branding of Scattered Spider, Lapsu$, and ShinyHunters) and it carries a daring declare that Salesforce, one of many largest SaaS and CRM suppliers on this planet, has been breached and shut to 1 billion information (989 million information) are up on the market.
The group says the assault befell in mid-2024 and that the stolen knowledge quantities to a number of terabytes. In messages posted to their website, they allege the info consists of extremely delicate private data resembling Social Safety numbers, driver’s licenses, and dates of delivery. They’re now demanding that Salesforce negotiate earlier than an October 10, 2025, deadline, warning that failure to take action will end result within the launch of the total cache.
Moreover, the hackers are additionally inviting legislation corporations to cooperate with them, even naming Berger Montague as a accomplice they’d share proof with. The hackers are presenting this much less like a menace and extra like a proposal. In addition they declare they may present detailed documentation to courts and regulators in america and Europe, alleging Salesforce acted with “prison negligence” by failing to dam repeated intrusions.
The checklist of firms named as victims on the leak website is very large. The group has listed 39 organizations whose knowledge they are saying was taken from Salesforce-hosted methods. The checklist consists of:
- KFC – 1.3GB
- ASICS – 9GB
- UPS – 91.34GB
- IKEA – 13GB
- GAP, INC. – 1GB
- Petco – 9.9GB
- Cisco – 5.6GB
- McDonald’s – 28GB
- Cartier – 1.4GB
- Adidas – 37GB
- Fujifilm – 155MB
- Instacart – 32GB
- Marriott – 7GB
- Walgreens – 11GB
- Pandoranet – 8.3GB
- Chanel – 2GB
- CarMax – 1.7GB
- Disney/Hulu – 36GB
- TransUnion – 22GB
- Aeroméxico – 172.95GB
- Toyota Motor Firms – 64GB
- Stellantis – 59GB
- Republic Companies – 42GB
- TripleA (aaacom) – 23GB
- Saks Fifth – 1.1GB
- Albertsons (Jewel Osco, and so forth) – 2GB
- Engie Sources (Plymouth) – 3GB
- 1-800Accountant – 18GB
- HMH (hmhcocom) – 88GB
- Instructurecom – Canvas – 35GB
- Google Adsense – 19GB
- HBO Max – 3.2GB
- FedEx – 1.1TB
- Qantas Airways – 153GB
- Vietnam Airways – 63.62GB
- Air France & KLM – 51GB
- House Depot – 19.43GB
- Kering (Gucci, Balenciaga, Brioni, AlexMcQ) – 10GB
Hackers Accuse Salesforce of Failure
The hackers accuse Salesforce of failing to implement multi-factor authentication and say they efficiently focused greater than 100 further unnamed situations via OAuth software weaknesses. In addition they level to earlier warnings, claiming they emailed Salesforce in July 2025 from an tackle linked to the operation and obtained no significant response.
The hackers current their message as half ransom demand, half technical briefing. They level out that their assaults ran for a yr, left clear traces, and argue Salesforce had sufficient time to identify and cease them
In addition they cite GDPR, CCPA, and HIPAA obligations, arguing that knowledge safety duties had been ignored. To again this up, they promise to launch forensic-style paperwork with assault fingerprints, affected populations damaged down by nation, and particulars in regards to the varieties of data uncovered.
The attackers present a tuta.io primarily based contact tackle and require any communication to incorporate a strict verification format within the topic line. They are saying verified representatives will then be forwarded to a dwell channel the place negotiations can happen.
Salesforce Apparently Is aware of
The hackers have additionally circulated a screenshot on their Telegram channel that seems to point out a Salesforce safety advisory acknowledging ongoing extortion makes an attempt. Within the message, Salesforce refers to social engineering threats, states that there isn’t a proof its platform was compromised, and reassures prospects that its groups are monitoring the scenario.
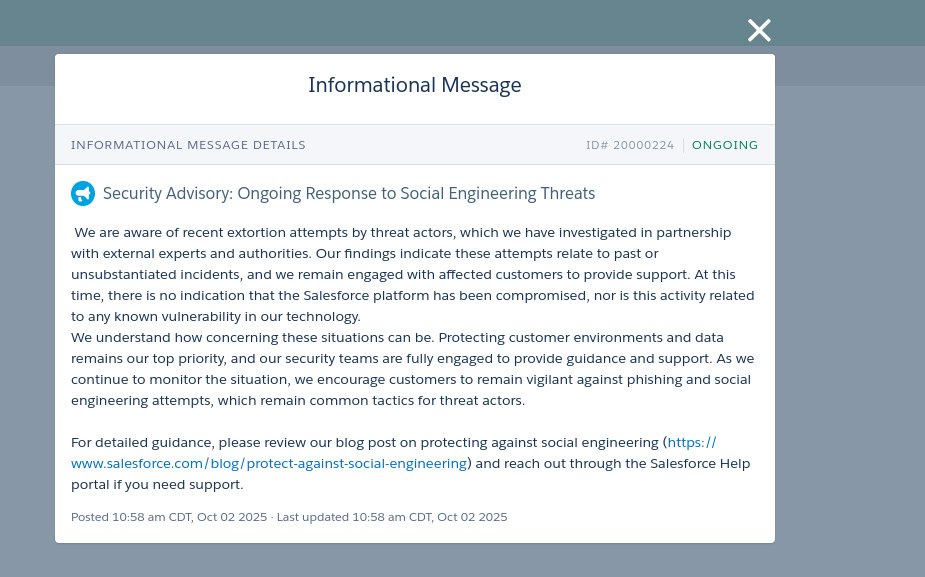
Because the picture can’t be independently verified, it’s unclear whether or not this advisory is genuine or fabricated as a part of the attackers’ marketing campaign. However, the group’s website maintains the deadline of October 10, 2025, with the standing listed as “Lively.” And, with the location dwell, the group now has a public device to extend stress on the corporate because the deadline approaches.